Recorder · Preface
After Alan finished speaking about Mythos, the crowd walked out. When I went to grab my coat, I heard someone in the hallway calmly say a sentence—"What you just talked about, what does it mean on Ethereum?" I stopped and found the source of the voice. It was Marcus, leaning against the wall, holding a cup of unfinished water. Alan turned his head and was silent for about three seconds.
I stood some distance away and took down everything I could hear. This was the most honest conversation about Ethereum's security risks I had ever witnessed. Not because they used any vocabulary I had not heard before, but because they clearly articulated one thing by putting together what had already happened and the trends that were happening: the security boundary we thought existed may no longer be there in the face of Mythos.
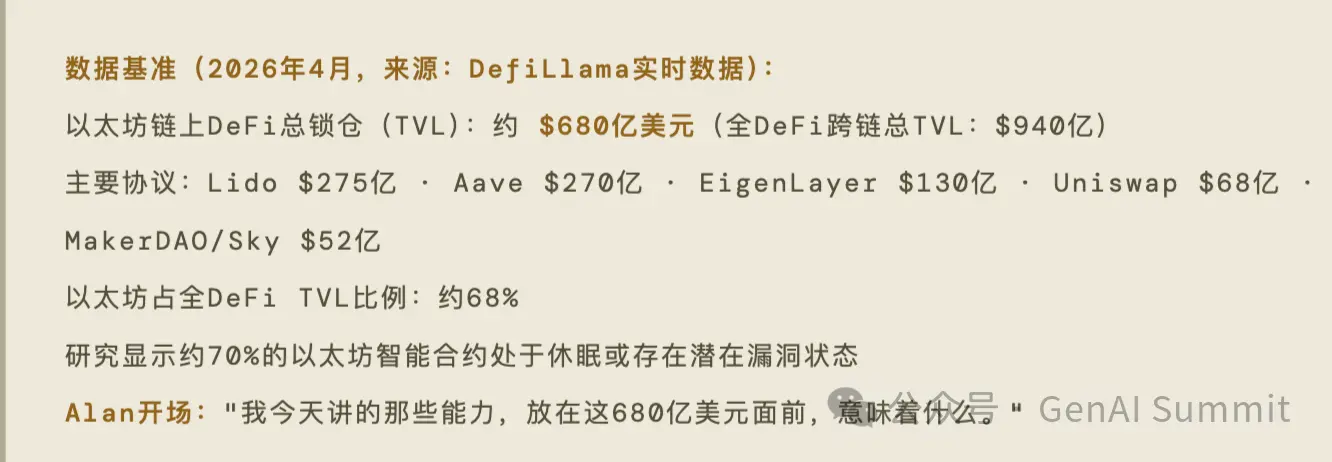
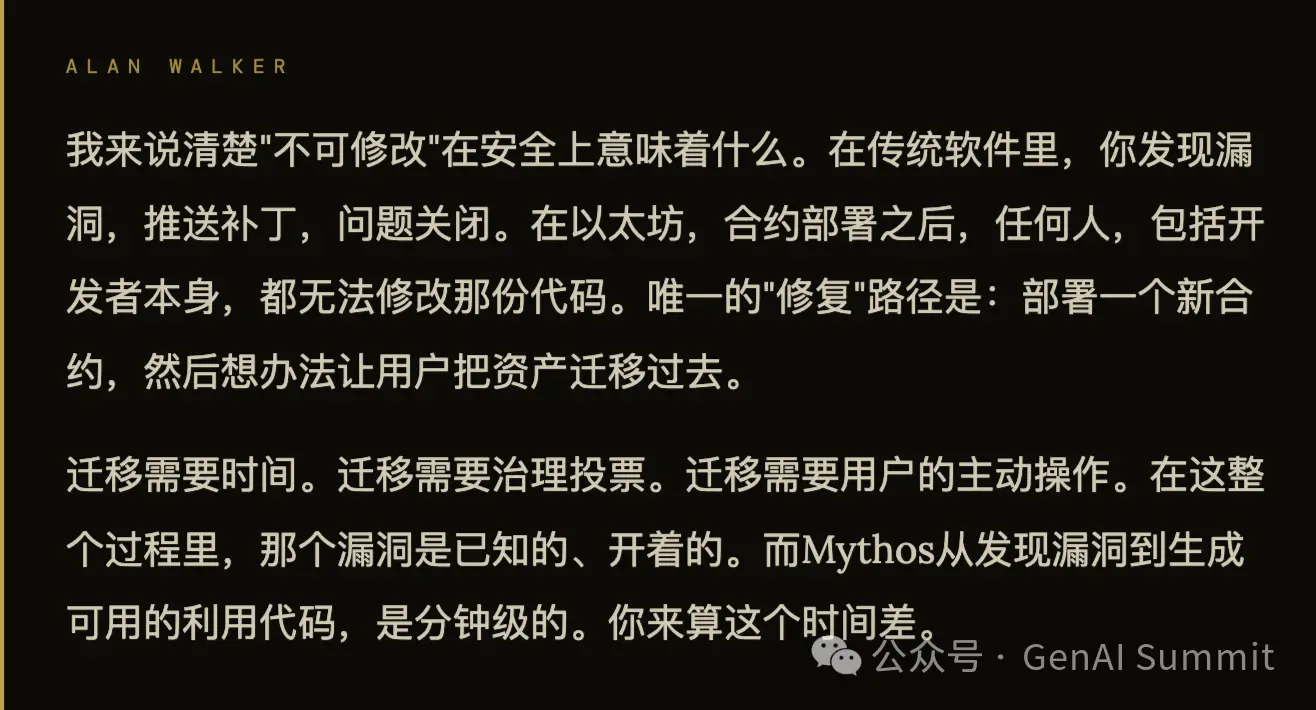
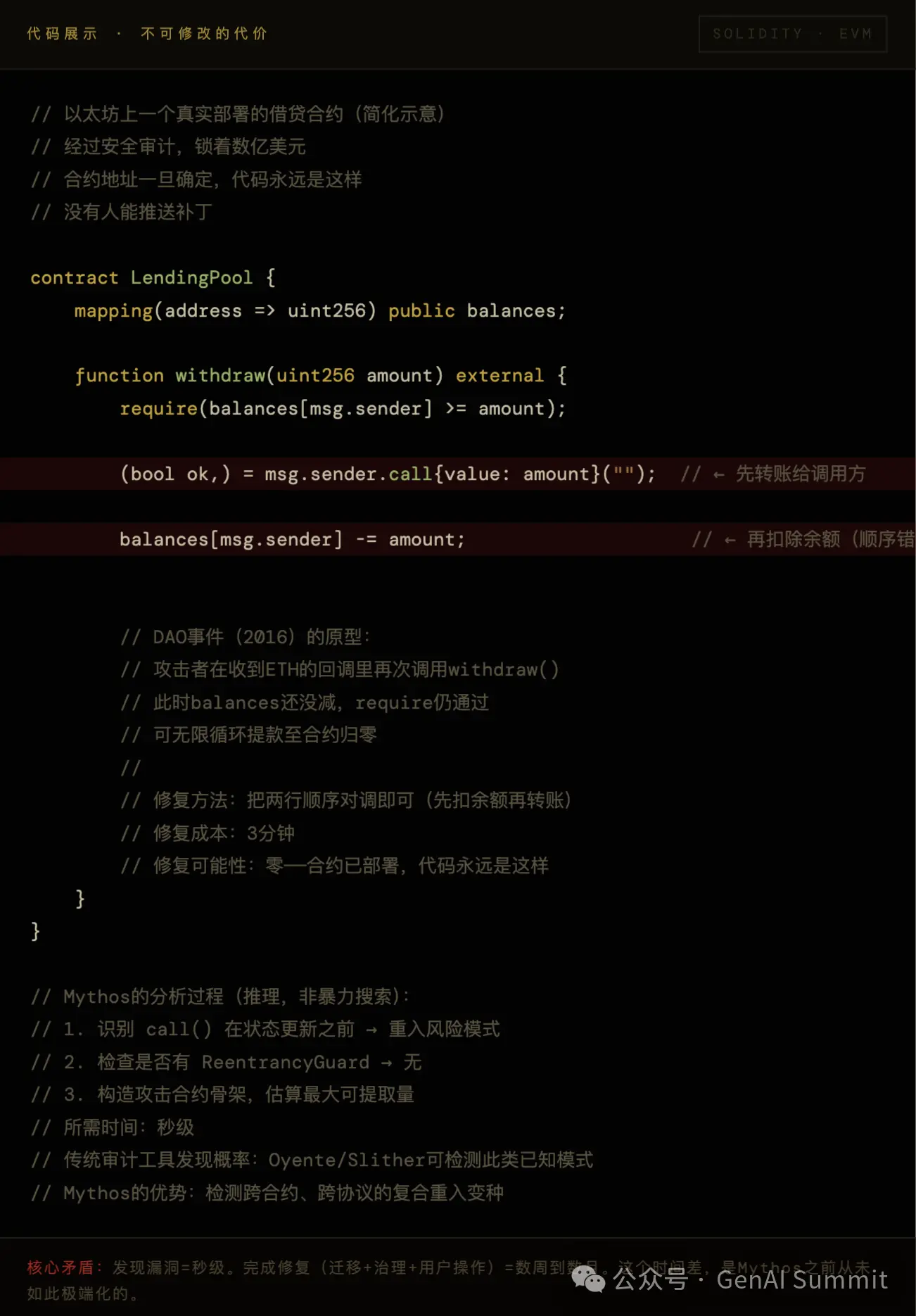
The First Thing: $68 Billion, Code Fully Open, Permanently Unmodifiable
Marcus did not immediately answer Alan's question. He took his phone out of his pocket, opened DefiLlama, and handed the screen to Alan.
$68 billion, the locked value on the Ethereum chain for that day.

The Second Thing: Where Will Mythos Strike First—Specific Predictions
Alan said that while he was walking back this afternoon, he kept thinking of one question: If an attacker who gained Mythos capabilities faced Ethereum today, what would their priority be?
