Introduction | OKX Web3 Wallet has specially planned the "Security Special Issue" section to provide special answers to different types of on-chain security issues. Through the most real cases happening around users, in collaboration with security experts or institutions, different perspectives are used to share and answer questions, in order to systematically summarize and summarize security trading rules from shallow to deep, aiming to strengthen user security education and help users learn to protect private keys and wallet assets from themselves.
Luring operations are as fierce as tigers, with a security coefficient of -5?
As a high-frequency user of on-chain interactions, security is always the top priority for luring users.
Today, the two "pitfall kings" of the chain will teach you how to carry out security protection strategies.
This issue is the 3rd issue of the Security Special Issue, and it specially invites the industry-renowned security expert 0xAA from WTF Academy and the OKX Web3 Wallet security team to explain the common security risks and preventive measures for "luring" users from the perspective of practical guidance.
WTF Academy: Thank you very much for the invitation from OKX Web3. I am 0xAA from WTF Academy. WTF Academy is an open-source Web3 university that helps developers get started with Web3 development. This year, we incubated a Web3 rescue project called RescuETH (on-chain rescue team), which focuses on rescuing the remaining assets in users' stolen wallets and has successfully rescued over 3 million RMB worth of stolen assets on Ethereum, Solana, and Cosmos.
OKX Web3 Wallet Security Team: Hello everyone, we are very happy to be able to share this time. The OKX Web3 Wallet security team is mainly responsible for the construction of various security capabilities of OKX in the Web3 field, such as wallet security capability construction, smart contract security audit, on-chain project security monitoring, etc., to provide users with multiple protection services such as product security, fund security, and transaction security, and contribute to maintaining the security ecosystem of the entire blockchain.
Q1: Please share several real risk cases encountered by "luring" users
WTF Academy: Private key leakage is one of the major security risks faced by "luring" users. Essentially, the private key is a string of characters used to control encrypted assets, and anyone with the private key can fully control the corresponding encrypted assets. Once the private key is leaked, attackers can access, transfer, and manage the user's assets without authorization, leading to economic losses for the user. So, I will focus on sharing several cases of private key theft.
Alice (pseudonym) was induced by hackers to download malicious software on social media, which led to the theft of her private key after running the malicious software. Currently, the forms of malicious software are diverse, including but not limited to: mining scripts, games, conference software, "Chongtudou" scripts, and clipper robots, and users need to raise their security awareness.
Bob (pseudonym) accidentally uploaded his private key to GitHub, which was obtained by others, leading to the theft of his assets.
Carl (pseudonym) trusted the fake customer service who actively contacted him in the official Telegram group of the project, and disclosed his mnemonic phrase, which led to the theft of his wallet assets.
OKX Web3 Wallet Security Team: There are quite a few such risk cases, and we have selected several classic cases encountered by users when luring.
The first type is the release of fake airdrops by high imitation accounts. User A found a notice of an airdrop activity below the latest Twitter of a popular project, and then clicked on the notice link to participate in the airdrop, which ultimately led to being phished. Currently, many phishers use high imitation official accounts and post false announcements under official tweets to induce users to take the bait. Users should be vigilant and not take it lightly.
The second type is the hijacking of official accounts. The official Twitter and Discord accounts of a certain project were attacked by hackers, and then the hackers posted a false airdrop activity link on the official account of the project. Since the link was posted from the official channel, user B did not doubt its authenticity and clicked on the link to participate in the airdrop, only to be phished.
The third type is encountering malicious project teams. User C participated in a mining activity of a certain project and, in order to obtain higher reward returns, invested all USDT assets into the staking contract of the project. However, the smart contract was not rigorously audited and not open-source, and as a result, the project team used the backdoor reserved in the contract to steal all the assets deposited by user C.
For luring users, who often have dozens or hundreds of wallets, how to protect wallet and asset security is a very important topic that requires constant vigilance and increased security awareness.
Q2: Common security risk types and protective measures for "luring" users in on-chain interactions as high-frequency users
WTF Academy: For "luring" users and all Web3 users, the two common security risks are phishing attacks and private key leakage.
The first type is phishing attacks: Hackers usually impersonate official websites or applications, lure users to click on social media and search engines, and then induce users to trade or sign on phishing websites to obtain token authorization and steal user assets.
