Written by: Chainalysis
Compiled by: AididiaoJP, Foresight News
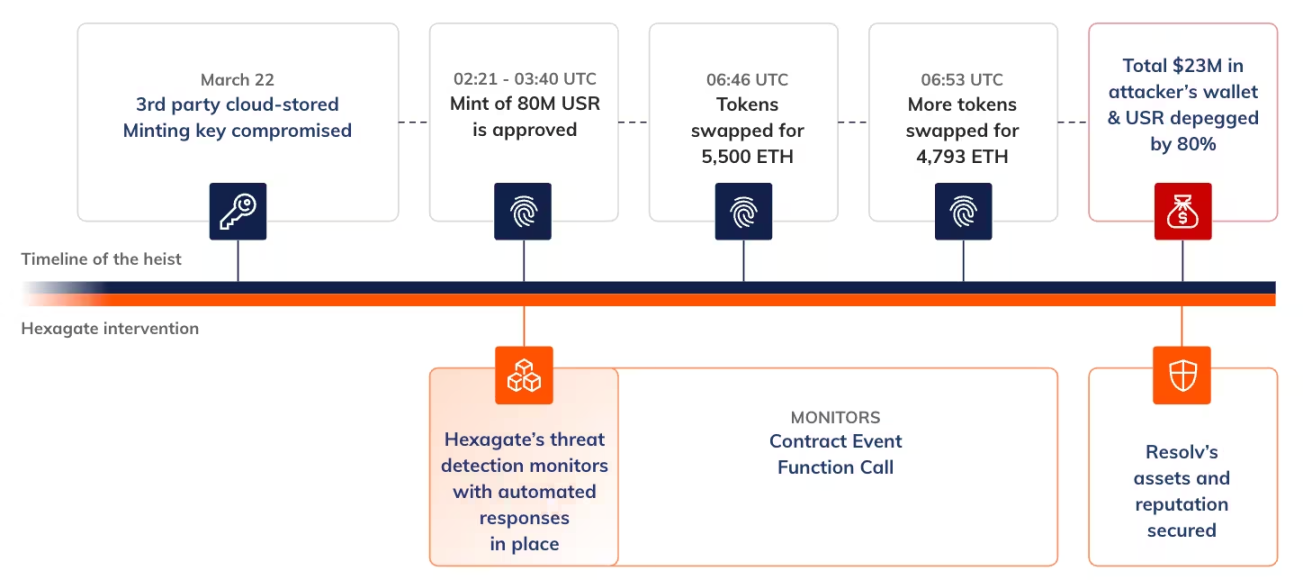
On March 22, 2026, the Resolv DeFi protocol became the latest example of how quickly the DeFi space can plunge into crisis when security assumptions fail. In just a few minutes, an attacker minted tens of millions of uncollateralized Resolv stablecoins USR and extracted approximately $25 million in value, causing the USR price to decouple sharply and forcing the protocol to cease operations.
At first glance, this seems to be another incident of a smart contract vulnerability. However, that is not the case. The way the relevant code operated was entirely consistent with its design.
In fact, this was an incident triggered by excessive trust in off-chain infrastructure. As DeFi systems become increasingly complex and increasingly reliant on external services, privileged keys, and cloud infrastructure, their attack surface has far exceeded the scope of the blockchain itself.
This article will outline the events and their impact and further explore: when off-chain components are compromised, only on-chain threat detection and response mechanisms with real-time capabilities can serve as a crucial last line of defense, making a fundamental distinction between controllable events and vulnerabilities that lead to millions of dollars in losses.
Event Overview
The attacker first deposited a small amount of funds (about $100,000 to $200,000 in USDC) and interacted with Resolv's USR stablecoin minting system. Under normal circumstances, users deposit USDC and receive an equivalent amount of USR. However, in this incident, the attacker successfully minted approximately 80 million USR tokens, far exceeding the reasonable limit corresponding to their deposit.
This situation occurred because the minting approval process relied on an off-chain service that used a privileged private key to authorize the minting quantity of USR. However, the relevant smart contract did not set any upper limit on the minting quantity—it only verified the validity of the signature.
After minting the uncollateralized USR, the attacker quickly converted it to the staked version wstUSR and then gradually exchanged it for other stablecoins before finally extracting it as ETH. By the end of the attack, the attacker had profited approximately $25 million worth of ETH. The sudden influx of uncollateralized USR into the market caused its price to drop by about 80%.
