Original Title: Quantum Isn't a Threat to Web3. It's an Upgrade.
Original Author: DAVID ATTERMANN
Translated by: Peggy, BlockBeats
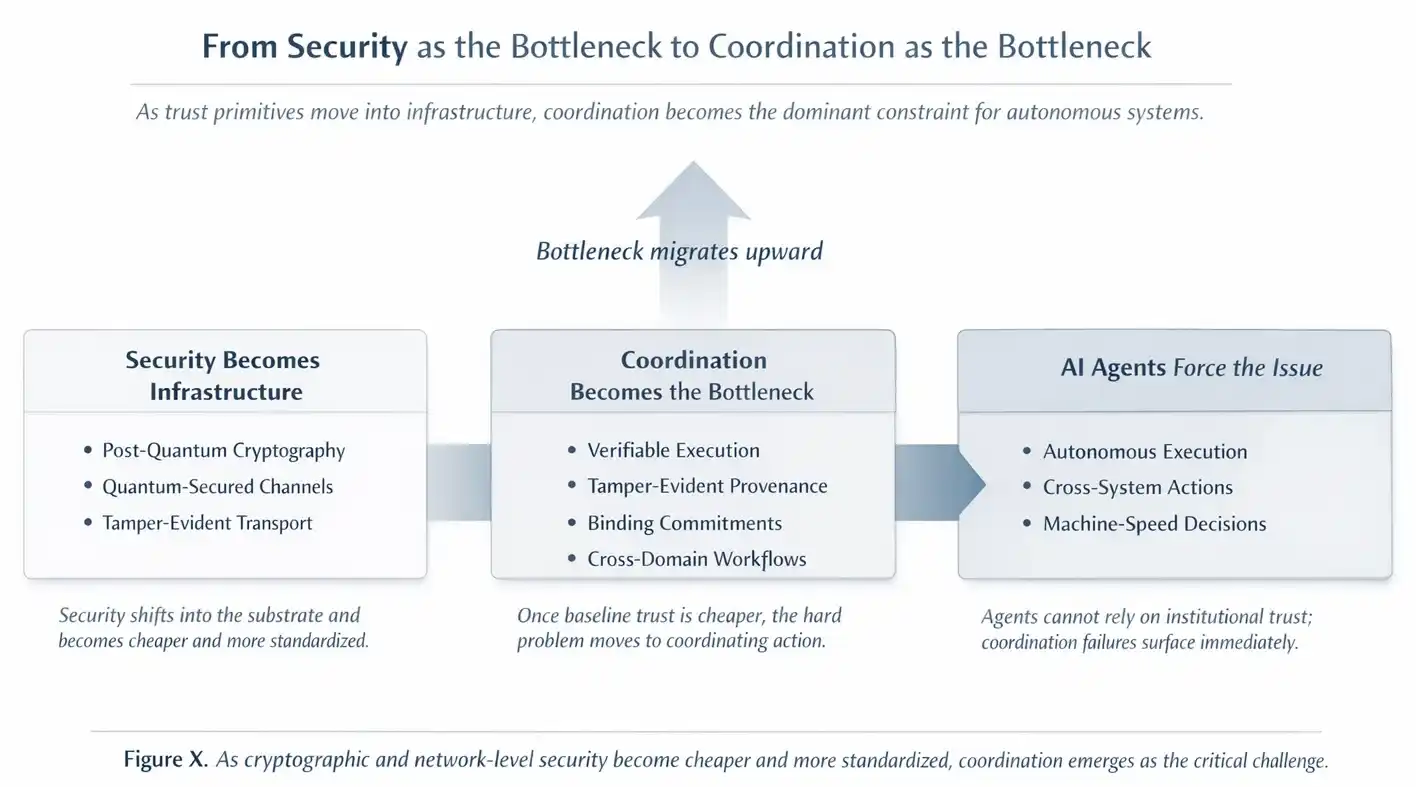
Editor's Note: Discussions around "whether quantum will destroy Web3" often neglect the real direction of change. This article points out that quantum is not a threat, but rather a migration of security infrastructure: strong cryptography, tamper-evident communications, physical-level randomness, and identity proofing are gradually sinking down as foundational capabilities. In this process, blockchain no longer needs to repeatedly "compensate" for untrustworthy network environments at the software layer, but can focus more on irreducible issues like governance, incentives, and cross-domain collaboration.
