Written by: systs
OpenBuild Guide:
In April 2026, DeFi faced its darkest moment, with thefts exceeding $625 million in a single month, setting a record high. Two attacks alone, from Drift and KelpDAO, consumed nearly $580 million. The explosion of AI has completely reversed the offense-defense landscape. Protocol vulnerability checks that originally took weeks by humans can now be done in just a few hours with large models, drastically reducing attack costs and significantly expanding attack surfaces, making more protocols targets.
Those well-resourced professional attackers with expertise in long-term strategies are eyeing every gap in protocols, while ordinary teams have dispersed energies, with passive and weak defenses. Only by maintaining extreme paranoia, building a comprehensive defense in advance, controlling losses, and preparing contingency plans can one survive this AI-dominated offense-defense battle. Below is the original content compiled by OpenBuild.

After developing the @openforage project and researching numerous historical attacks on DeFi protocols, I have become wary of nation-state attackers. Such opponents are seasoned, well-resourced, and adept at long-term positioning; like top-tier villains, they systematically scour every gap in your protocol and infrastructure for exploitable vulnerabilities. Ordinary protocol teams often have dispersed focus, balancing operations and security, making comprehensive defense impossible. I do not claim to be a security expert, but I have led teams in high-risk environments (both military experience and managing large funds in major financial institutions) and have practical experience in risk response and emergency planning. I firmly believe: only the paranoid can survive. No team begins with a "security is just a formality" mindset, yet hacker attacks persist. We must do better.
/ 01 AI Era: Everything Is Different
Hacker attacks are nothing new, but the frequency has recently surged significantly. The first quarter of 2026 set a new record for the number of DeFi hacker attacks, and with the second quarter just starting, it could break the previous quarter's record.
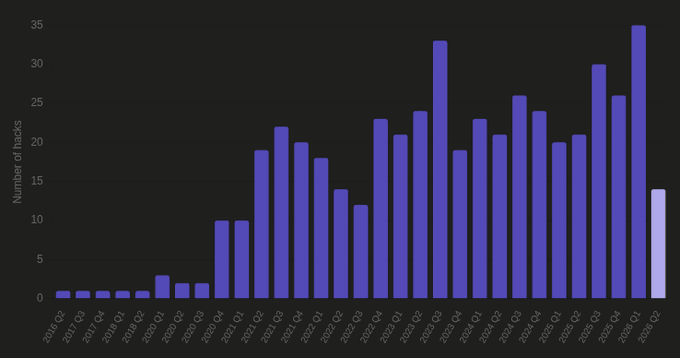
My core point is: AI has drastically reduced the cost of vulnerability scanning and exploration while greatly broadening the attack surface. Manually checking for configuration vulnerabilities across hundreds of protocols takes weeks; the latest large models can complete this in just a few hours. This fundamentally rewrites the underlying logic of protocol security defense and emergency responses. Established protocols, born before the rise of AI and reliant on traditional security measures, now face a significant risk of being accurately penetrated.
/ 02 Thinking Through Attack Surfaces and Layered Defense
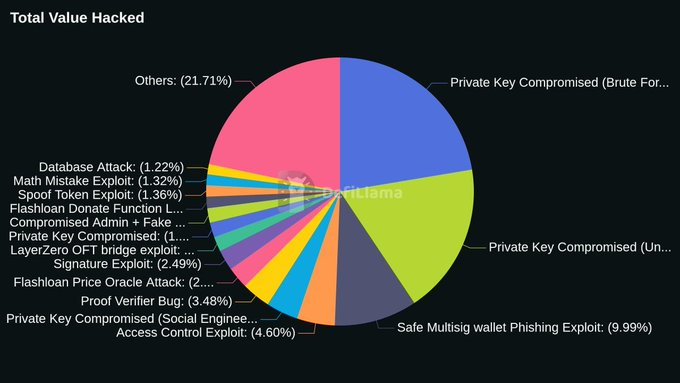
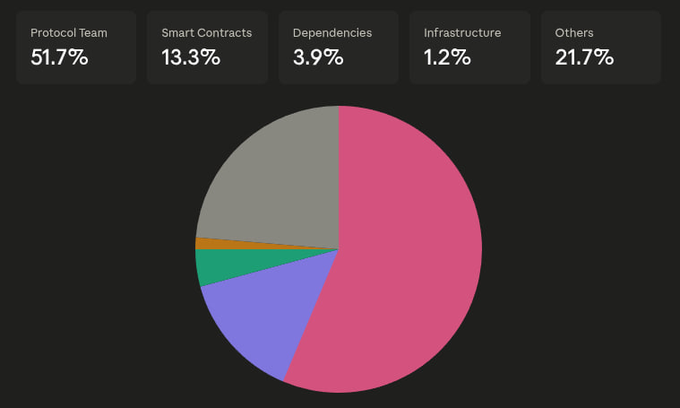
Practically, there are only three core breakthrough points for DeFi hacker attacks:
- Protocol operation teams
- Smart contracts and underlying infrastructure
- User trust boundaries (domains, social media, etc.)
