Written by: Vladimir S.
Translated by: Saoirse, Foresight News
In the first three months of 2026, I did something that most people in the crypto circle are unwilling to do: I read through all the significant security incident reviews, on-chain evidence reports, and leaked Discord chat records from this year. There were a total of 47 incidents with over $3.8 billion in assets disappearing. But in these cases, not one involved a so-called "genius-level zero-day smart contract vulnerability attack."
Each time, the funds were transferred out the front door — because someone opened the door.
Everyone blames the code, but I blame the people. Below are the ironclad evidence from the 47 cases...
I categorized them by the type of breach, and the patterns were obvious. No nonsense, only brutal truths:

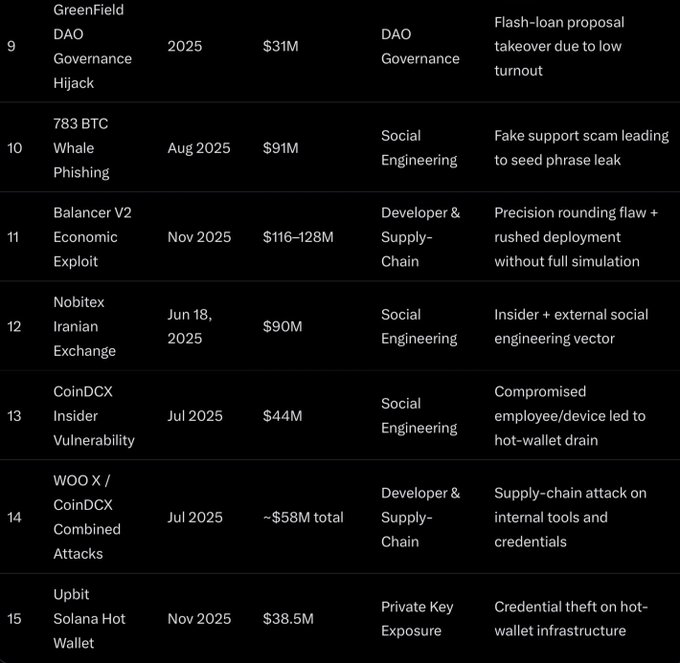
Overview of the Other 32 Incidents
- Social engineering attacks (13 new cases): Approximately $620 million in total, mainly involving whale phishing, deep fake voice scams, and Telegram "official development support" scams, averaging losses of $35 million to $40 million per incident.
- Developer and supply chain security (8 new cases): Approximately $480 million in total, including backdoor implants in npm/PyPI packages, malicious TestFlight applications, and developer computers being compromised.
- Private key and credential leaks (5 new cases): Approximately $310 million in total, including mnemonic phrase leaks, keys stored in the cloud, and weak 2FA being bypassed.
- DAO governance hijacking and flash loan attacks (6 new cases): Approximately $150 million in total, leveraging token-weighted voting vulnerabilities and low voter turnout proposals to conduct attacks.
Social Engineering Attacks Targeting Privileged Individuals (19 cases, losses over $1.2 billion)
This category far out ahead. The attackers didn’t need to crack algorithms; they breached trust in people.
- Drift Protocol (April 1, 2026, $285 million): North Korean hacker group UNC4736 spent six months gaining the trust of multisig signers and administrators. They forged LinkedIn profiles, conducted fake recruitment, and gradually infiltrated permissions. After forging collateral and obtaining permission from 2 out of 5 multisig signers, they emptied the treasury in a matter of minutes. The code was not hacked; it was the people who were compromised.
- Coinbase customer service contractor bribery (May 2025, estimated impact $400 million): Overseas insiders casually leaked user account data.
- 783 Bitcoin whale phishing (August 2025, $91 million): Victims thought they were communicating with "official customer service" of a hardware wallet and disclosed their mnemonic phrases in encrypted chats.
Developer and Supply Chain Intrusions (11 cases, losses over $1.7 billion)
The so-called "secure" wallet infrastructure only depends on the laptop that the developer used at 2 a.m.
- Bybit cold wallet theft (February 2025, $1.5 billion): Lazarus Group compromised a Safe{Wallet} developer's device and used it to authorize a significant transfer. One device, one person, led directly to a collapse.
- Phemex hot wallet (January 2025, $85 million): Following targeted phishing, unauthorized access occurred to the internal system.
Private Key and Credential Leaks (9 cases, losses over $650 million)
It's 2026, and these things are still happening. Really.
