Author: ZachXBT
Compiled by: Deep Tide TechFlow
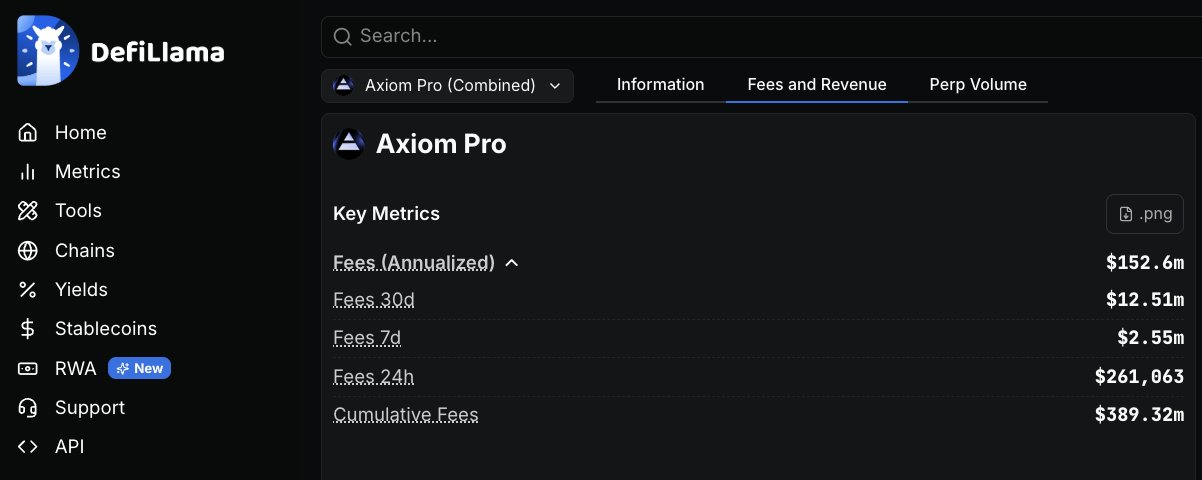
Deep Tide Introduction: On-chain detective ZachXBT has released a complete investigation report, accusing multiple employees of the cryptocurrency exchange Axiom of abusing internal system permissions for over a year to query users' private wallet information and engage in insider trading. The investigation was initiated at the request of a client, and the evidence includes recorded calls, internal screenshots, and on-chain fund flow charts. The employees involved were reported to have planned to help their accomplices earn $200,000 quickly. Axiom has generated more than $390 million in revenue to date, and this case reveals significant loopholes in the internal permission control of cryptocurrency platforms.
