Written by: nvk
Translated by: Saoirse, Foresight News
TL;DR
- Bitcoin does not use encryption but rather uses digital signatures. The vast majority of articles have gotten this wrong, and the distinction is crucial.
- Quantum computers cannot crack Bitcoin in 9 minutes. This description only refers to a theoretical circuit, the machine itself does not exist, and it will not appear for at least a decade.
- Quantum mining is physically impossible to achieve. The energy it requires is actually more than the total energy output of the sun.
- Bitcoin can be upgraded—it has successfully upgraded before (SegWit, Taproot), and relevant work has begun (BIP-360). But the community needs to speed up.
- The real reason for upgrading is not the quantum threat but rather that traditional mathematics has already compromised countless encryption systems, and secp256k1 is likely the next. Quantum computers have yet to break any encryption system.
- There is indeed a real risk: approximately 6.26 million Bitcoin public keys have already been exposed. This is not a cause for panic, but it is worth preparing for in advance.
Core Narrative
In one sentence, here is everything I am about to say:
The quantum threat to Bitcoin is real, but it's still far off; media reports are generally exaggerated; and the most dangerous thing is not the quantum computer, but the self-satisfied mindset masquerading as panic or indifference.
Both those shouting "Bitcoin is finished" and those claiming "there's nothing to worry about" are wrong. To see the truth, we need to accept two things simultaneously:
- Bitcoin currently faces no imminent quantum threat, and the actual threat may be far more distant than clickbait headlines suggest.
- But the Bitcoin community should prepare in advance, as the upgrade process itself takes years.
This is not a reason for panic but a reason for action.
Below, I will clarify with data and logic.
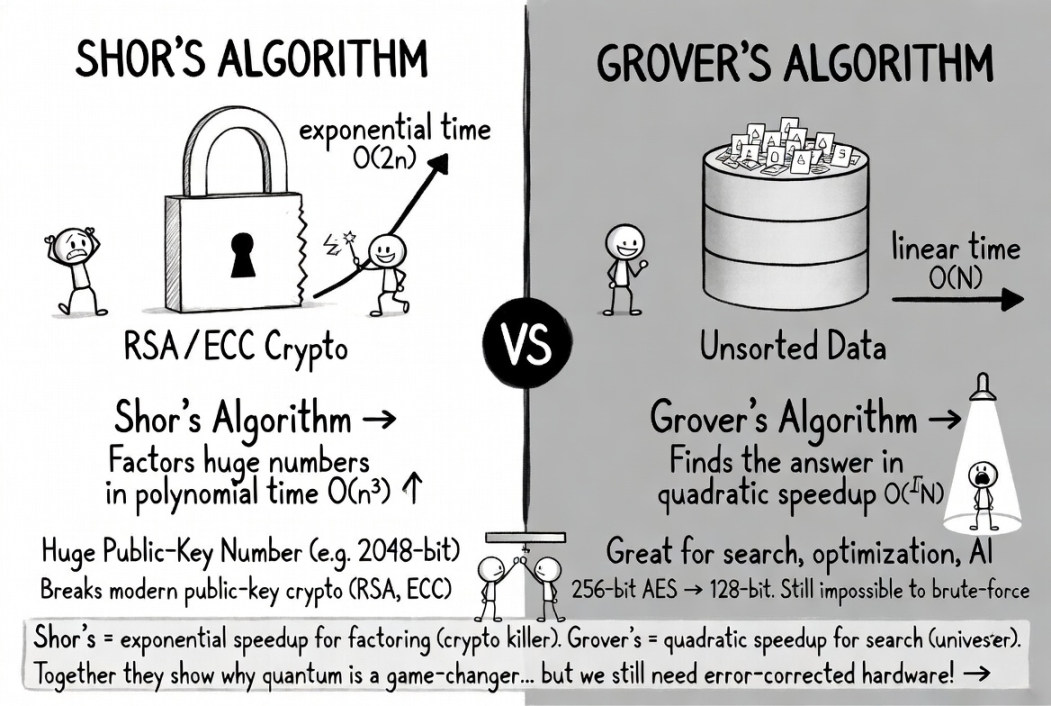
This image compares two major core quantum algorithms: Shor's algorithm (left) is a "crypto-killer" that can exponentially accelerate large number factorization and directly crack RSA/ECC public key cryptography, while Grover's algorithm (right) provides quadratic speedup for unordered searches. Both showcase the disruptive nature of quantum computing, but they are still limited by error correction hardware that cannot be implemented on a large scale.