More importantly, the arrival of quantum coincides with the realization of autonomous AI systems in the real world. When security becomes part of the infrastructure, Web3 truly enters a mature stage, serving "autonomy, commitment, and coordination."
Below is the original text:
Mainstream debates around "whether quantum computing will kill Web3" actually misfire. Such phrasing turns the issue on its head. Quantum computing will not make digital systems less secure; instead, it will further embed security into deeper foundational infrastructure. As new cryptographic standards are gradually implemented, and new secure communication methods become viable, foundational security capabilities will become cheaper and more standardized across the entire Internet.
At the same time, AI systems are beginning to shift from "thinking" to "acting." When intelligent assistants evolve from merely answering questions to booking flights, transferring funds, and managing resources, the real challenge shifts. The question is no longer whether AI can generate good answers, but whether software can safely take actions between different systems and organizations that do not trust each other. Proving what AI has done, where data comes from, and what it is allowed to do is becoming the most critical constraint.
This is precisely the same fracture line that has delayed the realization of all similar JARVIS concepts. A helper that still requires continuous human approval when spending money, accessing sensitive data, or reallocating resources cannot claim true autonomy. Once real authorization is involved, if there is a lack of a verifiable, shared method to prove identity, authority, and compliance, so-called "autonomy" will immediately fail.
At this very moment, quantum computing reduces the cost of security when the issues of trust and collaboration become unavoidable.
1. What Quantum Really Changes (and What It Doesn't)
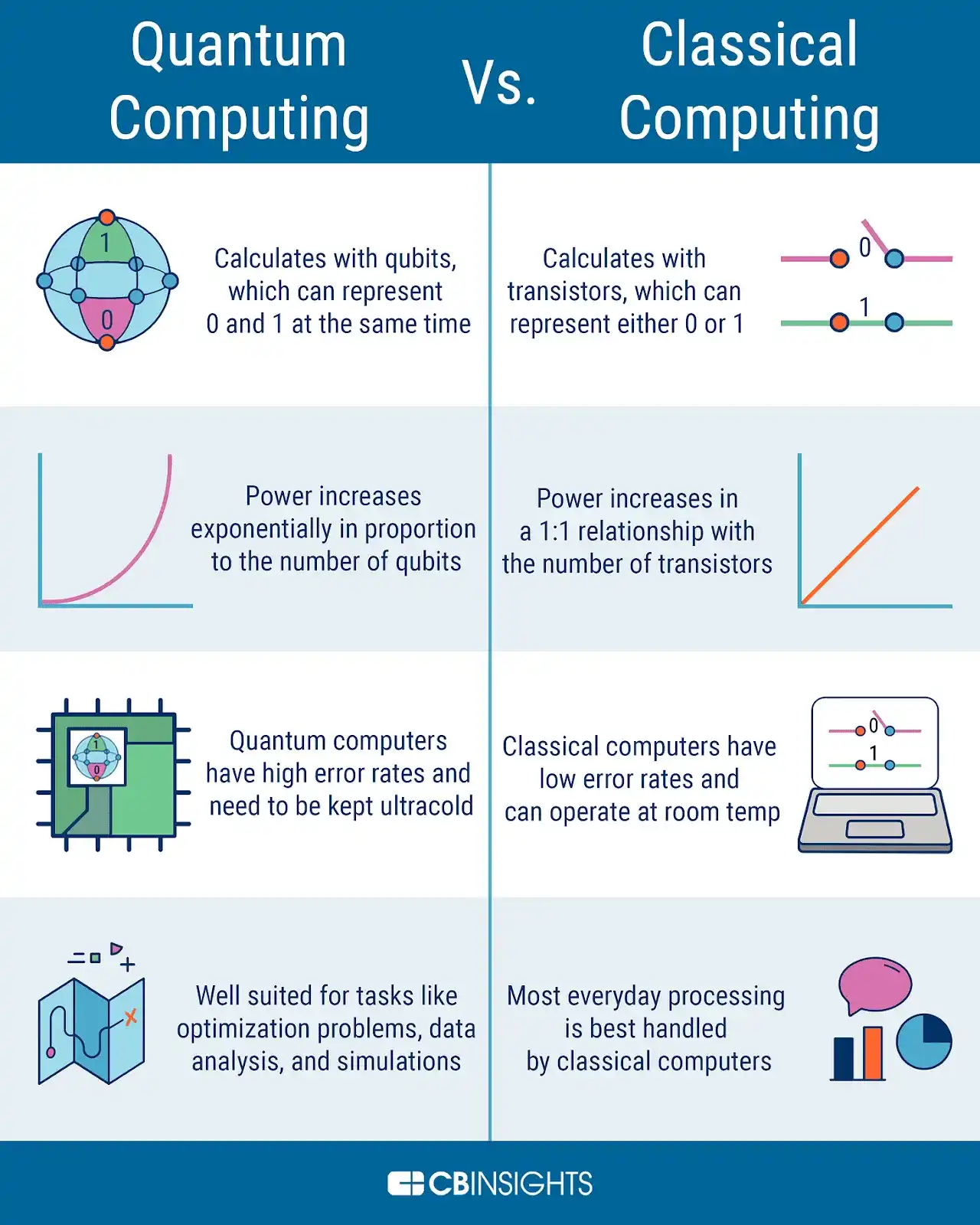
When people talk about "quantum," they typically refer to quantum computers. They are not "faster GPUs," but a class of machines that utilize quantum mechanics characteristics and can vastly outpace classical computers on certain specific problems.
