In the early hours of April 18, 2026, a few hours after the KelpDAO attack incident, Solidity developer 0xQuit posted a message on X.
“I wish I could bring better news, but WETH on Aave seems to be done for. If possible, withdraw, but it may already be too late. After the Umbrella settlement, normal deposits should be partially withdrawable. This is a huge blow to the DeFi vision.”
When this post was made, Aave’s founder Stani Kulechov had just issued another statement on the same platform: rsETH had been frozen, and Aave’s smart contracts “were not compromised”; the issue lay with Kelp DAO. The two posts scroll side by side on the same timeline.
Both posts state facts. However, they are answering different questions. Stani addresses who moved the code, while 0xQuit addresses who will bear the consequences.
The answer is: no code was manipulated. And the consequences fall on everyone who deposited WETH into Aave, thinking they were just earning a bit of interest.
In the six months leading up to the attack, Aave’s governance system approved every decision that made this possible. No one hacked any code. Someone used an approved set of rules to collapse the protocol as designed. This warrants a thorough recounting.
Twelve Days
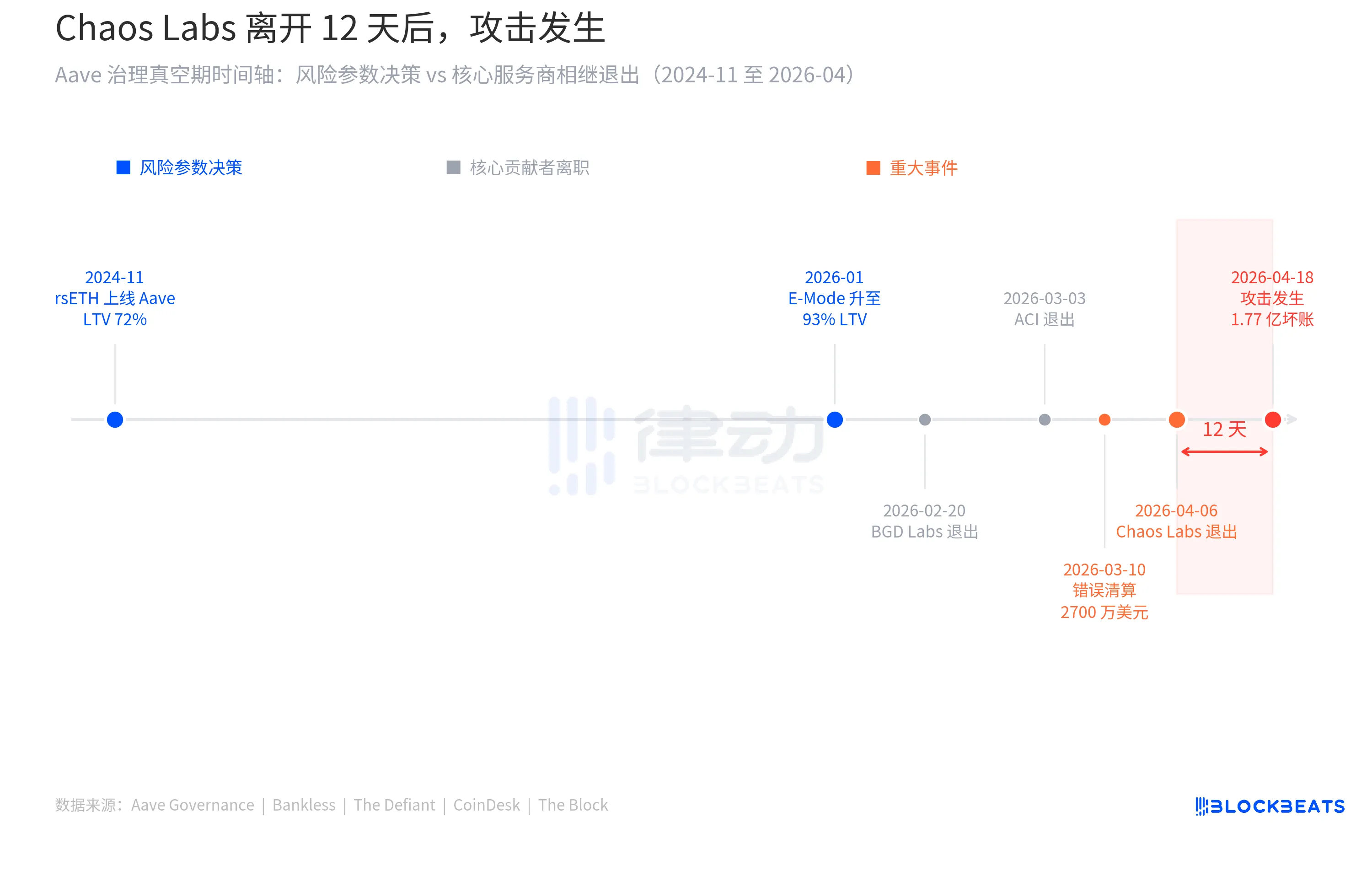
On April 6, Chaos Labs founder Omer Goldberg posted on X announcing that the collaboration between Chaos Labs and Aave DAO would officially come to an end.
For the past three years, Chaos Labs has led Aave’s risk parameter management. During this time, Aave’s TVL grew from $5.2 billion to over $26 billion. Behind every $100 million increase, there was a model from Chaos Labs calculating boundaries: which parameters could be pushed, which could not be altered.
Goldberg provided three reasons for his departure. First is a “fundamental disagreement” on risk strategy, especially after the introduction of new architecture in Aave V4. Second, the operational complexity brought by V4 has significantly increased, but resource compensation has not kept pace. Third, even under a $5 million budget plan, Chaos Labs remained at a loss, making it economically unsustainable.
“This partnership no longer reflects how we believe risk should be managed,” he wrote.
