The U.S. military experiments with Bitcoin nodes: the Softwar theory moves from MIT to the Pentagon.
Written by: Juan Galt
Translated by: AididiaoJP, Foresight News
From April 21 to 22, 2026, during a Senate Armed Services Committee hearing, Admiral Samuel Paparo, commander of the U.S. Indo-Pacific Command, commented on the role of Bitcoin in national military cybersecurity, describing it as "a valuable force projection computer science tool," and revealed that the Indo-Pacific Command is operating Bitcoin nodes for protocol experiments.
This statement from the commander of the Indo-Pacific Command came a few days after the Islamic Republic of Iran requested payment for safe passage through the Strait of Hormuz in Bitcoin. The term "force projection" brings to mind the work of the well-known and controversial Bitcoin advocate Jason Lowery — "Softwar: A New Theory of Force Projection," who is a researcher at MIT and a special assistant to the commander of the Indo-Pacific Command.
In his works (including the MIT paper and its expanded book version), Lowery explored Bitcoin's cybersecurity value and its unique "force projection" capability in cyberspace — an area of national security and military operations that traditionally lacks effective deterrent measures.
The book garnered significant attention among Bitcoin enthusiasts, earning Lowery both fans and criticism, but he later removed the book at the request of his superiors. This incident led some to believe that the book may contain important content that the U.S. military wishes to keep low profile.
But what unique value does Bitcoin really bring to the military domain? In this context, what does "force projection" actually mean?
According to the U.S. Department of Defense’s 2002 Dictionary of Military and Associated Terms, the definition of force projection is: "The ability of a nation to rapidly and effectively deploy and sustain military forces from multiple dispersed locations to respond to crises, enhance deterrence, and promote regional stability using all or some elements of national power — political, economic, informational, or military." In other words, it is the ability of a nation to influence other nations or political entities beyond its borders. Forms of expression can include diplomacy, economic influence, and military capabilities such as long-range missiles, drones, or a powerful navy.
The term "deterrence" also plays an important role here. The Department of Defense defines it as: "The act of preventing action by a fear of consequences. Deterrence is a psychological state induced by the presence of credible and unacceptable counterforces."
Lowery introduces Bitcoin into the realm of physical deterrence with a particularly interesting insight. He points out that just as microchips essentially move electricity via "encoded logic" on a computer motherboard, the global power grid can be viewed as a type of "macro chip" — giant wires transmitting substantial electricity from power sources to countries and around the world. These macro chips now also have logic gates — Bitcoin mining farms. Lowery argues that they consume vast amounts of energy, converting it into scarce digital assets which can be programmed via Bitcoin scripts.
Bitcoin macro chips theoretically bind cybersecurity with the physical world, as energy output is one of the most important and expensive resources a nation can mobilize. Governments can print money at will, but mobilizing substantial electricity to influence Bitcoin’s proof-of-work competition is several orders of magnitude more challenging, which is the foundation of Bitcoin’s resilience.
Bitcoin's Multi-Signature Deterrence
The most evident and powerful manifestation of Bitcoin's "embedded logic" security is the invention of multi-signature wallets, which today protect most of Bitcoin's wealth.
Multi-signature wallets require multiple predefined private keys to jointly sign transactions for them to be valid, allowing Bitcoin private keys to be geographically dispersed across different locations and jurisdictions.
Multi-signature not only requires hackers to break one key pair, but they must also break multiple key pairs located in different spots within a time limit, as legitimate users have direct access to these keys and may swiftly transfer Bitcoin in the face of threats. Hackers must obtain enough keys without triggering alarms and defensive measures or getting caught. Multi-signatures significantly raise the cost for attackers, making them very much in line with the definition of "deterrence." It may even align with the definition of "force projection" — enabled by Bitcoin's network-based censorship resistance, Bitcoin funds can be safely stored and sent anywhere globally when needed.
This differs from traditional finance and its centralized databases, as banks can freeze or seize assets from legitimate owners when faced with political pressure, as seen with the "bailout" of 40% of deposits in Cyprus or the U.S. seizing Russian foreign reserves held in Europe.
However, the Indo-Pacific Command did not explicitly discuss Bitcoin as an asset in their comments; they seemed to believe that Bitcoin's proof-of-work protocol could protect data and networks beyond Bitcoin assets. However, Bitcoin scripts (the logic within the Bitcoin blockchain) only govern the internal asset BTC.
