Author: Chain Analysis Crypto Laboratory
I. Event Background: Oracle Configuration Lays Hidden Dangers
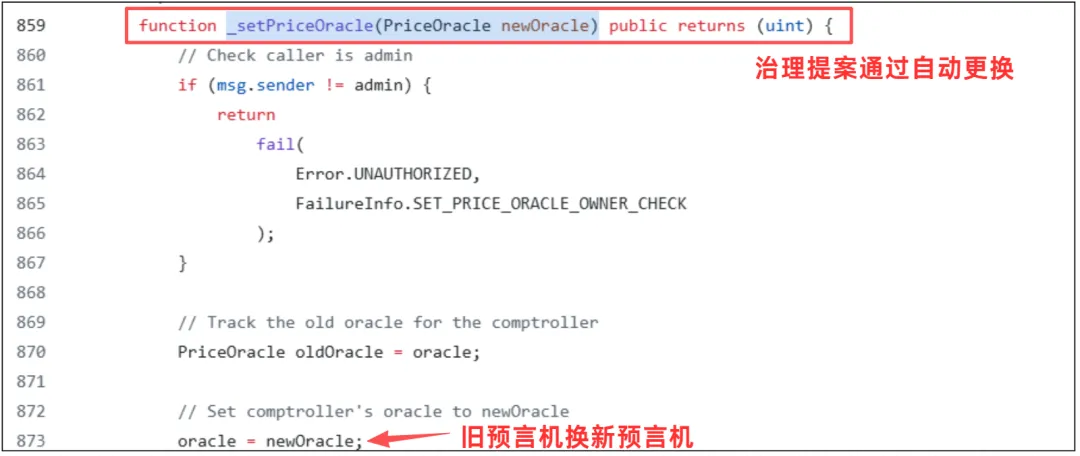
The reason for the attack began with a governance proposal (MIP-X43), which enabled a new Chainlink oracle configuration on the Moonwell market of the Base and Optimism networks. (Note: An oracle is a tool for obtaining real-time data before data is submitted to the blockchain.)
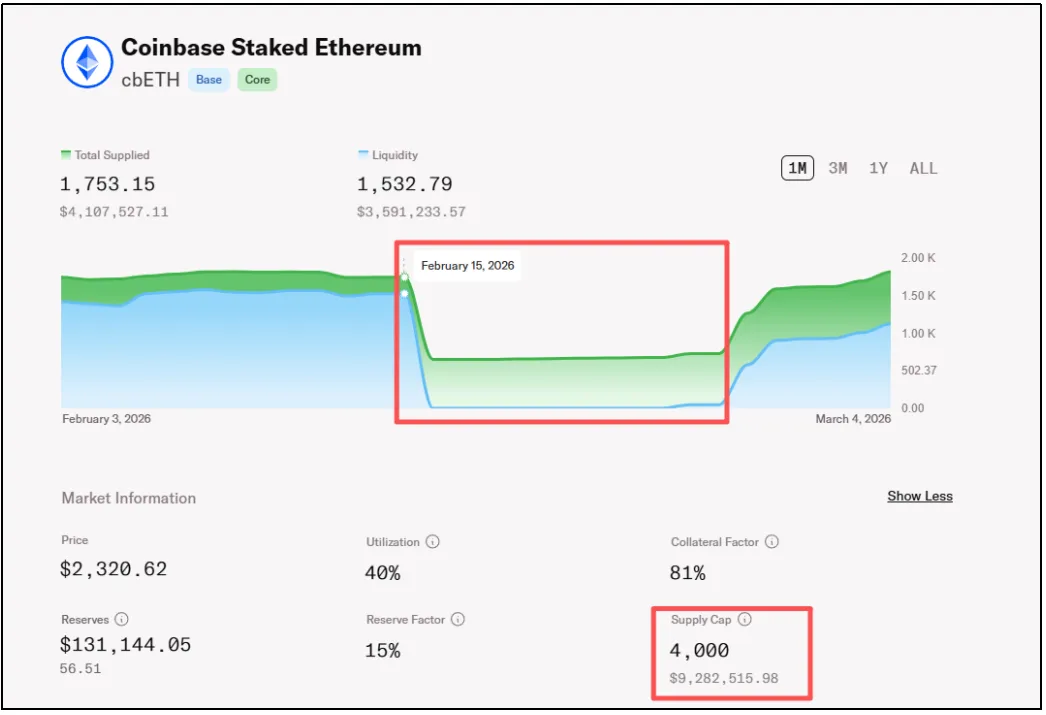
In lending protocols like Moonwell, users can deposit assets such as cbETH as collateral to borrow other tokens. If the market declines and the collateral value decreases, the collateral value debt will lead to automatic liquidation of positions by bots (users can use the total amount of their funds), repaying the debt and seizing the collateral at a discounted price.