- DMM Bitcoin (2024 legacy forensic case, $305 million): A classic private key leak case, still used by analysts as a template for exchange thefts in 2025–2026.
DAO Governance Hijacks and Flash Loans (8 cases, losses over $220 million)
Low voter turnout + token-weighted voting = anyone with a few million liquidity can pick up money for free.
- GreenField DAO (2025, $31 million): A single block flash loan governance attack.
- UPCX Protocol (2025, $70 million): Typical proposal takeover attack.
The amounts in the remaining cases are smaller, but the methods are exactly the same: buy low votes, empty the treasury, people disappear.
All victims, without exception, made the same fatal mistake: they took manual approval as a reliable security boundary.
In each case, there was one person (or a small group of people) whose decision served as the ultimate checkpoint. There was no technical enforcement of verification, no forced transaction simulation, no real-time identity verification, no time delays. Only one sentence: "Trust me, I am the signer."
This is the only single point of failure. It’s not the code; it’s the people in the chain.
Seven-Layer Operational Security Defense System
I am not just advocating this scheme theoretically; I have practically applied it in the security protection efforts of two eight-digit scale funds. The complete system below is sufficient to prevent any of the 47 security incidents mentioned above:
1. Air-gapped devices + MPC multi-signature
Never store mnemonic phrases on hot devices. Use hardware wallets or multi-party computation wallets to ensure that no one can see the complete key alone.
Air-gapped signing means that the final signature is completed on hardware that has never been connected to the internet. MPC takes it further: keys never fully appear in the same place. Key shards are distributed across multiple devices/multiple people; valid signatures can only be generated when a threshold is reached. Use MPC for hot operations, large fund transfers use air-gapped cold storage, and set rules on speed limits and whitelists within the MPC engine, so even if one shard leaks, the system will still intercept.
2. Cross-regional distributed multi-signature + high thresholds
At least adopt a 3/5 model, with signers distributed across different continents, devices, and time zones. Reject the 2/3 "everybody knows each other" weak setup.
Even if attackers social engineer two signers, they still need a third signer from a different time zone, who may be sleeping or offline. Rotate signatories every quarter, enforce the use of hardware keys, and never use 2/3.
3. Mandatory transaction simulation and preview
Every signature must be fully rehearsed in a sandbox, clearly showing what will happen on-chain. Blind signing is forbidden.
If the simulation results do not fully align with expectations, the transaction is aborted.
4. Real-time identity verification + challenge-response validation
Significant transactions must involve a real-time video call, paired with pre-shared secret phrases or real-time display of random numbers on-chain. Deep fakes are rendered ineffective here.
Pre-arranged calls and recorded audit trails can use tools like Signal.
5. Time locks + delayed execution
Transactions over $500,000 enter a 48–72 hour time lock queue, which is publicly verifiable and supports emergency pauses.
This allows the team time to respond to anomalies, blocking many flash loan governance attacks and hurried authorizations from being stolen.
6. Automated anomaly monitoring + emergency shutoff switch
On-chain and off-chain alerts for anomalous behavior from signers, IP changes, and transaction patterns. Freeze the entire treasury with one click.
Set a transaction that requires multi-signature to trigger, for pausing the treasury or initiating emergency recovery.
7. Quarterly red team drills + failure switches
Hire white hat hackers to perform social engineering tests on the team. If a core signer goes missing for 30 days, assets are automatically transferred to a recovery multisig address.
Red team drills can uncover human vulnerabilities missed by audits, and failure switches can address scenarios like "founders running away with the keys."
Drift Protocol Hacking Incident: Why Military-Grade Operational Security Systems Must Be Adopted
In April 2026, the North Korean state-sponsored hacking group UNC4736 spent six months fabricating identities, fake recruitment, and gradually gaining the trust of Drift’s multisig administrators, ultimately stealing $285 million. They didn’t breach any code; they compromised the "human trust layer" that all projects still rely on.