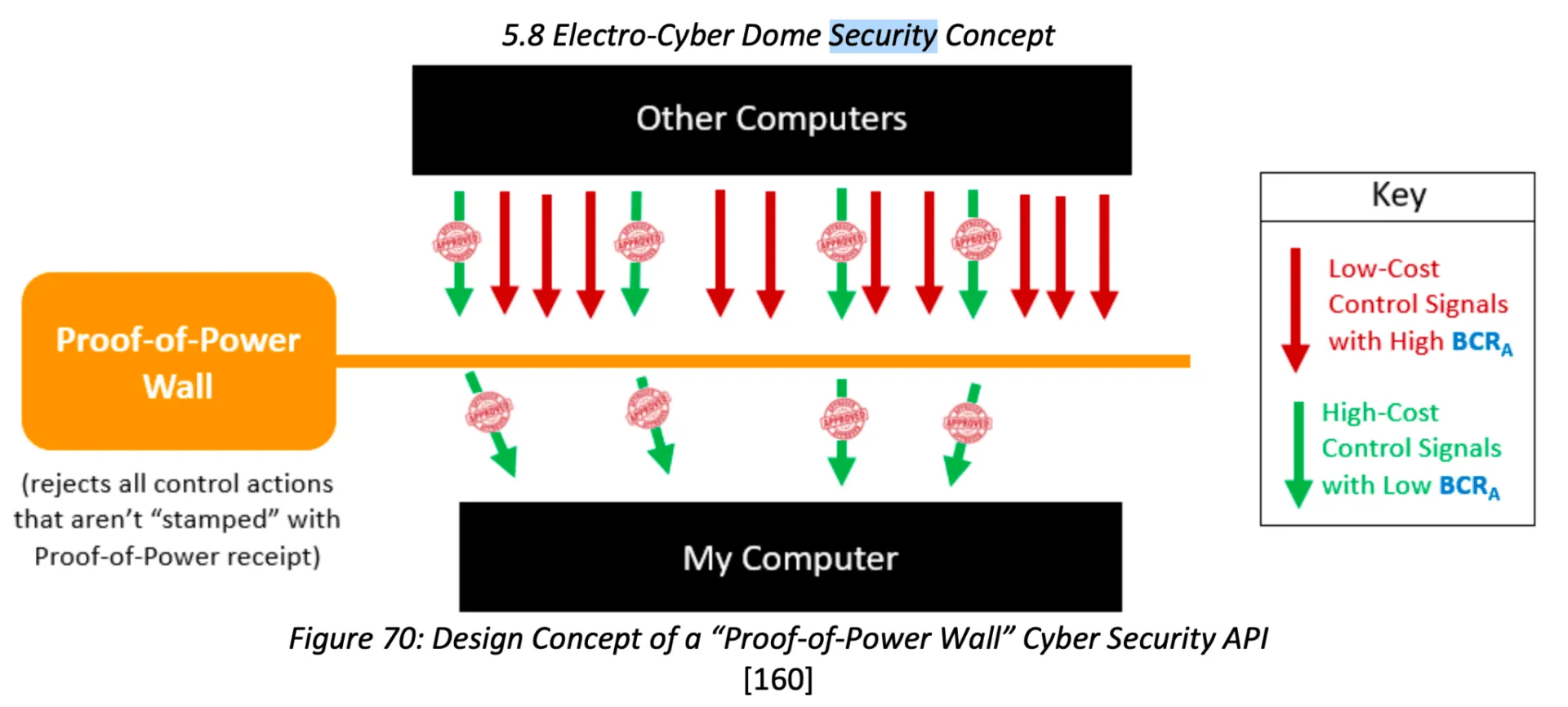
For external networks to benefit from the formidable proof-of-work macro chips of Bitcoin, they must somehow anchor to Bitcoin, which is the point where Lowery's argument starts to falter. However, he did further develop this idea, proposing the concept of the "Electro-Cyber Dome."
Cybersecurity Threats and the Electro-Cyber Dome
In "Softwar 2.5," Lowery argues that "security vulnerabilities in software systems stem from a lack of sufficient constraints on the control signals sent to networked machines." For example, false login attempts can cause websites to consume far more computational resources to verify them than the attacker sends. Lowery adds that such vulnerabilities "can be exploited to put the software into an insecure or dangerous state." Such cybersecurity attacks include but are not limited to:
- Email spam and comment spam — flooding inboxes or forums with useless emails and comments;
- Sybil attacks — creating large numbers of false identities to manipulate systems;
- Bot and troll farms — automated or collaborative accounts used to amplify malicious activities;
- Weaponized misinformation campaigns — drowning networks in false or manipulated information;
- Distributed denial of service (DDoS) attacks — flooding network bandwidth with excessive control signals (service requests);
- Forged or replayed control signals — impersonating legitimate commands, instructions, or data to make software enter insecure/dangerous states;
- Systemic exploitation of administrative privileges/internal abuse — leveraging trust-based hierarchies to breach or abuse high-privilege accounts.
