Original author: ChandlerZ, Foresight News
"I have bruises on me, I tried to resist, but my hands and feet were injured, the axe cut me, there's not much I can do now."
On March 5, 2026, cryptocurrency influencer sillytuna tweeted a very brief message stating that they had just been violently attacked, losing approximately $24 million in AUSD stablecoins, and described the incident involving violence, weapons, kidnapping, and threats of rape. The police have already intervened.
Sillytuna was previously the holder of Punk #7523 (commonly known as "Covid Alien"), which sold for $11.7 million at Sotheby’s in 2021, at one point setting the auction record for a single punk.
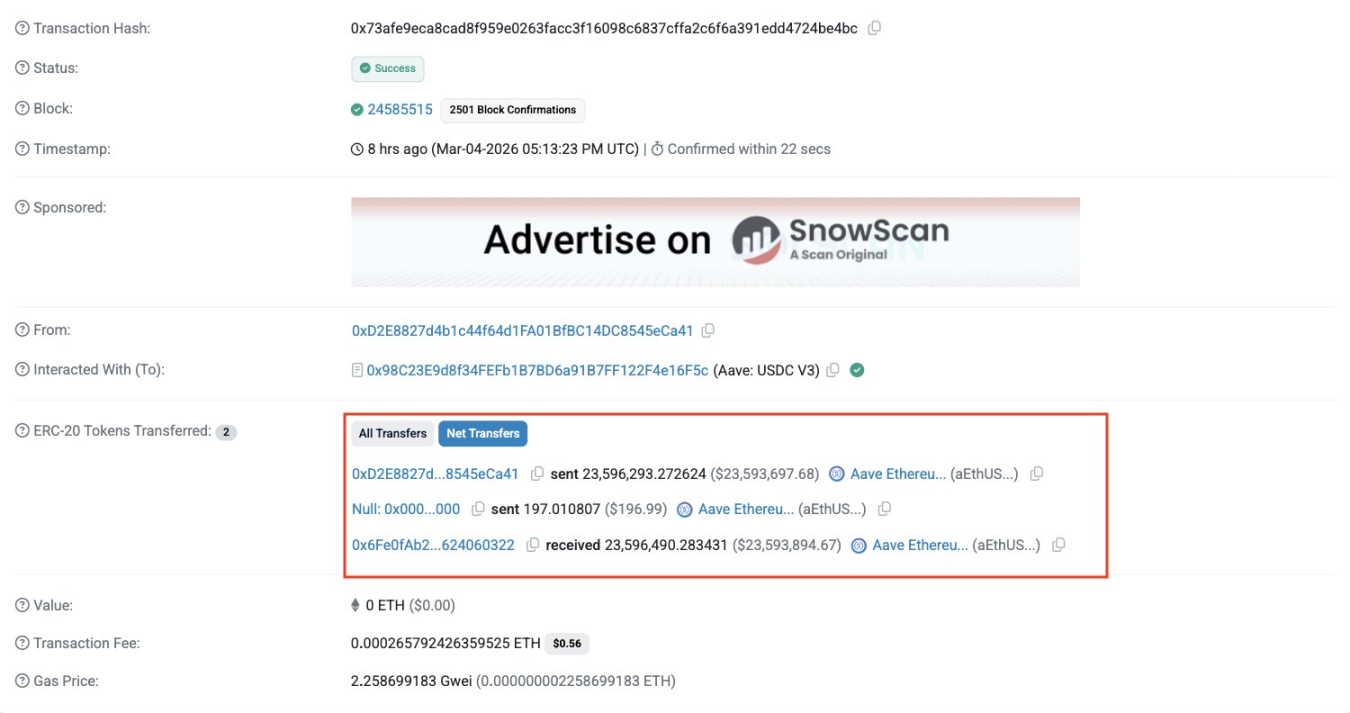
This tweet quickly spread throughout the crypto community. Security company PeckShield detected related on-chain transfers and initially flagged them as a "Poisoning Attack", which is a method of deceiving users into transferring funds by spoofing similar addresses.
