Written by: BlockSec
Key points: The $290 million bridging vulnerability of KelpDAO triggered a chain reaction, freezing over $6.7 billion of WETH liquidity across five chains, affecting users who had never interacted with rsETH. This event also revealed the actual boundaries of "permissionless" systems: The Arbitrum Security Council executed enforced state transitions through governance-authorized atomic contract upgrades, transferring 30,766 ETH without the need for holder signatures.
On April 18, 2026, KelpDAO’s rsETH cross-chain bridge was attacked, resulting in losses of about $290 million, marking the largest DeFi security incident of the year. Initial tracing points to the Lazarus Group, a well-documented state-level attack organization with a long history of targeting crypto infrastructure [1]. This attack did not exploit a smart contract vulnerability, but rather poisoned the RPC infrastructure relied upon by a single decentralized validation network (DVN) node, falsifying cross-chain messages and releasing rsETH tokens without corresponding burns on the source chain.
LayerZero [1] and KelpDAO [2] have both detailed the attack itself. This article approaches it from a different angle: rather than reiterating the attack process, it examines what happened in the aftermath: how a single point of infrastructure dependency led to the freezing of billions in liquidity across five chains, and how this chain reaction forced decentralized governance frameworks to exercise centralized emergency powers under public scrutiny.
The causal chain of the KelpDAO incident spans three levels of the "decentralized" tech stack: the single point DVN dependency made the attack possible; the composability of DeFi (i.e., "DeFi Legos," the property of protocols connecting like building blocks) subsequently transformed this bridging vulnerability into a systemic liquidity crisis; and the scale of the crisis, in turn, compelled governance frameworks to expose the centralized emergency powers embedded within them.
Background: Overview of the KelpDAO Attack
KelpDAO is the issuer of rsETH. rsETH is a liquidity-restaking token (LRT) representing ETH staking positions distributed across multiple operators. To enable the cross-chain circulation of rsETH, KelpDAO integrated LayerZero's messaging protocol. This protocol relies on the DVN to confirm the legitimacy of cross-chain messages on the target chain before execution.
Key configuration choice: KelpDAO’s rsETH OApp utilized a 1-of-1 DVN configuration, relying solely on the DVN operated by LayerZero Labs as the only validator. This means that the entire cross-chain security of rsETH depended on a single validation entity. LayerZero's integration documentation explicitly recommends using a redundant multi-DVN configuration, and LayerZero indicated that this best practice was communicated to KelpDAO prior to the incident [1]. KelpDAO responded that the 1/1 configuration was "recorded in LayerZero's documentation and published as the default configuration for any new OFT deployment," and that it was "explicitly recognized as an appropriate configuration during the L2 scaling process" [2].
The attacker compromised two RPC nodes used by LayerZero Labs’ DVN, replacing their binaries with malicious versions. These malicious nodes only returned forged on-chain state data for the DVN's IP address, appearing normal to all other observers (including LayerZero's own monitoring infrastructure). Meanwhile, a DDoS attack targeting the unbreached RPC nodes forced a failover to the poisoned nodes. As a result: the DVN confirmed a cross-chain message never occurred on the source chain, releasing 116,500 rsETH from the Ethereum side adapter (0x85d4...8ef3) without a corresponding source chain burn [1, 3]. The release transaction was 0x1ae232...db4222. On-chain evidence is unequivocal: the Ethereum target endpoint accepted nonce 308, while the maximum outbound nonce reported by the Unichain source endpoint remained 307 [10].
KelpDAO detected the anomaly within 46 minutes and paused all related contracts. This action prevented a subsequent attack aimed at an additional 40,000 rsETH (approximately $95 million) [2]. However, by this time, the attacker had already entered the next stage: converting the stolen rsETH into loanable assets through DeFi lending protocols.
From Forged Tokens to Loanable Assets
The attacker did not directly sell the stolen rsETH. The 116,500 tokens were dispersed into seven branch wallets and monetized through various channels, including direct exchanges for ETH via aggregators, supplying positions in Compound V3, and bridging to Arbitrum [10]. However, the most impactful route went through Aave: the attacker deposited 89,567 rsETH (approximately $221 million) into the Aave lending markets on two chains: Ethereum Core and Arbitrum. Utilizing Aave’s E-Mode (a funding efficiency feature that allows related assets to achieve a higher loan-to-value ratio), the attacker borrowed 82,620 WETH and 821 wstETH using the deposited rsETH as collateral [3].
