Source | Quantum Bit
How many lobsters are running naked on the internet?
The AI agent exposes your passwords and API keys to the entire web.
Illia Polosukhin, the author of Transformer, couldn't stand it any longer. He took action and reconstructed the secure version of the lobster: IronClaw.

IronClaw is now open-source on GitHub, providing installation packages for macOS, Linux, and Windows, supporting local deployment as well as cloud hosting. The project is still in rapid iteration, with binary files for version v0.15.0 now available for download.
Polosukhin (hereafter referred to as Brother Pineapple) also opened a thread on Reddit to respond to everything, gaining significant attention.
01 OpenClaw became popular, but also "on fire"
Brother Pineapple himself was an early user of OpenClaw and claimed it was the technology he had waited 20 years for.
It has changed the way I interact with computing.
However, the security status of OpenClaw is a disaster, with one-click remote code execution, prompt injection attacks, and malicious skills stealing passwords, all of these vulnerabilities have been exposed one by one in the OpenClaw ecosystem.
Over 25,000 public instances are exposed on the internet without sufficient security controls, directly referred to by security experts as a "security dumpster fire."

The root of the problem lies in the architecture itself.
When users give their email Bearer Token to OpenClaw, it is sent directly to the LLM provider’s servers.
Brother Pineapple pointed out on Reddit what this means:
All your information, even data that you did not explicitly authorize, could be accessed by any employee of that company. This applies equally to your employer’s data. It’s not that these companies have malicious intent, but the reality is that users do not have true privacy.
He stated that no convenience is worth risking the safety and privacy of oneself and one’s family.
02 Rebuilding everything from scratch with Rust
IronClaw is a complete rewrite of OpenClaw in Rust.
The memory safety features of Rust can fundamentally eliminate traditional vulnerabilities like buffer overflows, which is crucial for systems that need to handle private keys and user credentials.
In terms of security architecture, IronClaw has established a four-layer defense in depth.
The first layer is the memory safety guarantees provided by Rust itself.
The second layer is WASM sandbox isolation, where all third-party tools and AI-generated code run in independent WebAssembly containers. Even if a tool is malicious, its range of destruction is strictly limited to the sandbox.
The third layer is an encrypted credential vault, where all API keys and passwords are encrypted using AES-256-GCM and each credential is bound by policy rules, specifying it can only be used for a specific domain.
The fourth layer is a Trusted Execution Environment (TEE), utilizing hardware-level isolation to protect data, ensuring that even cloud service providers cannot access sensitive user information.
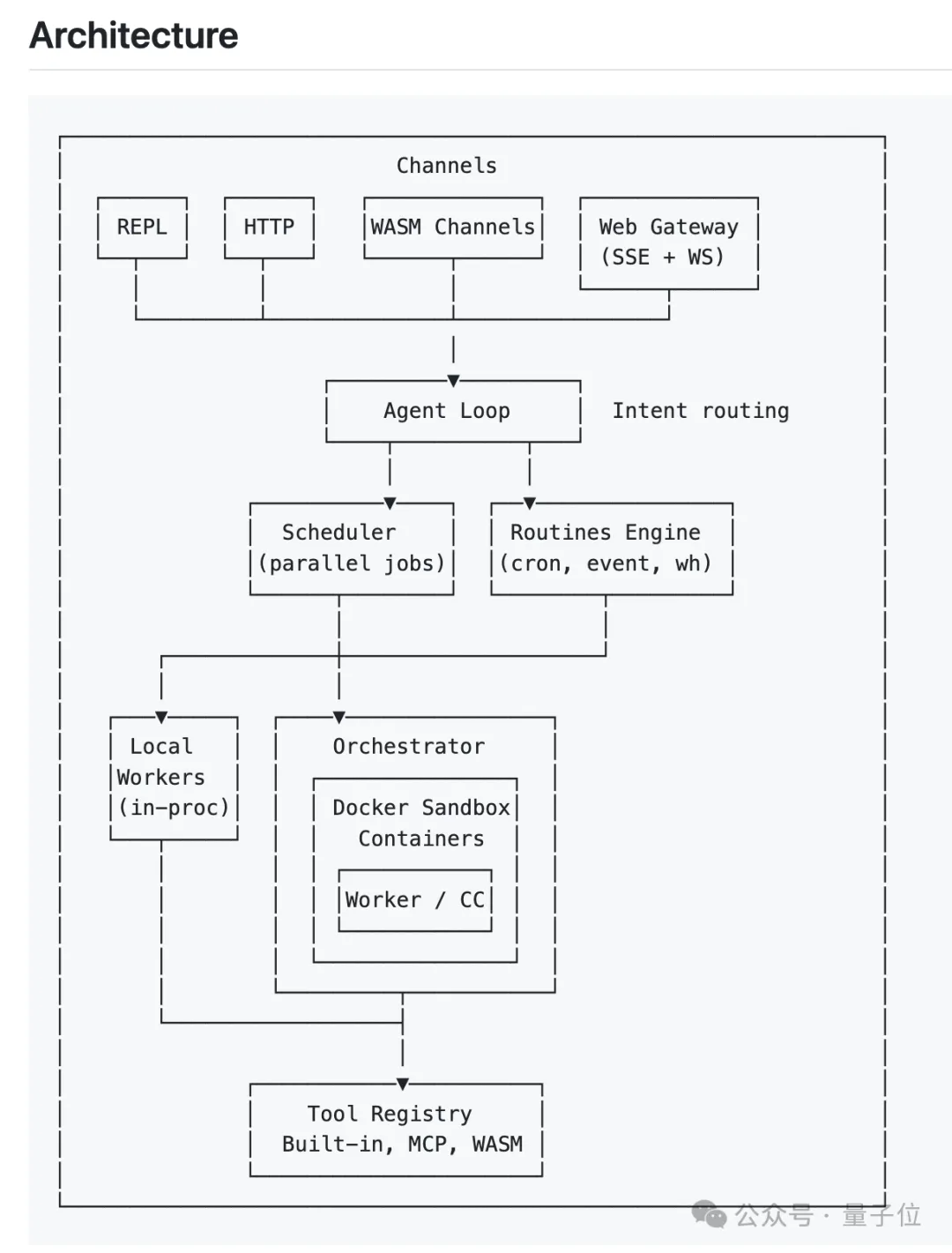
The most critical point of this design is: the large model itself never touches the original credentials.