Lowery believes that other networks could largely use similar proof-of-work (PoW) protocols to defend against these threats.
In the Bitcoin white paper, Satoshi Nakamoto elegantly defined Bitcoin's PoW: "Proof of work is to find a value that, when hashed (for example, using SHA-256), the hash begins with a certain number of zero bits. The average work required increases exponentially with the number of leading zero bits required, and it can be verified by performing a single hash."
Nakamoto specifically mentioned Adam Back's "Hash Cash: A Denial of Service Countermeasure," which makes spamming expensive by requiring the sending computer to generate a PoW stamp of difficulty defined by the recipient. The recipient's server needs to maintain a list of used stamps to prevent attackers from reusing the same work, thus preventing double-spending attacks. However, these stamps are non-transferable, while some cypherpunks sought to have them transferable in pursuit of digital currency. Hal Finney was one of the engineers advancing this field, who invented RPOW, reusable proof of work.
RPOW essentially tokenizes the PoW stamps through a centralized server that tracks and facilitates the transfer. One of Nakamoto's key innovations was decentralizing this server and its list of spent stamps into a blockchain form while defining a global difficulty algorithm that all Bitcoin miners must satisfy, rather than each site choosing its relative difficulty target.
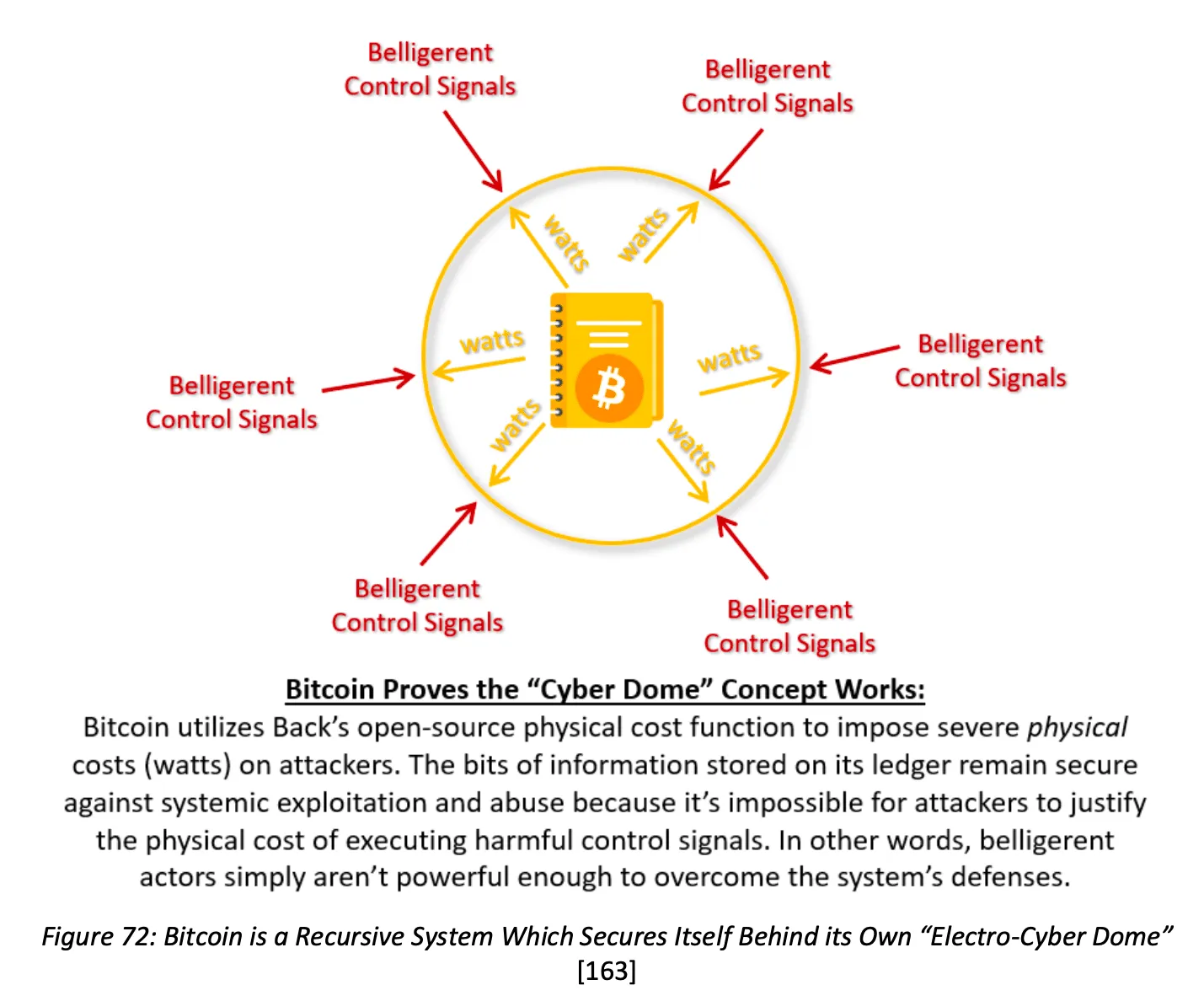
In the concept of the "Electro-Cyber Dome," Lowery is essentially discussing Hash Cash. He states explicitly that servers can select their own difficulty targets as they see fit and never suggested that the dome should use Bitcoin's SHA-256 protocol, even though his macro chip idea hints at it. What he did was present Bitcoin as the primary example of how this cybersecurity network could effectively operate on a large scale: "We know exactly that the Electro-Cyber Dome can successfully function as a security protocol because that is how Bitcoin protects itself and its information from systemic exploitation."
