On March 20, 2026, at 8 AM UTC, the UXLINK attacker's wallet, which had been silent for nine months, suddenly made a large-scale move, selling off 5,496 ETH within about one hour in exchange for approximately 12.3 million DAI. This batch of chips, estimated at current prices, accounts for about 13% of the total assets stolen during the multi-signature vulnerability attack in 2025, bringing a case that was already considered "old" back into the spotlight. From the theft of over 44 million USD on September 22, 2025, to the hacker choosing to liquidate in a concentrated manner now, the delay between the stolen funds and the secondary market is evolving into a new confrontation about liquidity absorption capability, investor sentiment resilience, and the hacker's game rhythm.
The wallet awakens to sell after nine months
Returning to the starting point, on September 22, 2025, UXLINK suffered a severe vulnerability in its multi-signature mechanism, resulting in the attackers stealing over 44 million USD in assets all at once. This incident was rated as one of the top ten security events of 2025 by several security agencies and media, not only due to the enormous loss but also because it occurred on what was regarded as a "security-enhanced" multi-signature wallet, directly impacting the project's and users' trust in multi-signature solutions and prompting a new round of reflection in the industry regarding multi-signature permission management, operational processes, and audit standards.
After that, the core hacker address related to the UXLINK attack maintained a long "playing dead" state on-chain. Apart from a small amount of exploratory transfers, the main address saw almost no significant activity over the subsequent approximately nine months, gradually fading from the daily public discourse. This long period of silence reduced the sensitivity of on-chain monitoring around that address, while also providing operational space for the attackers to strike at a later time. Until March 20, 2026, this apparent calm was suddenly broken, large-scale ETH sales occurred densely in a short period, announcing that this batch of sleeping chips officially began to exert substantive pressure on the market.
Why did the attackers choose to activate the wallet and liquidate in concentration at this time? It is difficult for outsiders to grasp their subjective intent, but reasonable inferences can be made from environmental and game-theoretic perspectives. First, from a time dimension, a nine-month gap is enough for some trading counterparts and on-chain observers to become "fatigued," leading to a decrease in monitoring frequency; second, in terms of market environment, under the backdrop of ETH volatility and derivative sentiment being bearish, hackers may have judged that even if it caused short-term price shocks, it would be easier to integrate funds smoothly into the already tumultuous market noise; third, on compliance and risk control levels, inactivity for a long time might reduce the real-time alert level of certain platforms and tools to that address, creating a relatively favorable window for them to disperse paths and process funds in batches.
An on-chain impact of selling 5,496 ETH within one hour
In this concentrated liquidation, the pace and path themselves constituted a clear narrative. According to on-chain data, this round of selling was highly concentrated and completed within one hour, exhibiting evident characteristics of segmented trading: the attackers did not sell everything at once but continuously pressured the market through multiple large transactions, attempting to find a relative balance between speed and slippage. The Onchain Lens monitoring report indicated that the abnormal transactions mainly concentrated between UTC time 03:00-04:00, which, while not the highest activity period, still had a certain level of liquidity, thus reducing the probability of being instantly intercepted and hunted.
In terms of specific impact, Onchain Lens pointed out that the attackers concentrated their ETH to exchange for DAI, which led to a related ETH/DAI trading pair instantaneous slippage expanding to 1.8%. For mainstream assets, a temporary slippage approaching 2% clearly deviated from the stable range of daily large transactions, indicating that the available depth in the corresponding pools was difficult to completely absorb this level of selling pressure. Especially under continuous segmented selling, buyers needed to continuously raise prices to absorb it, creating pressure on market-making funds and systematic liquidity in a short period.
From a broader liquidity perspective, what equivalent amounts of selling pressure mean for the on-chain ecosystem depends on the distribution structure of funds and the overall market sentiment at that time. When the selling concentrates on on-chain AMMs or aggregated routes rather than a single order book, price shocks will be partially diluted across multiple pools and paths, but spillover effects will still exist. Long-tail trading pairs with insufficient depth may be forced into passive repricing, and other asset pools associated with ETH may also experience linkage due to the opening of arbitrage paths, turning a sale originally limited to a single asset into a cross-pair chain reaction. This kind of “gradual release” impact might not be immediately reflected in a single large bearish candlestick but will embed longer-term price and liquidity distortions.
