The process has been so convoluted…
Author: International Student Uncle
In 2022, a man named Michael in Spain was troubled by a dilemma.
Back in 2013, he purchased Bitcoin, which was not yet popular, for a total price of $5,300, acquiring 43 coins in total.
He then stored these coins in an electronic wallet and, to prevent theft, generated a long random password of 20 characters using a password software.
Michael was concerned that saving this password with the same software was not secure enough; if it were decrypted by hackers or if his computer were lost, they could easily find the password and access his Bitcoin.
So, he cleverly pasted this long password into a document, disguising its purpose. He also set a password for this document and encrypted it.
After all these layers of encryption, Michael believed he had an unbreakable Bitcoin account password, just waiting for the price of Bitcoin to rise so he could cash out.
Unexpectedly, Michael ultimately fell victim to his own actions—his encrypted document containing the password inexplicably became corrupted and was completely inaccessible, making it impossible to retrieve the long 20-character password.
At the same time, he watched helplessly as the value of Bitcoin soared from $123 per coin to over $30,000 per coin.
"I have this wealth, I can see it, but I can't use it because I don't have the password."
Over the years, Michael sought out various password decryption experts to see if anyone could help him recover the randomly generated password from the software.
But countless cybersecurity experts told Michael: A 20-character random password?! Forget about your Bitcoin; it will never be recovered.
Upon hearing this grim news, Michael once thought he would never be able to access this vast fortune in his lifetime.
Until the year 2022, he learned about an American hacker named Joe Grand online, and then Michael sought Joe's help.
Joe is a world-renowned hardware hacker, as well as an electrical engineer and inventor, with a hacking history dating back to when he was 10 years old.
He is recognized by the mainstream and provides consulting for system developers on how to defend against hackers like him…
Joe also has experience helping two strangers recover lost cryptocurrency passwords.
Once, someone accidentally dropped a USB drive containing the password into a lake, and after divers retrieved it, Joe used a series of physical methods to restore the USB drive's functionality, allowing the person to find the stored password as if the USB drive had never been lost.
On another occasion, there was a password decryption case where a family member had passed away unexpectedly, and before dying, he mentioned that the Bitcoin password might be related to their grandmother's name. Joe helped search based on this clue using a "brute force search," trying millions of permutations one by one…
In 2022, Michael contacted Joe online, but Joe did not agree to help as he had before.
The reason was simple: Joe was a hardware hacker and was not skilled in dealing with software-generated random passwords.
Additionally, helping someone recover a cryptocurrency password was not his specialty or interest, regardless of the price offered.
Thus, Joe flatly rejected Michael's request that year.
However, last summer, when Michael reached out to Joe in despair again, Joe agreed to give it a try.
This time, it wasn't that Joe had softened his heart, but rather that his German partner, a young software hacker, suggested they had a certain chance of recovering Michael's lost password.
This young hacker, named Bruno, is German and specializes in software vulnerabilities. Like Joe, Bruno has shown great interest in finding security vulnerabilities in systems and software since he was a child.
Bruno often receives requests for help from people troubled by lost cryptocurrency passwords, but he had never encountered a case like Michael's before.
He proposed to Joe that they might have a chance to take a gamble, and both genius hackers were incredibly interested in this challenging yet slim opportunity.
Joe flew to Europe to meet with Bruno and Michael.