Credentials are only injected at the network boundary when the agent needs to communicate with external services.
Brother Pineapple gave an example, even if the large model is subjected to a prompt injection attack attempting to send the user's Google OAuth token to the attacker, the credential storage layer will directly reject the request, log it, and alert the user.
However, the developer community is still concerned, after all, OpenClaw has over 2000 public instances attacked and there are numerous malicious skills. Will IronClaw repeat the same mistakes if it becomes popular?
Brother Pineapple's response is that the architectural design of IronClaw has fundamentally blocked the core vulnerabilities of OpenClaw. Credentials are always stored encrypted and never touch the LLM, and third-party skills cannot execute scripts on the host, they can only run inside containers.
Even when accessed through CLI, a user’s system keychain is needed to decrypt, and the encrypted keys obtained are meaningless by themselves.
He also stated that as the core version stabilizes, the team plans to conduct red team testing and professional security audits.
Regarding the well-known industry problem of prompt injection, Brother Pineapple provided more detailed ideas.
Currently, IronClaw uses heuristic rules for pattern detection, and the future goal is to deploy a sustainably updated small language classifier to identify injection patterns.
But he also admitted that prompt injection can not only steal credentials but also directly tamper with the user's code repository or send malicious messages through communication tools.
Responding to such attacks requires a smarter strategy system capable of reviewing the agent's behavioral intentions without looking at input content, "more work is needed, and community contributions are welcome."
Someone asked about the trade-offs between local deployment and cloud deployment.
Brother Pineapple believes pure local solutions have obvious limitations: the agent stops working when the device is powered off, the energy consumption on mobile ends is hard to bear, and complex long-running tasks cannot be executed.
He believes that confidential cloud is currently the optimal compromise, providing privacy protection close to local devices while solving the "always online" problem.
He also mentioned a detail: users can set policies, for example, to automatically add additional security barriers during cross-border travel to prevent unauthorized access.
03 A bigger ambition
Brother Pineapple is not an ordinary open-source developer.
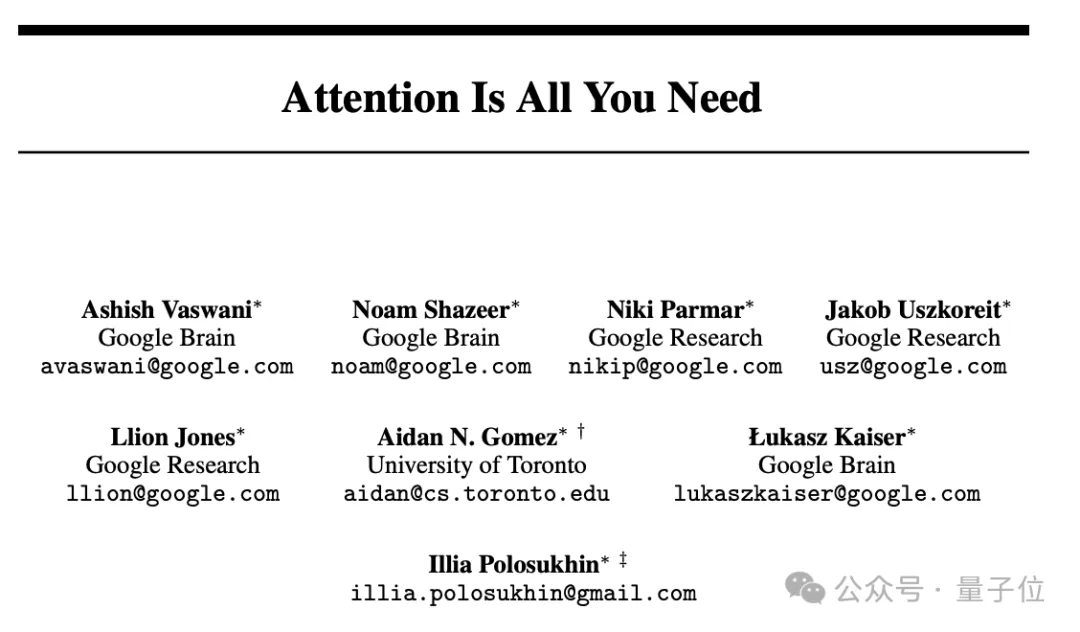
In 2017, he was one of eight co-authors of "Attention Is All You Need," which proposed the Transformer architecture that laid the foundation for all current large language models.
