On April 18, 2026, the liquidity re-staking protocol of Kelp DAO was attacked within hours, with attackers withdrawing 116,500 rsETH from a cross-chain bridge, amounting to approximately 293 million dollars at the time. The whole process was unusually efficient, moving from forging cross-chain messages to borrowing real assets by distributing illicit funds across three lending protocols: Aave V3, Compound V3, and Euler. On the same day, the attacker exited with 236 million dollars' worth of WETH. Aave, SparkLend, and Fluid promptly froze the rsETH market.
This is the largest DeFi attack event to date in 2026.
However, one thing distinguishes this attack from most hacker incidents. The smart contract code of Kelp DAO contains no vulnerabilities. Security researcher @0xQuit, who participated in the investigation, stated on X, "From what I know, this is a combination of two issues: the 1-of-1 DVN configuration and the DVN node itself being breached." LayerZero officials also did not mention the contract code in their statement, characterizing the issue as a "rsETH vulnerability" rather than a "LayerZero vulnerability."
293 million dollars is not found in any line of code. It is hidden in a configuration parameter that was incorrectly filled at deployment.
The general logic of DeFi security audits is: find contracts, read code, find vulnerabilities. This logic works quite smoothly when dealing with code logic vulnerabilities, and tools like Slither and Mythril are quite mature in their detection capabilities for known patterns such as reentrancy attacks and integer overflows. LLM-assisted code auditing, heavily promoted in the past two years, also has some ability to address business logic vulnerabilities (like flash loan arbitrage paths).
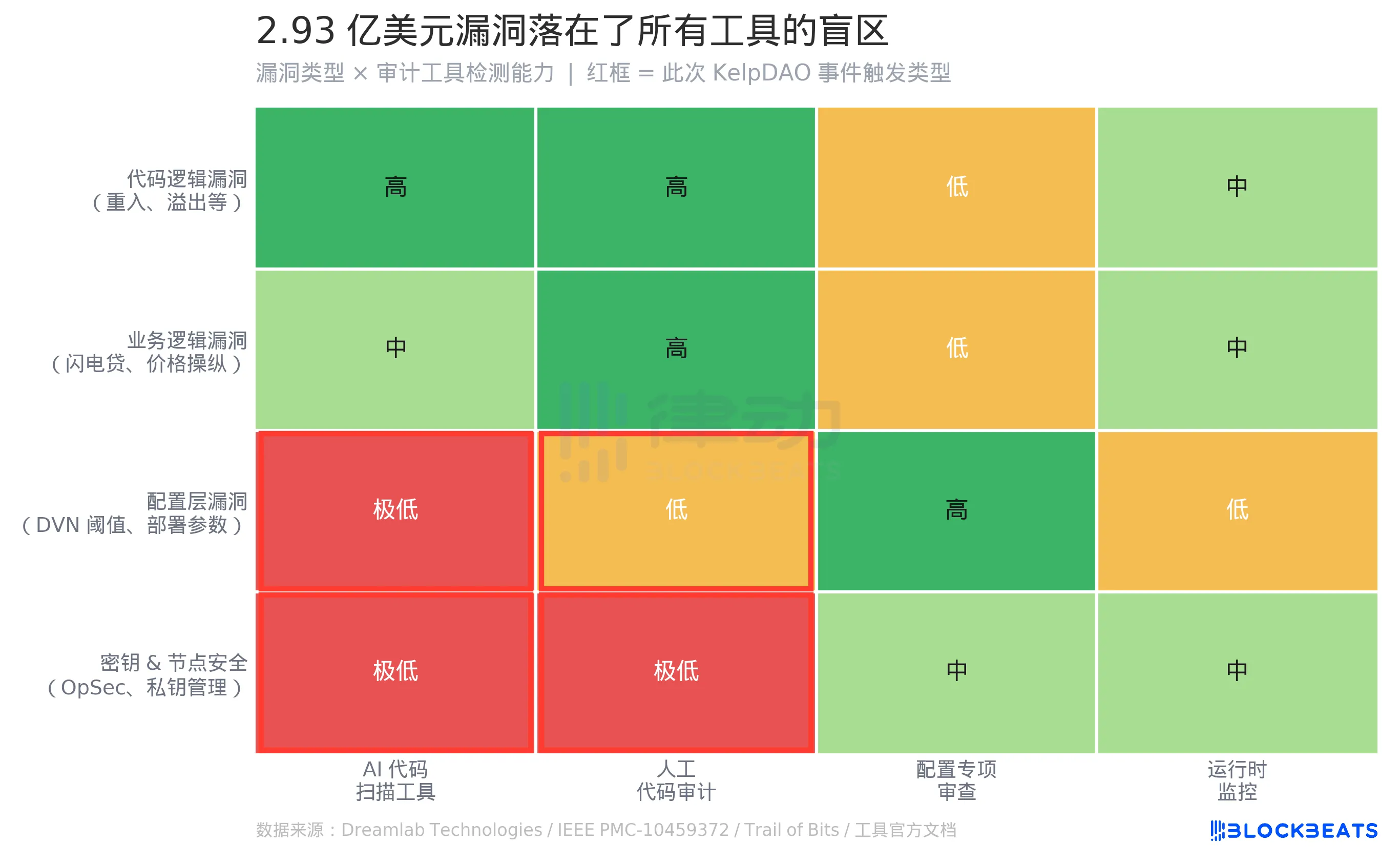
But there are two rows in this matrix that are red.