(1)
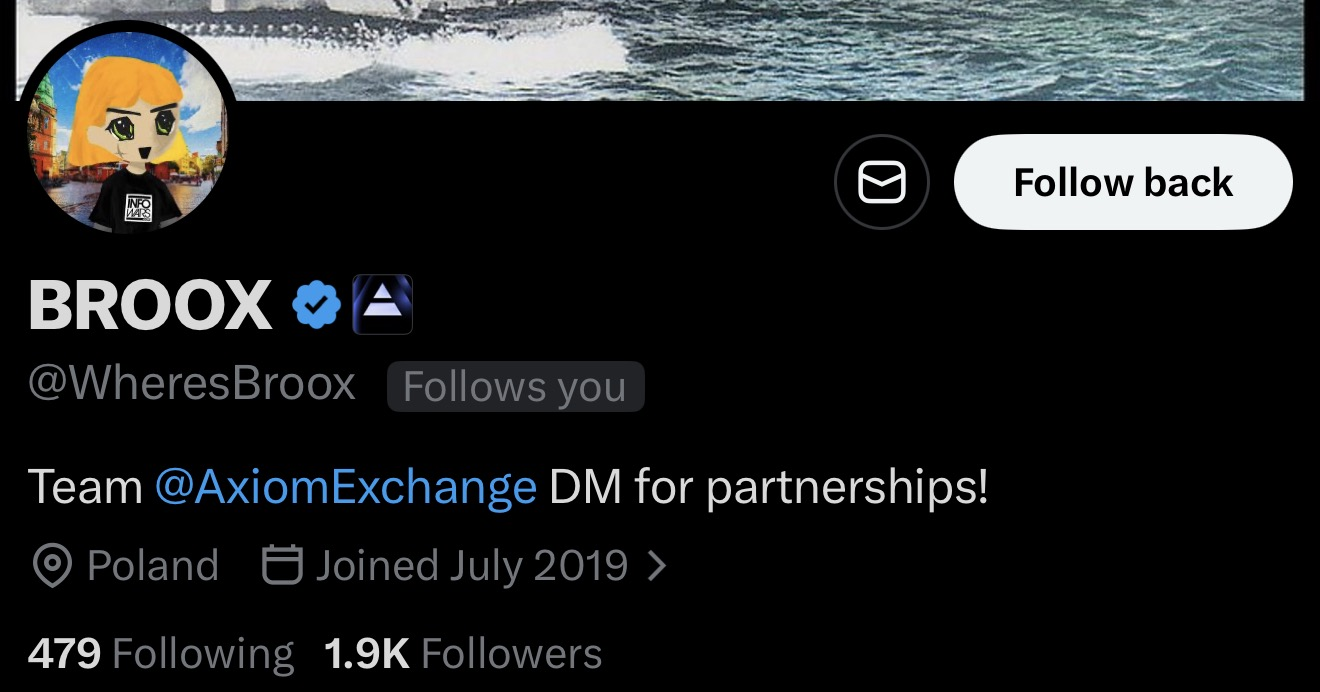
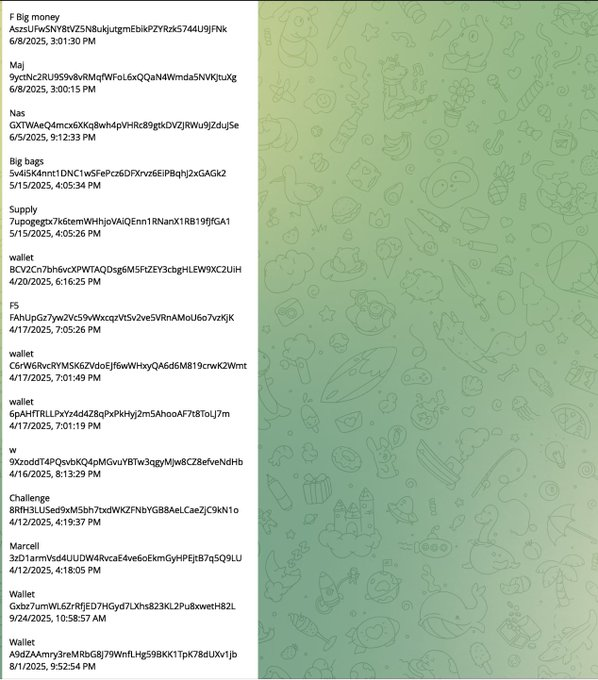
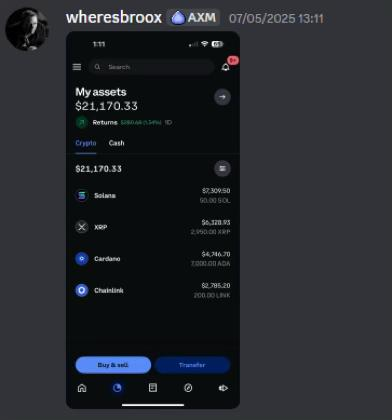
Meet @WheresBroox (Broox Bauer). He is one of the employees involved at @AxiomExchange, accused of using internal tools due to inadequate permission control to query sensitive user information since early 2025 and engage in insider trading by tracking private wallet activities.
(2)
Axiom is a cryptocurrency exchange platform founded by Mist and Cal in 2024. After being incubated in Y Combinator's Winter 2025 batch, it quickly became one of the most profitable companies in the field, accumulating over $390 million in revenue to date.