Lowery does not only discuss defenses; he also points out that as such systems are widely adopted, large miners may carry out attack behaviors. He writes, "It is important to note that this will not be a strictly 'defensive' force projection capability... Those with computational power could theoretically 'break through' these Electro-Cyber Dome defenses if they choose to. Thus, the power protocol is not only a 'defensive' protocol as some might suggest. The greatest threat to those who use physical cost-function protocols (like Bitcoin) is other users of the same protocol (which is why Nakamoto mentions the term 'attack' 25 times in the 8-page white paper, each time referring to those running the same protocol)."
Criticism of Lowery's Softwar Theory
Lowery's Softwar theory can fairly be described as controversial within the Bitcoin community. It optimistically believes that most military conflicts in the future can be resolved through computational power warfare, a viewpoint labeled as "delusional" by Shinobi of Bitcoin Magazine.
Overall, critics refuse to accept that the Bitcoin tech stack (whether PoW, blockchain, or native asset) can protect data or networks beyond Bitcoin in any way. Jameson Lopp has provided multi-part critiques of Lowery’s theories and books, praising many aspects of the theories but ultimately denying their conclusions, stating: "Softwar fails to provide an adequate blueprint for how we should build the future."
To me, the most obvious question is whether using SHA-256 proof of work to guard against network access beyond Bitcoin makes sense or could even be regarded as using Bitcoin. If the Electro-Cyber Dome does not require sufficiently high proof of work difficulty to mine any Bitcoin, and if it does not use Bitcoin's target difficulty, asset, or blockchain, does it count as using Bitcoin?
Moreover, given that China possesses most of the manufacturing capacity for Bitcoin mining ASIC chips, does the U.S. Indo-Pacific Command (the U.S. military branch responsible for maintaining stability in the Indo-Pacific region) really wish to protect its networks with an algorithm that can be brute-forced by chips produced on a massive scale in China? This seems at least an awkward decision, more likely prompting them to consider alternative PoW algorithms. But if that were the case, they certainly would not be using Bitcoin and would lose the macro chip argument. It would just be classic Hash Cash; perhaps this is the real lesson of the story. Lowery's affinity for Bitcoin might be more of a marketing strategy and tribute to the industry that inspired him rather than a tool the Indo-Pacific Command would ultimately use.
Middle Ground
In the blank space between theory, implementation, and criticism of Softwar-like ideas, there are some young but interesting projects that showcase how Bitcoin can protect more than just money.
SimpleProof is a Bitcoin notarization system based on OpenTimestamps, which has been used to record the hashes of data on the blockchain, proving that a particular version existed at a certain time. This narrow use of Bitcoin as a timestamp server helped one side of the Guatemalan elections fend off opposition fraud claims a few years ago and had real political consequences for the country.
On the other hand, Michael Saylor spearheaded the creation of a Bitcoin-native decentralized digital identity system known as the "Orange Check Protocol." The tech stack can be found on GitHub and generated some interest in the Bitcoin community when announced a few years ago, but it seems it has not been adopted.
Lastly, ironically, Jameson Lopp — one of Lowery's most outspoken critics, who has written three articles specifically critiquing him — actually implemented a proof-of-work-based spam protection mechanism on his website's submission form. According to Lopp, this mechanism works well. So even he can see the utility of these old ideas (even if only based on Hash Cash), there is hope we might someday see similar Bitcoin-like technologies used to protect networks and data around the world.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