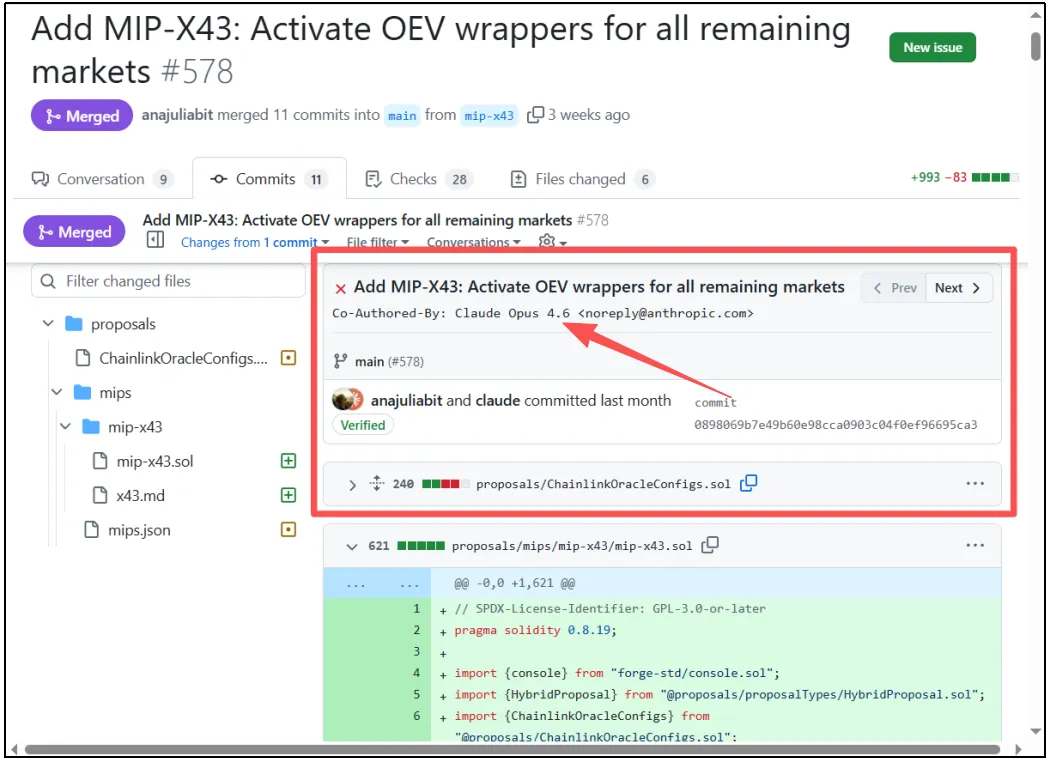
Before the incident, the cbETH market in Moonwell had ample funds and collateral, but the oracle testing was insufficient, missing a crucial multiplication step, leading to severe price errors and a sharp increase in risks.
II. Event Analysis: AI Wrote Incorrect Code
This incident is the first on-chain security accident triggered by Vibe Coding (AI-assisted coding) in the industry; its core is a low-level yet fatal oracle configuration flaw.
1. Cause of the Flaw
The root of this accident lies in the incorrect pricing of the cbETH asset by the oracle. cbETH is a highly liquid staking token, and its value includes accumulated staking rewards. Under normal circumstances, 1 cbETH is approximately worth 1.12 ETH.

Therefore, the correct dollar price calculation logic should be:
Dollar price of cbETH = (Exchange rate of cbETH to ETH) × (Dollar price of ETH)
For example: Assuming 1 cbETH ≈ 1.12 ETH, and 1 ETH ≈ 2200 dollars, then the real value of 1 cbETH should be 2464 dollars.
