How much money have you put into the DeFi protocol?
“Just use Aave,” this has been a long-standing mantra in the crypto circle, meaning, “Don’t mess around with those flashy little protocols, the risks are too high, just use Aave, which has undergone multiple audits, has been running for so many years, and is an industry benchmark; putting money in there is relatively safe.”
However, this phrase seems no longer taken for granted. There have even been antithetical expressions like “‘just use Aave’ is dead,” “Ethereum narrative has failed,” and even “DeFi is dead.”
Such emotional expressions in the market seem unsurprising during April, a month marked by frequent theft incidents in the crypto industry.
2026, the year with the most thefts in history
This month has only passed two-thirds; although the prices of BTC and ETH are slowly rising, the series of thefts in the crypto market remains astonishing.
In less than 20 days in April, the total losses exceeded $605 million, with at least 12 protocols being attacked. Some of the more well-known incidents include:
On April 1, Drift Protocol, the largest perpetual contract exchange on Solana, was hacked for $285 million in just 12 minutes, becoming the largest single DeFi attack of 2026 up until that point.
On April 10, decentralized GPU cloud infrastructure Aethir detected a malicious attack on its ETH cross-chain bridge contract and promptly severed the affected contract, keeping the loss within $90,000. On the same day, Hyperbridge suffered a validation vulnerability attack, where the attacker forged cross-chain messages, minted and dumped 1 billion bridged DOT tokens, resulting in a loss of about $2.5 million.
Around mid-April, multiple small protocols fell victim. Silo Finance lost $392,000 due to an oracle configuration error; bridging aggregator Dango suffered a loss of $410,000 due to a smart contract vulnerability attack; an attacker on the NEAR network prepared 423 wallets and 8 fake liquidity pools two days in advance to manipulate the oracle, ultimately stealing about $18.4 million.
On April 18, Kelp DAO was hacked for $292 million, breaking the record for DeFi thefts in 2026.
“2026 is likely to become the year with the most thefts in history,” said Charles Guillemet, head of security at Ledger.
This viewpoint is likely to come true, not because DeFi has become weaker, but because attackers have gained a new weapon—AI.
How do white hats and black hats use AI to find protocol vulnerabilities?