I was commissioned by a client to investigate the allegations of misconduct at Axiom after receiving relevant reports.
(3)
Broox is currently a senior business development employee at Axiom, based in New York.
In a recording, Broox stated that he could track any Axiom user through referral codes, wallet addresses, or UIDs, claiming he could "find out everything about this person."
He also described initially only checking 10 to 20 wallets and gradually increasing over time — "this way it wouldn't seem so suspicious."
In another segment of the same recording, Broox established rules for team members to apply to him for queries and stated he would send over the complete wallet list.
This full recording comes from a covert planning call among members of the group.
(4)
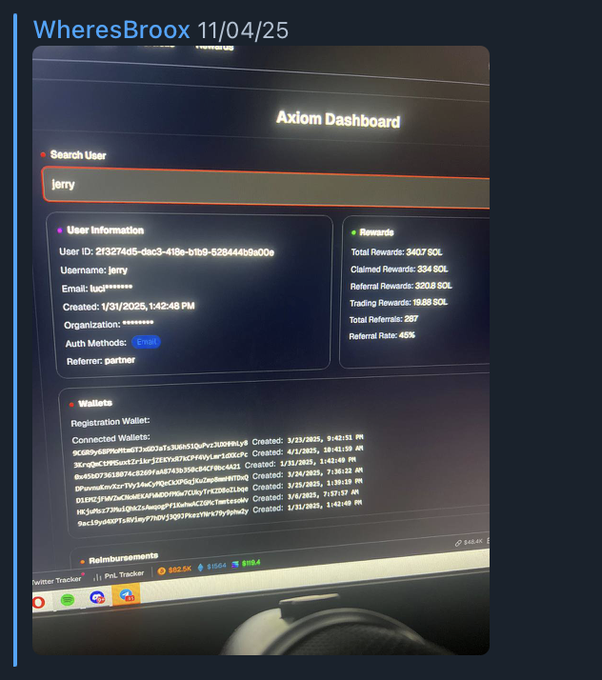
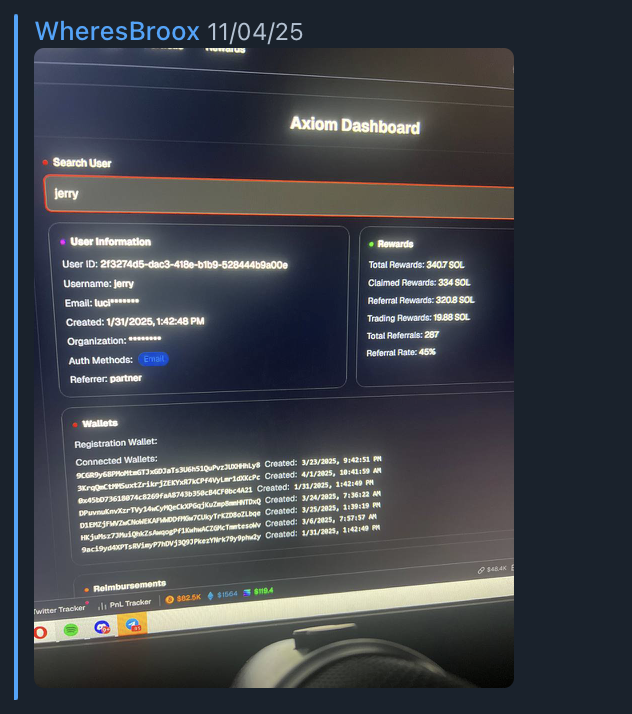
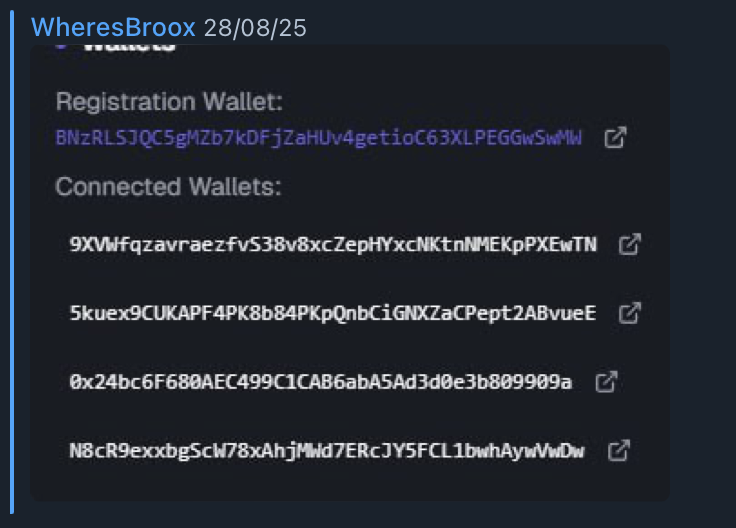
In April 2025, Broox shared a screenshot from Axiom's internal backend showing the private wallet information of trader "Jerry."