Aave's response came quickly. Stani Kulechov stated that the protocol would not interrupt operations, and the risk management agency LlamaRisk would take over all responsibilities, “the two-layer risk management system continues to maintain.” LlamaRisk immediately issued a statement, promising “full operational continuity” and submitted a formal renewal proposal to Aave DAO within a week. From the outside, this appeared to be an orderly handover.
Three days later, on April 9, LlamaRisk, as the new risk manager, submitted the first batch of regular adjustments: increasing the supply cap of rsETH on the Aave V3 mainnet from 480,000 to 530,000. The basis was on-chain data, indicating healthy utilization, ample liquidity, and collateral concentration within acceptable thresholds. There were no unusual markings.
Nine days later, at 17:35 UTC on April 18, the attacker invoked the LayerZero EndpointV2 contract on the Ethereum mainnet, passing a forged cross-chain data packet to Kelp DAO's rsETH bridging contract. The bridging contract did not recognize that the message was false. 116,500 rsETH flowed to an address controlled by the attacker.
Forty-six minutes later, Kelp DAO's emergency pause mechanism activated, preventing the attacker from two additional theft attempts, which combined were about $100 million. However, the initial batch was unrecoverable. The attacker's target was around $390 million, and they managed to acquire three-quarters of it.
Before the pause mechanism activated, the attacker had already deposited the stolen rsETH into Aave V3 as collateral, borrowing large amounts of WETH and ETH. The market price of rsETH began to plummet after the attack news spread, evaporating the value of the collateral. What was technically valid collateral became unable to be liquidated. Bad debts thus formed.
The Document That Was Never Written
On January 19, 2026, the Aave community approved governance proposal 434. The core of the proposal was to include WETH in the rsETH LST E-Mode while also increasing the maximum loan-to-value ratio of rsETH in this mode from 92.5% to 93%. The numerical change was small, but the meaning was clear: users could use $100 of rsETH to borrow $93 worth of WETH on Aave.