In the past year, the value of AI-driven exploitations has approximately doubled every 1.3 months, with the cost of scanning an individual contract now down to $1.22. The collapsing threshold for attacks might be the true reason behind the record numbers in 2026. In April of this year, Anthropic disclosed that its internal model, Claude Mythos Preview, autonomously discovered thousands of zero-day vulnerabilities in mainstream operating systems and cryptographic libraries, achieving a 72.4% exploitation success rate, whereas prior AI models were close to zero.
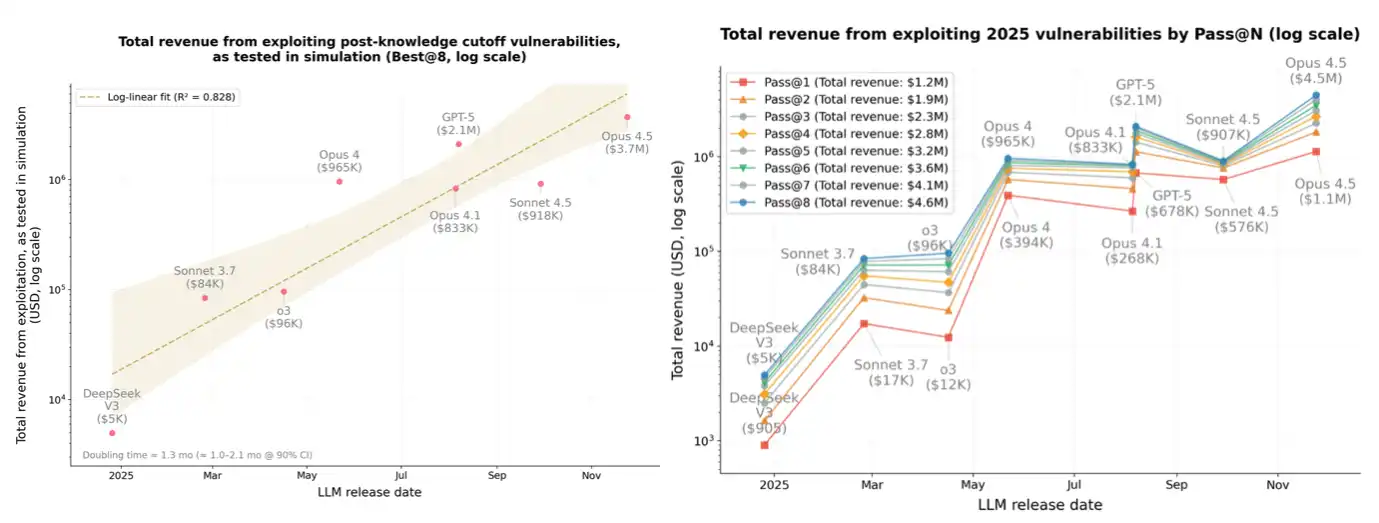
Illustration: The vertical axis shows the simulated theft amount (logarithmic scale), and the horizontal axis is time, demonstrating the trend of approximately doubling the exploitation gains of 10 cutting-edge AI models on contracts after their knowledge cutoff in the past year. The shaded area represents the 90% confidence interval.
A typical case is: On the day after Drift was hacked, a developer named Zengineer used Claude Code to create an AI-open-source risk auditing tool called Skill, which assessed the architectural risks of protocols using public data (DeFiLlama, on-chain contracts, governance documents, Safe API) and automatically compared them with historic attack patterns of Ronin, Harmony, Euler, Beanstalk, and others.
He believed that Drift’s incident and most recent larger thefts in DeFi did not exploit any vulnerabilities in Solidity code. The real fatal weaknesses lie in governance structures, administrative key permissions, and cross-chain bridge validator configurations; these “non-code” security blind spots are inherently unseen by traditional auditing companies’ code scanners, and the tool he developed is capable of detecting them.
Twelve days before Kelp DAO was hacked, he ran afull audit on Kelp DAO using this tool, and the report scored 72 points (medium risk), marking five main issues, including “DVN configuration is not transparent: the number of LayerZero validating nodes and thresholds are not publicly disclosed,” “16-chain single point of failure: if DVN fails, all rsETH on every chain simultaneously loses collateral,” “the attack scenarios of Ronin and Harmony, which were stolen $600 million and $100 million in 2022 respectively, are highly similar,” “governance scope is unclear,” “no insurance fund: there is no loss absorption mechanism in place; if something goes wrong, the downstream protocols bear the losses themselves,” etc.
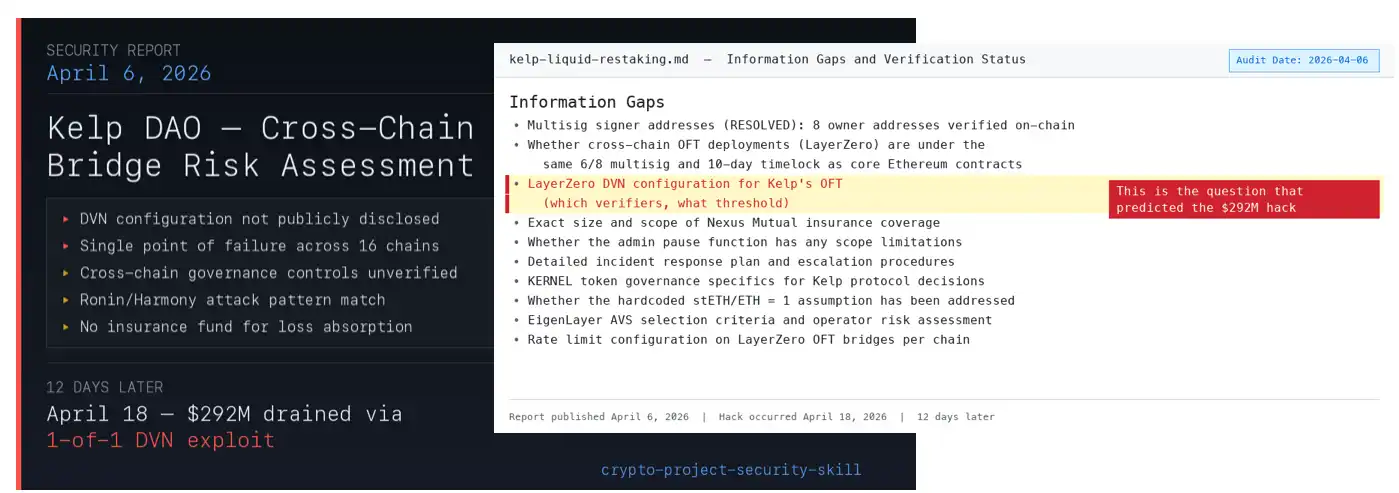
The issues regarding Kelp's DVN configuration mentioned in Zengineer's report