In August 2025, Broox sent a second screenshot showing the registration information and associated wallet of trader "Monix."
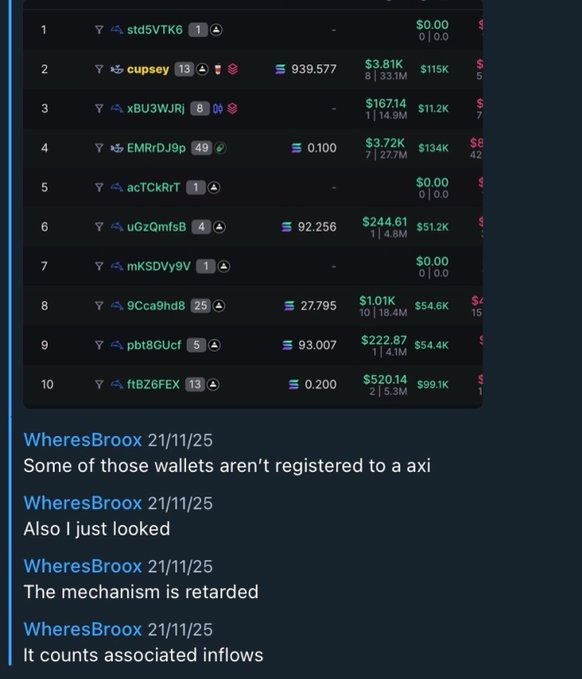
In the same August, Broox discussed querying Axiom users who had traded the meme coin "AURA."
(5)
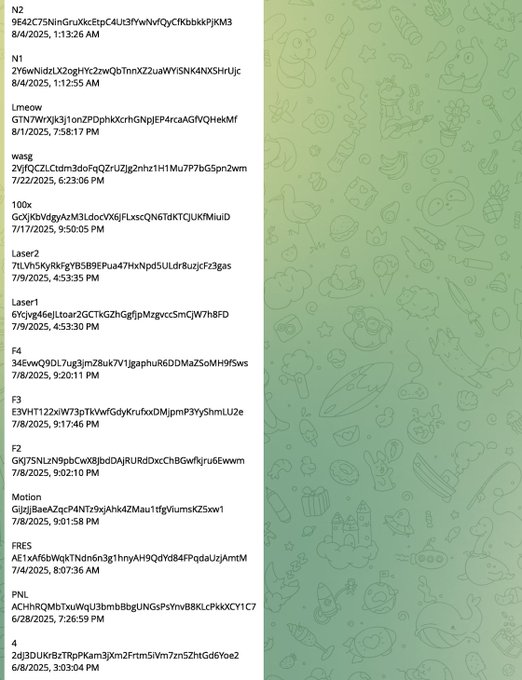
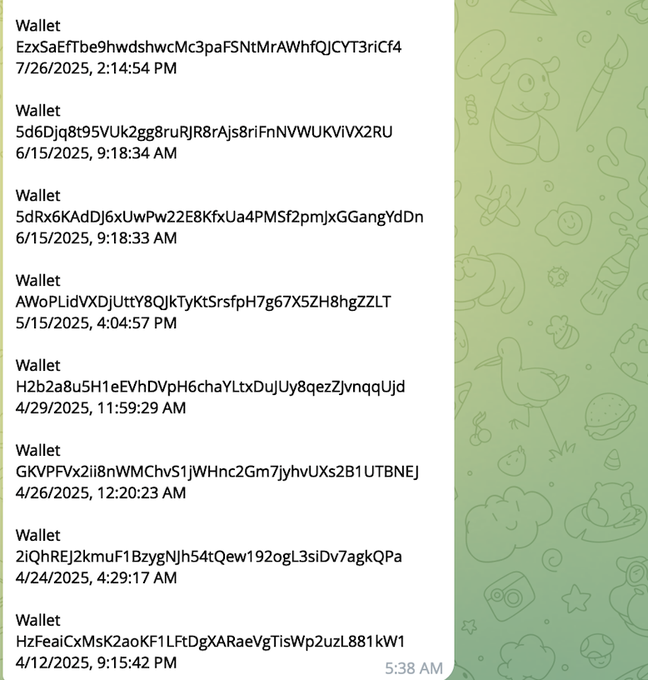
The group established a Google spreadsheet that compiled wallet addresses of multiple KOL targets. These addresses were all organized from data acquired by Broox from Axiom's internal backend.
Several KOLs named in the spreadsheet or appearing in the leaked screenshots have been contacted and independently confirmed the accuracy of the wallet data.
(6)
One of the targeted KOLs is Marcell, a trader infamous for treating his fans on X and Telegram as "exit liquidity."
He became a target because he has a habit of buying large amounts of tokens with his private wallet before promoting meme coins (i.e., "bundled hedging"), then calls out to his fans.
Traders like Marcell are excellent targets for such abuse of power — their address reuse rate is low, and private wallets are rarely disclosed, making the value of internal privileged information extremely high.
(7)
Through private messages, Broox’s main wallet was identified, and all directly associated addresses were mapped out.
FarpaWkzio7WQVpQeu2eURvNQZ3pCBZupJ95wUjoHcUN
Due to the involvement of numerous meme coin transactions, it is difficult to lock in high-confidence insider trading cases solely based on wallet data — unless internal logs from Axiom can be obtained to cross-reference the timing of trade placements.
