Due to zero-knowledge proofs, the future of digital identity management will undergo a major shift towards privacy and user control.
Authored by: Yi Tong
Translated by: Yvonne, MarsBit
Zero-knowledge proofs have many exciting potential applications, with one powerful use case being the ability to confirm specific identity attributes such as age or citizenship without revealing any other personal information, thus maintaining user privacy and reducing the risk of identity theft or fraud.
The Magical Key to Digital Identity
In today's digital environment, our personal data security is constantly threatened by intrusion and cyber attacks. Zero-knowledge proofs (ZKPs) are a revolutionary encryption technology that forms a strong defense for our digital identities. While the term "zero-knowledge proof" may seem abstract and even far-fetched, it represents an advanced approach to enhancing the way we protect, manage, and engage online.
The concept of ZKP originated from a 1985 paper titled "The Knowledge Complexity of Interactive Proof Systems," which stipulated that one party, the prover, can confirm the truth of a statement without revealing the actual statement.
Exploring Zero-Knowledge Proofs
Essentially, ZKP allows one party (the prover) to prove to another party (the verifier) that a statement on the chain is true without revealing any information about the statement itself. A famous example related to this concept is the "Where's Waldo?" challenge. The goal of this challenge is to allow the prover to prove that they know Waldo's location without revealing his exact position on the page. To achieve this, the verifier uses a board with a small hole that perfectly fits Waldo. The prover covers the book with this board, allowing Waldo to be seen only through the hole. Through this opening, the verifier can confirm Waldo's presence but still does not know his exact location on the page. While this method is not a perfect expression of zero-knowledge proof as it does provide some clues, such as Waldo's body posture, it still aptly captures the fundamental idea behind zero-knowledge proofs.
In addition to theoretical discussions, zero-knowledge proofs have practical significance in fields such as cryptography, ensuring more secure passwords, digital signatures, and identities. In the context of identity verification, the prover wants to confirm a specific detail, such as their age or nationality, without providing any other personal information. ZKP uses complex mathematical algorithms to create digital "proofs" that the verifier can trust without viewing the actual underlying data.
Why ZKP Shines in the Identity Space
In the real world, proving your identity often means having to surrender a large amount of sensitive data. With ZKP, you can lock up your personal information securely. For example, you can prove your age without revealing all the information on your driver's license. ZKP enables you to do this. It maintains user privacy and reduces the risk of identity theft or fraud while verifying information. Additionally, ZKP can be used to combat misinformation, provide content attribution, and ensure more authentic interactions in a trust-minimized environment.
Real-World Applications of ZKP
Smart Contract Applications: On-chain activity verification using ZKP can be applied to initiate smart contracts based on user operations without revealing any personal identity information. This method operates similarly to performing encrypted operations and observing outputs without revealing the underlying computation process. Use cases include:
- Users can verify that they have enough assets to complete a transaction without disclosing their entire account balance, enabling smart contracts to execute securely and privately.
- Users can prove eligibility to participate in activities such as NFT creation or governance voting by providing evidence of past transactions.
- Users can transfer their status and rankings between applications and blockchain networks to establish and strengthen their reputation.
Financial Services: For institutions and financial services, providing data privacy, enhancing security, and complying with regulatory standards are crucial. ZKP can enhance privacy by protecting customer data while still complying with regulatory requirements. Additionally, they enhance security by keeping transaction details confidential, minimizing potential data leaks. Furthermore, ZKP has the capability to comply with regulatory guidelines while verifying transactions and authenticating user identities.
User Insights: Organizations can use ZKP to gain insights into user behavior without accessing personal data. For example, companies can use ZKP to verify if a user has watched a specific movie without knowing their entire viewing history. This allows for targeted marketing without infringing on user privacy.
Decentralized Authentication: In the digital identity space, ZKP can also be used for decentralized authentication. This allows users to verify their attributes without exposing any personal information to the verifying party. Consider a scenario where you need to verify your employment status to access restricted systems. With ZKP, you can confirm your employment without revealing where you work or any other details about your job. This means you can securely access systems without sharing any unnecessary information.
Why Now?
In today's digital age, identity protection and efficient authentication are crucial. Traditional systems often expose personal information, but zero-knowledge proofs offer a solution. They open up the possibility of sharing more by sharing less. They enable individuals to retain control over their personal information without compromising the user experience. Particularly for on-chain activities, zero-knowledge proofs simplify the identity verification process, provide reusable single proofs, and reduce data storage pressure. By integrating zero-knowledge technology, blockchain can offload computation to coprocessors and maintain its security while scaling through mechanisms like zero-knowledge rollup.
Currently, the adoption barriers for ZKP in various use cases stem from the cold start problem. In the initial stages of a new system, practicality is limited or nonexistent due to initial barriers. The widespread adoption of ZKP requires a catalyst for a two-sided market. Consider the transformation Airbnb brought to the travel industry. Before this, the concept of staying in a stranger's home was largely unimaginable and fraught with trust issues. Due to the lack of a brand guarantee, travelers were skeptical, and hosts faced the risk of inviting unknown guests. The core issue was the absence of a reliable intermediary to bridge the trust gap between guests and hosts. However, with Airbnb introducing a trusted platform offering features such as liquidity discovery, trusted dispute resolution, accidental event insurance, and transparent reviews, the once inconceivable became mainstream. Airbnb not only provided an alternative to hotels but also expanded the horizons of travel.