Protective measures: First, it is recommended that users enter official websites and applications only through official channels (such as links in the official Twitter profile). Second, users can use security plugins to automatically block some phishing websites. Third, when entering suspicious websites, users can consult professional security personnel to help determine whether it is a phishing website.
The second type is private key leakage: This has been introduced in the previous question and will not be elaborated here.
Protective measures: First, if a user's computer or mobile phone has a wallet installed, try not to download suspicious software from unofficial channels. Second, users need to know that official customer service will not actively private message you, let alone ask you to send or enter private keys and mnemonic phrases on fake websites. Third, if a user's open-source project needs to use a private key, please configure the .gitignore file first to ensure that the private key is not uploaded to GitHub.
OKX Web3 Wallet Security Team: We have summarized 5 common security risks for users in on-chain interactions and listed some protective measures for each type of risk.
- Airdrop scams
Risk overview: Some users often find a large number of unknown tokens in their wallet addresses, and these tokens usually fail in common DEX transactions, with the page prompting users to exchange them on their official website. When users authorize transactions, they often grant permission to smart contracts to transfer account assets, ultimately leading to asset theft. For example, the Zape airdrop scam, where many users suddenly received a large number of Zape coins in their wallets, seemingly worth tens of thousands of dollars. This made many people mistakenly believe that they had unexpectedly made a fortune. However, this is actually a carefully designed trap. Since these tokens cannot be queried on regular platforms, many users eager to cash out will find the so-called "official website" based on the token name. After connecting the wallet as instructed, they think they can sell these tokens, but once authorized, all the assets in the wallet will be immediately stolen.
Protective measures: Avoiding airdrop scams requires users to remain highly vigilant, verify the source of information, always obtain airdrop information from official channels (such as the project's official website, official social media accounts, and official announcements), protect private keys and mnemonic phrases, do not pay any fees, and use communities and tools to verify and identify potential scams.
- Malicious smart contracts
Risk overview: Many unaudited or unopened smart contracts may contain vulnerabilities or backdoors, and the security of user funds cannot be guaranteed.
Protective measures: Users should only interact with smart contracts that have been rigorously audited by formal audit companies, or pay attention to checking the project's security audit report. In addition, projects with bug bounty programs usually have more security guarantees.
- Authorization management:
Risk overview: Over-authorization to interacting contracts may lead to fund theft. Here we illustrate: 1) The contract is an upgradable contract. If the privileged account's private key is leaked, attackers can use the private key to upgrade the contract to a malicious version, thereby stealing the assets authorized by the user. 2) If the contract has unidentified vulnerabilities, over-authorization may allow attackers to exploit these vulnerabilities to steal funds in the future.
Protective measures: In principle, only authorize the necessary amount to interacting contracts, and regularly check and revoke unnecessary authorizations. When signing off-chain permit authorizations, be clear about the target contract/asset type/authorization amount and think twice before acting.
- Phishing authorization
Risk overview: Clicking on malicious links and being induced to authorize malicious contracts or users.
Protective measures: 1) Avoid blind signing: Before signing any transaction, make sure to understand the content of the transaction to be signed, ensuring that each step of the operation is clear and necessary. 2) Be cautious when authorizing targets: If the authorization target is an Externally Owned Account (EOA) address or an unverified contract, vigilance must be increased. Unverified contracts may contain malicious code. 3) Use anti-phishing plugin wallets: Use plugin wallets with anti-phishing protection, such as OKX Web3 Wallet, which can help identify and block malicious links. 4) Protect mnemonic phrases and private keys: Any website that requests mnemonic phrases or private keys is a phishing link, so do not enter this sensitive information on any website or application.
- Malicious luring scripts
Risk overview: Running malicious luring scripts can result in the installation of trojans on the computer, leading to the theft of private keys.
Protective measures: Be cautious when running unknown luring scripts or luring software.
In conclusion, we hope that users can be extremely cautious and protect their wallets and assets when engaging in on-chain interactions.
Q3: Classic phishing types and techniques, and how to identify and avoid them?
WTF Academy: I would like to answer this question from a different perspective: once users discover that their assets have been stolen, how can they distinguish between a phishing attack and a private key leak? Users can usually distinguish between these two types of attacks based on the following characteristics:
Characteristics of phishing attacks: Hackers usually obtain authorization for a single or multiple assets in a user's single wallet through phishing websites, leading to asset theft. Generally, the types of stolen assets are equal to the number of authorizations granted by the user on the phishing website.