The funds from the associated addresses primarily flowed to the following centralized exchange deposit addresses:
9HtKkLzTVUGMS9BDMSXbVjooP1rVoeiFPj3tEtmj7Qn4
A8XSEaZXYo8eidAMivoAonf8skBeW1QkfprdBJm6eVz
HPr1MSrSB2i9r9Vcsj8Cmx2sUFGudpDum6kY9dp2ePCN
Afp4DargofX8K67BRUuhVuoBy1DJn9vTbH3ico9CaNs1
6rv1iSZ7YyR18R7EPvXwHdDkNp3qzrE9YPQtPnLVaYbv
(8)
On the call with Broox was also his friend Gowno (Seb), a new moderator recently hired at Axiom.
In the first recorded segment, Broox claimed that Ryan (Ryucio) — another business development employee at Axiom — had used the internal backend to query user information for others and stated that he helped get his friend Mystery into Axiom as a moderator.
In the second recorded segment, Broox discussed how Gowno's responsibilities would expand over time and indicated that he could eventually assist in wallet queries.
Ryan and Mystery did not appear in this recorded call.
(9)
In this recorded call from February 2026, Broox elaborated on a plan: using his permissions at Axiom to help Gowno earn $200,000 quickly. This aligns closely with similar misconduct he has engaged in with others since early 2025.
He also shared a screenshot of his exchange account balance in private chat, indicating that this scheme was already generating actual profits.

(10)
This investigation was commissioned by a client, and I acted as an independent investigator to look into the allegations of improper conduct within Axiom; all of the above constitutes the investigation's findings.
