The North Korean-related hacking organizations have gradually upgraded from traditional code vulnerabilities to a highly organized national-level attack system capable of deep supply chain penetration and large-scale money laundering.
Written by: Certik
On May 12, Web3 security company CertiK released the "Skynet North Korean Crypto Threat Report," which systematically tracks the evolution trends and flow of funds of North Korean-related hacking organizations in the crypto industry over the past decade. The report shows that from 2016 to the present, North Korean hacker organizations have accumulated plundered digital assets amounting to as much as $6.75 billion; in 2025 alone, their thefts resulted in losses of up to $2.06 billion, accounting for nearly 60% of total losses in the global crypto industry.
The report points out that North Korean-related hacking organizations have gradually upgraded from traditional code vulnerabilities to a highly organized national-level attack system capable of deep supply chain penetration and large-scale money laundering.
Core Data: Systematic Attacks and Industrialized Money Laundering
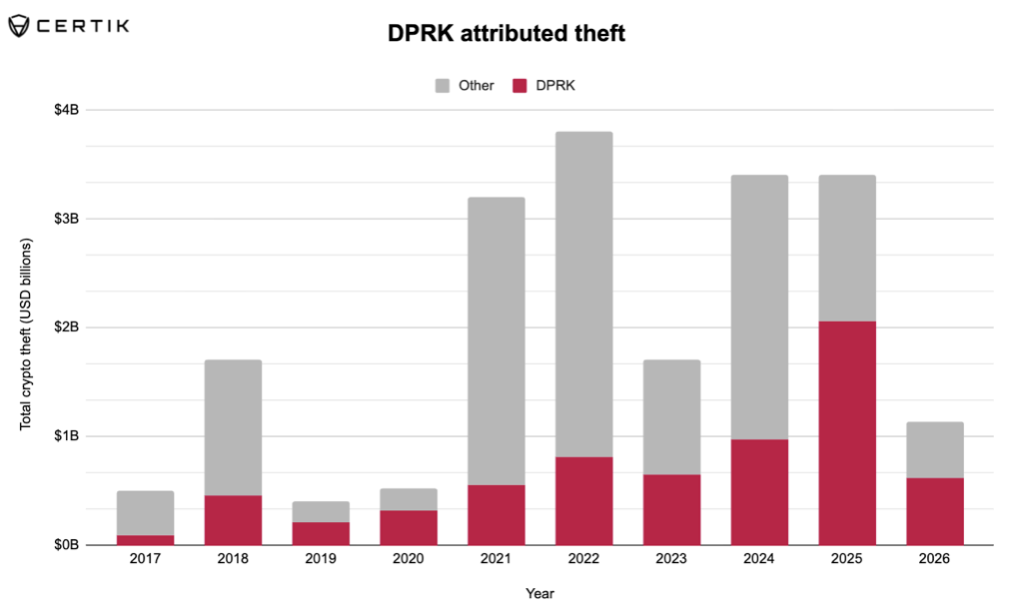
Comparison of the amount stolen by North Korea and the total amount of cryptocurrency theft worldwide
Report data shows that North Korean hackers' attacks exhibit highly precise "systematic" characteristics: the number of attacks is relatively small but focused on high-value targets with high liquidity.
- Total historical losses: Since 2016, North Korean-related hacking organizations have launched a total of 263 attacks, resulting in cryptocurrency asset losses of approximately $6.75 billion.
- 2025 catastrophic impact: In 2025, the number of North Korean-related attacks accounted for only 12% of the global total, but the amount stolen reached $2.06 billion, nearly 60% of the total losses in the crypto industry for the year. The Bybit incident, with losses of $1.5 billion, became the largest single theft in the history of the crypto industry.
- Threat continuation in 2026: As of early 2026, confirmed losses of cryptocurrency assets attributed to North Korean hackers are approximately $620.9 million, accounting for about 55% of global total losses.
- Amazing money laundering efficiency: In major cases like Bybit, over 86% of stolen funds (mainly Ethereum) were laundered and transferred within just one month through mixers, cross-chain bridges, decentralized exchanges (DEX), and over-the-counter (OTC) networks.
Tactical Evolution: From "Cracking Code" to "Exploiting Human Nature" and Infrastructure
The "Skynet North Korean Crypto Threat Report" deeply analyzes significant security incidents in recent years, pointing out a fundamental shift in the attack trajectory of North Korean hackers: they no longer simply search for vulnerabilities in smart contract code but aim at the weaknesses in human nature and supply chains.
The report outlines three major cases that represent the continual evolution of their capabilities:
- The Ronin cross-chain bridge incident (2022, loss of $625 million): Demonstrated the power of social engineering, hackers succeeded in implanting spyware into internal engineers through fake job phishing on LinkedIn.
- The Bybit exchange incident (2025, loss of $1.5 billion): Marked the emergence of supply chain attacks as a typical characteristic. The attackers did not directly target the exchange itself but instead breached the developers' devices of a third-party multi-signature platform (Safe multi-signature wallet) it used, tampering with a trusted user interface.
- The Drift protocol incident (2026, loss of $285 million): Exposed a new "physical infiltration" model. The attackers hired third-party intermediaries and personally attended crypto industry conferences for six months to establish offline relationships with core contributors of the protocol and invest real funds to build trust, ultimately conducting the attack through oracle manipulation and governance takeover.