What they excel at includes: factoring large numbers, solving discrete logarithm problems, and certain specific optimization and simulation problems.
What they do not excel at includes: general computing, running large software systems, replacing cloud computing infrastructure, and training AI models.
So, what will quantum computing really disrupt?
The answer is: part of today's public key cryptography. RSA and Elliptic Curve Cryptography (ECC) are built upon the types of mathematical problems at which quantum computers excel. This is significant because cryptography is not just the foundational primitive of blockchain; it is the trust bedrock of the entire Internet—login mechanisms, digital certificates, signatures, key exchanges, identity systems, all rely on it.
The real uncertainty lies in the timeline, not the direction. Most credible assessments suggest that quantum computers with "cryptographic destructive significance" will take another 10-20 years to emerge, but no one can completely rule out faster advancements or some kind of "quantum leap" breakthroughs.
The Most Immediate Risk: Harvest Now, Decrypt Later
The most pressing risk related to quantum is not that the global security system will suddenly collapse one day, but the so-called HNDL (Harvest Now, Decrypt Later).
Attackers could easily start recording encrypted communications and data today, then decrypt that historical data when quantum computing capabilities mature in the future.
This pattern presents long-term exposure risks for the following types of information: government and defense communications, corporate intellectual property and trade secrets, medical data and personal privacy records, legal and financial archives.
For this reason, post-quantum cryptography is being taken seriously by governments, cloud service providers, and regulated industries today. Data transmitted today often needs to remain confidential for decades; once you assume "it will certainly be decrypted in the future," the existing security promises effectively become null and void.
This is a Migration of Security, Not a Systemic Collapse
Post-quantum cryptography does not require quantum hardware. It is fundamentally a software and protocol-level upgrade covering TLS, VPNs, wallets, identity systems, and signature mechanisms. This does not occur on a specific "switch day," but as a gradual infrastructure migration process similar to IPv6—slow, uneven, but unavoidable.
This change will have a far greater impact on enterprise and national infrastructure than on blockchain itself. Blockchain is inherently a public system, and the real core secret that needs protection is the private key, not historical transaction data. For Web3, quantum computing does not bring a survival crisis, but rather the question of the cryptographic upgrade path, and not a total reboot of the entire system.
This shift is already visible in the mainstream ecosystem. The Ethereum Foundation recently elevated post-quantum security as a core protocol-layer priority, initiating special research and testing environments around quantum-resistant signatures, account models, and transaction mechanisms. This marks a shift from anticipating "a future issue" to recognizing "an ongoing infrastructure migration," even though truly large-scale quantum hardware has not yet emerged.
2. The Most Overlooked Change: Network Layer Changes
If quantum computing focuses on the mathematical foundations for protecting keys, then quantum communication focuses on the trust model of the network itself.
