Author: Zoltan Vardai
Compiled by: Deep Tide TechFlow
Deep Tide Introduction: Security researchers have discovered that the North Korean hacker organization Lazarus is using a new macOS malware called "Mach-O Man" to target executives of cryptocurrency firms and traditional financial companies through fake Zoom and Google Meet meeting links. Victims are induced to execute commands, after which the malware steals sensitive data such as browser credentials and Keychain passwords in the background, ultimately transmitting it via Telegram. Lazarus is indeed the mastermind behind the $1.4 billion theft incident at Bybit in 2025.
Security researchers have linked a new macOS malware activity to the Lazarus Group. Lazarus is a North Korean-associated hacking organization, responsible for some of the largest thefts in the cryptocurrency industry.
Mauro Eldritch, founder of the threat intelligence company BCA Ltd and an attack security expert, revealed this new malware toolkit named "Mach-O Man" on Tuesday. It spreads through ClickFix social engineering methods, targeting traditional businesses and cryptocurrency companies.
Attack Path: Fake Zoom Meeting → Backdoor Installation
The specific method works like this: victims are lured into joining a fake Zoom or Google Meet video call, and the page prompts them to execute a command. Once executed, the malware completes the download in the background, bypassing traditional security controls and triggering no alarms, directly obtaining your credentials and enterprise system permissions.
Eldritch noted in a report released on Tuesday that this attack could lead to account takeover, unauthorized infrastructure access, financial loss, and critical data leaks. The scope of Lazarus's attacks has expanded beyond cryptocurrency-native companies.
The Lazarus Group is a primary suspect in several of the largest cryptocurrency hacking incidents in history, including the 2025 $1.4 billion theft from Bybit exchange, which remains the largest single theft in the industry.
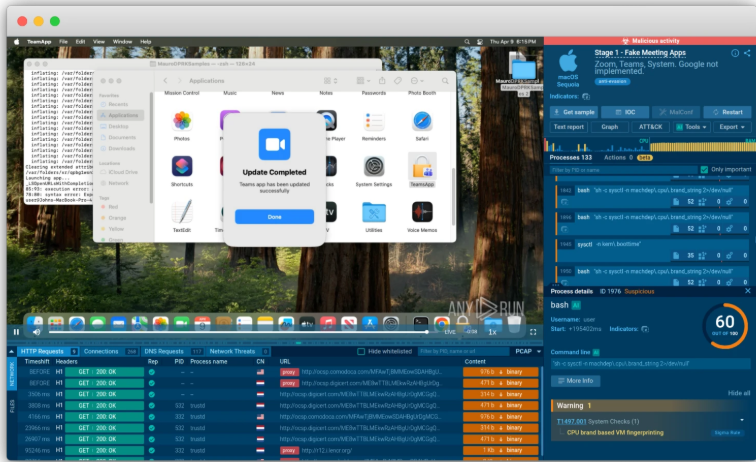
Figure caption: Fake Mach-O Man toolkit application interface
Source: ANY.RUN
Ultimate Goal: Steal Everything in Browser and Keychain
The final stage of the attack chain is a stealer program, specifically designed to extract browser extension data, saved browser credentials, cookies, macOS Keychain entries, and other sensitive information.