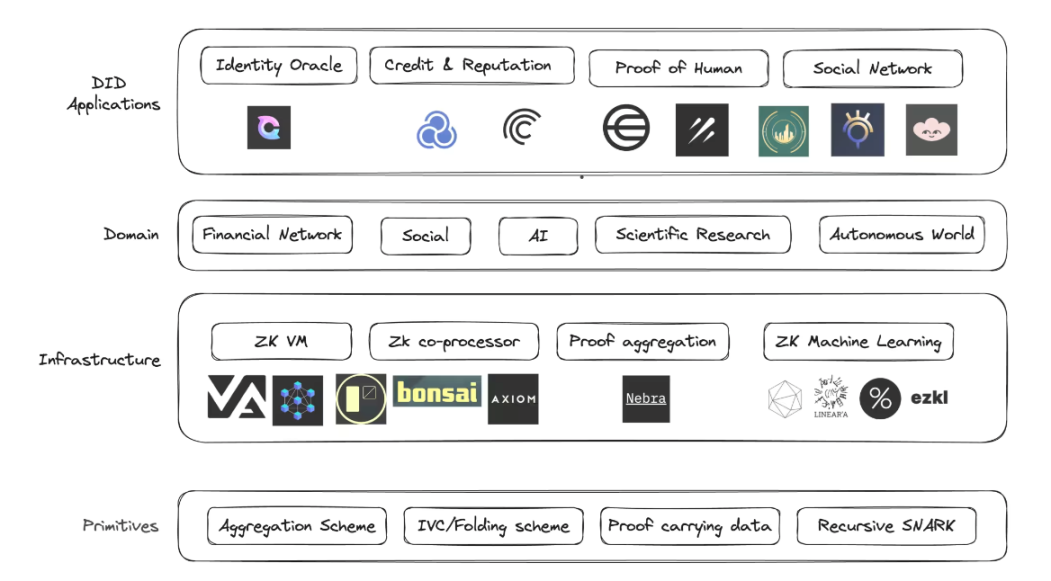
Similarly, ZKP enables individuals to disclose more information than they are willing to share while ensuring full privacy protection. These proofs provide verifiable data without revealing details. However, to fully realize this potential, a mechanism is needed to meaningfully process this additional information at scale, allowing applications to improve their functionality based on these insights. The overall vision is to create a trust-minimized digital ecosystem, simplifying the information sharing process. This will pave the way for a unified digital identity, ensuring seamless transitions across various platforms and bridging the gap between traditional Web2 structures and emerging Web3 paradigms. However, the high computational cost associated with verifying these proofs may be a barrier, limiting the range of feasible applications and restricting user access. Strategies must be devised to reduce the computational costs and duration associated with generating and verifying proofs, ensuring that everyone can truly access ZKP. Cryptographers are actively exploring various technologies to address this issue:
- Recursion allows provers to verify another computation's proof within a proof to maintain conciseness.
- Proof aggregation, whether homomorphic or ultimately heterogeneous, will horizontally scale proof capabilities and distribute the cost of each proof verification.
- Folding schemes like Nova, SuperNova, and Sangria are used to create faster, easier parallelized provers in untrusted settings, supporting customizable circuits.
The Future of ZKP
Zero-knowledge proofs represent a significant advancement in cryptography, providing a powerful method for securely and privately managing digital identities. As digital and online activities continue to permeate our lives, ZKP offers a way to protect privacy and regulate access to personal information.
There are many interesting projects leveraging ZKP innovations to expand the identity space:
- Clique is building a privacy-preserving identity oracle to bring arbitrary Web2 data onto the chain in a fully confidential, tamper-proof, and trust-minimized manner.
- Galxe is establishing an open, collaborative authentication network for Web3 developers and managing it.
- Sismo provides sovereign single sign-on, allowing applications to access previously unavailable data while protecting user privacy.
- Worldcoin seeks to create a global identity and financial network using "personhood proofs" to ensure each user is unique without revealing their real identity.
- Zuzalu Passport is an experimental passport using zero-knowledge proofs to prove Zuzalu citizenship without revealing who you are.
To make it easier for developers to access ZKP, many infrastructure companies are being established to improve the development experience:
- Axiom is building a coprocessor for accessing and processing historical data without trust.
- Nebra is developing general proof aggregation technology to aggregate proofs generated from different circuits and proof systems, scaling and reducing the cost of ZKP verification.
- Risczero is an investment firm that provides a general-purpose zkVM, a high-performance tool for correctly executing arbitrary code.
The evolution of the concept of proofs has had a philosophical impact on beliefs and has driven innovation that was once thought impossible. By adopting zero-knowledge proofs, a secure and private digital identity environment can be created, allowing individuals to share more information online while protecting their privacy. Additionally, as concerns about surveillance and data breaches continue to grow, zero-knowledge proofs bring hope for a more decentralized and user-centric internet.
The possibilities offered by ZKP are not limited to the theoretical field of cryptography but are rapidly becoming an integral part of our digital ecosystem. From enabling more secure online voting systems to creating tamper-proof academic transcripts, the potential applications are vast and diverse.
However, like all transformative technologies, the widespread adoption of ZKP requires technological evolution and social acceptance. Developers must focus on making these solutions more intuitive and accessible, and end-users need to understand the advantages of the new paradigm.
In conclusion, due to zero-knowledge proofs, the future of digital identity management will undergo a major shift towards privacy and user control. As we continue to explore and harness the power of ZKP, one thing is clear: the promise of a more secure and private digital world is not just a distant dream but an achievable reality. We have a responsibility to embrace emerging technologies, champion their advantages, and shape a future where digital identities are as protected as real-world identities.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