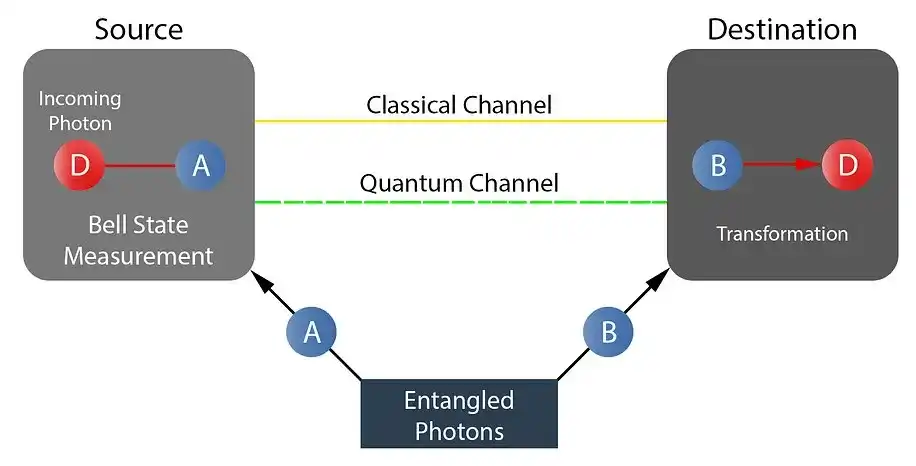
Quantum communication does not mean sending application data "through a quantum computer." Although it has various implementations (which will be elaborated later), the core application in reality is Quantum Key Distribution (QKD): using quantum states to establish a tamper-evident communication channel. The messages themselves remain classical data, still encrypted; the real change is that any silent eavesdropping will be detected on a physical level.
This is not a faster network but a network trust mechanism that cannot be quietly penetrated.
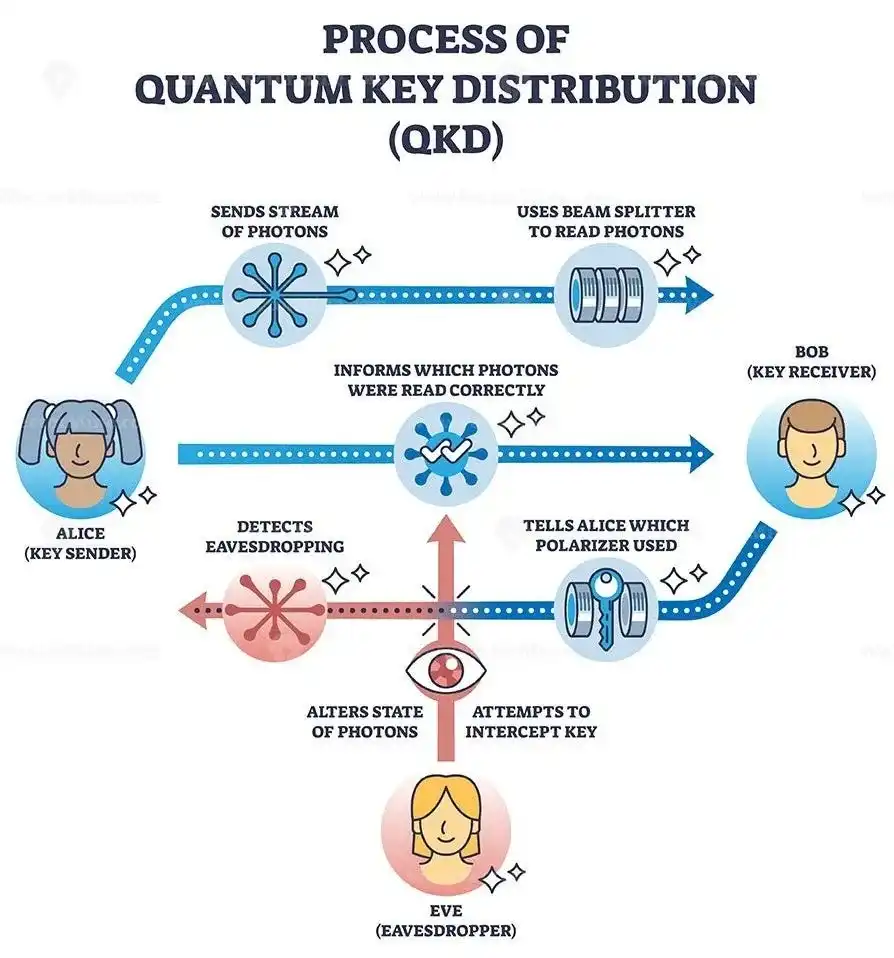
Some quantum properties cannot be duplicated nor observed without producing disturbances. When these properties are used to generate cryptographic keys or verify communication channels, intercepting actions are no longer "silent." Once someone tries to eavesdrop, the act of observation itself leaves detectable traces.