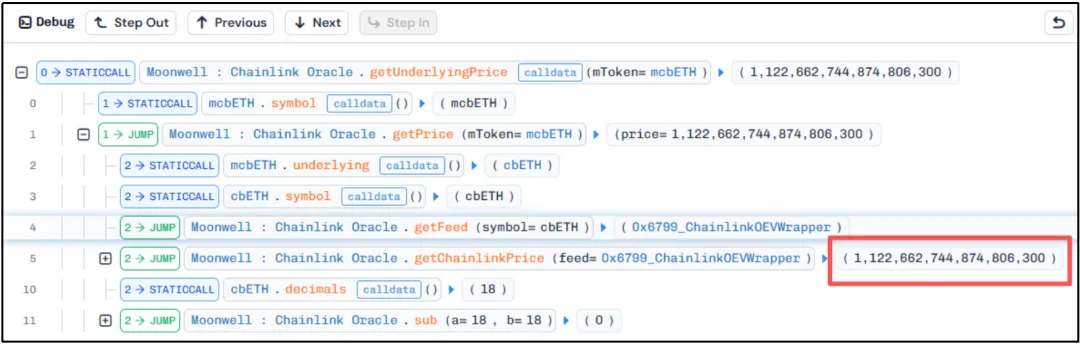
However, in the code generated by the AI tool Claude, due to a lack of comprehensive logical checks, the price source of cbETH was mistakenly pointed directly to cbETHETH_ORACLE. This data source could only provide the "exchange rate" (i.e., 1.12) between cbETH and ETH but could not retrieve the dollar price of ETH.
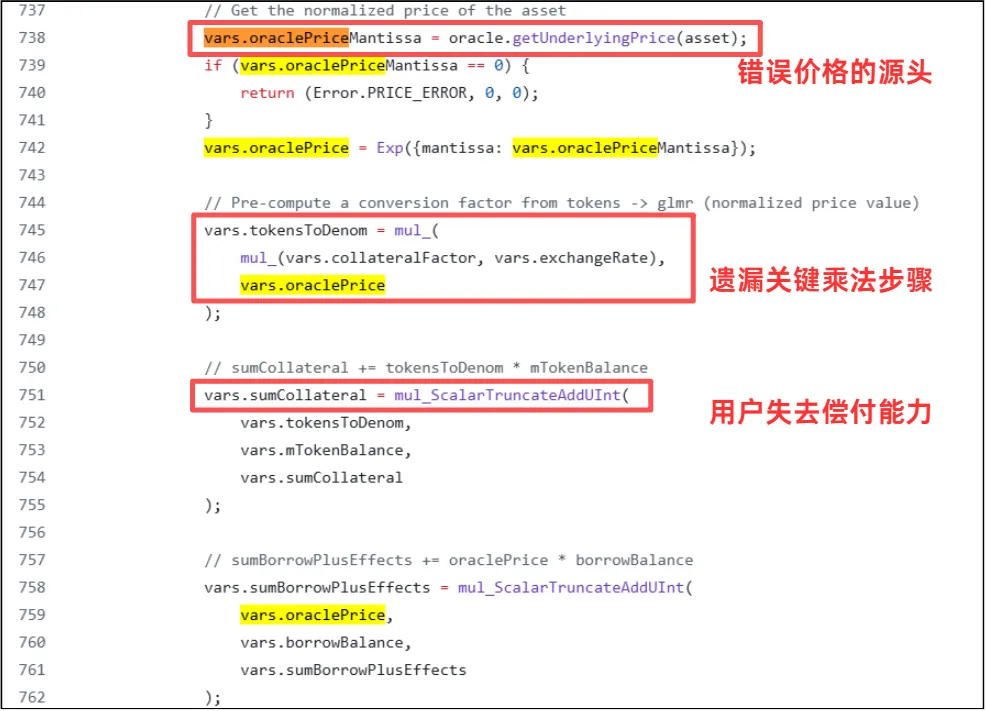
This error, which omitted a crucial multiplication step, caused the program to interpret the "exchange rate" as the "dollar value." An asset originally valued at over 2400 dollars was incorrectly marked in the system as 1.12 dollars, severely underestimating it by over 99.9%, with a price difference of nearly 2000 times.