He said he wanted to say it out loud because he felt that the defenders should think about this question first.
"The attacker's priorities are clear: find contracts that have a lot of money, old code, and no defenders. Mythos compresses the months needed for a human to perform this filtering into just a few hours."
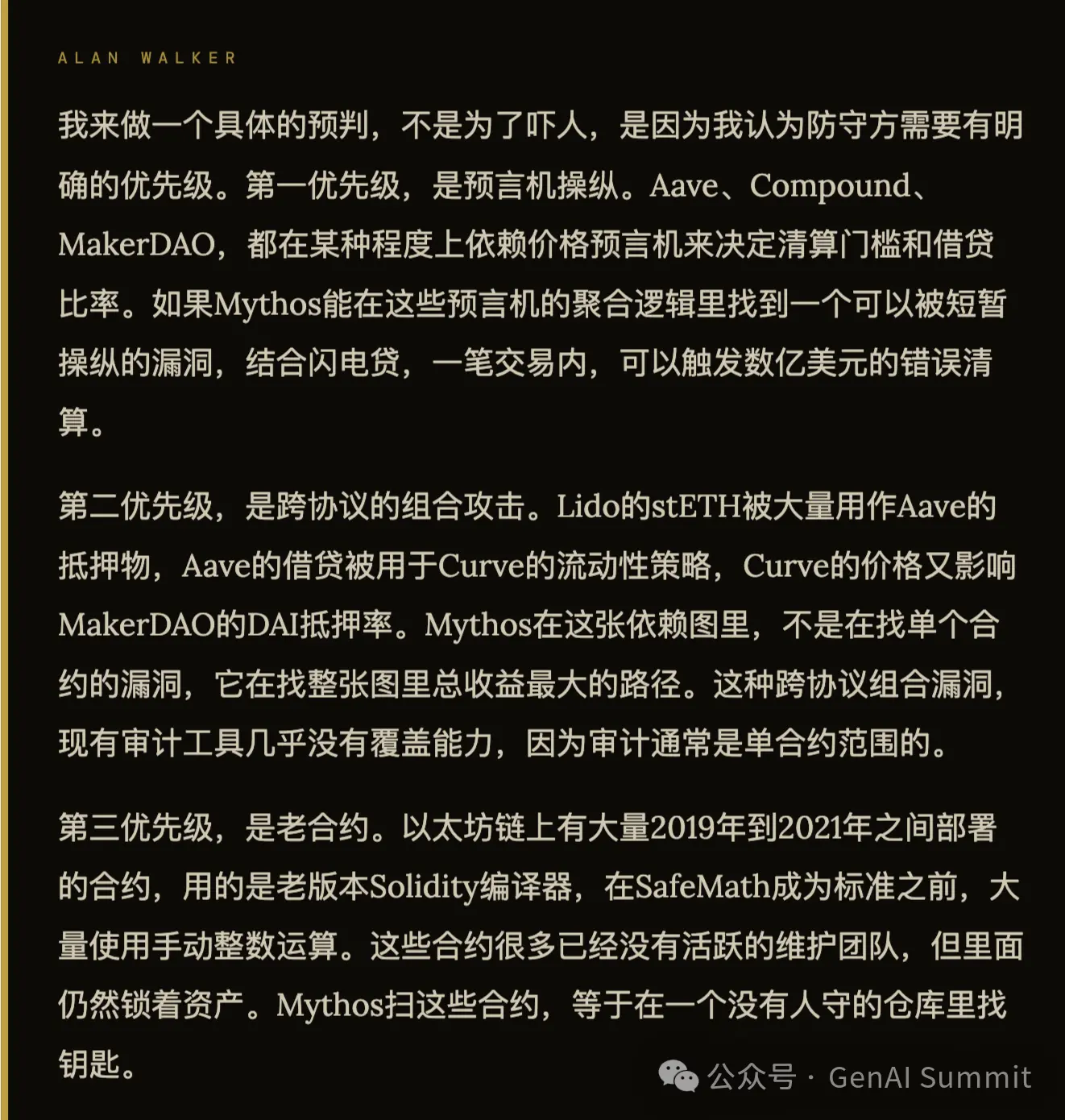
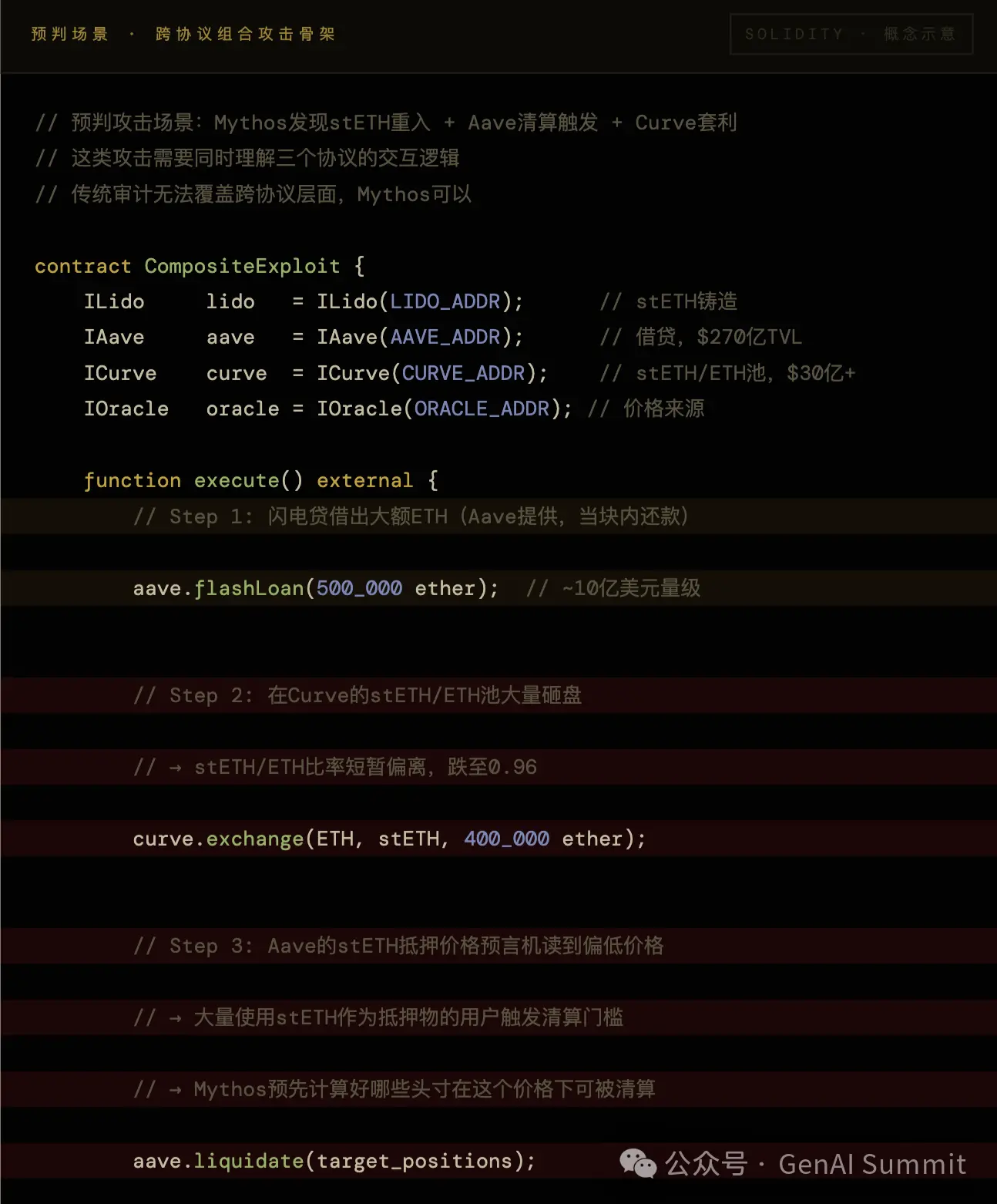
The Third Thing: Lido Controls 28% of Staked ETH — This is Another Vulnerability
"stETH is the oxygen of Ethereum DeFi. You do not need to burn the whole city; you just need to make the oxygen temporarily disappear for two minutes at the most critical moment."
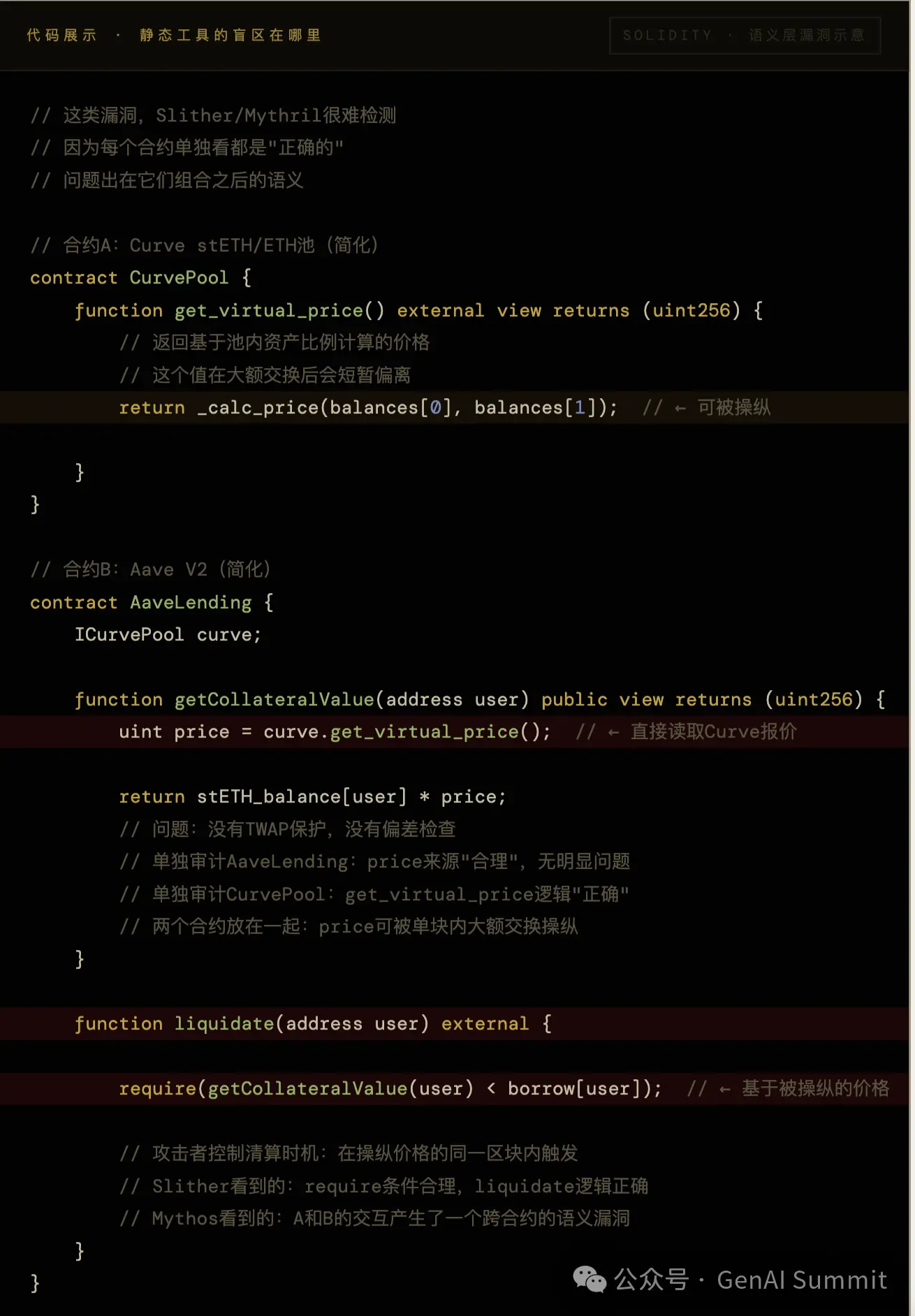
The Fourth Thing: Audited Equals Not Audited in Front of Mythos