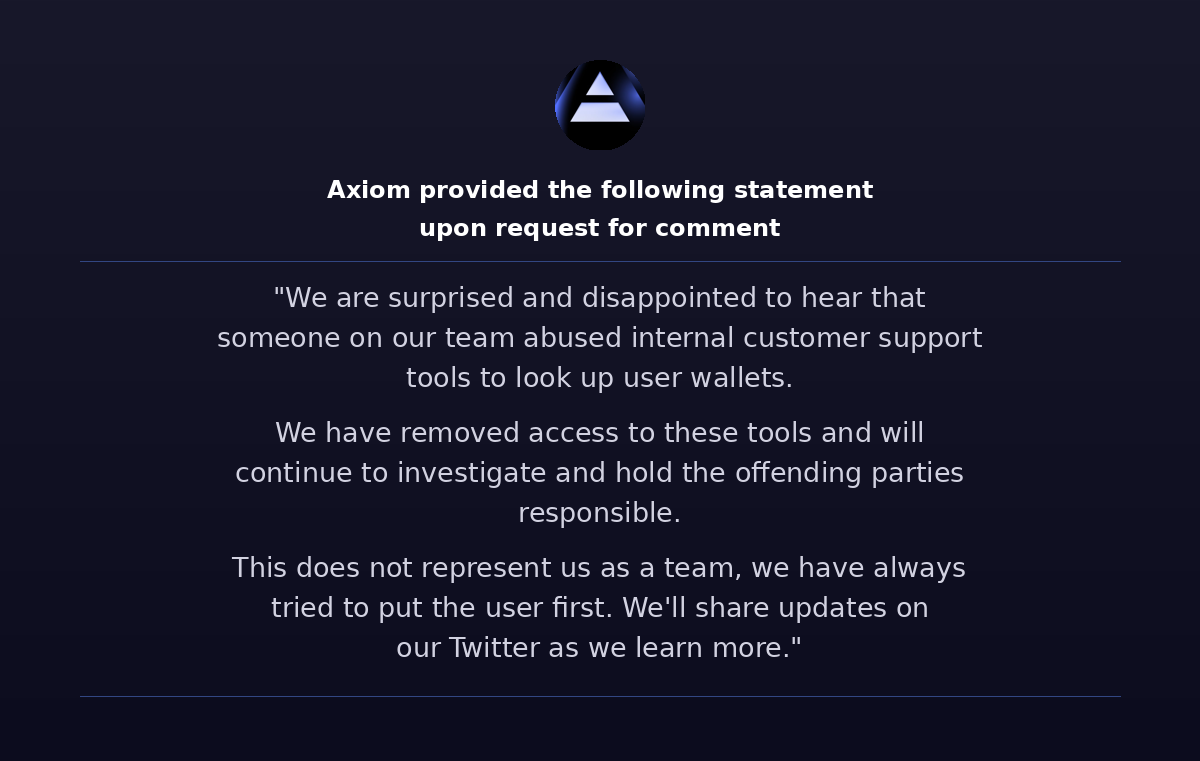
Earlier today, I contacted the Axiom team for comment, and their official statement is attached to the original text.
Whether Cal or Mist were aware, the company has almost never established any monitoring mechanisms or access control to prevent such abuses of power from occurring since the beginning.
The data access granted to employees is quite broad — in an easily accessible backend system, employees can see the complete wallet list of users (including date/time), wallets being tracked by users, transaction history, wallet notes, and associated accounts. Such permissions are indeed rare for business development positions.
Given that Broox is based in New York, I believe this case may present a good opportunity for the Southern District of New York federal prosecutors (SDNY) to intervene, as it may fall within their jurisdiction.
Regardless of whether criminal charges are ultimately filed, I hope that the co-founders of Axiom will further investigate these abuses of power internally and consider taking legal action against the employees involved.
---
⚠️ Editor's Note: This article is a translation of the tweet investigation report, with images serving as investigative evidence screenshots.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。