This proposal was driven by the ACI (Aave Chan Initiative, Aave's core governance service agency). The proposal text outlined expectations: by introducing the rsETH/WETH looping strategy, idle ETH liquidity within the protocol was to be absorbed, and it was anticipated to bring in “up to $1 billion of rsETH inflow,” while also returning the utilization rate of the WETH pool to optimal ranges.
The proposal had another, more straightforward reason: to “maintain competitive parity with ezETH and weETH.” Since competitors' LRT assets on Aave had already secured similar parameters, rsETH should align accordingly.
This is a common decision-making logic in DeFi, known as competitive benchmarking. Whatever your competitor has secured, you should have as well; otherwise, liquidity will flow away. In the context of pursuing capital efficiency, this logic is virtually impeccable. It also carries an inherent one-way pressure: parameters can only be pushed higher, not lower. Any proposal to tighten parameters is labeled as “undermining competitiveness.” The result is that the entire industry drifts in the same direction, and no one is asking where it is drifting to.
Opening the governance document for proposal 434, one thing cannot be found: a risk assessment report specifically addressing the question, “Can rsETH's LTV be raised to 93%?” LlamaRisk had submitted a complete collateral risk assessment upon rsETH's initial listing in November 2024, analyzing rsETH's yield accumulation mechanisms, smart contract structures, and liquidity characteristics. However, that report answered whether “rsETH could go on Aave.” When proposing to push the LTV to 93%, the basis in the governance document relied on horizontal benchmarking and anticipated protocol income.
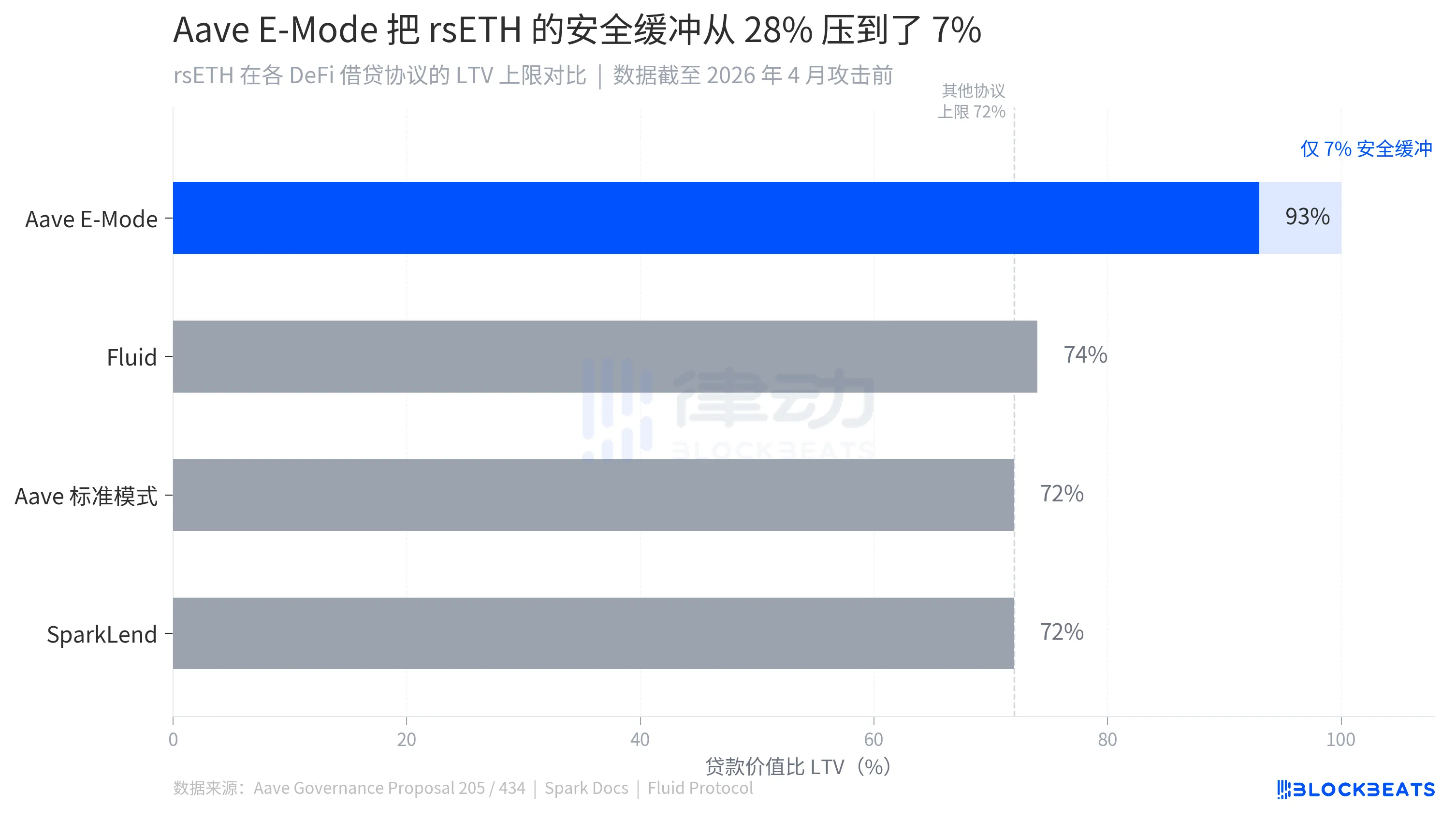
The other two DeFi protocols that accepted rsETH provided different answers: SparkLend set an LTV of 72% for rsETH, while Fluid Protocol applied a fixed minimum collateral rate equivalent to around 75% LTV. Both of these completed the market freezing of rsETH within hours of the attack. Aave's number is 93%. The additional 21 percentage points gained a competitive advantage.