How hackers avoid tracking after cashing out DAI
It is noteworthy that after completing this round of operations, the attackers chose to unify all the sold ETH into approximately 12.3 million DAI, rather than diversifying into multiple assets or directly entering centralized platforms. From an anti-money laundering and tracking perspective, this choice has both advantages and disadvantages: on one hand, DAI, as a commonly used on-chain valuation and settlement asset, is liquid, with numerous trading paths. Converting stolen funds into DAI could further split and obscure fund flows later through multiple protocols, multi-chain bridges, and various DeFi scenarios; on the other hand, converting into a single asset also delineates the hacker's fund "contours" clearly on-chain, providing security teams with a means to lock in the scale of funds and core addresses in the early stages.
PeckShield analysts pointed out that attackers "might use mixers to process part of the DAI" in subsequent steps and reminded that continuous tracking of related on-chain traces is necessary. The basic principle of mixers is to mix funds from multiple parties, then redistribute them according to certain rules, attempting to cut the visible paths between the original fund flow and the final landing point. However, the effectiveness of this tool is subject to multiple limitations: when large amounts of funds enter a concentrated mixing pool, the statistical "uniqueness" may still be identifiable; some mixing services are themselves under regulatory and sanction pressures, and relevant addresses have already been widely labeled; while excessively frequent and patterned splitting behaviors may also become signals for on-chain analysis tools.
In this context, the work focus of on-chain security teams often lies in tracking the fund splitting paths and time characteristics over a longer time dimension. By examining the rhythms of DAI flowing from the hacker's main address to various transit wallets, in combination with transaction sizes and types of interaction contracts, a multi-layered funding "tree diagram" can gradually be outlined. When one of these branches ultimately touches compliance platforms, OTC liquidity entry points, or known high-risk services, it provides a basis for further freezing, investigation, or early warning. Regarding the UXLINK case, although the attacker’s concentrated liquidation improved short-term profit efficiency, it also left an extremely clear "time scale" on-chain, providing crucial anchor points for subsequent tracking.
ETH options market amplifies bearish sentiment
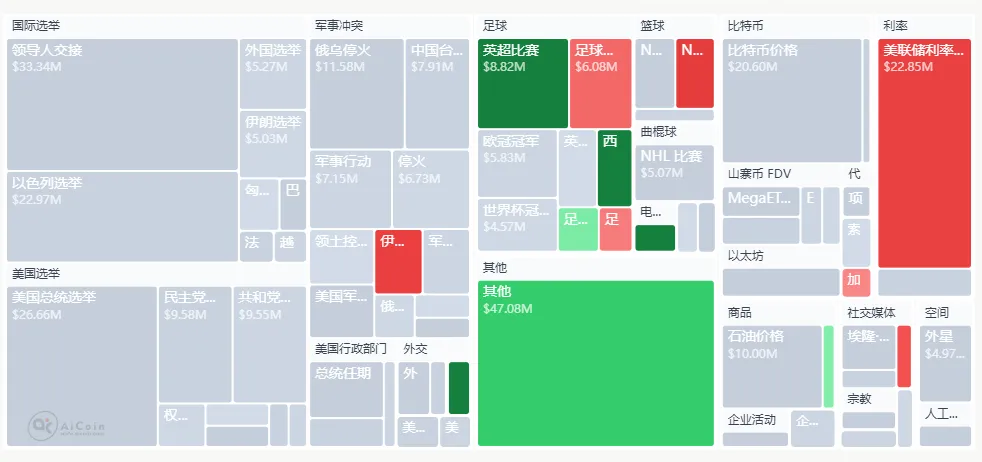
Concurrent with the on-chain selling was the sentiment already displayed in the derivatives market. According to Deribit data, the proportion of put contracts in the recent ETH options market has risen to 63%, reflecting that institutions and professional traders are overall more willing to pay for hedging against downside risks. Under such circumstances, the concentrated selling event by the UXLINK hacker could easily be absorbed by the market narrative as "new negative evidence," reinforcing the consensus on ETH being under short-term pressure.
It is important to distinguish that such hacker selling might not be a single price-driven factor but often becomes a catalyst for bearish narratives: on the spot layer, it directly squeezes liquidity through actual selling pressure; on the sentiment level, it symbolically stimulates investors' associations with potential selling pressure by suggesting “the old case is not resolved, and chips are still on the way”; on the derivatives layer, short sellers can leverage such news to reinforce their position logic, embedding what should belong to a case-specific volume and price fluctuation into a broader downtrend story.
In short-term structural terms, a self-reinforcing expectation cycle can easily form between spot selling pressure and bearish positions in derivatives: hacker dumping → ETH under short-term pressure → further rise in demand for put options, increased implied volatility → bullish traders reduce positions or remain observant due to cost and risk considerations → thickness of spot buying pressure decreases → even small-scale selling pressures later can cause larger fluctuations. As long as this cycle is not interrupted by new funds or significant positive news, the market will maintain a cautious or even excessively defensive posture amid uncertainties of “whether there will be another batch of stolen chips being dumped.”