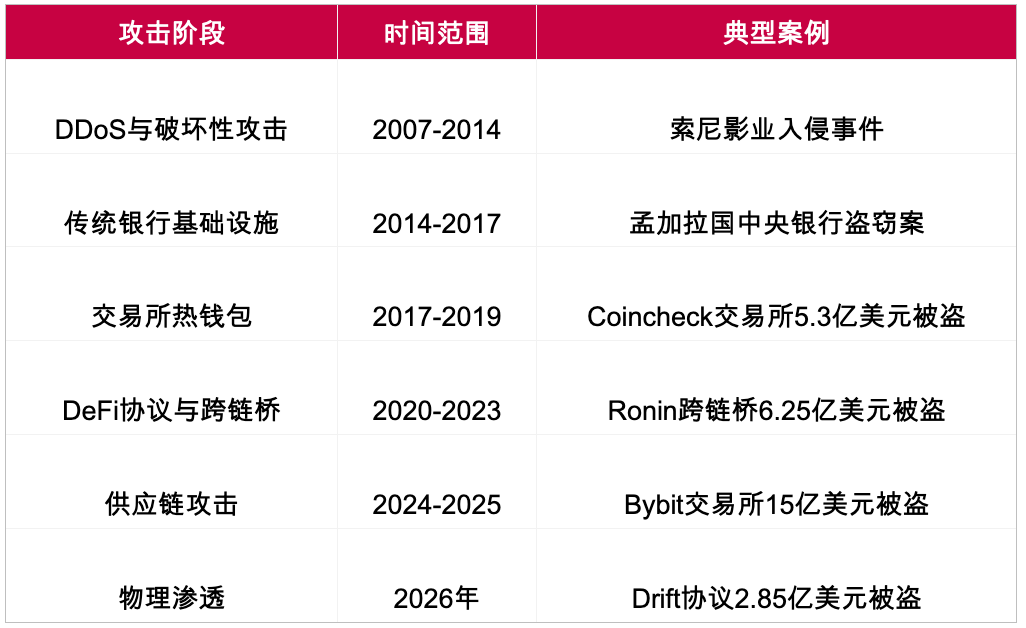
Changes in North Korean hacker tactics
Covert Threats: IT Personnel Infiltration and Blockchain C2 Facilities
In addition to external attacks, the report also reveals two covert methods by which North Korean hackers penetrate the internal crypto ecosystem:
- Real internal threats (IT workers): For years, thousands of North Korean IT professionals have used forged identities to enter DeFi protocols and work remotely for Western tech companies. They lurk as "trusted internal employees," secretly providing intelligence support, and in some cases (such as the Munchables platform incident), directly participated in stealing funds from the organizations they worked for.
- Abusing blockchain as infrastructure: In October 2025, Google's threat intelligence team disclosed that North Korean hacker organizations had first adopted "EtherHiding." They use public blockchains as decentralized command and control (C2) infrastructure, embedding malicious attack payloads within the transaction data of smart contracts, making the infrastructure nearly impossible for law enforcement to forcibly shut down.
Industry Defense Recommendations: Building a Deep Defense System Against National-Level Hackers
In response to the escalating attack patterns, Stefan Muehlbauer, head of government affairs at CertiK, warned: "The Drift protocol attack indicates a fundamental change in North Korea's attack methods. By the time on-chain attacks actually occur, the preliminary infiltration work has already been completed. Relying solely on technical security frameworks is no longer sufficient to effectively counter such threats." CertiK recommends that the crypto industry and related financial institutions focus on implementing the following defense measures:
- Implementing a zero-trust hiring model: Treat all remote freelancers and new employees as high-risk individuals by default and prohibit their access to core production code, private keys, and management backends until a long-term verifiable physical trust relationship is established. Enforce video interviews with live detection and use professional background verification services to screen for fake identities.
- Enhancing defense against social engineering: Conduct regular employee security training against fake job offers, disguised venture capital, and malicious code repositories. Prohibit receiving and executing code files, meeting links, and investment documents via instant messaging tools like Telegram and Discord without verified identities.
- Strengthening supply chain and infrastructure security: Implement strict security audits for third-party service providers (like multi-signature wallets and cloud service providers) to avoid over-reliance on single suppliers. Private keys for high-value transaction signing and vault funds management must be stored in physically isolated hardware security modules (HSM), with any operations requiring multiple human physical authorizations.
- Establishing a financial security cooling-off mechanism: Mandate a 24-72 hour cooling-off period for large withdrawals to give the security team a time window to intercept suspicious transactions. Enforce time locks on all protocol management and governance operations, prohibiting zero time lock permission changes.
While companies can establish the first line of defense internally through the above mechanisms, the defensive capacities of individual institutions often have clear limitations when facing systematic and sustained attacks from national-level hackers. Companies not only need to implement internal basic protective measures but should also build an external security support system covering the entire lifecycle.
From the perspective of risk prevention before attacks, professional institutions can provide security inspections like smart contract code audits, formal verification, and penetration testing to detect and repair potential vulnerabilities in advance; during project operation, continual 24/7 emergency responses, all-day risk monitoring, and in-depth on-chain anti-money laundering/KYT (Know Your Transaction) fund tracking are essential. In addition, as global regulatory environments tighten, professional proof of reserve (PoR) audits and licensing compliance support are key to cutting off illegal money laundering links. Building a multi-layered protective network from underlying code to on-chain fund tracking is already a survival lifeline for the sustainable development of the entire digital asset industry.
Full report: https://indd.adobe.com/view/a0a77d99-44d6-4b7e-9e2c-765ad54d36f2
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