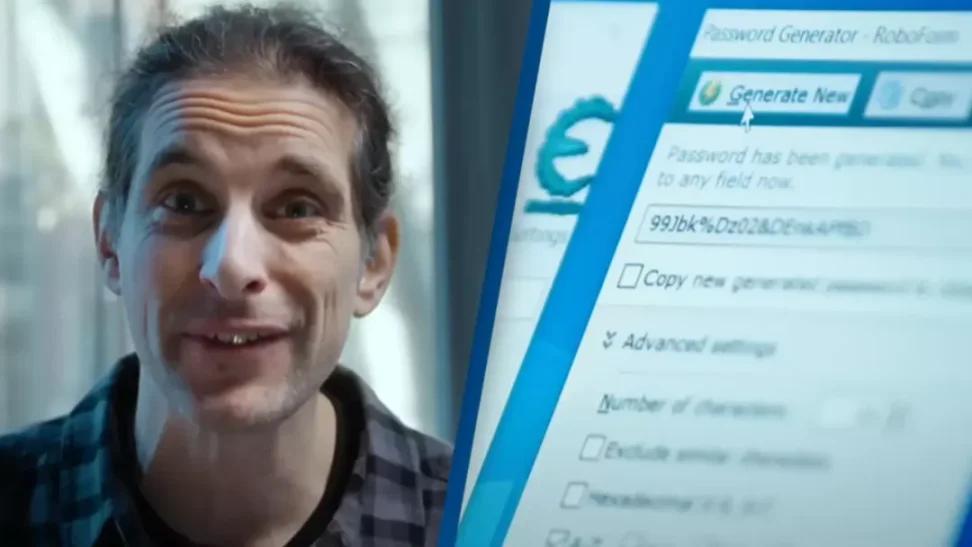
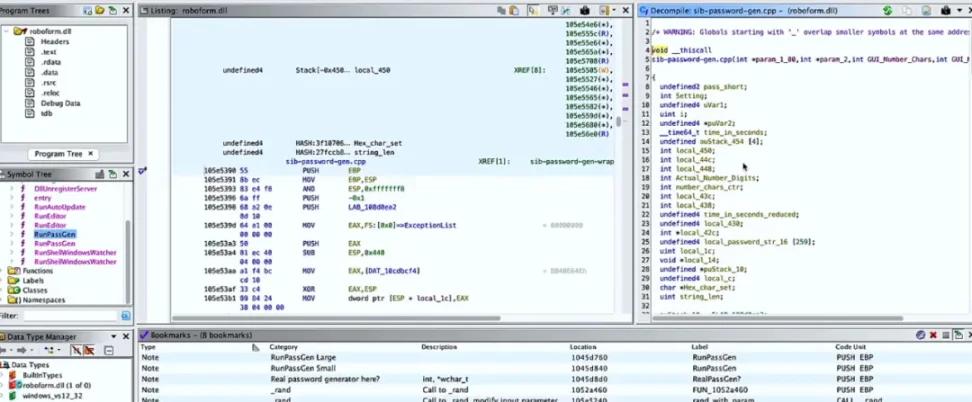
Michael had generated that random password using a software called "RoboForm," one of the earliest random password generators in the world, which is still in use today.
Joe and Bruno tested the software and found that it could generate completely different passwords at any given moment.
For the two of them, finding Joe's random password from back then was like searching for a needle in a haystack:
"If we have to try all possible password combinations, that would be equivalent to a trillion times the number of water droplets in the world.
If we imagine a password as a droplet of water, we would find that it could be flowing at the bottom of a river, it could be falling from the sky, it could be in any ocean anywhere in the world.
If we could somehow reduce this situation, we could turn this insurmountable problem into something we could succeed at."
After understanding how RoboForm works, they began to look for clues along the timeline to narrow down the search range.
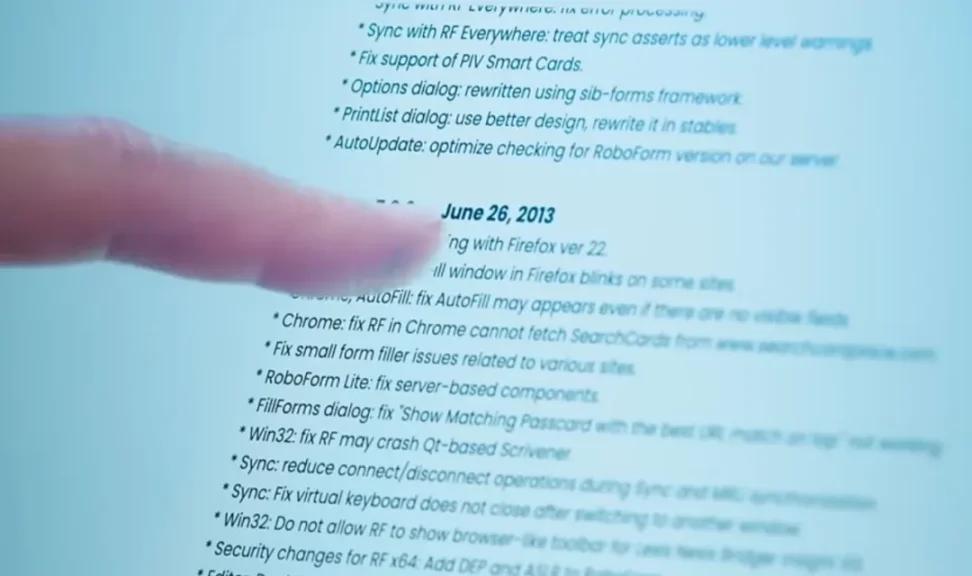
They quickly noticed that in the version release timeline of the software, the update notes for the 2015 version were somewhat suspicious:
"We increased the randomness of password generation."