Configuration layer vulnerabilities belong to a structural blind spot in tool audits. The problem with Kelp DAO lies not in the .sol file but in a parameter written during protocol deployment—the DVN threshold. This parameter determines how many verification nodes need to confirm the cross-chain message before it is considered valid. It does not enter the code, it does not fall within the scanning range of Slither, nor does it enter the symbolic execution path of Mythril. According to comparative research by Dreamlab Technologies, Slither and Mythril detected 5/10 and 6/10 vulnerabilities, respectively, in the tested contracts, but these results are based on the premise that "vulnerabilities are in the code." According to research by the IEEE, even at the code level, existing tools can only detect 8%-20% of exploitable vulnerabilities.
From the perspective of existing audit paradigms, there is no tool that can "detect whether the DVN threshold is reasonable." To detect such configuration risks, what is needed is not a code analyzer but a specialized configuration checklist: "Is the number of DVN nodes used for the cross-chain protocol ≥ N?" "Is there a minimum threshold requirement?" These types of questions currently have no standardized tools covering them, and there are not even widely recognized industry standards.
Also in the red area are key and node security. @0xQuit's description mentions that the DVN node was "breached," which falls within the category of operational security (OpSec), beyond the detection capabilities of any static analysis tool. No leading auditing firm or AI scanning tool can predict whether a node operator's private key will be leaked.
This attack triggered two red areas in the matrix simultaneously.
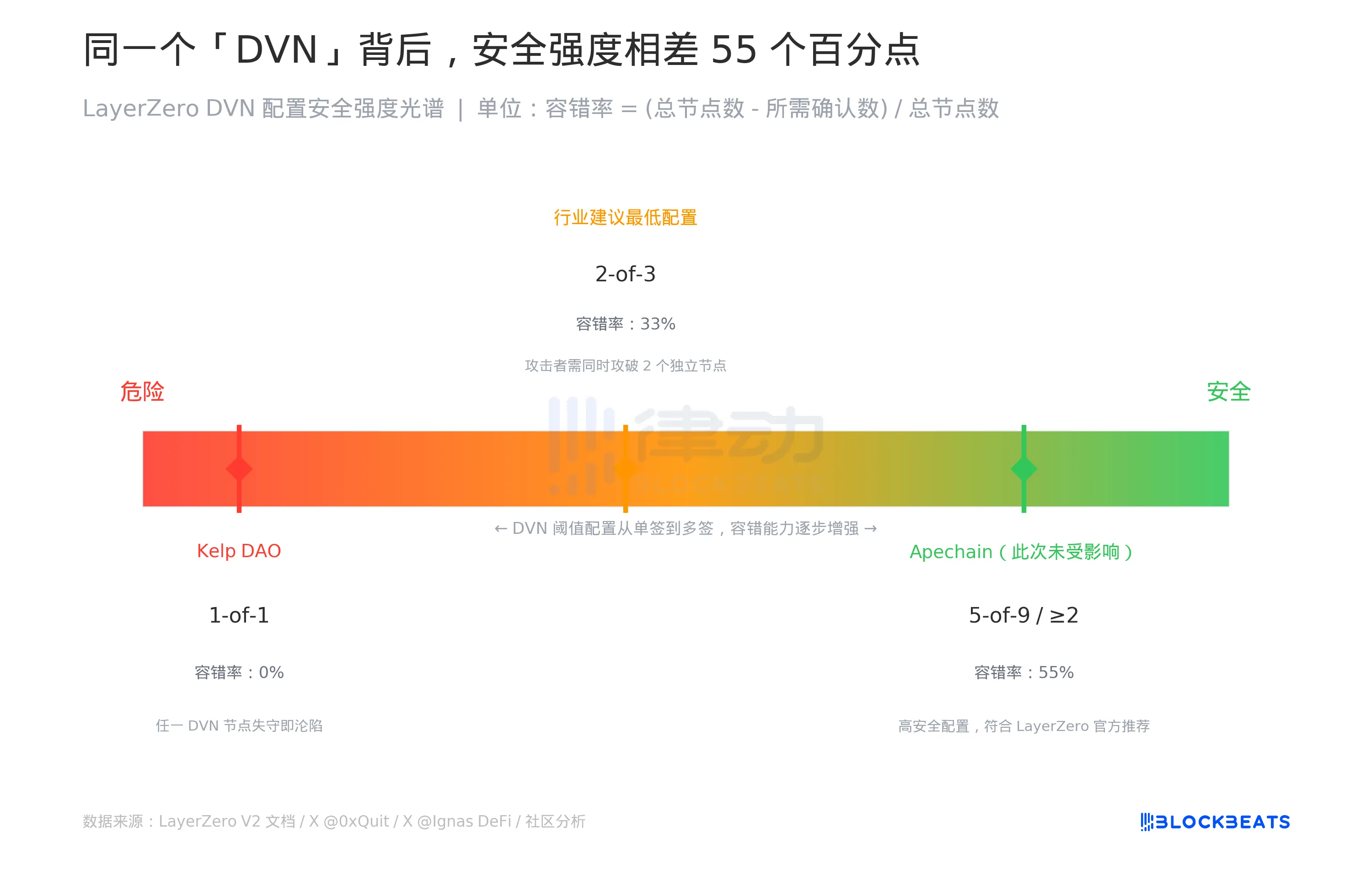