Characteristics of private key/mnemonic phrase leaks: Hackers gain complete control over all assets on a single or multiple chains in the user's wallet. Therefore, if one or more of the following characteristics are present, it is highly likely a private key leak:
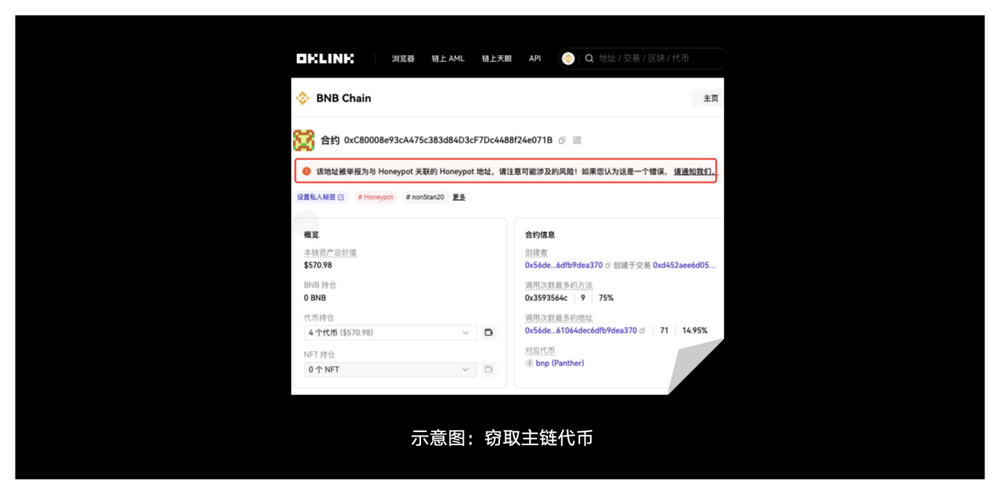
1) Theft of native tokens (e.g., ETH on the Ethereum chain) because native tokens cannot be authorized. 2) Theft of assets on multiple chains. 3) Theft of assets from multiple wallets. 4) Theft of multiple types of assets from a single wallet, and a clear memory of not authorizing these assets. 5) Theft of tokens without prior authorization (Approval event) or in the same transaction. 6) Gas immediately transferred by the hacker.
If the above characteristics are not met, it is likely a phishing attack.
OKX Web3 Wallet Security Team: To avoid phishing, it is important to pay attention to two points: 1) Remember not to enter mnemonic phrases/private keys on any webpage; 2) Ensure that the visited link is an official link and be cautious when clicking the confirmation button on the wallet interface.
Next, we will share some classic phishing scenarios to help users better understand.
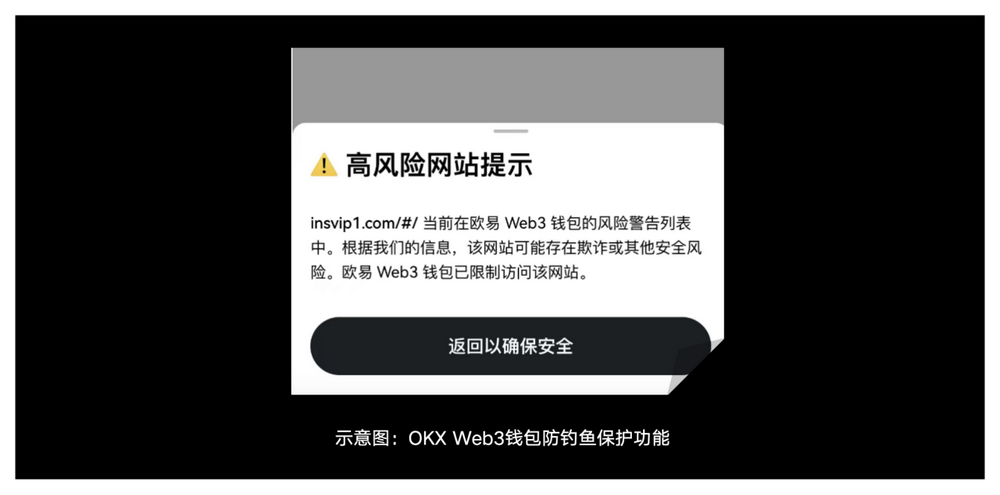
Fake website phishing: Impersonating official DApp websites to induce users to enter private keys or mnemonic phrases. Therefore, the user's primary principle is not to provide wallet private keys or mnemonic phrases to anyone or any website. Additionally, check if the URL is correct and try to use official bookmarks to access commonly used DApps and use mainstream wallets from reputable sources, such as OKX Web3 Wallet, which will issue warnings for detected phishing websites.