Once the attack surface is identified, a five-layer layered defense system should be established:
- Prior Prevention: Implement standardized processes; strict enforcement can greatly reduce the probability of being breached.
- Loss Mitigation: Once prevention fails, control the scale of losses quickly.
- Emergency Shutdown: Under pressure, no one can make optimal decisions. Confirming an attack should trigger an emergency shutdown switch immediately to freeze assets and prevent further loss while allowing the team time to assess calmly.
- Control Recovery: If a malicious module or compromised component spirals out of control, it should be detached and replaced immediately.
- Post-Incident Recovery: Recover stolen assets. Pre-established partnerships with institutions can freeze funds, roll back transactions, and assist in tracing investigations.
/ 03 Core Principles
The following principles guide us in implementing the entire layered defense system.
Bold Frontier AI Empowered Defense
Make full use of cutting-edge large models to scan code repositories and configuration files for vulnerabilities, and conduct red-blue penetration tests over a wide attack surface: proactively explore front-end vulnerabilities to verify whether back-end intrusion is possible. Attackers will certainly do this; vulnerabilities found by defensive scans can also be discovered by attackers' probe scans. Tools such as pashov, nemesis, and AI security platforms like Cantina (Apex) and Zellic (V12) can quickly complete initial code screening before formal audits.
Time and Process Friction is Defense
All potentially risky operations should be designed with multi-step processes + time-lock mechanisms. Once anomalies are detected, ample manual intervention and asset freeze windows should be reserved. The industry used to resist time locks and multi-step permissions, mainly due to the cumbersome process affecting team operational efficiency. But now the situation has changed: AI can automatically bypass such human process frictions in the background; protocols sticking to simple operations are meaningless.
Invariable Design
Smart contracts can defend by defining core invariants that cannot be violated: once these rules are broken, the entire logic of the protocol becomes invalid. The core invariant of @openforage is designed around solvency: vault assets + deployed assets ≥ unpaid debts. General protocols should only set a few critical invariants; do not hard-code multiple checks for every function, as this leads to bloated and hard-to-maintain code.
Checks and Balances
Many hacker attacks stem from wallet private key leaks/multi-signs being compromised. Reasonable permission configurations must ensure: that even if multi-signatures are compromised, losses can be rapidly stopped, and the protocol can be switched to a stable state manageable by governance decisions. The key is to manage two types of power balances:
- Governance Permissions: Control all core decisions of the protocol
- Emergency Rescue Permissions: Responsible for restoring governable stable order but without the authority to override or replace the existing governance system
Expect Things to Go Wrong
It is essential to establish a baseline understanding: no matter how professional the team, they will eventually face attacks. Smart contracts or dependent components may fail, teams may encounter social engineering attacks, and version upgrades may introduce unknown vulnerabilities. Adopting this mindset, limiting flow risk and implementing emergency shut-off become essential measures: controlling a single loss to within 5%-10%, freezing assets before calmly devising a response plan. In critical situations, hasty decisions must be avoided.
Implement Contingency Plans Early
The best time to prepare for an attack is always before something goes wrong. Institutionalize and formalize emergency processes, and have the team repeatedly practice to avoid chaos during crises. The AI era means: supporting tools and algorithms must be in place to quickly gather all information, generating concise summaries and comprehensive details delivered to the core decision-making circle.
Survival is the Ultimate Goal
No need to pursue absolute perfection, but survival is a must. No system has ever been impregnable from the moment it is launched; only through ongoing review and iteration, absorbing lessons, can one grow into an anti-fragile architecture. Never being hacked does not mean being inherently safe; the moment of greatest comfort and relaxation is often when risks are highest.
/ 04 Pre-Prevention System
Smart Contract Design
After clarifying core invariants, incorporate them into runtime verification logic and carefully select truly necessary rules for forced verification. It is recommended to follow the FREI-PI design pattern (Function Requirement - Execution Impact - External Interaction - Protocol Invariants): all functions involving asset changes should re-verify their core invariants before execution ends. Many attacks that conform to CEI (Check - Execute - Interact) standards but still get hacked (flash loan arbitrage, oracle malicious liquidation, cross-function solvency loss) can be intercepted by invariant checks at the end of functions.
Improve Testing Systems
Stateful fuzz testing: generate random call sequences for all public interfaces of the protocol, verifying invariants at each step. The overwhelming majority of on-chain attacks are multi-transaction composite attacks, and stateful fuzz testing is virtually the only reliable way to uncover such vulnerabilities before the attacker does. Writing invariant tests ensures these rules hold in any call sequence generated during fuzz testing; when paired with formal verification, proof should be provided that the rules remain permanently valid across all reachable states. The protocol's core invariants must undergo formal verification.