On April 6, Chaos Labs announced its exit from Aave risk management. On April 9, the newly appointed LlamaRisk submitted a routine Risk Stewards adjustment proposal, raising the supply cap of rsETH from 480,000 to 530,000. The rationale was that on-chain data was healthy, utilization was normal, liquidity was ample, and collateral concentration was within acceptable limits. All metrics came from on-chain.
Those on-chain metrics record the circulation conditions of rsETH within Aave, how many people are using it, whether the risk is diversified, whether liquidity is abundant. What they fail to cover is: what kind of bridge rsETH passed through before arriving at Aave.
An Alarm That Was Not Understood
In the early hours of March 10, this year, a series of unusual liquidation transactions began to appear on the Ethereum chain. 34 highly leveraged positions using wstETH as collateral triggered liquidation lines without any warning. Users had no time to react, and the liquidation bots completed the operation.
The trigger was a configuration error in Aave's CAPO oracle system, creating an inconsistency between snapshot ratios and snapshot timestamps, causing the reported price of wstETH to be about 1.1939, while the actual market exchange rate was about 1.228. The deviation was 2.85%, which could normally be regarded as negligible.
However, in the E-Mode environment, a 2.85% price undervaluation was sufficient to push 34 high-leverage positions over the liquidation line, resulting in about $27 million in erroneous liquidation losses. From the suggestion issued by Chaos Labs' Edge Risk system to the execution of BGD's AgentHub in the next block, then to the liquidation bots completing the operation, the entire chain took place within minutes, leaving no window for human intervention.
After the fact, Chaos Labs published an analysis report. The conclusion was: “This event does not reflect a defect in the underlying CAPO or off-chain risk oracle design, but rather an inconsistency in the on-chain configuration under different update constraints, leading to discrepancies between snapshot ratios and timestamps.”
Configuration issues, not design problems. Accidents, not warnings.
