Written by: Tiger Researcher
Translated by: AididiaoJP, Foresight News
Key Points
- By April 2026, Web3 hacker attacks have occurred successively, with 12 incidents reported just in April.
- The proportion of social engineering attacks is increasing year by year, accounting for 74.7% of total hacker losses in the first quarter of 2026. It's easier to attack people than code.
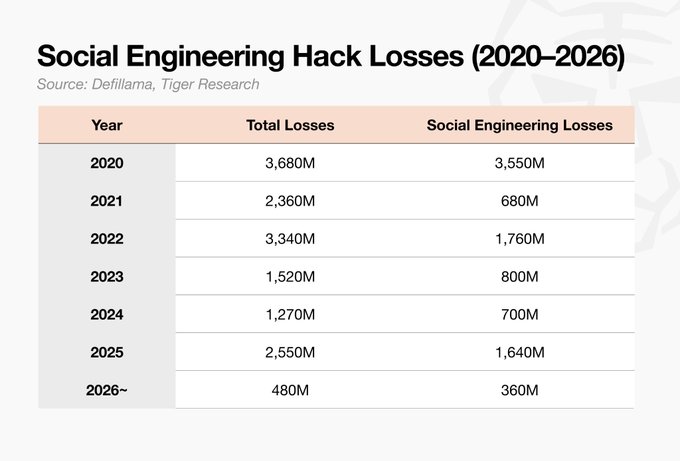
- Since 2020, the average recovery rate of stolen funds has remained below 10%. Unlike traditional finance, Web3 cannot prevent direct on-chain theft; funds are drained the moment the attack occurs.
- After Bybit suffered a $1.5 billion hacking attack, it was still able to continue operations without causing losses to investors, thanks to inter-exchange coordination and reserve funds. In contrast, DeFi projects have no such buffer time once assets leave the protocol.
- Repeated hacker attacks and a recovery rate of less than 10% are key obstacles preventing institutional investors from entering the market. Web3 needs not ideas but structured and accountable operational mechanisms.
Hacker Attacks Continue to Occur
@hyperbridge (a cross-chain bridge protocol connecting Polkadot and Ethereum) was attacked.
The attacker exploited a vulnerability in the proof validation logic to forge cross-chain messages, resulting in the unauthorized minting of about 1 billion bridged DOT on Ethereum. It has been confirmed that user losses across Ethereum, Arbitrum, Base, and BNB Chain totaled $2.5 million.

Before the Polkadot cross-chain bridge was attacked, DeFi protocol @DriftProtocol suffered a severe attack of $295.7 million. A hacker group linked to North Korea took six months to build trust with team members before seizing governance control, marking a highly sophisticated social engineering operation. Tether then proposed a $127.5 million support plan, but the total assistance amount of $147.5 million was still far from covering the total $295.7 million loss.
Subsequent hacker attacks did not stop. Along with the minor attacks after the Drift incident, there were 12 incidents just in April. In this industry based on programmable finance, security vulnerabilities continue to accumulate, leaving both investors and institutions increasingly uneasy.
Hacker Attacks Target People
The attack on Drift Protocol stemmed from a team member's computer being compromised. The target of the attack was not a vulnerability in the smart contract or system defect, but a person.
The larger issue is that the proportion of social engineering attacks in Web3 hacker incidents is continually increasing.
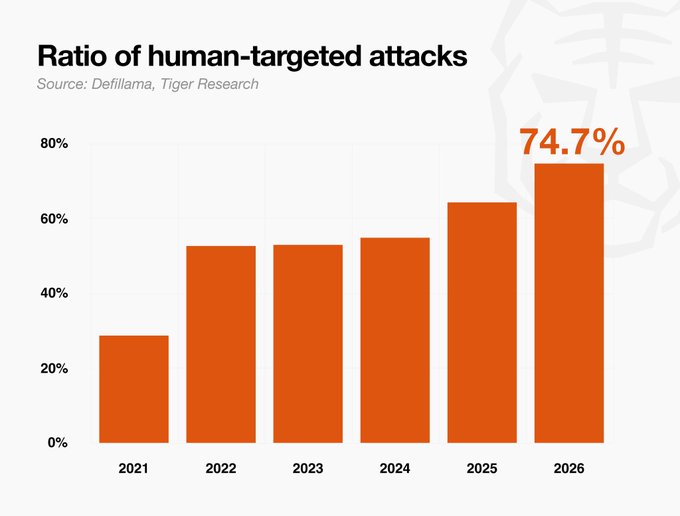
In 2021, social engineering attacks accounted for 28.7% of total hacker losses, rising to 64.3% in 2025, further reaching 74.7% in the first quarter of 2026. Attacks targeting people are continuously expanding, while the exploitation of code-level vulnerabilities is relatively declining.