Theft of native chain tokens: Malicious contract functions named Claim, SecurityUpdate, AirDrop, etc., with misleading names, have empty actual function logic and only transfer the user's native chain tokens.
Similar address transfers: Scammers generate addresses with the same first and last digits as the user's associated address through address collision, use transferFrom for zero-value transfers to contaminate the user's transaction history, or use fake USDT for transfers of certain amounts to corrupt the user's transaction history, hoping that the user will copy the wrong address for subsequent transfers.
Impersonation of customer service: Hackers impersonate customer service and contact users through social media or email, requesting private keys or mnemonic phrases. Official customer service will not request private keys, so users should ignore such requests.
Q4: Security precautions for high-frequency luring users when using various tools
WTF Academy: Due to the wide variety of tools used by luring users, it is important to strengthen security precautions when using these tools, such as:
Wallet security: Ensure that private keys or mnemonic phrases are not leaked, do not store private keys in insecure locations, and avoid entering private keys in unknown or untrusted websites. Users should back up private keys or mnemonic phrases in a secure location, such as offline storage devices or encrypted cloud storage. Additionally, for wallets holding high-value assets, using multi-signature wallets can enhance security.
Phishing attack prevention: When visiting any related website, carefully verify the URL and avoid clicking on links from unknown sources. Try to obtain download links and information from the project's official website or official social media to avoid using third-party sources.
Software security: Users should ensure that their devices have antivirus software installed and updated to prevent malware and virus attacks. Additionally, they should regularly update wallets and other blockchain-related tools to ensure the use of the latest security patches. Due to previous security vulnerabilities in fingerprint browsers and remote desktops, it is not recommended to use them.
By implementing these measures, users can further reduce security risks when using various tools.
OKX Web3 Wallet Security Team: Let's start with a publicly known industry case.
For example, the BitFingerprint browser provided features such as multi-account login, prevention of window correlation, and simulation of independent computer information, which was favored by some users. However, a series of security incidents in August 2023 exposed its potential risks. Specifically, the "plugin data synchronization" feature of the BitFingerprint browser allows users to upload plugin data to a cloud server and quickly migrate to a new device by entering a password. While this feature was designed for user convenience, it also poses security risks. Hackers gained access to user wallet data by infiltrating the server. Through brute force methods, hackers cracked the user's wallet password from the data, gaining wallet access. Server records showed that the server storing extension cache was illegally downloaded in early August (log records as late as August 2). This incident reminds us to be vigilant about potential security risks while enjoying convenience.
Therefore, it is crucial for users to ensure that the tools they use are secure and reliable to avoid the risks of hacker attacks and data leaks. Generally, users can enhance security from the following perspectives:
Use of hardware wallets: 1) Regularly update firmware through official channels. 2) Use on secure computers and avoid connecting in public places.
Use of browser plugins: 1) Be cautious when using third-party plugins and tools, and choose reputable products whenever possible, such as OKX Web3 Wallet. 2) Avoid using wallet plugins on untrusted websites.
Use of transaction analysis tools: 1) Use trusted platforms for transactions and contract interactions. 2) Carefully check contract addresses and method calls to avoid errors.
Use of computer devices: 1) Regularly update computer system and software, patch security vulnerabilities. 2) Use security antivirus software and regularly scan computer systems for viruses.
Q5: How can luring users manage multiple wallets and accounts more securely compared to a single wallet?
WTF Academy: Since luring users engage in high-frequency on-chain interactions and manage multiple wallets and accounts simultaneously, it is important to pay special attention to asset security.
Use of hardware wallets: Hardware wallets allow users to manage multiple wallet accounts on the same device, with each account's private key stored in the hardware device, which provides relatively greater security.
Separation of security strategies & operational environments: Firstly, separate security strategies by using different wallets for different purposes to diversify risks. For example, separate wallets for airdrops, trading, and storage purposes. For instance, use a hot wallet for daily transactions and luring operations, and a cold wallet for long-term storage of important assets, so that if one wallet is compromised, the others will not be affected.