This statement raised suspicions for both genius hackers: Increased randomness??
Does this imply that the passwords generated by versions prior to 2015 were not as random??
Joe and Bruno, being computer hardware and software geniuses, also knew that, in reality, it is "very, very difficult" for a computer to continuously generate a string of "completely random" numbers; many random numbers are often related to some reference parameters:
"If we could manipulate this 'randomness,' we might be able to obtain a predictable output that could be used to attempt to crack Michael's wallet password."
But now it is 2023, how can we go back to the time when Michael created the password ten years ago and make the software mimic Michael's actions back then?
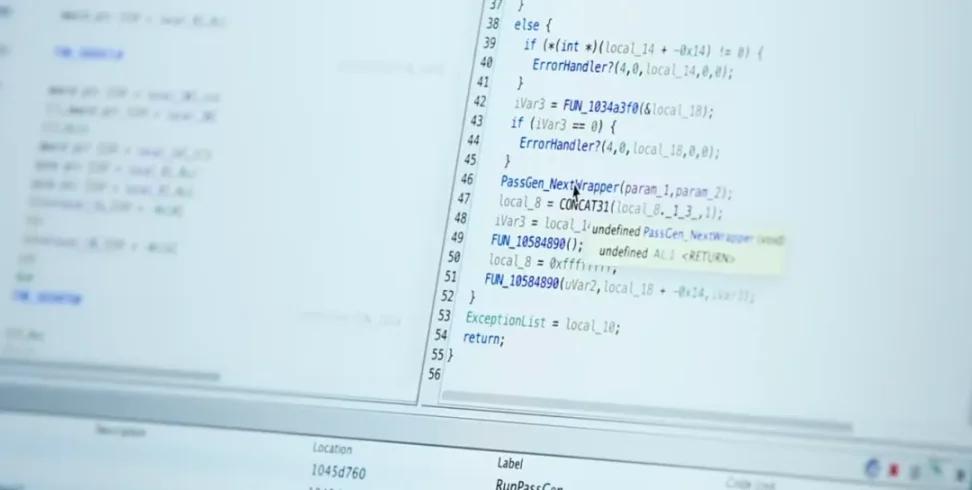
At this moment, the expertise of the two became evident: they reverse-engineered the software, not only reverting it to the 2013 version but also manipulating the system data to make the software believe it was executing a user command from 2013:
"We can deceive the system into thinking it's still within the time window when Michael generated the password in 2013."
Riding the "time machine" back to around ten years ago, the two used a software tool also employed by the NSA to try to understand the patterns of password generation from the past:
"This software is like a Russian nesting doll. Our goal is the little doll in the middle that generates the password."
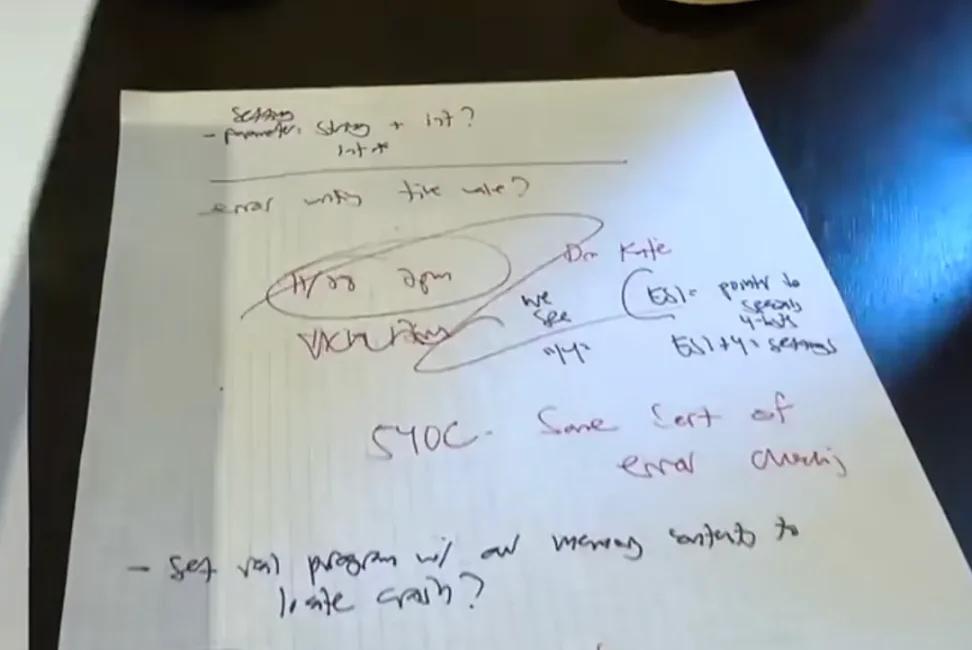
Through calculations and tests, the two were pleasantly surprised to discover that the random password generation from back then indeed had a pattern, and that pattern was the system time!