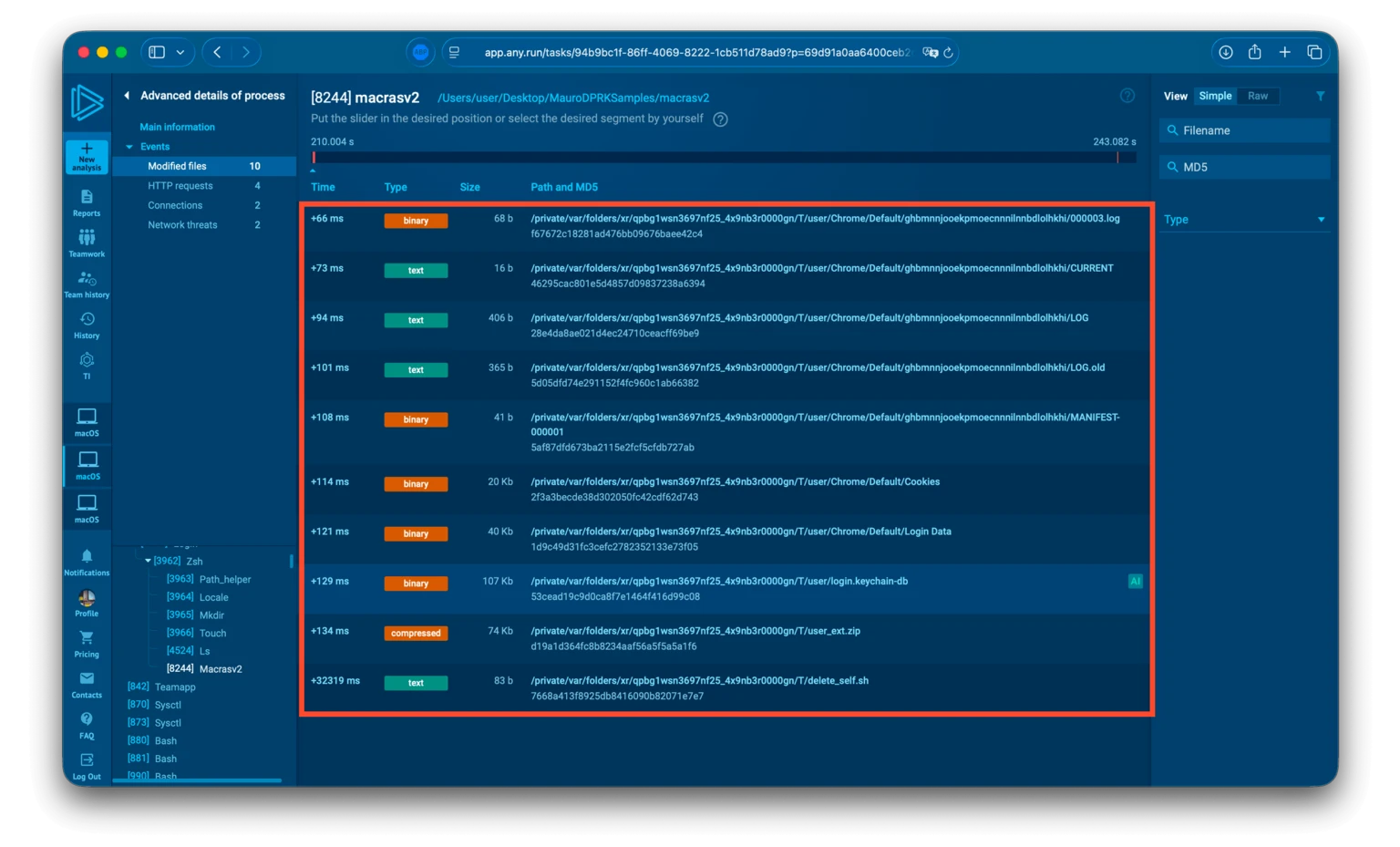
Figure caption: Final deployment directory structure of the stealer program
Source: ANY.RUN
Once the data collection is complete, the malware packages everything into a zip file and sends it to the attacker via Telegram. Finally, the malware's self-destruct script uses the system's rm command to delete the entire toolkit, a command that skips user confirmation and permission checks, forcibly deleting files without leaving traces.
This new malware toolkit was reconstructed by security experts using ANY.RUN's cloud macOS malware sandbox analysis capabilities.
North Korean Hacker Attack Surface Continues to Expand
Earlier this April, North Korean hackers stole approximately $100,000 from the cryptocurrency wallet Zerion using AI-driven social engineering techniques. The attackers gained access to logged-in sessions, credentials, and company private keys of some team members.
Additionally, CZ recently issued a warning that the security team "SEAL" discovered 60 infiltrators posing as IT workers associated with North Korea within cryptocurrency companies.
The infiltration of the North Korean hacking scene into the cryptocurrency industry is no longer just a simple "hacking attack." From posing as employees to AI social engineering and customized malware, the attack surface continues to expand. macOS users have always been considered relatively safe, but Lazarus clearly disagrees.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