These positions were leveraged to the maximum. The health factor of the attacker’s seven addresses ranged between 1.01 and 1.03, just slightly above the liquidation threshold [3]. This was possible because Aave's E-Mode set an LTV of 93% for rsETH, with a liquidation threshold of 95%, providing only a 2 percentage point safety buffer.
The details for each address across the two markets are as follows:

Table 1: Details of the attacker’s rsETH supply and WETH/wstETH borrowing across Aave's two markets
Data source: On-chain data statistics, combining Etherscan, Arbiscan, and DeBank as of 2026-04-22 16:51 UTC. The USD value reflects the token prices at the time of each transaction.
Chain Reaction: How a Bridging Vulnerability Frozen WETH Across Five Chains
The following illustration outlines the complete chain reaction. Steps 1 and 2 (the bridging vulnerability and Aave collateral deposits) were introduced in the background section above. This section delves into steps 3 to 5: why WETH had to be frozen, which parameters shaped the severity of the chain reaction, and the actual cost of the freeze.
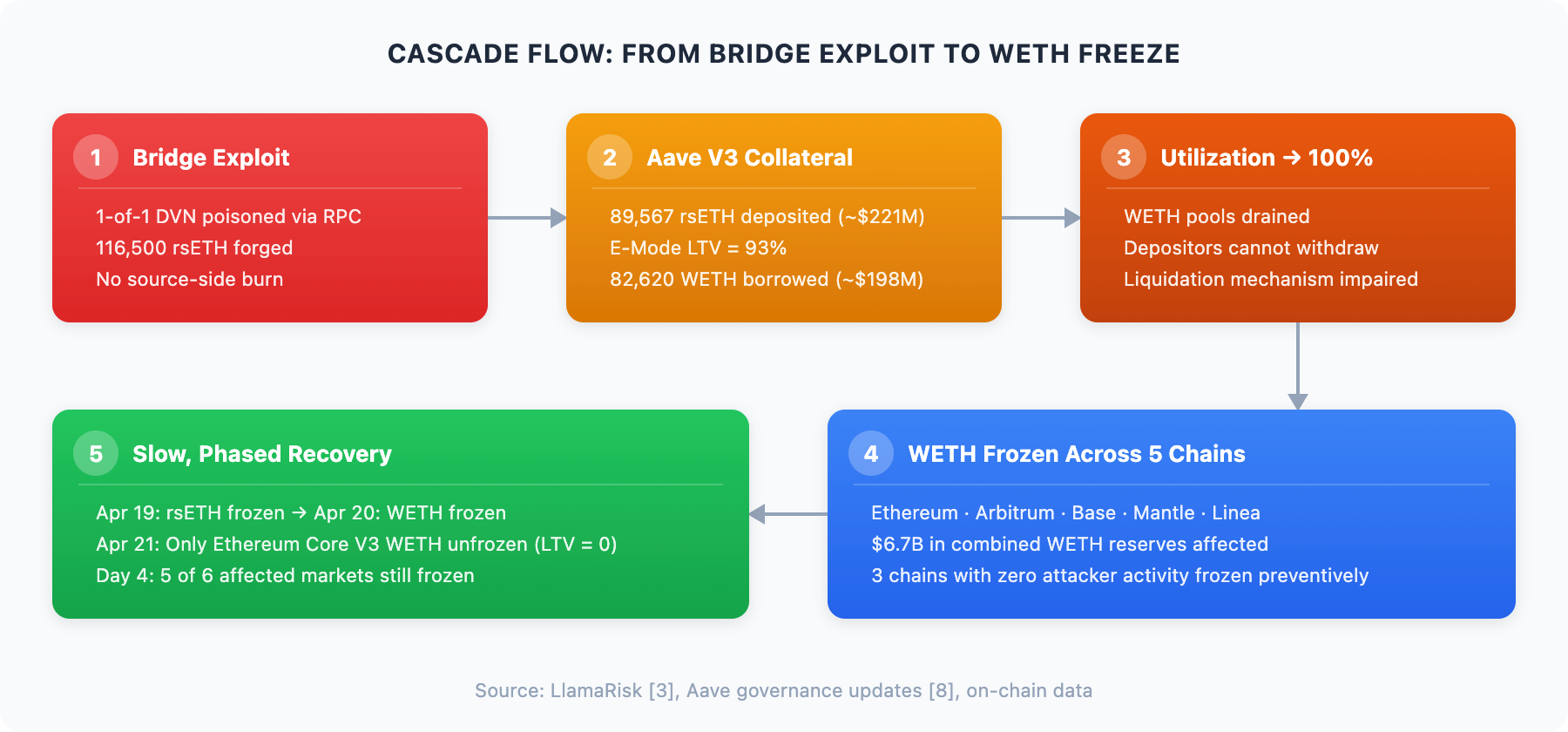
Figure 1: Chain reaction process from the bridging vulnerability to WETH freezing across five chains
Why WETH Had to Be Frozen
On April 19, Aave's Protocol Guardian froze all rsETH and wrsETH markets on Aave V3 and V4, prohibiting new deposits and borrowings using rsETH as collateral [8]. This was the anticipated first step response.