DVN is the cross-chain message verification mechanism of LayerZero V2, fully called Decentralized Verifier Network. Its design philosophy is to hand over security decision-making authority to the application layer: each protocol accessing LayerZero can choose how many DVN nodes need to confirm a cross-chain message before allowing it.
This "freedom" creates a spectrum.
Kelp DAO chose the leftmost end of the spectrum, 1-of-1, requiring only one DVN node to confirm. This means there is zero fault tolerance; an attacker only needs to breach that one node to forge any cross-chain message. In contrast, Apechain, which also accesses LayerZero but is configured with more than two required DVNs, was not affected in this incident. LayerZero's official wording in the statement was "all other applications remain secure," implying that safety depends on the configuration choice made.
The normal industry advice is at least 2-of-3; the attacker must breach two independent DVN nodes simultaneously to forge a message, increasing fault tolerance to 33%. High-security configurations like 5-of-9 can achieve a fault tolerance of 55%.
The problem is that external observers and users cannot see this configuration. Labeled as "supported by LayerZero," it could either mean 0% fault tolerance or 55% fault tolerance. Both are referred to as DVN in documentation.
Veteran crypto investor Dovey Wan, who has experienced the Anyswap incident, directly stated on X: "LayerZero's DVN is actually a 1/1 validator... all cross-chain bridges should immediately conduct a comprehensive security review."
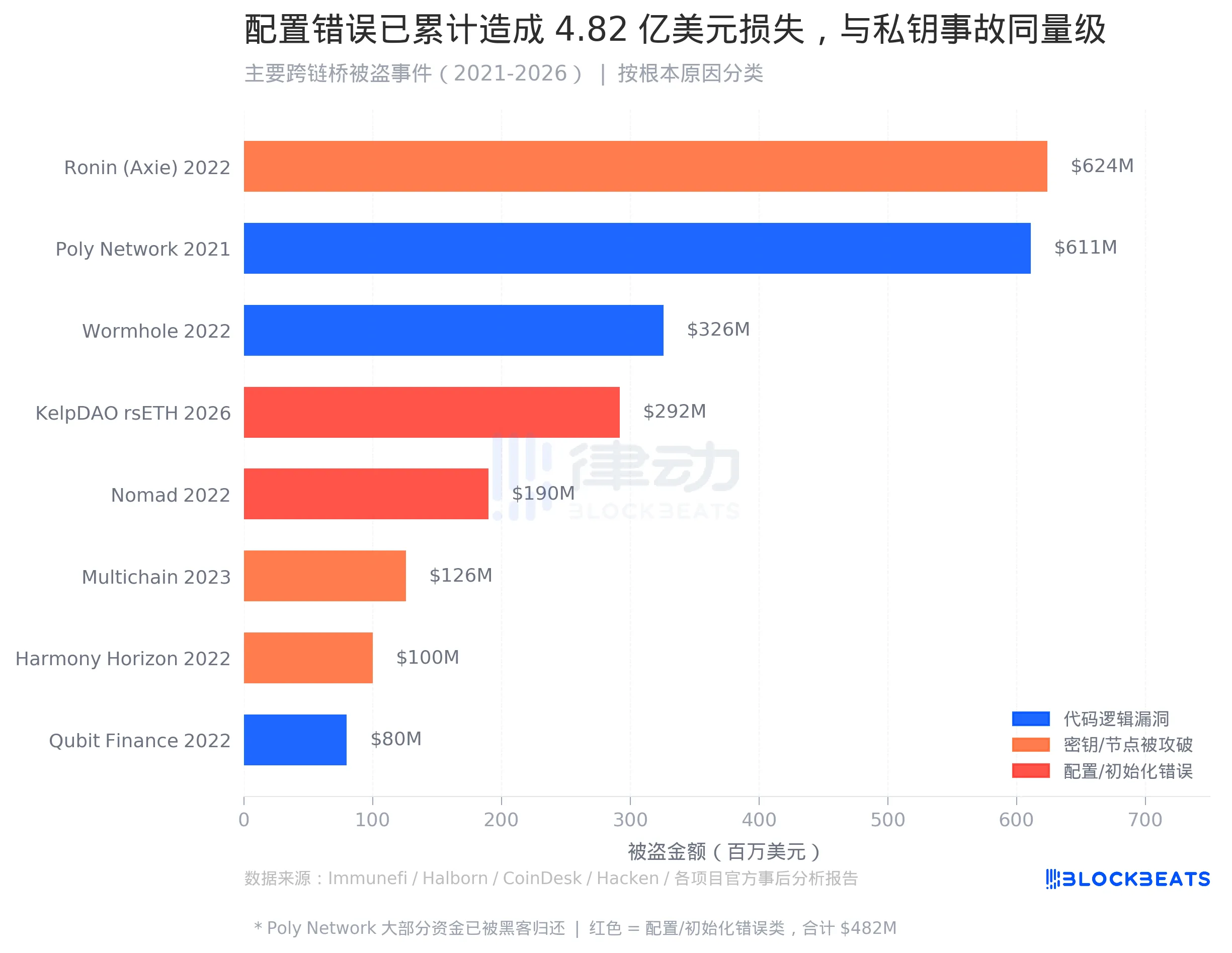
In August 2022, the Nomad cross-chain bridge was found to have a vulnerability. Someone duplicated the first attack transaction, made slight modifications, and found it was successful as well—hundreds of addresses then began replicating and, within a few hours, drained 190 million dollars.