Aave fully compensated affected users from recovered funds and the DAO treasury through governance proposals. The incident was thus concluded. A later industry report stated, “Despite this incident, Aave's overall deposits and loans remained stable at the beginning of 2026, without substantial weakening of confidence in the protocol's core design.”
Six weeks later, the term “core design” would undergo another test, at a different scale.
The Bill Arrived
About an hour after the attack occurred, Stani Kulechov emphasized on X that Aave's smart contracts themselves “were not compromised.” This was technically correct; no code was hacked, no private keys were stolen, and the contract operated exactly as it was set to.
The problem lay here. When rsETH became unpegged and massively devalued due to the attack, the “highly correlated” design of E-Mode worked in reverse: the system continued to view the significantly devalued rsETH as valid collateral, preventing normal liquidation of the borrowed WETH and ETH. The mechanism designed to enhance capital efficiency turned, in extreme cases, into a lock holding bad debts.
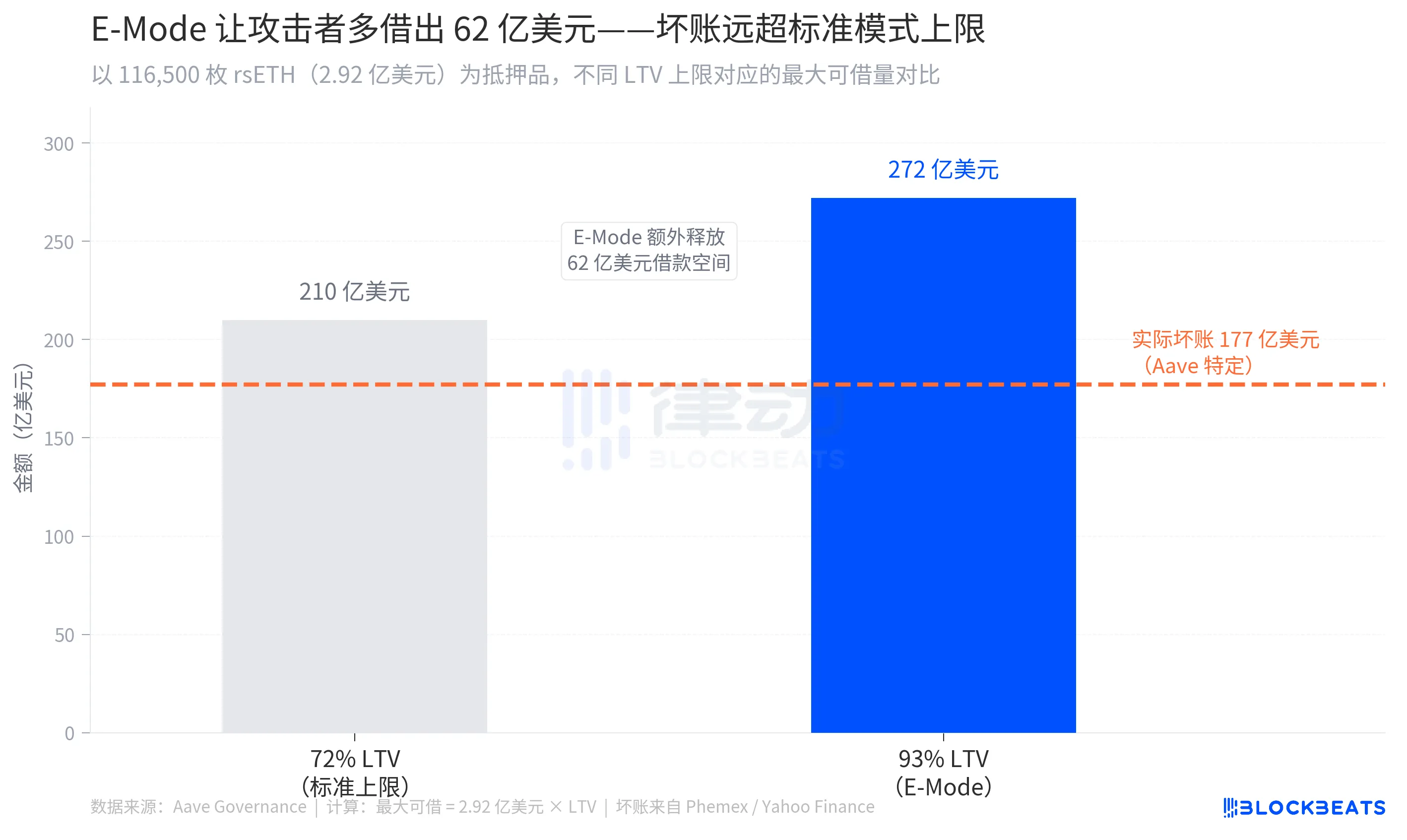
The estimated scale of bad debts ranged between $177 million and $200 million (according to multiple sources including Phemex and Yahoo Finance), while the total borrow positions opened by the attacker exceeded $236 million (according to CryptoBriefing). With 116,500 rsETH as collateral, under the 93% E-Mode LTV, up to approximately $272 million in WETH could be borrowed, which was about $62 million more than the standard 72% LTV limit, compressing the safety buffer from 28% to 7%, making any slight price fluctuation enough to put the position out of control.