An unexpected second step occurred on April 20: Aave froze WETH reserves on Ethereum, Arbitrum, Base, Mantle, and Linea [3, 8].
Why freeze WETH? It is an asset that was not attacked and has no relationship with the cross-chain bridge. Because the rsETH deposited by the attacker was minted without any corresponding asset on the source chain. Aave's oracles continued to price these tokens at the full market price, treating them as valid collateral indistinguishable from legitimately bridged rsETH. The attacker exploited this information asymmetry to borrow real WETH against uncollateralized liabilities at the system level. This drained WETH from the lending pools, pushing the utilization rate of the affected markets to 100%. With full utilization, existing WETH depositors could not withdraw, and liquidators could not obtain the underlying assets needed to execute liquidations. The liquidation mechanism, which is the core defense against bad debts for protocols, was effectively paralyzed [3].
If WETH borrowings remained open, the remaining pool liquidity across other chains could be drained through the same mechanism: depositing rsETH, borrowing WETH, and then exiting. Freezing WETH was not optional; it was the only means to control the damage.
Three Parameters Shaping the Chain Reaction
The severity of this chain reaction was not coincidental. Three protocol parameters determined the scale of direct damage and the resulting extent of the freeze.
1. LTV: How Much Healthy Asset Can Be Extracted Per Unit of Contaminated Collateral
Aave's E-Mode set an LTV of 93% for rsETH, meaning that for every $1 of contaminated rsETH deposited, $0.93 of WETH could be borrowed. In contrast, during the same period, Spark Protocol's rsETH LTV was 72%, and Fluid's was approximately 75% [3]. Aave's parameters were the most aggressive in the market.
This was a well-considered design decision rather than an oversight. In January 2026, Aave governance raised the E-Mode LTV for rsETH from 92.5% to 93%, further compressing an already thin safety buffer from 2.5% to 2% [3]. The base (non-E-Mode) LTV was deliberately set at a near-zero level (0.05%), effectively forcing all meaningful rsETH borrowing to come through the high LTV E-Mode path.
2. Pool Depth: The Vulnerability of Markets to Liquidity Extraction
The same amount borrowed can have drastically different impacts in target pools of varying depths.

Table 2: Scale of WETH reserves in Aave V3 markets across chains and the proportion directly extracted by attackers
Attackers only deposited rsETH in the Aave V3 market. Aave V4 (deployed only on Ethereum and launched on March 30, 2026) was also preemptively frozen for rsETH [8], but this is not reflected in this table. WETH reserve data is sourced from LlamaRisk [3]; attacker borrowing data comes from the detailed address table above.
The attacker focused on borrowing operations within Ethereum Core and Arbitrum. But the key observation is what happened on chains untouched by the attacker. Since rsETH was accepted as collateral on Mantle, Base, and Linea, any existing user positions collateralized by rsETH on these chains faced potential bad debt risks once the underlying bridge support was broken. Aave's decision to preemptively freeze WETH across all five chains was a reasonable response: keeping those markets open would expose them to the same extraction mechanisms that the attacker had already validated on Ethereum and Arbitrum [3, 8].