Why This Will Change System Design
This is significant because a large portion of the current defense architecture in Web3 is built on a premise: that network channels are hostile and invisible.
Traffic can be quietly intercepted; man-in-the-middle attacks are difficult to detect; trust at the network layer is extremely weak.
Therefore, upper-layer systems must "overcompensate" through replication, verification mechanisms, and economic security designs.
If the infrastructure layer itself embeds guarantees of channel integrity, quantum communication is actually lowering the cost of maintaining channel security. This is often overlooked in mainstream narratives of "quantum destructionism."
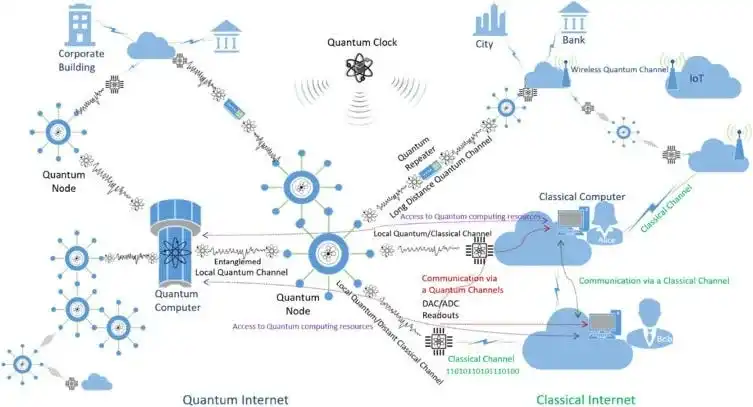
Will It Really Scale?
Similar to quantum computing, widespread adoption of Quantum Key Distribution (QKD) may still take 10-20 years. However, the possibility of a sudden compression of the timeline cannot be ruled out—especially with breakthroughs in quantum repeaters, satellite networks, or integrated photonics technologies.
3. The Trust Dilemma of Autonomous Systems
Quantum drives a security migration across the Internet. Over time, strong cryptography and tamper-evident communication channels will become part of the infrastructure, rather than differentiated capabilities.
But what truly makes "collaboration" a core bottleneck is the rise of autonomous AI agents.
Autonomous systems cannot rely on informal trust or institutional shortcuts like humans do. They default require:
Verifiable execution: You cannot simply trust an agent's claim of what it has done; proof must exist.
Coordination mechanisms: Workflows among multiple agents require a neutral shared state carrier.
Data provenance: When synthetic data and adversarial data flood in, provenance verification is crucial.
Commitment mechanism: Agents must be able to make binding commitments that other agents can rely on.
A quantum network does not directly solve coordination issues, but it will "commoditize" security capabilities at the foundational level. When security becomes part of the infrastructure, more coordination can happen off-chain with stronger guarantees, identities and memberships will be more aligned with the underlying network structure. For certain types of workflows, global broadcast replication will no longer be necessary. Blockchain will begin to shift from a "pure broadcast system" to a coordination foundation for autonomous systems.
4. Cutting-Edge Quantum Primitives
The following content represents long-term possibilities, assuming quantum networks can emerge from niche applications and achieve scalability. Once realized, they will enhance underlying security guarantees and open new protocol design spaces. Similar to QKD, the significance of these primitives lies in releasing resources for the "coordination bottleneck."
Some of these are closer to realistic production environments, while others are more like architectural signals of future trust mechanism evolution.
First Level (0-10 Years)
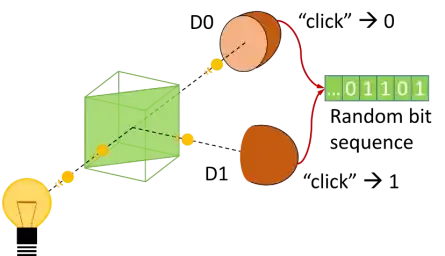
Physically enforced randomness: Random number generation is directly constrained by physical processes, difficult to predict or manipulate.
Unclonable identity and proof mechanisms: Identity and authentication methods based on physical characteristics that prevent copying and forgery.
Second Level (10 Years and Beyond)
Time synchronization as a first-class primitive: Time will no longer be merely a system parameter but a verifiable foundational capability.
Verifiable state transitions: State changes across systems can be directly proven by underlying mechanisms.
Third Level (Research Frontier, High Uncertainty)
Entanglement-based coordination primitives: Establish new collaborative structures using quantum entanglement.
Minimal trust cross-domain communication mechanisms: Achieve message transmission between different trust domains with almost no additional trusting assumptions.