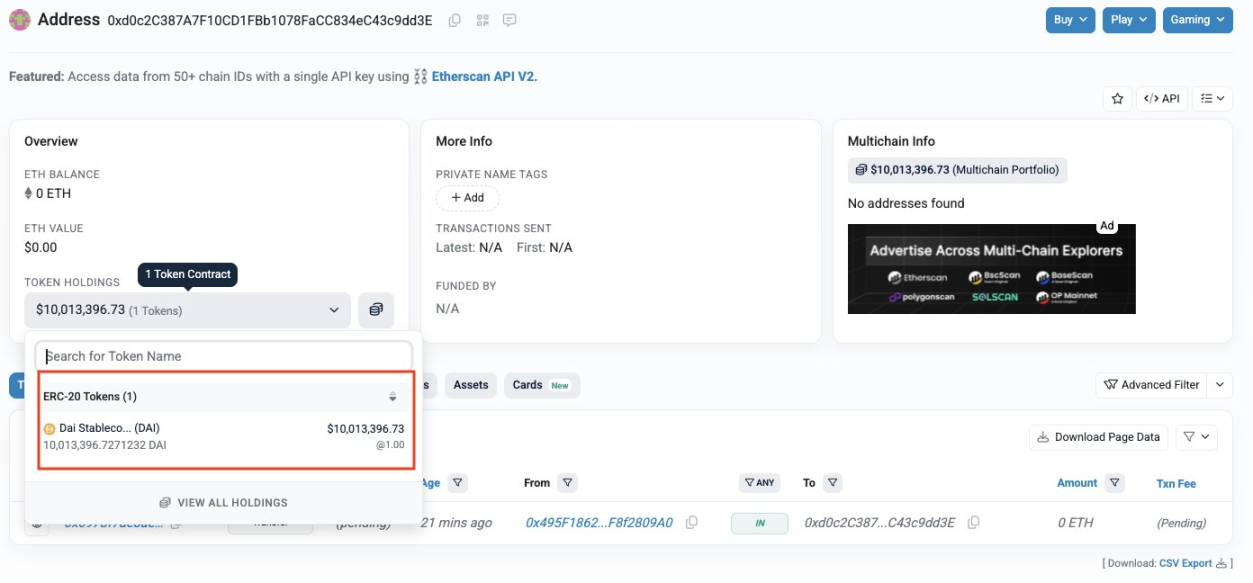
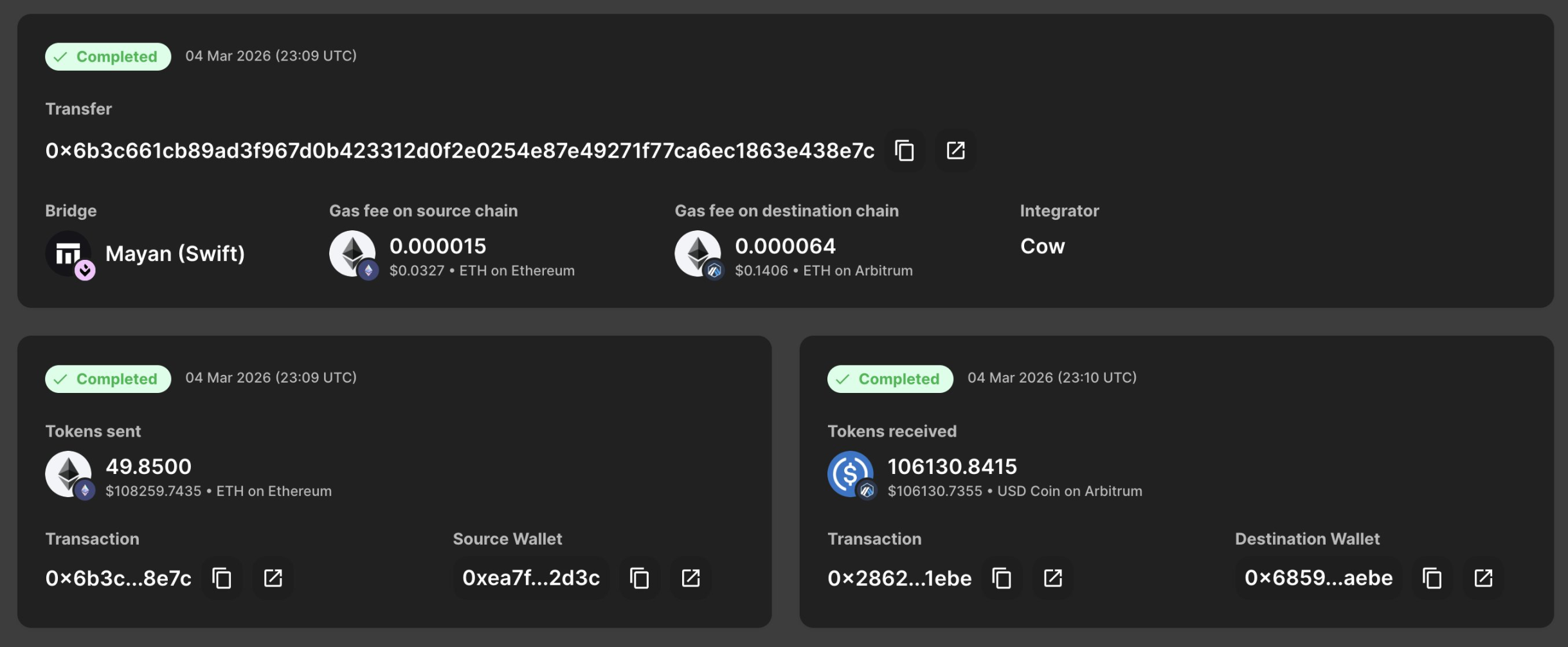
According to PeckShield's monitoring, approximately 20 million DAI are currently located in 2 wallets controlled by attackers (still unwashed): an address starting with 0xdCA9 (about $10 million) and an address starting with 0xd0c2 (about $10 million). The attackers have begun to transfer small amounts of funds to Arbitrum across chains.