3. Number of Cross-Chain Deployments: The Extent of the Freeze Propagation
rsETH was listed as collateral in 11 of the 23 Aave V3 markets, with 7 having substantive exposure [3]. The attacker operated on only 2 chains, but the preemptive WETH freeze impacted at least 5 chains, including markets where the attacker had never deposited a single token. LTV determines how much is withdrawn on each chain, and pool depth dictates the impact each market faces. But it was the number of chains that accepted rsETH as collateral that ultimately determined the spread of the freeze.
These parameters are not static. Nine days before the attack, on April 9, Aave's Risk Steward raised the supply cap for rsETH: from 480,000 to 530,000 in Ethereum Core and from 52,000 to 70,000 in Mantle [3]. While this does not imply causation (the attacker’s preparation likely predated these adjustments), it highlights how regular parameter adjustments can inadvertently amplify the impact of future events.
Real Effects of the Freeze
As a result: a $290 million bridging vulnerability led to the freezing of WETH liquidity across five chains, with combined reserves in the affected markets exceeding $6.7 billion.
The direct losses are limited to the amount borrowed by the attacker. However, in DeFi lending, a freeze is far from a minor operational interruption. It locks user liquidity, prevents withdrawals, disrupts active positions, and undermines the protocol's liquidation mechanism that protects against bad debts. The vast majority of affected users had never interacted with rsETH, KelpDAO, or any cross-chain bridge. They are the WETH depositors and borrowers on Aave, participating in what they reasonably believed to be a straightforward lending market.
WETH is the most foundational liquidity asset in DeFi. Freezing it is analogous to shutting down the withdrawal channels of the largest bank in town, because another financial institution was scammed using a product most depositors have never heard of.
LlamaRisk’s event report [3] established two bad debt scenario models and provided chain-by-chain shortfall forecasts, which is currently the most detailed risk propagation analysis. However, even this analysis focuses on potential bad debts rather than the broader operational costs stemming from the freeze itself, including withdrawal locks, obstructed positions, and diminished liquidation capacities across all affected markets. A comprehensive quantification of the overall impact of the chain reaction remains an open question.
If the attack’s chain reaction is complex, the recovery process is equally intricate. Composability imposes constraints on both damage and resolution. Aave cannot simply “unfreeze everything.” Each market needs to be assessed independently, facing different risk conditions based on local rsETH exposure, WETH utilization, and the status of the attacker’s activities. The timeline clearly illustrates this:
April 19: The Protocol Guardian froze all rsETH and wrsETH reserves on Aave V3 and V4 [8].
April 20: WETH was frozen on Ethereum, Arbitrum, Base, Mantle, and Linea [3, 8].
April 21: Only WETH from Ethereum Core V3 was unfrozen, with the LTV kept at 0 as a precaution. WETH on Ethereum Prime, Arbitrum, Base, Mantle, and Linea remained frozen [8].
Four days after the attack, only one of the six affected markets had been unfrozen. The recovery path mirrored the complexity of the attack path: advancing protocol-by-protocol and chain-by-chain, each step requiring governance coordination and risk assessment.
Emergency Response: How Arbitrum Transferred 30,766 ETH Without Holder Signatures
While Aave managed the lending crisis, a parallel response action was taking place on Arbitrum. On April 21, the Arbitrum Security Council announced an emergency action, freezing 30,766 ETH held by the attacker on Arbitrum One [6]. These funds were transferred to an intermediate frozen address (0x...0DA0), which could only be disposed of through subsequent Arbitrum governance voting [7].
Governance Actions
The Arbitrum Security Council is an official component of the Arbitrum DAO governance structure and is not an external body or ad hoc committee. This emergency action was publicly announced through the Arbitrum governance forum [7], executed after law enforcement confirmed the attacker’s identity [6], and included complete transaction details for anyone to verify. The Security Council acted within its established authority, weighing "the commitment to the security and integrity of the Arbitrum community while not affecting any Arbitrum users or applications" [6].
This was not a decision made behind closed doors, but an emergency action authorized through governance, executed transparently, with on-chain evidence clearly visible.
Technical Mechanisms
What makes this action noteworthy is not the governance decision itself, but how it was executed on-chain. Based on BlockSec's Phalcon trace analysis [9], the Security Council employed an atomic three-step operation:
The Upgrade Executor temporarily upgraded the Ethereum inbox contract (DelayedInbox), adding a new function called sendUnsignedTransactionOverride.