Once the results of the event were clear, the following analysis will further explore how the design flaws in the minting mechanism provided the conditions for this attack.
Normal Minting Process for Resolv Tokens
To understand the cause of this attack, it is necessary to first clarify the design of Resolv's minting mechanism.
When users wish to mint Resolv's native token USR, their interaction does not involve a fully autonomous on-chain mechanism but requires passing through an off-chain process with two steps:
requestSwap — Users deposit USDC into the USR Counter contract and initiate a minting request.
completeSwap — An off-chain service controlled by a privileged private key named SERVICE_ROLE audits the request and calls back to determine the final USR minting quantity.
The contract only specifies a minimum output quantity for USR but does not set any upper limit. There is no check on the ratio between the collateral deposit quantity and the USR minting quantity on-chain, nor does it integrate limitation mechanisms such as price oracles, total quantity limits, or maximum minting ratios. In other words, any quantity signed by this key can be executed for minting.
Detailed Attack Steps
Step 1: Gain Access to Resolv's AWS KMS Environment
The attacker gained access to the AWS Key Management Service environment used by Resolv by infiltrating its cloud infrastructure, where the protocol's privileged signing keys were stored. After gaining control of the KMS environment, the attacker could use Resolv's own minting key to authorize any minting actions needed.
Step 2: Mint USR Tokens
After acquiring the signing key, the attacker initiated two swap requests, each backed by a small amount of USDC deposits, totaling about $100,000 to $200,000 spread across multiple transactions. The attacker then called the completeSwap function using the SERVICE_ROLE key and filled in inflated output amounts, thereby authorizing the minting of tens of millions of USR with only a small amount of USDC invested.
Two main transactions have been identified on-chain:
- 50 million USR minting transaction
- 30 million USR minting transaction
These transactions collectively minted 80 million USR tokens, worth approximately $25 million.
Step 3: Bypass Liquidity Constraints through wstUSR
The attacker then converted USR to wstUSR. wstUSR is a derivative token representing a share of the staking pool, and its value does not maintain a fixed ratio with USR. By converting funds to wstUSR, the attacker avoided directly impacting the USR market and instead shifted their position to a relatively lower liquidity but more substitutable asset form.
Step 4: Cash Out
With wstUSR in hand, the attacker further exchanged it for stablecoins and then converted it to ETH, utilizing multiple decentralized exchange liquidity pools and cross-chain bridges for fund transfers, maximizing withdrawal amounts and increasing the difficulty of tracking the funds.
As of the writing of this article, the attacker’s address still holds:
- About 11,400 ETH (worth approximately $24 million)
- About 20 million wstUSR (valued at about $1.3 million based on decoupled prices)
Impact on USR Holders
This incident caused a direct and serious impact on USR holders.
The newly minted 80 million uncollateralized USR tokens continued to enter the liquidity pools of decentralized exchanges. With the surge in supply, the anchored price of USR against the US dollar collapsed rapidly. The token briefly dropped to $0.20, a decline of 80%, before recovering to about $0.56 within hours.
After the incident, Resolv Labs issued a statement suspending all functions of the protocol to prevent further losses and began investigating the breach. Given that the attacker was still attempting to mint more USR, the urgency to take timely action to prevent further losses is clear, highlighting the extreme importance of responding quickly to such attacks.
A Sound Security Philosophy Should Be Based on the "Assumption of Vulnerabilities Arising"
Although Resolv had implemented all conventional security measures and completed up to 18 security audits, this hacker attack, from one perspective, is essentially a straightforward story: the attacker obtained the key, used it to illegally mint assets, and liquidated the illicit assets before the relevant parties noticed.
However, at a deeper level, this incident reveals how DeFi protocols inherit the security assumptions and potential risks embedded in the off-chain infrastructure they rely on. On-chain smart contracts operated exactly as designed, while the overall system design and the compromised off-chain infrastructure failed to meet the corresponding security standards.
In an environment where various exploit incidents can often be completed in minutes, and passive responses are difficult to implement once the losses become evident, real-time monitoring and automated response mechanisms are no longer optional supplements but essential safeguards.
Hexagate Preventive Case Analysis
The hack that Resolv experienced fully illustrates the scenarios for which real-time on-chain monitoring mechanisms are designed to detect. If Chainalysis Hexagate had been used, the following two specific detection methods could have been effective:
Option 1: Monitoring for Anomalous Minting Events
By configuring monitoring systems like Hexagate, the invocation behavior of the completeSwap function can be monitored to identify serious discrepancies between the quantity of minted USR and the deposited collateral.