Media Tactics: Clickbait is the Real Danger
The same script plays out every few months:
- A quantum computing lab publishes a rigorous research paper with many limited conditions.
- Tech media immediately writes: "Quantum computers crack Bitcoin in 9 minutes!"
- Crypto Twitter simplifies it to: "Bitcoin is doomed."
- Your relatives message you asking whether you should sell quickly.
- But the original paper does not say this at all.
In March 2026, Google's quantum AI team published a paper indicating that the number of physical qubits needed to crack Bitcoin's elliptic curve cryptography could be reduced to less than 500,000, which is a 20-fold improvement over earlier estimates. This is indeed important research. Google has been very cautious and has not disclosed a practical attack circuit, only releasing zero-knowledge proofs.
However, the paper never stated that Bitcoin can be cracked now, has a clear timeline, or that everyone should panic.
Yet the headline reads: "Crack Bitcoin in 9 Minutes."
CoinMarketCap once published an article "Will AI-Accelerated Quantum Computing Destroy Bitcoin in 2026?", whose text thoroughly explains that the answer is almost certainly "no." This is a typical tactic: use sensational headlines to draw traffic while maintaining caution and accuracy in the text. But 59% of shared links are never clicked on— for most people, the headline is the information itself.
There is a saying that aptly summarizes: "The market prices risk extremely quickly. You cannot steal something that goes to zero the moment you acquire it." If quantum computing were truly to disrupt everything, Google's own (similarly utilizing the same types of cryptography) stock would have collapsed long ago. But Google's stock has remained stable.
Conclusion: The headline is the real rumor. The research itself is real and worth understanding; let's take a serious look.
What Quantum Computers Really Threaten and What They Do Not
The Biggest Misconception: "Encryption"
Almost all articles discussing quantum and Bitcoin use the term "encryption." This is wrong, and it misleadingly affects the overall understanding.
Bitcoin does not protect assets through encryption but rather through digital signatures (ECDSA, later using Schnorr through Taproot). The blockchain itself is public; all transaction data is always visible to everyone, and there is nothing that needs to be "decrypted."
As said by Adam Back, the inventor of Hashcash quoted in the Bitcoin white paper: "Encryption means data being hidden and can be decrypted. Bitcoin's security model is based on signatures to prove ownership, without exposing the private key."
This is not just a matter of semantics. This means that the most urgent threat in the quantum realm of "collecting data now, decrypting later" does not fundamentally apply to the security of Bitcoin assets. There is no encrypted data to collect, and the exposed public keys are inherently public on the chain.
Two Quantum Algorithms: One is a Real Threat, One is Ignorable
- Shor’s algorithm (real threat): Provides exponential speedup for the underlying mathematical problems of digital signatures, allowing the public key to be used to deduce the private key and forge transaction signatures. This is what is truly concerning.
- Grover’s algorithm (not a threat): Only provides quadratic speedup for hash functions like SHA-256, and while it sounds alarming, it is immediately clear that it is simply not realistic.
A 2025 paper titled "Kardashev-Level Quantum Computing and Bitcoin Mining" calculated that under current Bitcoin difficulty, quantum mining would require:
- About 10²³ physical qubits (currently, there are only about 1,500 worldwide)
- About 10²⁵ watts of energy (the total output of the sun is approximately 3.8 × 10²⁶ watts)
To mine Bitcoin using a quantum computer would require an energy consumption comparable to roughly 3% of the total energy output of the sun. Humanity is currently only at 0.73 on the Kardashev scale, and to use quantum computers for mining would require energy levels only achievable by a Type II civilization; humanity is far from that and it is almost physically impossible to achieve.
(Note: Relating to the Kardashev civilization levels: Type I: can fully utilize the energy of a planet (Earth); Type II: can utilize all the energy of an entire star (sun))
In comparison: even with the most ideal design, the computational power of a quantum mining machine would only be around 13.8 GH/s; whereas an ordinary Antminer S21 can achieve 200 TH/s. The speed of conventional ASIC miners is 14,500 times that of quantum mining machines.