Oracles and External Dependencies
Complexity is the greatest enemy of security. With every additional layer of external dependency, the attack surface grows. If developing core foundational components, the trust choice should be given to users; if dependencies cannot be removed, ensure multiple redundant decentralizations to avoid single points of failure collapsing the entire protocol. The audit scope must cover failure scenarios of oracles and external dependencies, and set limits, so even if anomalies occur, disaster losses can be controlled within manageable ranges. The recent KelpDAO attack is a typical case: the project used LayerZero's default configuration requiredDVNCount=1, which was not included in the audit scope; ultimately, the target attacked was foundational infrastructure outside the audit.
Comprehensively Sort Out Attack Surfaces
The known attack vectors in DeFi have long been established in a complete list. Check each item against your own protocols and implement corresponding control measures. Establish internal red-blue confrontation capabilities and force AI agents to actively uncover protocol vulnerabilities; this is now the baseline requirement for the industry.
Native Built-in Emergency Rescue Permissions
In a voting governance model, initial powers are highly centralized among the team’s multi-signatures and later gradually decentralized. Even if token distributions are widespread, delegated powers often condense down to a few wallets, and in extreme cases, may include only one key address. Once such a wallet is breached, the protocol directly collapses. It is advised to deploy guardian wallets with strictly narrowed permissions: they may only pause the protocol; under extreme conditions, a threshold of 4/7 or more is required to rotate the compromised delegated power to a backup wallet. Guardians have no authority to initiate or pass any governance proposals.
This way, the protocol has an independent emergency rescue layer: it can restore governable stable states without overruling the native governance system. The probability of all 4/7 or more guardians failing simultaneously is very low due to the dispersion of holding addresses; once the governance system matures and permissions are sufficiently decentralized, this emergency layer can be gradually phased out.
Wallet and Key Architecture
Multi-sign wallets are standard, adopting at least a 4/7 multi-sign structure, where no one person can independently control all seven keys. Periodically rotate signer addresses discreetly. Signature keys must not be mixed with everyday devices: if the signing device is used for browsing the web, sending and receiving emails, and logging into office software, it is automatically assumed that the device has been compromised. Utilize multiple multi-sign wallets, each tasked with different responsibilities. Preset at least one multi-sign wallet to be completely compromised and design contingency plans based on this premise. No individual, even if facing threats or personal violence, has the authority to independently compromise the protocol.
Vulnerability Bounty Planning
I strongly agree with Nascent's views on vulnerability bounties. Protocols with financial strength should set bounties that are proportionally very high compared to the protocol's TVL; even if the scale is smaller, the bounty should be as generous as possible (starting at least in the seven-figure range). When facing high-level nation-state attackers, bounty negotiations are generally ineffective; however, a white-hat security haven plan can be launched: authorize white hats to safeguard stolen funds in exchange for a percentage of the bounty, essentially costing the depositors the bounty expense.
Select Quality Audit Agencies
I previously thought that with the improvement of large model capabilities, the marginal value of traditional audits would decline, but my view has now adjusted:
- Top auditing agencies always stay at the forefront. If a protocol adopts innovative designs and the code and potential vulnerabilities are not included in the training data, merely piling up computational power has not been proven to uncover new logical vulnerabilities. No one wants to be the first victim of a new attack method.
- An easy-to-overlook point: auditing agencies back their own industry reputation. Once an audit report is issued, if the protocol is hacked, these agencies have strong motivation to help review and mitigate losses. Establishing long-term cooperation with professional security teams is itself a valuable asset.
Implement Operation and Maintenance Security
Include operation and maintenance security in core assessment indicators. Regularly conduct phishing drills; hire trusted external red teams to conduct targeted social engineering attack tests on the team. Keep spare hardware wallets and backup devices ready, which can fully replace a complete multi-sign configuration, avoiding last-minute purchases and hasty remedies during incidents.
/ 05 Loss Mitigation
Exit Channels as Loss Limits
All asset outflow channels must set upper limits; the theoretical maximum loss caused by exploiting these channels must be locked down. Simply put: a minting function without single block limits equates to giving an unlimited minting vulnerability a blank check; a redemption function without weekly caps is akin to granting unrestricted access for asset balance manipulation vulnerabilities. Prudent setting of hard limits for each outflow channel is required, balancing between acceptable maximum losses and extreme user experience. Once the defenses fail, this restriction can prevent the protocol from going to zero.