There is a clear contradiction between the two statements; if this is a poisoning attack, the victim would have been deceived into transferring actively, and physical violence would not be a necessary prerequisite; if it is physical coercion, the attackers must have the victim's real identity and address.
The details of the incident are still pending police investigation confirmation, and some members of the community are questioning whether it is a "traffic post." But regardless of the final conclusion of this case, the panic it triggered has already highlighted one thing:
In today's highly transparent world of crypto wealth, a single erroneous on-chain exposure may incur a real axe.
Not an isolated case: 169% Increase in Physical Attacks in 2025
所谓的「扳手攻击」,是指攻击者通过暴力、恐吓、绑架等物理手段,迫使受害者交出私钥或密码。这类攻击不依赖技术漏洞,而是直接将矛头指向加密资产背后的个人。
According to a report released by CertiK, "wrench attacks" surged by 75% in 2025, with physical violence becoming a significant threat in the crypto space.
From the perspective of attack patterns, the report indicates that kidnapping remains the main attack path, with 25 incidents occurring throughout the year; direct personal attacks increased by 250% year-on-year, becoming one of the most concerning changes. Geographically, Europe has become the area with the highest risk in the world for the first time. In 2025, Europe accounted for over 40% of known incidents worldwide, with France recording the highest number of attacks, surpassing the United States. In terms of financial impact, losses related to confirmed wrench attacks in 2025 exceeded $40.9 million, a year-on-year increase of 44%.
Jameson Lopp, Chief Security Officer of Bitcoin security company Casa, and a long-time tracker of physical attack incidents, maintains a database covering over 225 verified cases to date. This list grew at an unprecedented rate in 2025, and this data is also rapidly increasing in 2026.

Furthermore, due to a significant number of victims choosing to remain silent out of fear, privacy concerns, or distrust of law enforcement, the actual number of incidents is likely much higher. The victim group now far exceeds crypto elites, encompassing teachers, construction workers, firefighters, and their families.
Three Significant Cases in 2025
Case 1: Ledger Co-founder Kidnapped, Finger Amputated (France, January 2025)
In January 2025, David Balland, co-founder of the cryptocurrency hardware wallet company Ledger, and his wife were kidnapped from their home in the central French city of Vierzon and locked up separately. The attackers then sent a video of Balland's severed finger to another Ledger co-founder, Eric Larchevêque, demanding a ransom of 10 million euros in cryptocurrency.
After the elite French police force GIGN (National Gendarmerie Intervention Group) intervened, they successfully located and rescued Balland, while his wife was found hours later in a truck. Almost all of the ransom that had been paid was tracked, frozen, and confiscated. Ten suspects aged between 20 and 40 years were arrested, with prosecutors stating that if convicted, the involved parties would face life imprisonment.
Case 2: Paymium CEO's Daughter Attacked on the Streets of Paris (France, May 2025)
On the morning of May 13, 2025, the daughter of Pierre Noizat, CEO of the French cryptocurrency exchange Paymium, was walking on the streets of the 11th district of Paris with her young grandchild when she was intercepted by three masked men who attempted to forcibly push her into a van.
The attack occurred in broad daylight on a busy street, captured entirely by surveillance cameras. Noizat's daughter fought back fiercely, grabbing one of the guns and throwing it on the ground; bystanders quickly joined in, with one passerby picking up the gun and pointing it at the attackers, while another used a fire extinguisher to disperse them. The three assailants ultimately retreated in panic.