Overall, quantum is not a force to "destroy Web3" but a force driving the upgrade of security infrastructure. When the cost of security declines, the true bottleneck will no longer be cryptography, but how to reliably coordinate autonomous systems in untrustworthy environments.
1. Verifiable state transition
From "software-enforced scarcity" to "physical-layer unclonability"
In today's blockchain systems, unclonable ownership is achieved through network consensus. Scarcity is a rule maintained through a protocol that is upheld by the replication and consistency of numerous nodes. The existence of the ledger is largely to ensure that the same state cannot be copied or double-spent.
Quantum teleportation introduces a completely different primitive: states can be transferred, but cannot be copied during the transfer process and will be "consumed" at that moment. In other words, unclonability no longer entirely relies on software and protocol constraints, but becomes a property of the physical layer itself.
Why is this important? How will it change system design?
Hardware-backed custody: Regulated bearer instruments, sovereign-level credentials, or physical assets in the real world whose control can be bound to unclonable states with hardware proof capabilities.
Lower trust assumptions for asset anchoring: Some mechanisms for bridging real-world assets can rely on physical layer unclonability, without entirely depending on committees, multi-signatures, or purely social trust.
Protocol simplification: Part of the guarantees for scarcity are embedded deeper within the matrix, reducing complexity in protocols that are only used for "anti-copying."
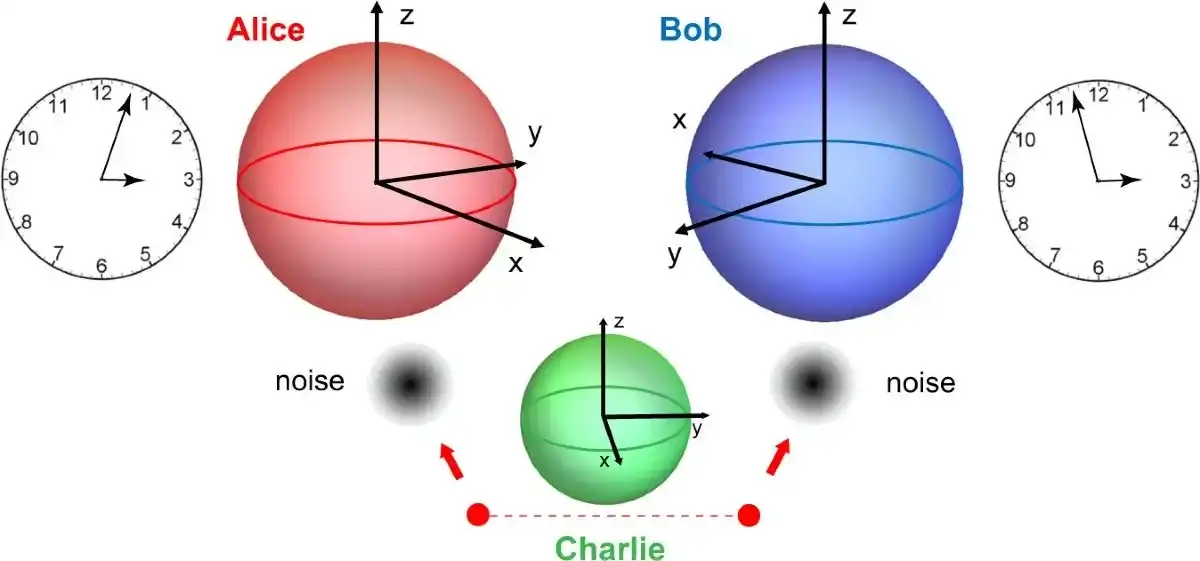
2. Entanglement as a trust primitive
Blockchains resolve conflicts by globally replicating states and using consensus mechanisms, thus achieving coordination. Cross-domain interactions often rely on heavy validation processes or trusted relays; sequencing is often determined retrospectively through blocks and finality.
Quantum entanglement introduces another primitive: establishing shared relationality without a central coordinator. It enables participants to establish consistency or alignment of attributes at an earlier stage without exposing the underlying data itself.
From this perspective, entanglement is not "faster consensus," but a mechanism that creates trust constraints at the front end of the pipeline, opening new design spaces for future cross-system, cross-domain collaborations.
Why is this important, and how will it change system design:
Earlier synchronization: Sequencers can establish a consistent view of the "ordering commitment" before final settlement.