Secondly, separate operational environments by using different devices (e.g., mobile phones, tablets, computers) to manage different wallets to prevent security issues on one device from affecting all wallets.
- Password management: Users should set strong passwords for each wallet account, avoid using the same or similar passwords, or use a password manager to manage passwords for different accounts to ensure that each password is independent and secure.
OKX Web3 Wallet Security Team: For luring users, it is not easy to manage multiple wallets and accounts more securely. For example, you can improve wallet security from the following dimensions:
Risk Diversification: 1) Do not keep all assets in one wallet, diversify storage to reduce risk. Choose different types of wallets, such as hardware wallets, software wallets, cold wallets, and hot wallets, based on asset types and purposes. 2) Use multi-signature wallets to manage large assets and enhance security.
Backup and Recovery: 1) Regularly back up mnemonic phrases and private keys and store them in multiple secure locations. 2) Use hardware wallets for cold storage to prevent private key leaks.
Avoid Reusing Passwords: Set strong passwords for each wallet and account separately to avoid using the same passwords, reducing the risk of one account being compromised and threatening others.
Enable Two-Factor Authentication (2FA): Where possible, enable 2FA for all accounts to enhance account security.
Automation Tools: Reduce the use of automation tools, especially those that may store your information in the cloud or on third-party servers, to minimize the risk of data leaks.
Limit Access Permissions: Only authorize trusted individuals to access your wallet and accounts, and limit their operational permissions.
Regularly Check Wallet Security Status: Use tools to monitor wallet transactions and ensure that no abnormal transactions occur. If a wallet's private key leak is detected, immediately replace all wallets, and so on.
In addition to the above dimensions, there are many more. In any case, users should ensure wallet and asset security through multiple dimensions and not rely solely on a single dimension.
Q6: What protective measures can be taken against transaction slippage and MEV attacks relevant to luring users?
WTF Academy: Understanding and preventing transaction slippage and MEV attacks is crucial, as these risks directly impact transaction costs and asset security.
For MEV attacks, common types include: 1) Front-running, where miners or trading bots preemptively execute the same transaction as the user to profit. 2) Sandwich attacks, where miners insert buy and sell orders before and after the user's transaction to profit from price fluctuations. 3) Arbitrage: exploiting price differences across different markets on the blockchain.
Users can use MEV protection tools to submit transactions through dedicated channels to miners, avoiding public broadcasting on the blockchain. Alternatively, they can reduce the public exposure time of transactions, minimize the time transactions stay in the mempool, use higher gas fees to expedite transaction confirmation, and avoid large transactions concentrated on a single DEX platform to reduce the risk of being attacked.
OKX Web3 Wallet Security Team: Transaction slippage refers to the difference between the expected transaction price and the actual execution price, usually occurring when the market is highly volatile or has low liquidity. MEV attacks refer to attackers exploiting information asymmetry and transaction privileges to gain excess profits. Here are some common protective measures for these scenarios:
Set Slippage Tolerance: Due to the inherent delay in on-chain transactions and the potential for MEV attacks, users need to set reasonable slippage tolerance in advance to avoid transaction failures or fund losses due to market fluctuations or MEV attacks.
Batch Transactions: Avoid large transactions at once and split them into smaller batches to reduce their impact on market prices and lower slippage risk.
Use High-Liquidity Trading Pairs: When trading, choose trading pairs with sufficient liquidity to minimize slippage.
Use Anti-Front-Running Tools: Avoid using the mempool for important transactions and use professional anti-front-running tools to protect transactions from being captured by MEV bots.
Q7: Can users use monitoring tools or professional methods to regularly monitor and detect abnormal wallet account activities?
WTF Academy: Users can use a variety of monitoring tools and professional methods to regularly monitor and detect abnormal wallet account activities. These methods help improve account security, prevent unauthorized access, and mitigate potential fraudulent activities. Here are some effective monitoring and detection methods:
1) Third-Party Monitoring Services: Many platforms can provide users with detailed reports of wallet activities and real-time alerts.
2) Use of Security Plugins: Some security tools can automatically block certain phishing websites.
3) Wallet Built-in Features: Wallets like OKX Web3 can automatically detect and identify certain phishing websites and suspicious contracts, providing warnings to users.