2. Attack Restoration
The severe undervaluation of the assets by the system directly led to a large number of normal users' collateral positions being misjudged as "insolvent" by the system. The entire exploit process was extremely efficient, showing obvious automated characteristics:
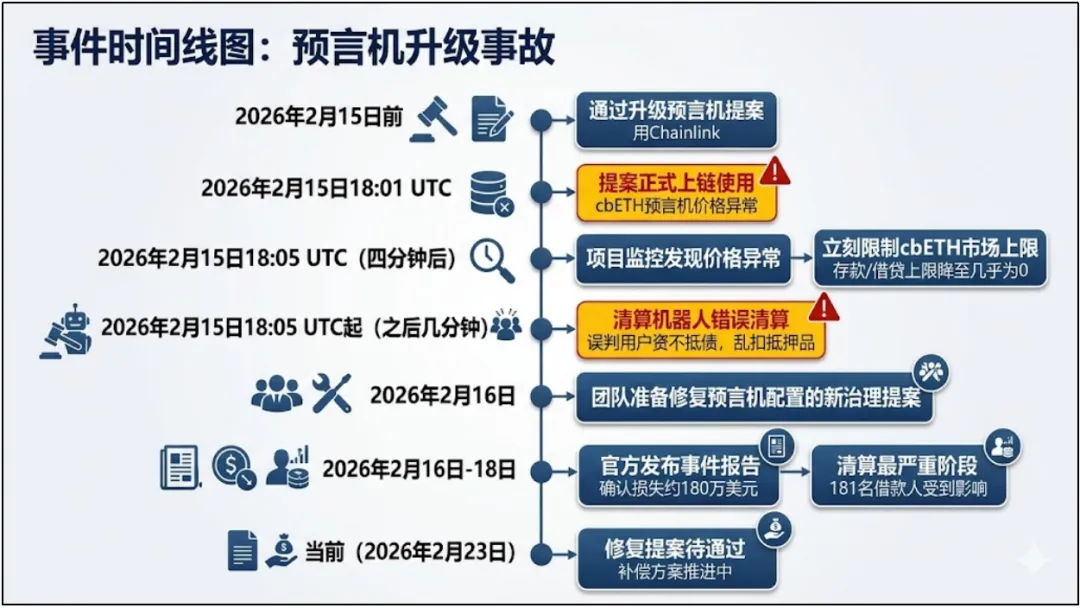
February 16, 2026, at 2:01 AM UTC+8: The MIP-X43 proposal was executed, and the incorrectly configured cbETH oracle on the Base chain was activated.
The on-chain liquidation bot monitored the profit opportunity, quickly borrowed a small amount of USDC through a flash loan at a very low cost to repay the borrower's debt (because the system assumed 1 cbETH was worth just over 1 dollar), thus gaining liquidation rights.

After seizing the cbETH collateral, which had a real high value, the bot immediately sold it at market price on a decentralized exchange for profit. Multiple bots operated in a crazy loop within just a few minutes, seizing a total of 1,096.317 cbETH.
This attack did not involve a long-planned hacker, but rather liquidation bots executing absurd code. Since there was no traditional meaning of a "thief," the question remains: where did the 1.78 million dollars that vanished into thin air end up? We must take a look at the following flow of funds.
III. Flow of Funds: No Hacker, Only Arbitrageurs
Since there was no traditional hacker, where did this 1.78 million dollars that vanished into thin air end up?
Where did the money go?
The answer is: Arbitrageurs behind the deployment of liquidation bots.
Liquidation bots did not appear out of nowhere; they are automated scripts written and deployed on-chain by real programmers or quantitative teams (i.e., MEV seekers). When the system legally sold $2400 worth of assets for just over $1 due to an AI's omission of a multiplication sign, these patrolling bots, like hunters, immediately seized the opportunity.
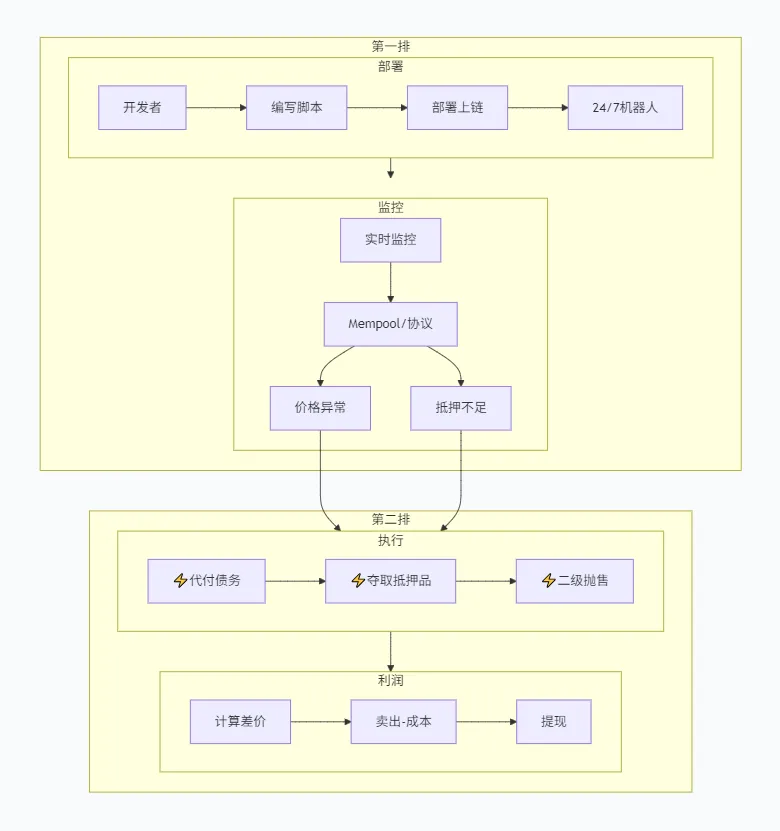
They automatically paid off the $1 debt on behalf of the users, seized the high-value collateral, and resold it at real market price. Ultimately, this nearly $1.78 million price difference flowed entirely into the personal crypto wallets of the bot owners. They exploited the system's flaw to complete this million-dollar withdrawal legally and compliantly.