The post-incident analysis of Nomad stated that the source of the vulnerability was "initializing the trusted root to 0x00 during a routine upgrade." This is a configuration error occurring during the deployment stage. The Merkle proof verification logic has no issues, and the code itself has no problems; the issue is that an initial value was filled incorrectly.
This time, combined with Nomad, configuration/initialization vulnerabilities have now caused approximately 482 million dollars in losses. In the entire history of cross-chain bridge thefts, this category's scale can now be matched alongside key leakage incidents (Ronin 624 million dollars, Harmony 100 million dollars, Multichain 126 million dollars, totaling about 850 million dollars).
However, the product design of the code auditing industry has never been aimed at this category.
The industry still primarily discusses code logic vulnerabilities. Wormhole lost 326 million dollars due to a signature verification bypass, and Qubit Finance lost 80 million dollars due to a false deposit incident. These cases have complete vulnerability analysis reports, have CVE numbers for comparison, and have reproducible PoCs, making them suitable for training and optimization of auditing tools. Configuration layer issues are not written in code, making them hard to enter this production cycle.
It is worth noting that the triggers for the two configuration incidents are entirely different. Nomad involved mistakenly filling in an incorrect initial value during a routine upgrade, categorized as a mistake. Kelp DAO's 1-of-1, however, is an active configuration choice—LayerZero does not prohibit this option, and Kelp DAO did not violate any protocol rules. A "compliant" configuration choice and a "mistake" in an initial value ultimately lead to the same outcome.