Twelve days later, on April 18, Kelp was hacked, and the root cause was indeed the 1-of-1 DVN configuration, which was highlighted as the first risk in the report.
Ledger BlockBeats found that Zengineer's AI open-source risk auditing tool Skill has completed full audits on 56 out of the top 100 TVL protocols on DeFiLlama; besides Kelp DAO, it also identified several other protocols with high-risk vulnerabilities, including the outdatedly audited JustLend (TVL $3.3 billion); Falcon Finance (TVL $1.6 billion), which is associated with DWF Labs and has an insurance fund only 0.6% of its TVL; Grove Finance (TVL $2.87 billion), whose governance structure is undisclosed and whose parent company was previously subjected to a DNS hijacking; and Camelot, which has a 2/3 multisig, zero time lock, and anonymous team.
These protocols have not encountered issues today, but this does not mean they are completely safe; it could very well be that attackers have yet to find an entry point.
The cost to attack a contract is only $1.22?
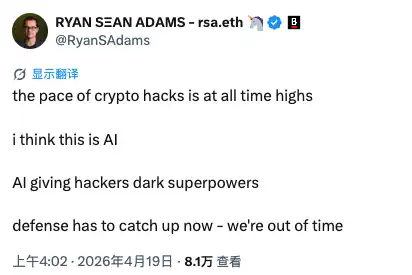
The frequency of crypto hacks has reached an all-time high. I believe this is related to AI. AI is giving hackers “dark superpowers.” Defenses must catch up quickly; we no longer have time,” warned Ryan Sean Adams, co-founder of Bankless.
In October last year, Anthropic researchers conducted a set of experiments, allowing Sonnet 4.5 and GPT-5 to scan 2,849 newly deployed real-world smart contracts with no known vulnerabilities. Both models independently discovered two previously unknown zero-day vulnerabilities and generated corresponding attack plans, simulating a profit of $3,694. The API cost for GPT-5 to accomplish this was around $3,476. With less than $3,500 in computational power, new holes can be dug in real deployed contracts.
Even more alarming is the cost curve; as mentioned earlier: in the past year, the value of exploitation from AI-simulated attacks has approximately doubled every 1.3 months, while the token cost required to generate effective attack code has sharply declined with the iteration of new models. Attackers, with the same budget, can obtain increasingly more effective attacks. The cost to scan an individual contract has already dropped to $1.22.
What does this mean? Anyone with a few thousand dollars in computational power can, in theory, point AI agents at thousands of smart contracts, allowing it to automatically scan for vulnerabilities, generate attack code, all without needing to write any code or have a deep background in security research.
The barrier for ordinary people to become hackers has significantly lowered.