Although he is listed last in the authorship, there is a footnote in the paper stating "Equal contribution. Listing order is random." The ranking is purely random.
However, that same year he left Google and founded NEAR Protocol, focusing on integrating AI with blockchain technology.
IronClaw is part of a bigger strategic vision behind NEAR Protocol: User-Owned AI.
In this vision, users have complete control over their data and assets, and AI agents perform tasks on behalf of users in a trusted environment.
NEAR has built infrastructures such as AI cloud platforms and decentralized GPU markets for this purpose, and IronClaw serves as the runtime layer of this system.
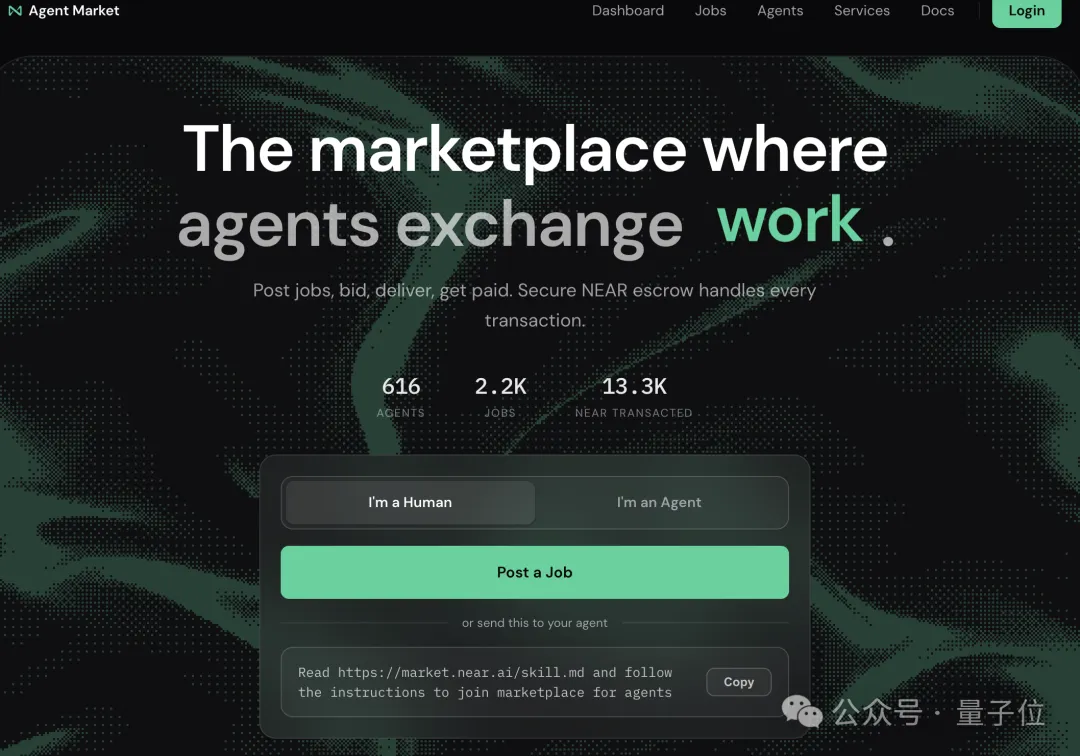
Brother Pineapple even developed a market for AI agents to hire each other.
On NEAR's market.near.ai, users can register their specialized AI agents, and as the agents accumulate reputations, they will receive more high-value tasks.
When asked how ordinary people should adapt to the AI era in the next five years, Brother Pineapple's advice is to quickly adopt the working methods of AI agents and learn to automate the entire workflow.
This judgment of his did not suddenly emerge recently.
As early as when founding NEAR AI in 2017, Brother Pineapple was telling everyone "in the future, you will only need to talk to the computer, you will no longer need to write code."
At the time, people thought they were crazy, speaking nonsense.
Nine years have passed, and this is becoming a reality.
"AI agents are the ultimate interface for human interaction with everything online," Polosukhin wrote, "but let’s make it safe."
---
GitHub address:
https://github.com/nearai/ironclaw
Reference links:
[1] https://www.reddit.com/r/MachineLearning/comments/1rlnwsk/d_ama_secure_version_of_openclaw/
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