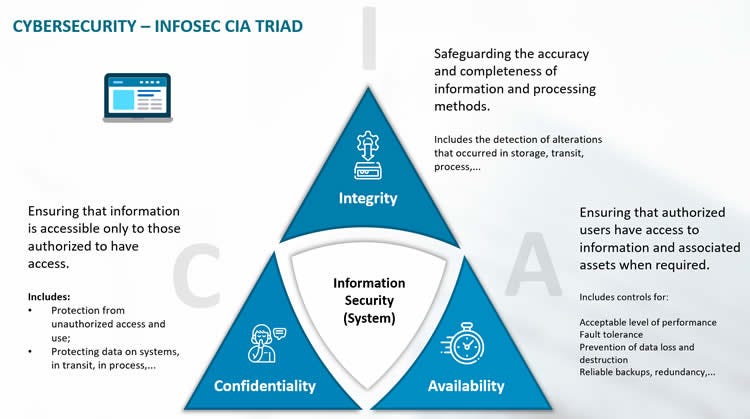
This incident illustrates a reality: once a state-level force sets its sights on your funds, civilian-level security is completely inadequate. Projects must adopt genuine military-grade operational security, grounded in the zero-trust philosophy of "never trust, always verify," and implement based on the three core security principles of confidentiality, integrity, and availability.
Every critical operation must have an aviation-grade checklist: mandatory simulation, real-time verification, independent review, and adherence to a "default assumed compromised" mindset. Failing to meet this standard is merely waiting for the next state-level hacker to walk in through the front door.
Why Project Teams Need a Dedicated Internal Security Officer
Projects that survive into 2026 are not just spending money on audits; they are hiring full-time internal security officers whose sole responsibility is internal operational security and emergency response.
This is not a part-time developer or a team member who is casually overseeing security. This person must be familiar with all reputable audit firms, on-chain tracing teams, and white hat emergency groups, knowing whom to contact first in case of an incident.
In traditional industries, security officers often come from military or specialized forces backgrounds due to their emergency muscle memory. The crypto industry is no different — it needs someone deeply involved in the on-chain world, capable of coordinating multisig freezes at 3 a.m., and synchronizing notifications to security agencies.
Without such a core responsible person, even the most perfect seven-layer system will collapse under real pressure in an instant.
Resolv Labs Incident: Detection Alone Is Not Enough
The Resolv Labs review released in early April 2026 is a typical case among the 47 incidents involving supply chain and infrastructure breaches.
The attackers accessed the system through GitHub permissions left by outsourced staff, horizontally infiltrated cloud facilities, altered signing policies, minted 80 million unauthorized tokens, and stole approximately $25 million ETH.
Although real-time monitoring flagged anomalous transactions, the team took over an hour to begin remediation.
This is why there must be a dedicated security officer: they can dial emergency and forensic teams with one click, and emergency procedures have long been trained into muscle memory.
Why Every Project Needs a Bug Bounty, Continuous Auditing, and Audit Competitions
Smart teams view security investment as insurance: no return is visible during regular times, but it saves lives when incidents occur.
The mentality of "we have already audited once" is the root of the losses of billions from the 47 projects.
It must be done:
- Maintain an open and adequately funded bug bounty program (minimum $50,000–$250,000 based on TVL);
- Audit before every update goes live;
- Hold at least one audit competition every quarter.
A significant hacking incident can directly destroy a project. Only by treating security as a continuously quantifiable cost, rather than a one-time checkbox task, can one survive.
Personal Security Recommendations
No matter how strong the seven layers of protection at the protocol level, it cannot stop your own computer or phone from becoming a weak link.
- Windows/Linux devices: Install Malwarebytes + professional EDR endpoint protection;
- iPhone: Enable lock mode, install iVerify to check for spyware and zero-click vulnerabilities;
- Mac: It is recommended to use S1, ensure that the new Apple chip has FileVault enabled, disable AirPlay if not in use, and set a password for the screensaver.
For all operations involving keys or signatures, use a dedicated "clean" MacBook: never sign into iCloud, avoid casual internet browsing, reinstall the system quarterly, and keep it in a Faraday bag when not in use. Overlay enterprise-level DLP data loss prevention and lightweight SIEM log alerts.
You may directly use the OpSec minimum checklist from Trail of Bits.
Personal security is the last line of defense. Once the attacker reaches you, there is no pause button.
Core Viewpoints
This system is not just theory. I have used it to stress-test against the pressures of current top hacking attacks, proving it to be effective.
The security of smart contracts is improving year by year, but human security awareness has not progressed in tandem. In 2026, if you are still operating protocols, DAOs, or large personal wallets, and still relying on phrases like "the team is trustworthy" or "the contract has been audited," it indicates that your vigilance is far from sufficient.
The next one to be attacked could be you.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