Cleaner cross-domain alignment: Multiple domains can prove they observed the same event stream without relying on a single relayer.
Reducing overcompensation at higher levels: Some "alignments" can be established before requiring heavy global adjudication, thus lowering the additional reinforcement costs for high-level protocols amid hostile networks.
4. Physically enforced randomness
From gamed random beacons to unpredictability backed by physics. Randomness underpins validator selection, block producer elections, committee sampling, auctions, and various incentive mechanisms. Today's random numbers are mostly constructed at the protocol layer, hence there still exists room for manipulation or bias in edge cases.
Quantum processes can generate randomness that is unpredictable and cannot be biased under physical assumptions.
Why is this important, and how will it change system design:
Cleaner committee and proposer selection: reduces the attack surface for subtle manipulation strategies.
Fairer sorting and auctions: diminishes the gains of adversarial "timing" strategies, making the system less sensitive to timing games.
More robust mechanism design: incentive structures become harder to game at the "randomness layer."
5. Unclonable identity and proof
From "keys as identity" to "devices as identity." In today's Web3, identity almost equates to "holding a certain key." Sybil resistance primarily relies on economic costs or social heuristics. Node identities are also mostly only loosely anchored at the software level.
Quantum states cannot be copied. Combined with hardware attestation, it could enable unclonable device identities and stronger remote proofs: proving that a message or computation indeed originates from a specific physical endpoint.
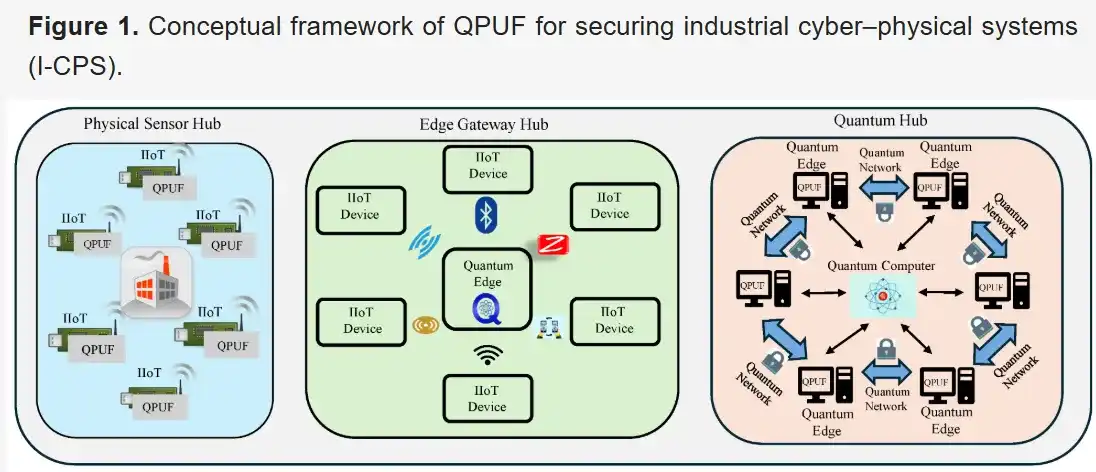
Why is this important, and how will it change system design:
Stronger endpoint guarantees: messages and execution claims can be bound to specific physical environments.
Reducing trust surfaces for relayers and oracles: proving capabilities are closer to hardware, rather than relying solely on software identity and claims.
More reliable verifiable computation: execution provenance becomes harder to forge.
6. Making time synchronization a first-class primitive
From "soft clocks" to "protocol-level time." The way blockchains handle time is fundamentally a soft assumption. Slot timing and ordering have exploitable aspects, and slight advantages in latency can drive MEV. Quantum-enhanced clock synchronization allows for tighter time coordination over long distances.
Why is this important, and how will it change system design:
Fairer block production windows: reducing latency asymmetry, thus limiting certain frontrunning strategies.
Cleaner cross-domain settlements: tighter time windows reduce race conditions.
More stable ordering: protocol timing becomes less sensitive to network jitter.
7. Minimal trust cross-domain collaboration
From "committees everywhere" to "physically-backed message passing." Cross-chain safety remains one of Web3's biggest operational risks. Bridges rely on committees, multi-signatures, relayers, and oracles—each adds to the trust surface and potential failure modes.
As entanglement and tamper-evident channels gradually mature, different domains can prove they observed the same set of commitments or event streams with fewer social trust assumptions.