Whitelists and Blacklists
Most protocols have implicit lists of callable interfaces, tradable assets, and authorized addresses, as well as explicit boundaries for prohibited user actions. Even if the rules are implicit, they must be institutionalized in writing. After clarifying black and white lists, two-step permission changes can be set to artificially increase attack friction. Attackers must first tamper with the whitelist/remove blacklist restrictions before implementing malicious operations. Under the dual mechanism, attackers must overcome two hurdles for new attack vectors: passing entry audits (integration/deployment) and bypassing security prohibitions (risk control reviews).
/ 06 Control Recovery
Algorithmic Automated Monitoring
Having an emergency shutdown switch with no one monitoring it is as good as non-existent. Build an off-chain monitoring system to 24/7 continuously inspect core invariants, and automatically escalate alerts upon detecting anomalies. The alert chain ultimately reaches core personnel of the guardians’ multi-sign, complete with full context to support minute-level decision-making.
First Shut Down, Then Assess
When under attack, prioritizing loss control is essential; do not make hasty decisions under crisis countdown. Corresponding to the protocol, it means activating an emergency shutdown switch (simultaneously displayed on the frontend): a single transaction can pause all asset transfer pathways. Prepare a “one-click pause all” script in advance, which automatically traverses all modules that can be paused and atomically executes shutdown operations. Governance permissions themselves cannot be closed; if the guardian level can pause governance contracts, if the guardians are breached, the recovery process will be permanently locked.
Activate an Emergency Task Force
After freezing assets and halting losses, gather pre-designated core trusted personnel to establish a dedicated communication channel. Strictly control the scope of informed parties to prevent information leaks to attackers, public opinion, or profit-seeking arbitrageurs. Predefine specific roles and rehearse:
- Decision-maker: coordinates and makes final decisions
- Maintenance executor: adeptly executes defense scripts and shutdown operations, collaborating with the decision-maker's directives
- Vulnerability reviewer: reconstructs the attack chain and identifies root causes
- External liaison: interfaces with key partners
- Incident recorder: documents progress, key decisions, and timelines throughout the incident
With clear responsibilities for all personnel and prior rehearsals, processes advance smoothly during incidents rather than becoming chaotic and disordered.
Anticipate Secondary Risks
Assume attackers possess top-tier skills: the initial vulnerability may merely be a diversion or a prelude to subsequent chain attacks. This invasion may also serve as bait, prompting our side to make mistakes that trigger deeper vulnerabilities. Shutdown operations must undergo rigorous evaluation and be completely closed-loop, without possessing exploitable vulnerabilities. The protocol should freeze globally; avoid shutting down only a single module, which may expose other weak links. After locating root causes and attack vectors, simultaneously inspect surrounding related attack surfaces and chain risks, repairing all at once.
Activate Pre-Set Succession Rotation Mechanisms
Permission rotations are only safe and reliable if pre-set succession addresses are in place. I advocate for a pre-set succession address registry mechanism: attackers find it difficult to stealthily replace normal guardian/governance wallets with malicious ones. The logic is consistent with black and white list risk control. All key roles should pre-register succession addresses. Emergency permissions should only allow one operation: replacing role X with the pre-set successor. During peacetime, select and conduct due diligence on candidates thoughtfully without needing to make hasty decisions during incidents.
Cautious Testing Before Version Upgrades
After locating the root cause and impact scope, contract upgrade patches must be released. This is often the highest risk code deployment: under pressure, writing hastily while adversaries have fully grasped protocol logic and are well-versed in vulnerability exploitation. Never skip testing and launch directly. If there is no time for formal audits, leverage white-hat networks or initiate a 48-hour bug bounty competition before launch to bring in external offensive and defensive perspectives for formal deployment.
/ 07 Post-Incident Recovery
Swift Action
Stolen funds have a laundering half-life; once attacks succeed, funds are quickly split, transferred across chains, and laundered. Pre-establish connections with on-chain analysis service providers like Chainalysis to real-time mark the attackers' multi-chain address clusters and synchronize alerts with exchanges' risk control teams, tracking the cross-chain fund transition paths. Prepare a list in advance: compliance departments of centralized exchanges, operators of cross-chain bridges, custodial administrators, and all third-party partners authorized to freeze cross-chain messages and intercept assets in transit.
Negotiation Mediation
Though reluctant, it is advisable to proactively communicate with attackers. There is always room for negotiation. Issue a time-limited white-hat bounty announcement, publicly committing to dropping all legal pursuits if funds are fully returned on time. If the opponent is a nation-state entity, negotiations are likely to yield no results; however, many attackers might just happen to find vulnerabilities and wish to profit discreetly, leaving room for negotiation. Legal personnel must be involved throughout the process.
/ 08
Hacker attacks will not disappear, and with the iteration of AI capabilities, attacks will only become more frequent. The defensive side cannot rely solely on self-improvement; we must adopt the same AI tools as attackers, normalizing red-blue confrontations, continuous real-time monitoring, and hard-setting loss limits to withstand extreme risks and survive industry cycles.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