It turned out that the software in 2013 generated a "pseudo-random password" strictly linked to the time the user created the password, with each password directly associated with the creation time.
With this important clue linking the password to the time Michael created it, both Joe and Bruno were excited.
This meant that their search range could be significantly narrowed; as long as they knew the day and approximate time Michael created the random password, they could calculate a limited number of passwords and try them one by one.
However, Michael couldn't remember exactly which month and day he opened the software to generate the Bitcoin password ten years ago…
Joe and Bruno did not lose heart and patiently continued their investigation.
They found out the time when Michael deposited the Bitcoin into the electronic wallet: April 2013.
Logically, Michael should have created the random password within a few months before this date. Therefore, Joe and Bruno set the search time from March to the end of April of that year.
They discussed and calculated overnight, waiting for the computer to run the results, but the outcome disappointed them: not a single result could unlock Michael's Bitcoin account.
In desperation, the two contacted Michael again, asking him to recall the exact date more carefully.
But Michael was also confused, after all, who could remember such details from ten years ago?
However, this time Bruno asked Michael to send him several other passwords he had created using the same software back then. Joe and Bruno hoped to find some clues from the other passwords created by Michael using the same software.
The two discovered that Michael's other two passwords did not contain any special characters (like ¥…& and similar).
Whether special characters appeared in the random password could be set by the user, and Joe and Bruno, holding onto a glimmer of hope, removed the option for special characters from the search range and extended the search time to June 1, 2013.
Then, in an ordinary early morning, a specific string of characters composed of numbers and letters suddenly popped up on Bruno's computer:
A unique result bounced onto the computer screen!
This result was something even software expert Bruno did not expect; there was actually a unique result!
Ecstatic Bruno
The result showed that Michael clicked to create this password on May 15, 2013, at 4:10:40 PM…
Last November, Joe and Bruno kept this astonishing news from Michael; they customized a huge foam board stating that Michael was awarded $1.6 million and successfully shipped this board to Barcelona by plane.
Then, while Michael was in front of the camera narrating how he lost this enormous fortune, Joe and Bruno suddenly appeared before him, informing him of this good news with a medal!
All three were overjoyed.
After five months of effort, Joe and Bruno truly turned what was previously impossible into a 100% success!
In return, after successfully cracking the password, Joe and Bruno received a specific percentage of Bitcoin from Michael's account (they had agreed with Michael beforehand that they would only collect fees after successfully decrypting the password).
By last November, Michael's Bitcoin had risen from $5,300 ten years ago to $1.6 million.
Joe and Bruno turned the entire story into a short and exquisite documentary, and by May of this year, when the documentary aired, this $1.6 million had risen to $3 million…
At the end of last year, Michael sold some coins, giving some to his benefactors while keeping 30 coins for himself.
He plans to sell the remaining coins when Bitcoin reaches $100,000 per coin.
In the end, Michael not only thanked Joe and Bruno but also reflected on his own "cleverness backfiring":
"If I hadn't lost the password, I might not have waited ten years; I could have sold it long ago."
How to say, if it weren't for the dedicated help of the two genius hackers, combined with the fact that the software happened to have a huge system vulnerability in past versions, Michael's password would have long been lost to the Pacific Ocean.
Hopefully, he can learn a lesson…
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。