A deposit of $100,000 in USDC, yet authorizing the minting of 50 million USR—this anomalous ratio far exceeds any normal user's operating range. Setting alert rules for this function call pattern, such as triggering an alert when the minting ratio exceeds 1.5 times the normal value, would mark the abovementioned two major transactions immediately.
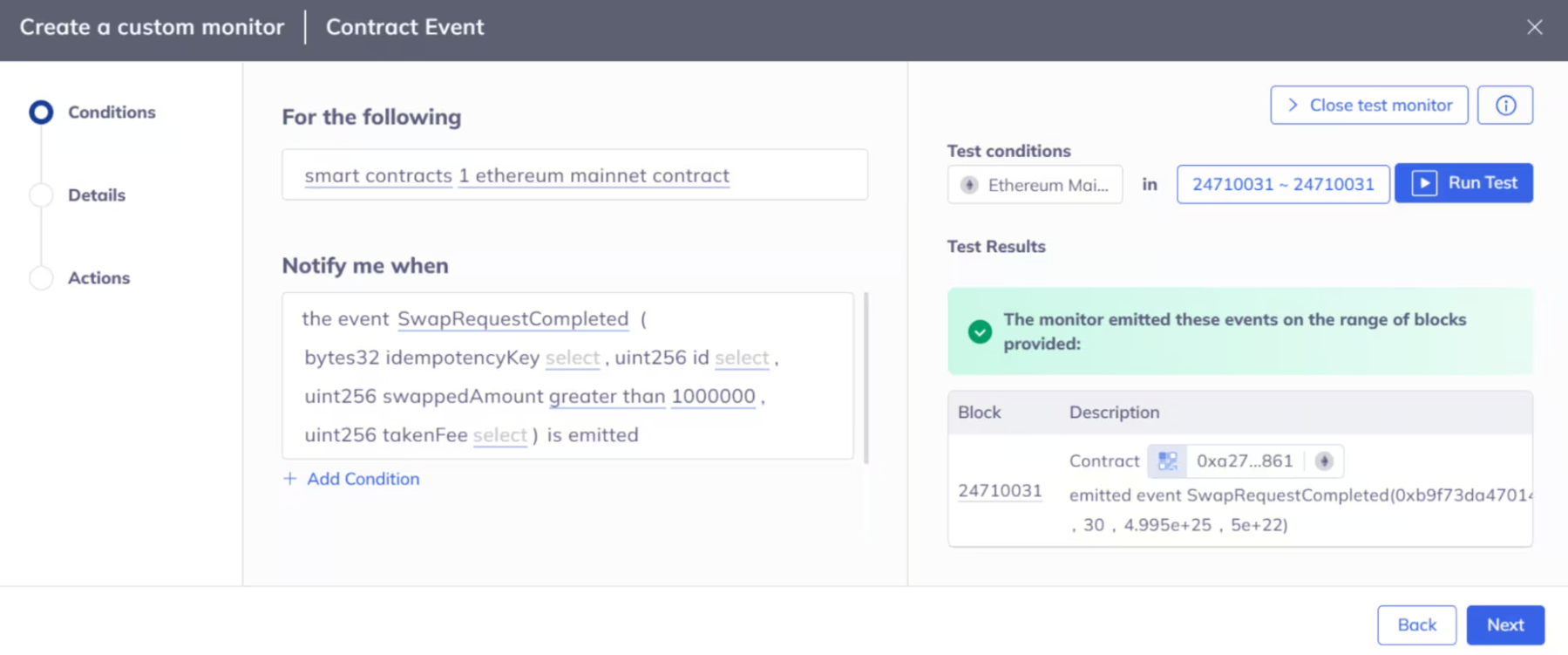
Hexagate's custom monitoring mechanism could have triggered automated responses upon detecting anomalous behaviors utilizing Resolv's minting logic.
Option 2: Combining GateSigner and Custom Functions to Control Key Contract Events
The attacker had to execute the requestSwap and completeSwap processes sequentially, and each phase of this process would generate on-chain events. Combining Hexagate's GateSigner functionality with contract event monitoring could have been configured to automatically trigger a contract pause upon detection of anomalous Mint events, thereby blocking any funds from the 80 million USR from entering the public market.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