In April of this year, Anthropic revealed its internally developed model, Claude Mythos Preview, limited to use by 40 carefully selected corporate and government partners. It autonomously discovered thousands of zero-day vulnerabilities in mainstream operating systems, browsers, and cryptographic libraries, including critical infrastructure relied upon by underlying DeFi protocols. One of these vulnerabilities had lurked in OpenBSD systems for 27 years, existing within global key financial infrastructure, until this model found it. The exploitation success rate of Mythos Preview reached 72.4%, whereas prior AI models were close to zero.
However, Anthropic currently refuses to release this model to the public, one reason being: if released, the balance of power between attackers and defenders would be disrupted, potentially plunging the industry into an abyss.
Another practical case comes from the AI security company Cecuro. They analyzed 90 DeFi smart contracts hacked from October 2024 to early 2026, which involved total losses of $228 million. Their dedicated AI security agent successfully identified vulnerabilities in 92% of the contracts, while a generic AI programming agent running the same underlying model only identified 34%. The crucial detail is that several contracts in this batch had undergone professional human audits before being hacked, yet AI found the holes missed by human auditors.
Attackers' weapons are becoming stronger at an exponential rate, while the defensive infrastructure is clearly lagging behind.
Ethereum may be the biggest victim
Returning to the Kelp DAO hack incident.
Kelp's rsETH is a product of the Ethereum re-staking ecosystem. Users deposit stETH to receive rsETH, which can be used as collateral to borrow WETH on Aave and can also be cross-chain transferred, circulating across more than 20 networks, showcasing the magic of DeFi composability.
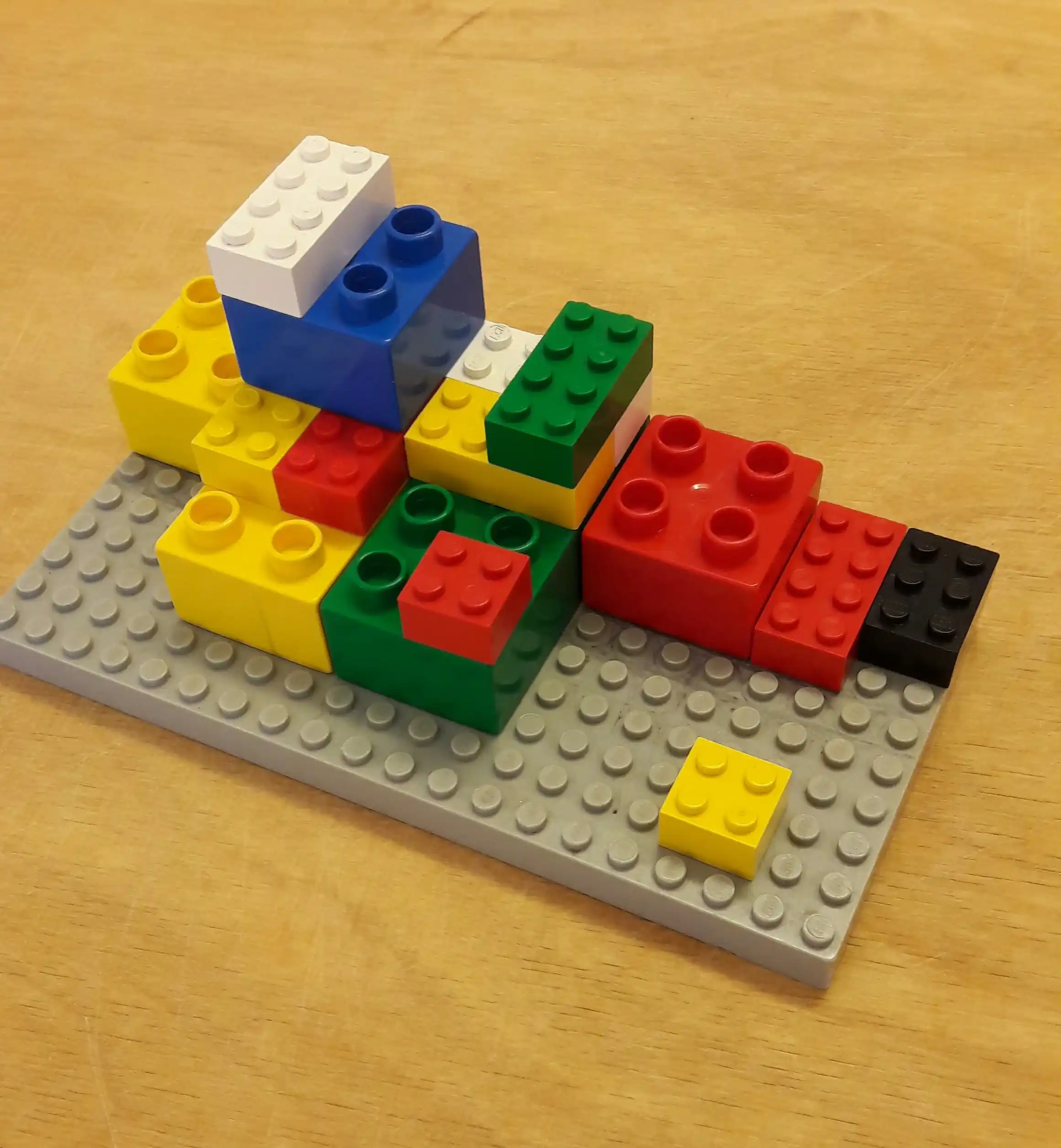