Aave has a safety mechanism specifically designed for such situations, called Umbrella. Users can stake aWETH into Umbrella's security vault to earn additional yield, and when the protocol incurs bad debt deficits, this portion of assets is automatically destroyed to cover losses, requiring no governance vote intervention throughout the process. Users who opt to stake are generally those who understand the mechanism's design, are willing to exchange principal for higher yields, and are taking on the protocol's backstop function; they are active supporters of the protocol. Umbrella went live at the end of 2025, replacing the old Safety Module, and this was its first real test.
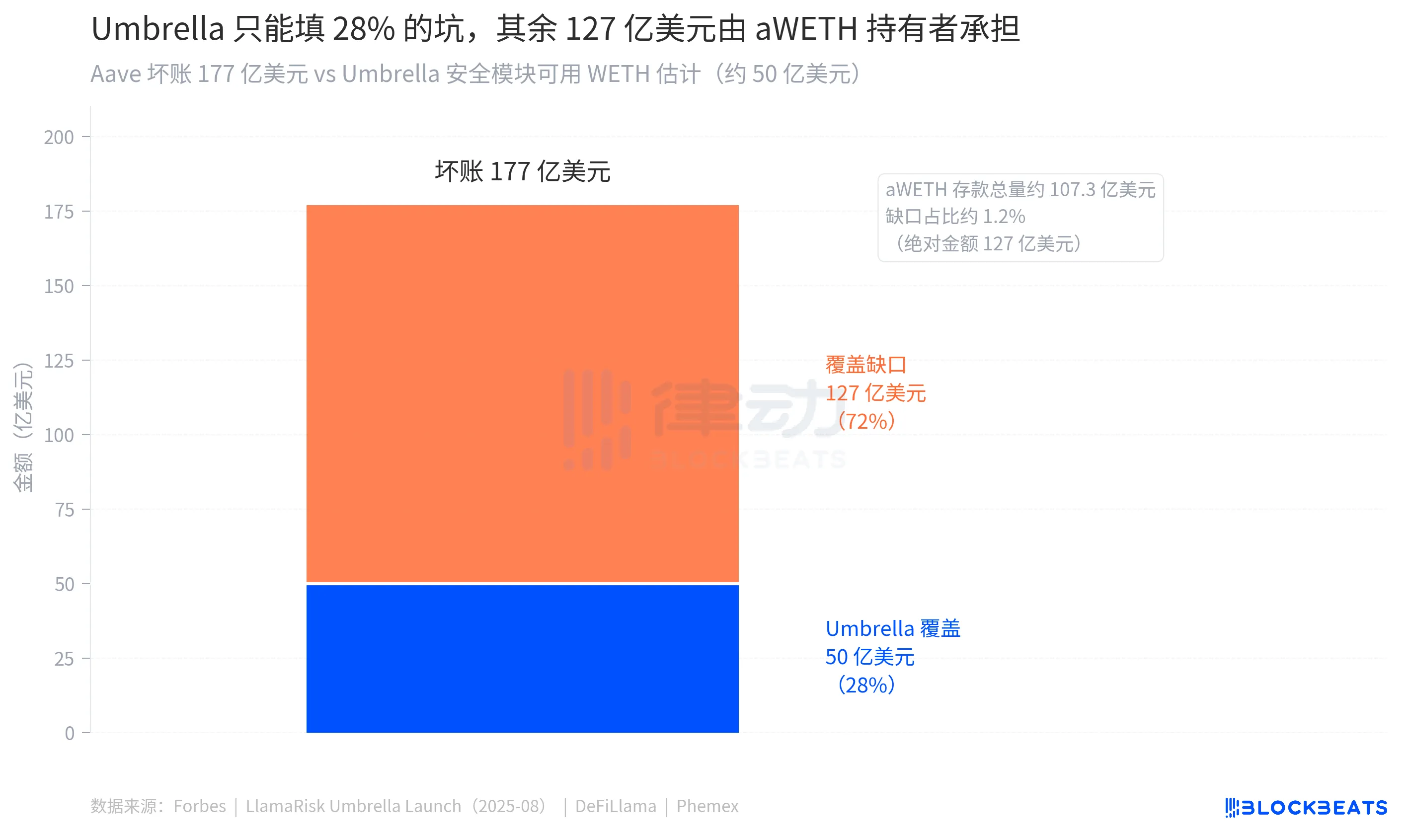
There was about $50 million of WETH in Umbrella available to absorb losses (according to Forbes). The scale of bad debts ranges from $177 million to $200 million. The gap between the two figures is approximately $127 million to $150 million.
This part would be borne by ordinary WETH depositors who did not stake. Aave's official document describes the Umbrella mechanism: after staked assets are destroyed, “remaining WETH suppliers should be able to partially withdraw, but there is no guarantee of complete recovery, and depositors may face a haircut.” “Haircut” means losing a portion of the principal.