In the end, quantum mining simply does not hold. It is not possible now, it will not be possible in 50 years, and it may never be possible. If someone says that quantum computers can "break Bitcoin mining," they are confusing two entirely different algorithms.
Of the 8 Claims Circulating, 7.5 Are Wrong
Claim 1: "As soon as quantum computers appear, all Bitcoin will be stolen overnight."
The fact is, only Bitcoin whose public keys have been exposed face security risks. Modern Bitcoin addresses (P2PKH, P2SH, SegWit) do not make public their public keys until you initiate a transfer. As long as you never reuse an address and have never sent assets from that address, your public key will not appear on the blockchain.
The specific breakdown is as follows:
- Class A (directly at risk): Approximately 1.7 million BTC use the outdated P2PK format, and their public keys are fully exposed.
- Class B (exists risk but can be fixed): About 5.2 million BTC are located in reused addresses and Taproot addresses, and users can avoid risks by migrating.
- Class C (temporary exposure): Each transaction's public key is temporarily exposed during the roughly 10 minutes it waits in the memory pool for packaging.
According to Chaincode Labs estimates, a total of approximately 6.26 million BTC are at risk due to exposed public keys, accounting for about 30%–35% of the total supply. The number is considerable, but it is by no means "all Bitcoin."
Claim 2: "Satoshi's coins will be stolen, directly crashing to zero."
Partly true and partly false: Satoshi holds approximately 1.1 million BTC in P2PK format, and the public keys are fully exposed, which indeed makes them high-risk assets. But:
- Quantum computers capable of cracking these private keys do not exist at present.
- Countries mastering early quantum technologies would prioritize intelligence and military systems, rather than staging a "public Bitcoin theft PR stunt" (as stated by the Quantum Canary Research Group).
- Expanding from the current approximately 1,500 qubits to hundreds of thousands will require years of engineering breakthroughs, with progress being highly uncertain.
Claim 3: "Bitcoin cannot upgrade—too slow and chaotic governance."
This claim is not correct, but it also has some merit. Bitcoin has successfully completed several major upgrades in its history:
- SegWit (2015–2017): Highly controversial, almost failed, leading to the Bitcoin Cash fork, but ultimately went live successfully.
- Taproot (2018–2021): Smoothly implemented, taking about 3.5 years from proposal to mainnet launch.
The mainstream anti-quantum proposal BIP-360 has been officially incorporated into Bitcoin's BIP library in early 2026, adding new bc1z address types and removing key spending logic in Taproot that are susceptible to quantum attacks. Currently, this proposal is still in draft status, and the testnet is running a post-quantum signature instruction set using Dilithium.
Co-author Ethan Heilman estimates that the complete upgrade cycle will take about 7 years: 2.5 years for development and review, 0.5 years for activation, and 4 years for ecosystem migration. He admitted: "This is just a rough estimate; no one can provide an exact timeline."
Objective conclusion: Bitcoin can be upgraded and has already started the upgrade process but is still in the early stages and needs to speed up. Claiming "it is completely impossible to upgrade" is wrong, while claiming "the upgrade has already been completed" is also not valid.
Claim 4: "We only have 3–5 years left."
This is highly unlikely, but we shouldn’t be completely complacent either. Experts estimate a wide time span:
- Adam Back (Hashcash inventor, quoted in the Bitcoin white paper): 20–40 years
- Jensen Huang (NVIDIA CEO): Practical quantum computers still need 15–30 years
- Scott Aaronson (Quantum computing authority at the University of Texas at Austin): Refused to provide a timeline and indicated that cracking RSA might require "hundreds of billions of dollars投入"
- Craig Gidney (Google Quantum AI): Probability of achieving this before 2030 is only 10%; he also believes that under current conditions, it is difficult for the qubit requirements to see another 10-fold optimization; the optimization curve may have flattened out
- A survey of 26 quantum security experts found: The probability of risk appearing within 10 years is 28%–49%
- Ark Invest: "It's a long-term risk, not an immediate one."
It’s worth noting that Google's Willow chip broke the quantum error correction threshold by the end of 2024. This means that for every level of correction code distance improved, the logical error rate will decline by a fixed factor (Willow is 2.14). This error suppression effect improves exponentially, but the actual speed of expansion depends entirely on hardware, which could be logarithmic, linear, or possibly extremely slow. Breaking the threshold only demonstrates that expansion is feasible, not that it will be quick, easy, or inevitable.