Given the open-source nature of blockchain, it was initially thought that code vulnerabilities would dominate. However, in reality, social engineering has become the more significant attack vector. The reason is simple: breaking into a person with existing permissions is much easier than finding a vulnerability in code.
Traditional industries exhibit the same pattern. By 2025, 70% of corporate hacking incidents involved social engineering, and this method of attack has been directly transplanted into the Web3 realm.
However, a key difference between Web3 and traditional finance exists: in traditional finance, successful attacks rarely lead to complete theft of funds; account freezes, transaction reversals, and institutional interventions can play roles. In Web3, protocol funds can be directly drained on-chain, and once a transaction is confirmed, it cannot be reversed.
This is precisely why Web3 has become an enticing target.
Recovery Rates Continue to Decline; Losses Are Irreversible
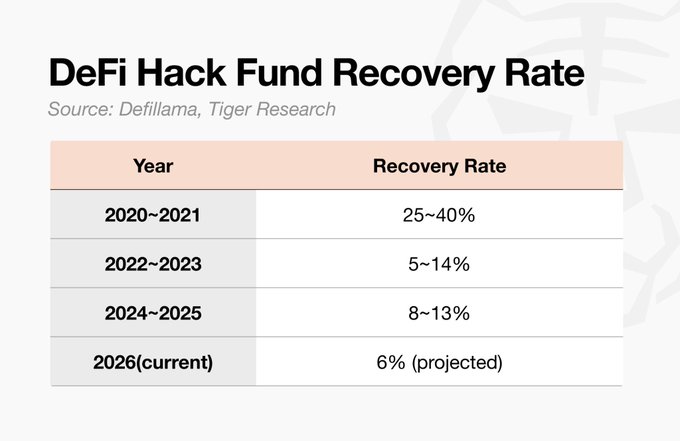
DeFi protocol hacker attacks cause billions of dollars in losses each year, but the actual percentage of recovered stolen funds continues to decline. As state-sponsored attackers like the North Korean Lazarus Group emerge, along with increasingly complex money laundering through mixers and cross-chain bridges, recovering funds has become increasingly difficult.
If stolen funds can be recovered, it can at least maintain a minimum safety standard, but the recovery rate in DeFi has always remained at an extremely low level.
Since 2020, the annual average recovery rate has consistently been below 10%. The only exception was in 2021 when Poly Network was hacked for $611 million, an incident in which the attacker voluntarily returned the full amount, greatly boosting that year’s data. Excluding that incident, the recovery rates have remained low every year.
Survivors Are Players with Coping Abilities
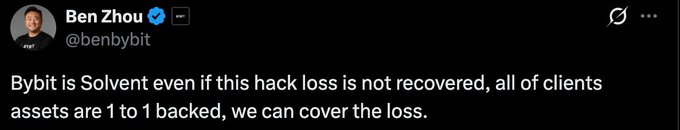
Not all Web3 projects collapse after suffering hacker attacks. Unlike DeFi projects that usually crash after one attack, some players have successfully weathered the storm.
In 2025, Bybit survived after suffering a $1.5 billion hacking attack. Coordination between exchanges and reserve funds sufficient to cover losses played a key role. While not all stolen funds have been recovered, the exchange was able to continue operations without causing losses to investors, which is the main point. Exchanges typically have independent SAFU funds to deal with hacking attacks and other emergencies.
DeFi projects have no such buffer space. Once a transaction is completed, protocol assets disappear with no room for maneuvering. The most realistic path to recovery is to negotiate with the attacker, but attackers have little willingness to negotiate. For state-sponsored groups like Lazarus, negotiation is completely impossible.
Traditional finance would introduce institutional power after an attack occurs, with account freezes, investigations, insurance, and legal claims unfolding sequentially. In Web3, there is no authoritative body capable of reversing confirmed transactions. Projects may occasionally request chain-level intervention to freeze assets, but freezing does not equate to returning.
The core limitation still exists: in Web3, once a mistake is made, it cannot be undone.
How to Convince Institutions in the Institutional Era
We are in an institutional era. Whether accepted or not, institutions are leading the market direction, and this trend is irreversible.
If hacker attacks continue to happen and projects keep collapsing, Web3 will have nothing to offer to institutions. Institutions already have a high interest in blockchain and DeFi. Operational efficiency in asset management, new yield structures, and 24/7 markets are all very attractive features.
But if projects continue to be hacked and trend towards collapse, even the most enticing improvements in efficiency and yield structures will lose significance. No matter how significant the technological advantage is, the underlying assets must be secure. A recovery rate of less than 10% remains one of the biggest reasons institutional investors choose to wait and see.
Once institutional capital truly enters, the market scale will far exceed the current level. It will not be technological superiority that opens this door, but a trustworthy response framework. Whether the industry can successfully convince institutions while defending decentralization will determine whether Web3 can move to the next stage.
What Web3 needs now is not philosophy, but a structure designed for failure and an operational mechanism built on accountability.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