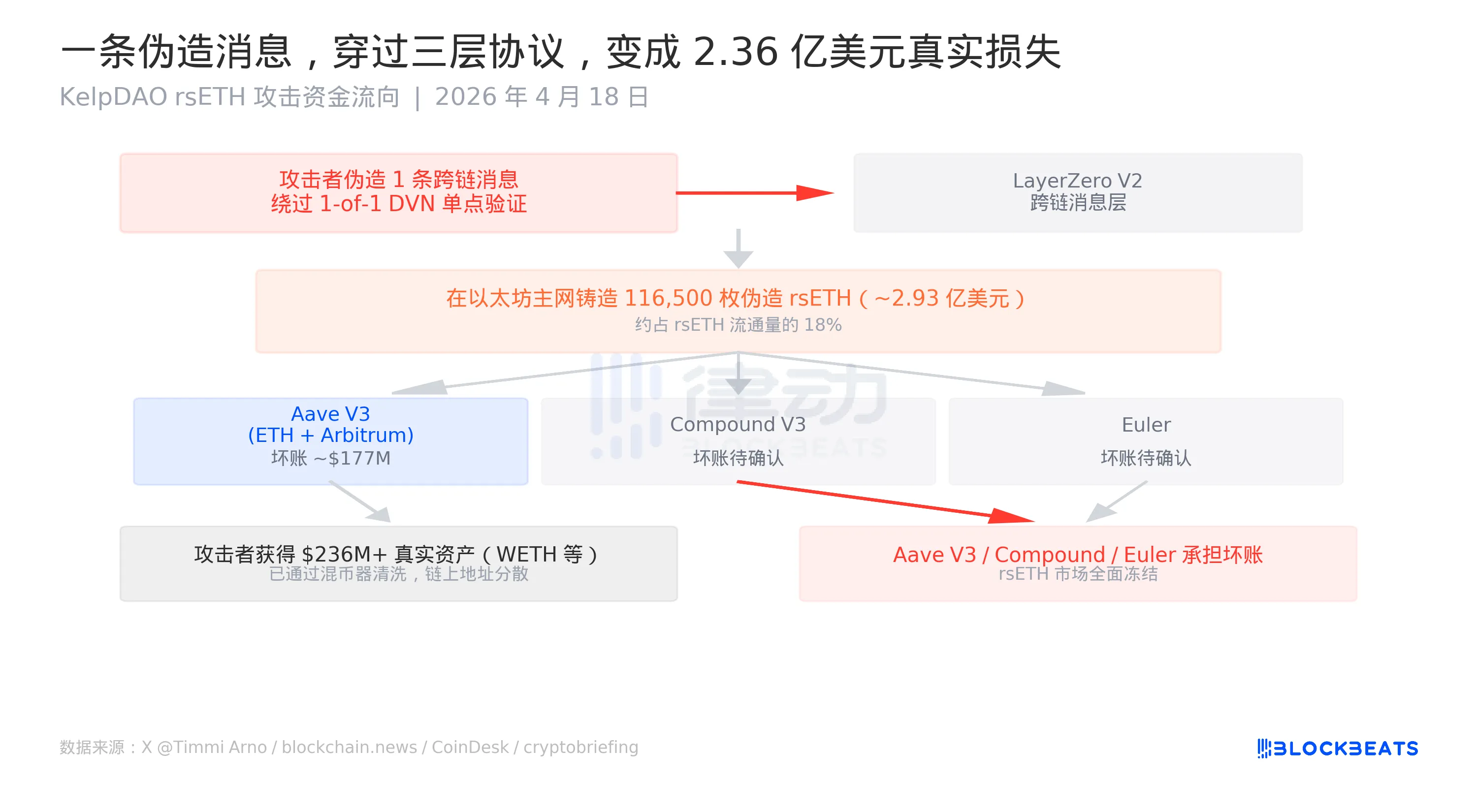
The execution logic of this attack is straightforward: a forged cross-chain message tells the Ethereum mainnet, "someone on another chain has locked equivalent assets," triggering the mainnet to mint rsETH. The minted rsETH has no actual backing, but its on-chain record is "valid," allowing it to be accepted as collateral by lending protocols.
The attacker then scattered 116,500 rsETH across Aave V3 (Ethereum and Arbitrum), Compound V3, and Euler, borrowing out a total of over 236 million dollars in real assets. According to multiple reports, Aave V3 alone faces an estimated bad debt of about 177 million dollars. Aave's security module Umbrella can absorb a bad debt WETH reserve of about 50 million dollars, covering less than 30%, with the remainder to be borne by aWETH stakers.
The bill ultimately fell on those who just wanted to earn some WETH interest.
As of the time of publication, LayerZero officials are still investigating in conjunction with the security emergency response organization SEAL Org, and stated that they will jointly publish a post-incident analysis report with Kelp DAO after obtaining all the information. Kelp DAO has stated they are conducting "proactive remediation."
The 293 million dollar vulnerability is not in the code. The phrase "audit passed" does not cover the location of that parameter.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