But on the flip side, if attackers only need to tear open a gap at the weakest point, the entire LEGO composable structure will reverse-transmit: fake rsETH becomes real collateral, real WETH gets borrowed away, and bad debts are left behind on Aave, causing panic to spread to all protocols that have integrated rsETH, and SparkLend, Fluid, and Lido's earnETH all urgently paused.
Aave founder Stani Kulechov stated immediately: Aave’s contracts themselves were not hacked, this was an external event. This is true. But the reality is that Aave's WETH lending pool utilization rate once soared to 100%, and ordinary depositors found themselves unable to withdraw. The TVL dropped from $26.4 billion to $17 billion within four days, with nearly $10 billion flowing out, and the AAVE token also fell by about 18%.
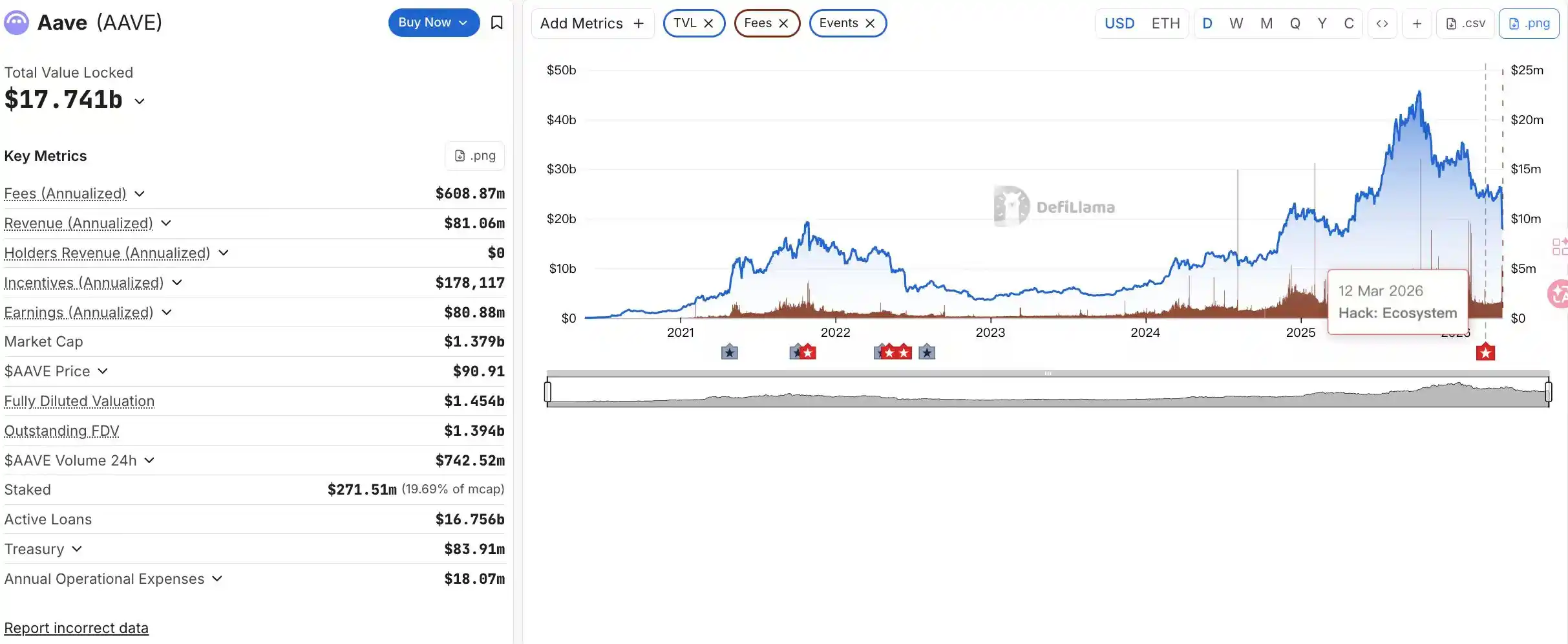
Data source: DefilLama

Data source: tradingview
But the statement “Aave's contracts were not exploited” offers no consolation to those liquidity providers trapped inside. As Cyvers CEO Deddy Lavid put it succinctly: “This reflects the composability risks of DeFi; when a protocol’s token is integrated across multiple platforms, a single vulnerability can cascade through the entire ecosystem.”
And this might also be the structural paradox of the Ethereum DeFi narrative.
What Ethereum takes pride in the most is its “composability,” its financial LEGO, where any protocol can stack like building blocks. This is both its core value and its core vulnerability. Every layer of a new protocol, every new bridge, every new type of collateral expands the attack surface of the entire system. And this expansion cannot be covered by any single auditing entity.
The Kelp attackers did not break the cryptography or find a zero-day vulnerability in the smart contract. They exploited a configuration choice in the cross-chain validators, deceiving LayerZero’s messaging layer to mint 116,500 rsETH out of thin air on the Ethereum mainnet. The contract itself was not broken; it was the verification layer that failed. This distinction is crucial because the next wave of attackers does not need to wait for configuration errors. They will have AI.” wrote Jason Jones, an analyst at Brave New Coin.