This function was used to create a cross-chain message impersonating the attacker’s address. The message was injected via Bridge.enqueueDelayedMessage, with kind=3 corresponding to L1MessageType_L2Message in the Arbitrum Nitro stack. This message type permits the execution of L2MessageKind_UnsignedUserTx on L2. The key point is that this path does not require signature verification. The sender parameter switched from the standard msg.sender path to caller-controlled input, carrying the attacker’s address context through L1→L2 address aliasing.
Once the transfer was completed on L2, the inbox contract was reverted to its original implementation.
Both the L1 transaction [4] and the resulting L2 transaction [5] can be publicly viewed on the Phalcon Explorer. The L2 transaction shows "from attacker to 0x...0DA0", but this is not a standard user-signed transfer; it is a protocol-level enforced state transition: assets were transferred without the asset owner's private key through governance-level infrastructure upgrade permissions.
The Dilemma of Decentralization
The principle itself is straightforward: upgradeable contracts grant infinite capabilities. If a contract is upgradeable, its behavior can be modified to do anything, including transferring assets without holder signatures. This is an inherent capability of any system built on upgradeable contracts. The 30,766 ETH currently sits in a frozen address. Only subsequent Arbitrum governance votes can decide its disposal. The atomic upgrade-execute-revert pattern left no permanent changes to the inbox contract and did not affect any other users or applications [6].
From most reasonable assessments, the actions of the Arbitrum Security Council were correct. The attacker was identified as a nation-state actor, law enforcement was involved, the governance process was public and transparent, and $71 million of stolen assets were recovered or at least prevented from further laundering.
But the capability that made this all possible extends far beyond this specific case. The same upgrade-execute-revert mechanism could, in principle, be used to transfer any asset held by any address on Arbitrum One. The Security Council's power is not limited to the attacker’s address or the stolen funds; it is a general capability constrained by governance norms rather than code.
This is the dilemma. Users hold an implicit mental model when interacting with L2: "My assets are controlled by my private keys; without my signature, no one can transfer them." The emergency response to the KelpDAO incident demonstrates that this model is incomplete. On Arbitrum and any L2 with upgradeable bridging contracts and a Security Council, assets can be transferred through governance-level actions that completely bypass signature verification.
Arbitrum is not an outlier. The freezing of Aave markets was likewise a governance-driven emergency action. In the KelpDAO incident, multiple protocols simultaneously exercised centralized emergency powers: Aave froze markets on five chains, the Arbitrum Security Council executed forced transfers, and KelpDAO globally paused contracts. The crisis response of this "decentralized" ecosystem was, in practice, a coordinated exercise of centralized power.
The issue is not whether emergency powers should exist. The KelpDAO case provides a strong argument for their necessity. The question is whether the boundaries, triggering conditions, and accountability mechanisms for these powers are sufficiently transparent. Users who deposit assets on L2 should be able to answer a fundamental question: Under what circumstances can the Security Council transfer my funds? What recourse do I have?
Current Status of Stolen Funds
Independent on-chain tracing of the stolen funds (for complete visualization see MetaSleuth [11]) shows that the attacker dispersed 116,500 rsETH into seven top-level addresses, most of which were deposited into Aave (Ethereum Core and Arbitrum) as collateral to borrow WETH and wstETH; the borrowed tokens, after a minor DEX exchange, aggregated to the same address 0x5d39...7ccc (Ethereum / Arbitrum) on both chains. As of 2026-04-22 05:42 UTC, the stolen funds are distributed across four states:

Table 3: Distribution of Four States of Stolen Funds (as of 2026-04-22 05:42 UTC)
Approximately 31% are frozen or intercepted, 23% remain in an untouched address on Ethereum, and 46% have already been or are in the process of being distributed to 103 top-level downstream addresses. The attacker’s rsETH collateral in Aave has not yet been redeemed, and the borrowed WETH and wstETH have not been returned; the lending positions have been abandoned.
The causal chain of the KelpDAO incident spans three levels of the "decentralized" tech stack.
The starting point is single point dependency. KelpDAO's 1-of-1 DVN configuration reduced cross-chain validation to a single entity, allowing the entire bridge to be compromised through a single breached infrastructure component. The architecture supports decentralization, but the configuration does not.