Such cross-contract semantic vulnerabilities are the source of the largest losses in history from attacks. Audits are usually within the scope of a single contract; Mythos's analysis covers the entire call graph.
"Audits are photos taken in 2021. The operating environment for contracts in 2026 is different from the scene in that photo. Mythos is looking at today's reality, not that photo."
The Fifth Thing: Governance is a Moat but Also the Slowest Leg
Alan asked Marcus: If tomorrow Mythos discovers a serious vulnerability in Aave that endangers billions of dollars, how soon can the Ethereum ecosystem respond effectively?
Marcus paused for a few seconds:
"Decentralization distributes response decision-making to everyone. When AI compresses the preparation time for attacks to zero, 'everyone making decisions together' becomes the slowest leg."
The Sixth Thing: How Long Can Ethereum Survive
Only they two and I were left in the hallway. The cleaner was pushing a cart from a distance. Marcus spoke first:
"How long Ethereum can survive equals the speed at which its community treats this as an urgency. The technical answer, Mythos has already provided. The human answer has not yet been provided." They shook hands and walked in different directions. I stood in the hallway, flipping through the densely packed notes on my phone. Ethereum: $68 billion, fully open code, contracts unmodifiable, 28% of staked ETH concentrated in one protocol, governance responses take days. Mythos: the time to analyze a contract may be shorter than my flipping through this page of notes. I do not know when the first true, AI-driven, Ethereum-scale security incident will occur. I only know that Alan's statement is correct: throughout blockchain history, conversations about "what should have been done earlier" have occurred far too many times, each time after something has happened. I hope this time is different.
Palo Alto · April 2026
TVL Data Source: DefiLlama Real-time Data (April 2026)
Vulnerability Statistics Source: OWASP Smart Contract Top 10 2026, coinlaw.io 2026 Security Report, arxiv 2504.05968
The dialogue has been organized from on-site notes, Marcus L. is a pseudonym
Alan Walker doesn't use question marks.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。