OKX Web3 Wallet Security Team: Many companies or organizations currently provide a wide range of tools for monitoring and detecting wallet addresses. We have compiled some based on publicly available information, such as:
Blockchain Monitoring Tools: Use blockchain analysis tools to monitor abnormal transactions and fund changes for wallet addresses, set up address transaction notifications, and more.
Secure Wallets: Use professional wallets like OKX Web3 Wallet to support transaction pre-execution and timely detection of suspicious transactions. It can also promptly detect and prevent interactions with malicious websites and contracts.
Alert Systems: Set conditions to receive alerts for transaction or balance changes, including SMS, email, or app notifications.
OKLink Token Authorization Query: Check wallet authorizations for DApps and revoke unnecessary authorizations to prevent misuse by malicious contracts.
Q8: How to protect on-chain privacy and security?
WTF Academy: While the public and transparent nature of blockchain brings many benefits, it also means that users' transaction activities and asset information may be misused, making on-chain privacy protection increasingly important. However, users can protect their personal identity privacy by creating and using multiple addresses. It is not recommended to use fingerprint browsers due to the many security vulnerabilities that have occurred.
OKX Web3 Wallet Security Team: More and more users are paying attention to privacy and security protection. Common methods include:
Multiple Wallet Management: Diversify user assets to reduce the risk of tracking or attacks on a single wallet.
Use of Multi-Signature Wallets: Transactions require multiple signatures for execution, increasing security and privacy protection.
Cold Wallets: Store long-term assets in hardware wallets or offline storage to prevent online attacks.
Avoid Publicizing Addresses: Refrain from sharing wallet addresses on social media or public platforms to avoid being tracked by others.
Use of Temporary Email Addresses: Use temporary email addresses to protect personal information from exposure when participating in airdrops or other activities.
Q9: How should users respond if their wallet account is stolen? Have efforts been made to help stolen users recover their assets and protect user assets?
WTF Academy: We have separate responses for phishing attacks and private key/mnemonic phrase leaks.
First, in the event of a phishing attack, the assets authorized to the hacker will be transferred to the hacker's wallet, and this part is almost irretrievable. However, the remaining assets in the user's wallet are relatively safe. The RescuETH team recommends that users take the following measures:
1) Revoke the authorization of assets given to the hacker.
2) Contact a security company to track the stolen assets and hacker addresses.
Second, in the event of a private key/mnemonic phrase leak, all valuable assets in the user's wallet will be transferred to the hacker's wallet, and this part is almost irretrievable. However, the assets in the user's wallet that cannot be transferred away can be rescued, such as unlocked staking assets and unreceived airdrops, which are our main rescue targets. The RescuETH team recommends that users take the following measures:
1) Immediately check if there are assets in the wallet that the hacker has not transferred, and if so, transfer them to a secure wallet. Sometimes hackers overlook assets on less popular chains.
2) If the wallet contains unlocked staking assets and unreceived airdrops, users can contact professional teams for rescue.
3) If there is suspicion of installing malicious software, promptly scan the computer for viruses and remove the malicious software. If necessary, consider reinstalling the operating system.
Currently, we have made many attempts to rescue stolen user assets.
First, we are the first team to conduct large-scale rescue of stolen wallet assets. In the airdrop event on Arbitrum in March 2023, I collected over 40 leaked wallet private keys from nearly 20 fans and raced against the hacker for the $ARB airdrop. Ultimately, we successfully rescued over $40,000 worth of ARB tokens, with an 80% success rate.
Second, when a user's wallet is stolen, assets with economic value will be transferred by the hacker, while NFTs or ENS with sentimental value to the user will remain in the wallet. However, due to the wallet being monitored by the hacker, the incoming gas will be immediately transferred out, and the user cannot transfer this portion of the assets. To address this, we have developed a self-rescue application: the RescuETH App. It is based on Flashbots bundle MEV technology and can bundle the incoming gas and outgoing NFT/ENS transactions to prevent the hacker from transferring out the gas, thus successfully rescuing the assets. The RescuETH App is currently in internal testing and is expected to start public testing in June.
Third, for the portion of assets in the user's stolen wallet that can be rescued (unlocked staking and unreceived airdrops), we offer paid customizable white-hat rescue services. Currently, our white-hat team, consisting of nearly 20 security/MEV experts, has rescued over 3 million RMB worth of assets from stolen wallets on chains such as ETH, Solana, and Cosmos.