The narrative of Ethereum's value in this cycle mainly has two strands. One is the RWA and ETF narrative on the institutional side, with tokenized assets from BlackRock and Morgan Stanley still running on Ethereum, and ETF funds slowly flowing in; this narrative is generally still intact. But regarding the narrative of “Ethereum as the foundational settlement layer of DeFi,” which underpins countless retail investors holding ETH, it is currently undergoing its most rigorous test of trust.
From the market's reaction, it is evident that panic has indeed spread beyond the Kelp hack incident itself, beginning to impact the entire DeFi ecosystem. Morpho, Sky, JupLend are all experiencing withdrawal surges, even though they have no financial connection to Kelp.
Clearly, this is a crisis of trust, not a crisis of technology.
Let’s return to the initial question. How much money have you put into DeFi protocols?
If your answer is “not much, just playing around,” then you can consider it as nothing happened. But if your position is significant, it may be time to reassess the DeFi industry: The security model of DeFi projects is “audit once before deployment,” but now AI can continuously scan and find new vulnerabilities in real-time post-deployment, and it’s becoming cheaper.
This is not to say that Ethereum has no future. The Ethereum chain has not been hacked, Aave’s code has no vulnerabilities, and Uniswap is still operating normally today. But the assumption of “just use Aave” needs to be reassessed in an AI-driven, stacked composability attack environment.
The security of LEGO blocks up and down the supply chain is transferable, and no one can guarantee that all blocks are absolutely safe.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