How centralized exchanges face hacker fund pressure
From the trading path perspective, this large-scale dump mainly occurred on-chain, with the attackers choosing to directly exchange ETH for DAI rather than heavily impacting the order books of any one centralized exchange. This is distinctly different from traditional hackers quickly depositing stolen coins into exchanges and swallowing buy orders in concentrated depths, and it also alters how regulatory and risk control issues may present themselves. If large amounts of funds flow directly to centralized platforms, the platform’s KYC, address blacklists, and monitoring of abnormal behavior usually form the first line of defense: known risk addresses are mostly blacklisted, and any deposit could trigger a freeze; even through dispersed transfers, multiple highly similar on-chain transfer records may be classified and analyzed by risk control systems, becoming primary targets for manual review.
In contrast, the on-chain path of exchanging ETH for DAI leaves more price impact within the DeFi ecosystem, while the direct shock to centralized exchanges is relatively limited. However, this "skirting around CEX doors" strategy does not mean platforms can rest easy: once these DAI or any subsequent split assets ultimately attempt to intersect with an exchange through deposits, OTC channels, or fiat inflows/outflows, the platform must make difficult trade-offs between compliance and user experience. On one hand, in cooperation with regulatory and industry self-discipline, they require a heightened sensitivity towards funds related to the UXLINK attack, potentially pre-setting filtering strategies based on on-chain monitoring agency prompts; on the other hand, overly aggressive freezes and restrictions may unintentionally "catch" ordinary users unaware, eroding trust in the platform.
Therefore, the pressures faced by major platforms when dealing with assets related to the UXLINK attack come not only from external compliance and law enforcement cooperation requirements but also from internal consistency in risk control and difficulties in user communication. Balancing respect for facts, user protection, and maintaining overall industry security will test the platform's ability to absorb on-chain intelligence and its tiered disposal mechanisms for suspicious funds. This also highlights a reality: even if the starting point of the attack behavior is on-chain, the endpoint often cannot bypass centralized entrances, as the roles of CEX and DeFi in the security ecosystem have become highly coupled.
From top security events to the extension of long-term shadows
From a longer-term perspective, the UXLINK multi-signature vulnerability incident is considered one of the top ten security events of 2025 not only due to the astonishing amount of losses, but also because it revealed systematic shortcomings in the entire industry regarding sections that were thought to be "secure." Following this incident, project teams have reevaluated their trust boundaries regarding the distribution of multi-signature permissions, signer management, emergency plans, and third-party audits, pushing security practices from "merely passing audits" towards "continuous governance and drills."
However, this hacker selling again reminds the market that the impact of an attack extends far beyond the days immediately following the news, and prolonged lurking of stolen funds on-chain waiting for opportunities to be liquidated in batches poses a chronic threat to the market that is often more insidious and persistent. Every time old case chips awaken, they will challenge the limits of market liquidity absorption with actual selling pressure and amplified panic; meanwhile, psychologically for investors, the cognition of "the hacker is still in the market" will be a long-term factor affecting valuation discounts and risk premiums. This shadow will not automatically dissipate with a single risk control announcement or the marking of an individual wallet; it requires the combined actions of time, technology, and system to gradually dilute.
Looking forward, as on-chain monitoring tools continue to evolve, the response speed of project teams and security organizations in identifying fund movements from old cases is expected to significantly increase: finer-grained funding mappings, smarter abnormal path identifications, and interactions with exchange risk control systems may allow the aftershocks of similar UXLINK old cases to be exposed earlier and digested more quickly by the market, thus transforming one-off explosive events into predictable and manageable risk release curves. Meanwhile, the investments of project teams in security infrastructure—from contract design and multi-signature architecture to emergency responses and user compensation mechanisms—will also determine the “half-life” of similar events in terms of public opinion and price.
The resurgence of the UXLINK old case is not just a story about a hacker address and 5,496 ETH, but serves as a reminder to the entire industry: the life line of security events is far longer than imagined, and the true endpoint lies not in the moment an attack occurs, but before the last stolen chip leaves the market.
Join our community to discuss and grow stronger together!
Official Telegram community: https://t.me/aicoincn
AiCoin Chinese Twitter: https://x.com/AiCoinzh
OKX welfare group: https://aicoin.com/link/chat?cid=l61eM4owQ
Binance welfare group: https://aicoin.com/link/chat?cid=ynr7d1P6Z
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。