After the case escalated, French authorities launched an investigation centered on this attempted kidnapping, indicting a total of 25 individuals, including 6 minors. This detail sparked a significant amount of discussion in the French media about the "Mexicanization of France."
Case 3: Former American Police Officer Conducts Crypto Wrench Attack (Los Angeles, 2024-2025)
At the end of 2024, a former Los Angeles Police Department (LAPD) officer was found guilty by a jury for using physical coercion against cryptocurrency holders, forcing victims to move approximately $350,000 in Bitcoin. The peculiarity of the case lies in the perpetrator's law enforcement background—indicating he possessed professional knowledge of how to evade surveillance and implement coercion.
The conviction was widely cited in the crypto community as it shattered the assumption that "physical attacks only come from street criminals."
Why Are Crypto Holders Particularly Vulnerable, and What Can Users Do?
The key judgment in the CertiK report is that attackers are actively screening targets based on risk-reward analysis, prioritizing combinations of "high potential reward, low security defense." This logic has given rise to four typical target categories.
The most direct victims are retail investors who publicly disclose their asset holdings on social media, where on-chain balances can be checked, and security is nearly nonexistent. Industry executives and protocol founders represent higher value targets; although they typically have security, they are still exposed during travel or public activities. The third category consists of family members and close friends, who are often overlooked; criminals know well that when spouses, children, or elderly parents are controlled, the primary targets will bypass any safety protocols. Additionally, many family members often lack basic operational security training and have protection levels far below the main targets themselves. The fourth category is over-the-counter traders, where attackers disguise offline transactions as normal business meetings; once the victim displays proof of assets, they immediately implement abduction.
At the same time, monitoring tactics have evolved from human tracking to OSINT-driven digital footprint analysis; attackers may lock onto target vulnerabilities weeks before their actions. During the infiltration phase, impersonating couriers or utility workers remains the most effective penetration method, catching victims off guard psychologically. Once inside, they deploy Faraday bags and signal jammers to cut off network connections for devices, forcibly isolating victims from their families.
The era of purely relying on mnemonic phrases is over. Humans remain the most vulnerable single point of failure in the entire security system.
On a personal level, the critical first step is to establish a separation structure of "decoy wallet + core wallet." The decoy wallet needs to hold a reasonable amount of small assets; having too little can anger attackers and trigger further violence. In the event of coercion, it provides a negotiable exit, protecting core assets from being touched. Meanwhile, mnemonic phrases and signing devices must never be stored in the same location; ideally, mnemonic phrases should be stored in a bank safe rather than at home.
In everyday behavior, "do not flaunt" is the bottom line; avoid posting wallet addresses, asset screenshots, or travel arrangements on any public platform. Use a dedicated phone for travel, retaining only the minimum necessary account permissions, and avoid installing high-value wallet applications on everyday devices. High-value transactions should only be conducted on dedicated computers that are not brought outside.
For individuals and institutions holding large assets, the report provides two structural tools: multi-signature solutions (like 2/3 or 3/5) fundamentally eliminate the possibility of a single person being coerced to transfer funds; time-lock contracts impose forced delays on withdrawals exceeding a certain threshold, providing a window for external intervention.
In addition, CertiK has also listed three categories of warning signs to be alert for, including receiving unsolicited two-factor verification codes (which may indicate that an attacker has obtained your digital credentials and is testing responses); real-world anomalies, such as receiving deliveries for orders not placed and repeated harassment to confirm whether a residence is occupied; and acquaintances not contacted for many years suddenly reaching out and stressing the need for an in-person meeting. These three categories of signals recur in the case database but are seldom recognized as dangerous by the victims at the time.
This Is Not Just a Personal Safety Issue
Every time Bitcoin reaches a new all-time high, Jameson Lopp's database welcomes a batch of new entries. The correlation between price and violence has been tracked by him for nearly a decade.
The crypto industry has spent fifteen years solving private key security problems, building wallets, protocols, and multi-signature architectures that are increasingly difficult to hack. However, when attackers turn towards human beings, these technical defenses become virtually meaningless.
The sillytuna case remains controversial, but it raises a real question: As the transparency of crypto wealth becomes a selling point for the industry, does it also sketch out a hunting map for some individuals?
France has begun discussing whether a dedicated legislative framework is needed to address crypto ransom crimes, while law enforcement agencies in the UK, Singapore, and other regions are also updating safety guidelines for digital asset holders.
The next person forced by an axe might not be a billionaire. It could simply be an ordinary user with an on-chain balance visible to others.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。