OKX Web3 Wallet Security Team: We approach this from two perspectives: user measures and the security mechanisms of OKX Web3 Wallet.
I. User Measures
Once a user discovers that their wallet has been stolen, it is recommended to take the following urgent measures:
Emergency Response Measures
1) Immediately transfer funds: If there are still funds in the wallet, they should be immediately transferred to a secure new address.
2) Revoke authorizations: Immediately revoke all authorizations through management tools to prevent further losses.
3) Track fund flow: Timely track the flow of stolen funds and compile detailed information about the theft process to seek external assistance.
Community and Project Support
1) Seek help from projects and communities: Report the incident to projects and communities, as sometimes projects can freeze or recover stolen assets. For example, USDC has a blacklist mechanism that can block fund transfers.
2) Join blockchain security organizations: Join relevant blockchain security organizations or groups to collectively address the issue.
3) Contact wallet customer support: Promptly contact the wallet's customer support team for professional assistance and guidance.
II. OKX Web3 Wallet Security Mechanisms
OKX Web3 Wallet places high importance on the security of user assets and continuously invests in protecting user assets, providing multiple security mechanisms to ensure the security of users' digital assets.
Blacklisted Address Library: OKX Web3 Wallet has established a rich library of blacklisted addresses to prevent users from interacting with known malicious addresses. This library is continuously updated to address evolving security threats and ensure the security of user assets.

Security Plugins: OKX Web3 Wallet provides built-in anti-phishing protection to help users identify and block potential malicious links and transaction requests, enhancing the security of user accounts.
24/7 Online Support: OKX Web3 Wallet provides 24/7 online support for customers to promptly address cases of stolen or deceived assets, ensuring that users can quickly receive assistance and guidance.
User Education: OKX Web3 Wallet regularly publishes security tips and educational materials to help users raise their security awareness, understand how to prevent common security risks, and protect their assets.
Q10: Can you share some cutting-edge security technologies, such as whether AI can be used to enhance security protection?
WTF Academy: Security in the blockchain and Web3 domains is a continuously evolving field, with various cutting-edge security technologies and methods constantly emerging. Currently, some popular ones include:
1) Smart Contract Auditing: Automated security audits of smart contracts using AI and machine learning to detect vulnerabilities and potential risks, providing faster and more comprehensive analysis than traditional manual audits.
2) Anomaly Detection: Using machine learning algorithms to analyze on-chain transactions and behavior patterns to detect abnormal activities and potential security threats. AI can identify common attack patterns (such as MEV attacks and phishing attacks) and abnormal transaction behavior, providing real-time alerts.
3) Fraud Detection: AI can analyze transaction history and user behavior to identify and flag potential fraudulent activities.
OKX Web3 Wallet Security Team: AI has already been widely applied in the Web3 domain, and here are some scenarios where AI is used to enhance Web3 security protection:
First, anomaly detection and intrusion detection: Using AI and machine learning models to analyze user behavior patterns and detect abnormal activities. For example, deep learning models can be used to analyze transaction behavior and wallet activity to identify potential malicious behavior or abnormal activities.
Second, phishing website identification: AI can analyze webpage content and link features to detect and block phishing websites, protecting users from the threat of phishing attacks.
Third, malicious software detection: AI can detect new and unknown malicious software by analyzing file behavior and features, preventing users from downloading and executing malicious programs.
Fourth, automated threat response: AI can automate response measures, such as automatically freezing accounts or taking other protective actions upon detecting abnormal activities.
Finally, thank you for reading the 3rd issue of the OKX Web3 Wallet "Security Special Issue". We are currently preparing the content for the 4th issue, which will include real cases, risk identification, and practical security operations. Stay tuned!
Disclaimer:
This article is for reference only and does not intend to provide (i) investment advice or recommendations; (ii) solicitations or offers to buy, sell, or hold digital assets; or (iii) financial, accounting, legal, or tax advice. Holding digital assets (including stablecoins and NFTs) involves high risks and may experience significant volatility, even becoming worthless. You should carefully consider whether trading or holding digital assets is suitable for you based on your financial situation. You are responsible for understanding and complying with applicable local laws and regulations on your own.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