On the night of the attack, Marc Zeller stepped forward to speak. He is the founder of ACI and a key proponent of proposals 205 and 434, who will be leaving Aave this July. He refuted the extreme estimates of the scale of bad debts, stating that the actual number was “far below that figure,” and urged users to withdraw WETH from Aave V3 to reduce risk. He also added that “this event will effectively test Umbrella,” as if it were a stress test rather than a real loss of user principal.
That day, the AAVE token fell by 10.27%, closing at $105.73. This occurred while the scale of bad debts was still undetermined and a large number of WETH depositors awaited the time node for Umbrella's settlement.
Conclusion
0xQuit's post was widely forwarded on the night of the attack. Many of those forwarding it were WETH depositors of Aave. Before sharing, they read those few lines repeatedly. “After the Umbrella settlement, normal deposits should be partially withdrawable.” How much is “partial”? What does “normal” mean? What does the word “should” imply?
0xQuit's last statement was, “This is a huge blow to the DeFi vision.” Within the vision of DeFi is a principle: your assets, your rules, and no one can make decisions behind your back that you are unaware of.
Those decisions were made over the past six months, in governance forum proposal texts. No hacker burst through the door, and no code vulnerability predetermined this outcome from the onset. It was repeated pursuits of “efficiency,” continuous disregard for “signals,” and a critical gap of time that collectively delivered this bill. The cost of governance was ultimately paid by those who neither participated in governance nor knew it had ever occurred.
The code ran as approved. The bill arrived in the hands of those who did not participate in those approvals.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