Furthermore, in March 2026's paper, Google did not disclose practical attack circuits, only releasing zero-knowledge proofs. Scott Aaronson also cautioned that future researchers may no longer disclose resource estimates needed to crack passwords. Therefore, we might not be able to detect "quantum crisis day" long in advance.
Even so, building a computer with hundreds of thousands of fault-tolerant qubits remains a massive engineering challenge. The most advanced quantum computers cannot even factor numbers larger than 13 digits, while cracking Bitcoin's encryption equates to factoring a number of about 1,300 digits. This gap cannot be filled overnight, but the technological trends are worth noticing, not ignoring.
Claims 5–8: Quick Clarifications
"Quantum computing will destroy mining."
False. The energy consumption requirements are close to the total output of the sun, see part two for details.
"Collecting data now, decrypting later."
Not applicable for stealing assets (the blockchain itself is public), only has some impact on privacy, which is a secondary risk.
"Google says 9 minutes to crack Bitcoin."
Google refers to a theoretical circuit running on a non-existent 500,000 quantum bits machine, which hypothetically takes about 9 minutes. Google itself has explicitly warned against such panic rhetoric and has concealed the details of the attack circuit.
"Post-quantum cryptography technology is still immature."
The National Institute of Standards and Technology (NIST) has completed standardization of algorithms like ML-KEM, ML-DSA, SLH-DSA. The algorithms themselves are mature; the difficulty lies in deploying them within the Bitcoin system, not in inventing them from scratch.
Five Concerns I Truly Worry About
An article that completely denies everything will lose credibility. Here are five issues that deeply concern me:
- The estimated number of qubits needed to break passwords continues to decline, although this trend may be slowing. In 2012, it was estimated that cracking a password system would require 1 billion qubits; by 2019, it declined to 20 million; and by 2025, it had dropped below 1 million. In early 2026, the company Oratomic claimed that using a neutral atom architecture requires only 10,000 physical qubits to achieve cracking. However, it is worth noting that all nine authors of this study are shareholders of Oratomic, and the estimated conversion ratio of 101:1 of physical qubits to logical qubits has never been validated (the historical actual ratio is closer to 10,000:1). It’s also essential to clarify that what would take "9 minutes" to compute on Google’s superconducting architecture would take approximately 10²⁶⁴ days to complete on neutral atom hardware—these are completely different devices with vastly different computing speeds. Gidney himself also noted that the curve for algorithm optimization might have reached a plateau. Even so, no one knows when the turning point of "required number of qubits" versus "number of qubits available" will arrive. The most objective conclusion is: There is currently a vast uncertainty.
- The range of exposed public keys is expanding, not contracting. The latest and most widely promoted Bitcoin address format, Taproot, will publicly disclose adjusted public keys on the chain, leaving an infinite offline cracking window for quantum attackers. The recent Bitcoin upgrade ironically undermined quantum security, which is a thought-provoking irony. Additionally, the problem is not limited to on-chain addresses: Lightning Network channels, hardware wallet connections, multi-signature schemes, and extended public key sharing services are all designed to spread public keys. In a world where fault-tolerant quantum computers (CRQC) with password-cracking capabilities become a reality, when the entire system is built around public key sharing, it is entirely unrealistic to "protect public key privacy." BIP-360 is just the first step, far from a complete solution.
- The governance process of Bitcoin is slow, but there is still a time window. Since November 2021, Bitcoin's underlying protocol has not activated a soft fork for over four years, remaining in a prolonged stagnation. Google plans to complete its own system’s quantum migration by 2029, while Bitcoin's most optimistic estimates won’t arrive until 2033. Given that practical password-cracking quantum computers are likely still a long way off (most reliable predictions indicate they won’t appear until the 2040s, or might never realize), there is no immediate crisis now, but we must not grow complacent. The earlier preparations start, the more relaxed it will be later.
- Satoshi's holding of Bitcoin presents an unsolvable game-theory puzzle. Approximately 1.1 million BTC are stored in P2PK addresses, and since no one possesses the corresponding private keys (or Satoshi has vanished), these assets can never be migrated. Whether to let them sit idle, freeze, or destroy them all comes with significant consequences, and there is no perfect solution.
- The blockchain is a permanently locked list of attack targets. All exposed public keys will b
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