In this incident, a total of 11 assets suffered losses, with the specific amounts of loss as follows:
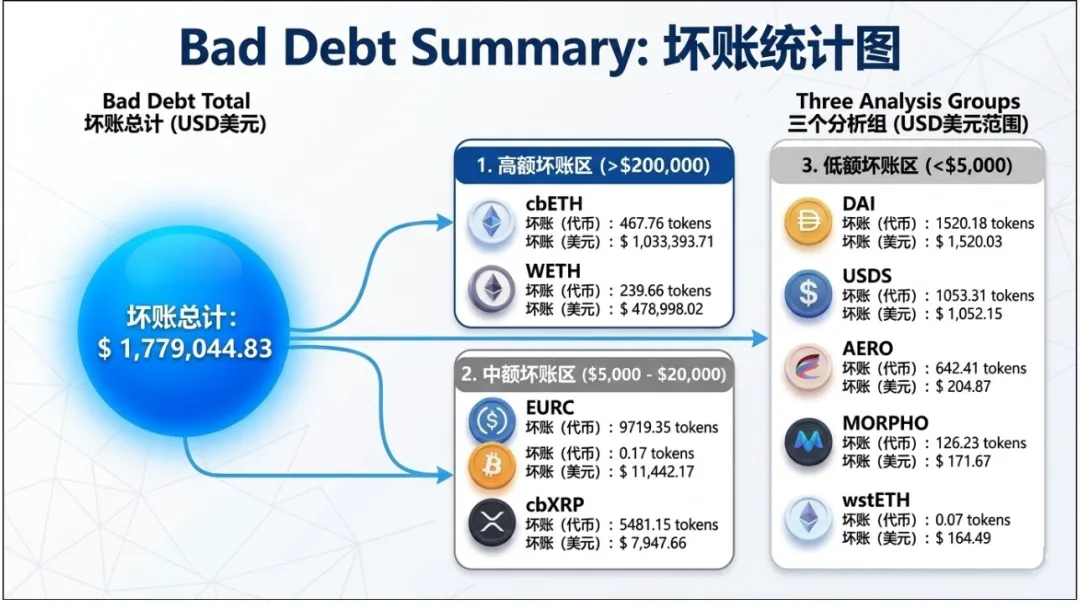
After the incident, the Moonwell team quickly suspended lending and liquidation functions and promptly submitted a new corrective proposal to reconfigure the oracle parameters. To regain trust, the protocol had to tap into its treasury funds to fill the $1.78 million bad debt gap and fully compensate the innocent users who were liquidated.
IV. With AI in Charge: A Boost in Efficiency or a Security Risk?
After the incident, the public opinion was largely "Claude wrote a fatal flaw," but objectively speaking, blaming this $1.78 million disaster on AI seems a bit unfair.
This flaw was not some profound vulnerability; it was just a super simple configuration error—a missed multiplication for an exchange rate.
To be honest, this kind of basic mistake could also occur with human programmers.
The truly fatal aspect is that the quality control process of the entire project was almost non-existent. Before the project went live, no one manually checked whether the "price was reasonable" in the code. If given the correct instructions, AI can clearly help write the test cases needed to prevent errors.
Therefore, the biggest lesson from this incident is not "AI cannot write code," but that in the rush for speed, crucial review stages were neglected.
No matter how good or fast AI is, it has no concept of real money and cannot be held accountable. AI can never replace humans; it is ultimately just a very useful tool. Humans must use AI; it absolutely must not become AI calling the shots while humans follow along.
V. In Conclusion: When AI Writes Code, Humans Should Be More Vigilant
The Moonwell incident is essentially not complicated; there were no top hackers, no sophisticated vulnerabilities, or even complex attacks. It was simply AI writing incorrect code, and humans did not pay much attention.
But in the world of blockchain, an oversight in a piece of code can mean millions of dollars in real money. In the DeFi world, code is the rule, and when the rules are written on-chain, they will be executed unhesitatingly by machines. As more and more projects begin to rely on "Vibe Coding," code auditing and risk control should become the last line of defense.
Technology can become increasingly automated, but security must never be automated.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