Why is this important, and how will it change system design:
Smaller trust sets for bridges: closer verification to the underlying layer reduces catastrophic failure modes.
Cleaner multi-domain ordering: eliminates the need for centralized operators, making it easier to establish shared orders.
Security migrating down the stack
Today's blockchains need to "simulate" scarcity, randomness, identity, ordering, and cross-domain messages at the software layer because the underlying network and hardware are assumed to be untrustworthy. Quantum networks push parts of authenticity, unclonability, tamper detection, randomness, and synchronization into the foundational infrastructure matrix.
This is similar to past infrastructure developments: TLS brought cryptography into the network layer; TEE brought trust into hardware; secure boot introduced integrity into the firmware layer.
Blockchain will not become obsolete; it will no longer bear the heavy burden of repetitively implementing every kind of trust primitive in software, but will focus more on those problems that cannot be eliminated: governance, incentives, collusion, and adversarial shared states.
5. Objections and Real-World Constraints
Even if quantum-secure networks are limited to a few strategic corridors, this alone is sufficient to reshape the standards and design assumptions of the entire technology stack. High-trust communications do not need to be "accessible to the whole network" to impact the way systems are constructed: as long as a portion of the network defaults to providing tamper-evident channels, threat models will migrate upstream, and foundational security assumptions will begin to change more broadly.
In reality, quantum-safe communications remain expensive, fragile, and limited in coverage. The difficulty of hardware deployment and maintenance, alongside poor integration with existing internet infrastructure, poses challenges. For many use cases, relying solely on post-quantum cryptography may already be sufficient, thus quantum-safe links are more likely to concentrate in high-value environments: government networks, financial infrastructures, and critical national systems.
This will ultimately form a mixed trust landscape: certain corridors will have stronger default guarantees while the open Internet remains hostile.
This uneven rollout will not undermine the architectural shift; it will merely present it in a "skewed" form.
6. How Systems Will Adapt Over Time
Major infrastructure changes rarely happen "all at once." Changes in system design often precede the widespread adoption of new technologies, especially in the domain of security. Once new standards are adopted and early deployments emerge, builders will begin to assume a new baseline, even if the infrastructure rollout is still uneven.
A more realistic evolution path is roughly as follows:
Next 5 Years: Commoditization of Security Capabilities
Post-quantum cryptography will gradually spread among cloud service providers, enterprises, and regulated industries. "Quantum safety" will become part of the default security checklist rather than a unique selling point. Early quantum-safe network links will appear in high-value scenarios such as finance, government, and critical infrastructure.
Even if these upgrades are not universal, they will begin to shape the way systems are built: teams will assume a stronger baseline for network and cryptographic layers, directing more attention to how systems interact, coordinate actions, and enforce rules among untrusting participants.
5-10 Years: Shift in Design Assumptions
As stronger security primitives become standard, systems will no longer need to undergo heavy over-engineering to deal with hostile networks and weak cryptography. Underlying platforms will begin to integrate execution integrity, hardware proof, and verification tools—components that were once considered "advanced features."
At this stage, changes will be more about "how people think about system design" rather than the infrastructure itself. Builders will start designing systems for a world where "default security holds," with real complexity shifting to: how systems interact, how permissions are enforced, and how cross-boundary actions are coordinated.
Over 10 Years: Infrastructure Catching Up with Design Paradigms
Quantum-safe channels and tamper-evident communications will become more common in major financial centers, government networks, and key corridors. By then, most modern systems will have already been designed under stronger security assumptions while infrastructure finally catches up to the design models that emerged years ago.
Quantum: The Next Phase of Driving Autonomy
Viewing quantum as a threat to Web3 is fundamentally misguided. Quantum appears more like an accelerator: arriving simultaneously with autonomous AI systems as they begin to enter the real world.
It pushes security primitives into the infrastructure layer. Strong cryptography, tamper-evident channels, and execution integrity become cheaper, more standardized, and no longer a differentiating advantage. This reduces the underlying "trust costs," releasing new design space to build the primitives that AI agents genuinely need to have real power: verifiable execution, enforceable permission boundaries, and commitments that can be bound between systems without shared trust.
Quantum will not kill Web3; it will force Web3 to grow.
When security becomes part of the infrastructure, what remains is the truly tough problem—also the issue Web3 initially set out to solve: establishing autonomy, commitment, and collaboration in inherently untrustworthy systems.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