Composability then transformed a bridging vulnerability into a systemic liquidity crisis. An attack froze WETH, the most fundamental asset in DeFi, impacting five chains and affecting billions in liquidity, involving users who had no relation to rsETH or KelpDAO. The reach of the cascade was shaped by quantifiable parameters: aggressive LTV settings, shallow liquidity pools, and extensive cross-chain collateral deployments.
The scale of the crisis forced decentralized governance to exercise centralized emergency powers. The Arbitrum Security Council transferred 30,766 ETH without holder signatures through governance-authorized atomic contract upgrades. Aave froze markets across multiple chains through governance-driven emergency action. These responses were effective, transparent, and arguably necessary, while also providing clear proof of the actual boundaries of "permissionless" existence.
Single point dependency made the attack possible, composability amplified the damage, and the damage revealed the longstanding centralized powers embedded within upgradeable contracts and governance frameworks. Addressing these interconnected issues requires collective action from participants on all sides:
For Protocols: The overall security level of a protocol depends on its weakest link; in this incident, the shortcoming lay with the DVN infrastructure rather than the smart contracts [10]. Effective security requires systemic coverage across multiple dimensions, including code security, infrastructure security, key management, and operational security. Comprehensive security assessments and penetration tests should stress-test the complete tech stack rather than inspecting isolated components. On-chain monitoring enables protocols to trigger emergency responses within minutes rather than hours, and rapid cross-chain fund tracking is crucial for coordinating asset freezes and maximizing recovery. Specifically for lending protocols, collateral for cross-chain synthetic assets should be stress-tested against "complete collateral failure" scenarios, combined with the three parameters discussed above (LTV, pool depth, number of cross-chain deployments).
For L2 Governance and DAOs: Emergency powers should be transparent and accountable. Most major L2s already possess such capabilities, but they are often buried deep within technical documentation rather than presented in user-facing materials. Governance frameworks should explicitly codify triggering conditions, scope limitations, time constraints, and post-hoc accountability requirements.
For Users: Understand the systemic risks inherent in DeFi composability. In this incident, WETH depositors who had never interacted with rsETH saw their liquidity frozen across five chains. The risk of a single position is only part of the picture; the protocols, pools, collateral types, and chains your assets interact with create an interconnected risk landscape.
References
[1] LayerZero Core, "KelpDAO Incident Statement": https://x.com/LayerZero_Core/status/2046081551574983137
[2] KelpDAO, "April 18 Incident: Additional Context": https://x.com/KelpDAO/status/2046332070277091807
[3] LlamaRisk, "rsETH Incident Report" (April 20, 2026): https://governance.aave.com/t/rseth-incident-report-april-20-2026/24580
[4] BlockSec Phalcon Explorer, L1 Transaction (Arbitrum Security Council action): https://app.blocksec.com/phalcon/explorer/tx/eth/0x079984c56c5670108f5c6f664904178f9b364340351949a42e4637d1f645f770
[5] BlockSec Phalcon Explorer, L2 Transaction (Arbitrum forced transfer): https://app.blocksec.com/phalcon/explorer/tx/arbitrum/0x5618044241dade84af6c41b7d84496dc9823700f98b79751e257608dac570f6b
[6] Arbitrum, "Security Council Emergency Action": https://x.com/arbitrum/status/2046435443680346189
[7] Arbitrum Governance Forum, "Security Council Emergency Action 21/04/2026": https://forum.arbitrum.foundation/t/security-council-emergency-action-21-04-2026/30803
[8] Aave, rsETH incident updates (April 19-21, 2026): https://x.com/aave/status/2045593585966252377
[9] BlockSec Phalcon, "Arbitrum Security Council freeze analysis": https://x.com/Phalcon_xyz/status/2046467830498173088
[10] banteg, "Kelp rsETH Unichain → Ethereum Path Investigation": https://gist.github.com/banteg/705d0284513b74ad20f61d90f5b5de62
[11] MetaSleuth, KelpDAO exploit trace: https://metasleuth.io/result/eth/0x1ae232da212c45f35c1525f851e4c41d529bf18af862d9ce9fd40bf709db4222?source=600c61cd-f0cd-4dff-8687-14e02f6ccd24
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



