On March 31, in the timezone of UTC+8, a supply chain attack that seemed to belong solely to engineers' workstations unfolded almost simultaneously with a shocking Asian financial drama on traders' screens. OpenClaw was reported to be involved in an npm ecosystem attack, where the core dependency axios had malicious versions, triggering a new wave of security panic in the developer community. Meanwhile, stock indices in Japan and South Korea recorded the most severe monthly declines since 2008, with the Nikkei 225 index dropping approximately 13.2% and the KOSPI index about 19.1%, alongside significant volatility in the yen, collectively compressing the global risk appetite for assets. Caught between a technological black swan and a macroeconomic storm, the cryptocurrency industry had to reevaluate how to find a new balancing path across the three battlefields of development toolchains, trading systems, and asset allocation.
Chain Reaction of Poisoning for OpenClaw
On March 31, the founder of Slow Fog, Yuxian, was the first to issue a warning about the OpenClaw supply chain attack, elevating a risk that was initially confined to the engineering sphere to a broader security discussion. He specifically pointed out that tools like OpenClaw, which integrate security and development assistance capabilities, are becoming a concealed pathway for attackers to “intrusively invade” projects. As the warning spread, market attention quickly focused on one of the fundamental network request libraries in the npm ecosystem, axios.
According to publicly disclosed information, malicious versions 1.14.1 and 0.30.4 of axios were identified, allegedly contaminating the dependency chain, including plain-crypto-js. This means that the attackers were not directly targeting a specific CEX or DeFi contract, but instead, were trying to leverage a “basic screw” deep within the toolchain to pry open the entire application and security links. Since relevant technical details are still being disclosed, the Slow Fog team has only provided a qualitative assessment — “it represents a supply chain attack with a substantial impact,” suggesting that its potential reach far exceeds individual projects.
In this phase where information is not fully transparent, the trust boundaries of the developer community in third-party dependencies are put to the test. The “default trust + rapid iteration” culture of the npm ecosystem reveals its vulnerability: once an upstream package is poisoned, dependent projects may be passively drawn in without sensing a thing. For developers in the cryptocurrency industry, this incident forces a pause, compelling them to reassess whether they have implemented sufficient auditing and isolation mechanisms when using public infrastructures like npm and GitHub.
From a Line of Code to Chain-wide Infiltration
The danger of tools like OpenClaw lies in their deep integration into CI/CD pipelines and daily security inspection processes. Once they are contaminated, malicious logic can seep down through automated building, testing, and deployment processes, ultimately embedding itself into the front end, back end, or even script operations of the project. This “pipeline-style diffusion” gives a single altered line of code an amplifying effect capable of infiltrating the entire business chain.
In the cryptocurrency world, front-end DApps, backend services, script tools, and monitoring services are generally highly dependent on foundational network libraries like axios, which are responsible for requesting nodes, invoking exchange APIs, and processing on-chain data. Once these foundational packages are “swapped out,” the attack radius is no longer just a specific functional module but extends to the entire project and the external interfaces where users interact. The risks extend beyond data leakage and could evolve into profound manipulation concerning on-chain signatures, transaction constructions, and asset transfers.
In response to this supply chain incident, Yuxian proposed a remarkably timely suggestion — “Use prompts to allow Agents for self-checks and comprehensive inspections.” This acknowledges the reality that manually checking each package is unfeasible and emphasizes the value of automated audits in supply chain defenses: as dependency trees become too complex for the human eye to exhaustively inspect, prompt-driven auditing Agents can serve as the first line of anomaly screening.
In the long term, such events may likely propel exchange and wallet teams to accelerate the construction of private image repositories and whitelist dependency frameworks. Locking core dependencies within self-built repositories for unified auditing, signing, and distribution, and subsequently restricting external packages that can be introduced into pipelines through a whitelist mechanism, is shifting from a “compliance option” to a “survival prerequisite.” The pace at which the cryptocurrency industry advances on this path largely depends on the destructive power of the next similar poisoning event.
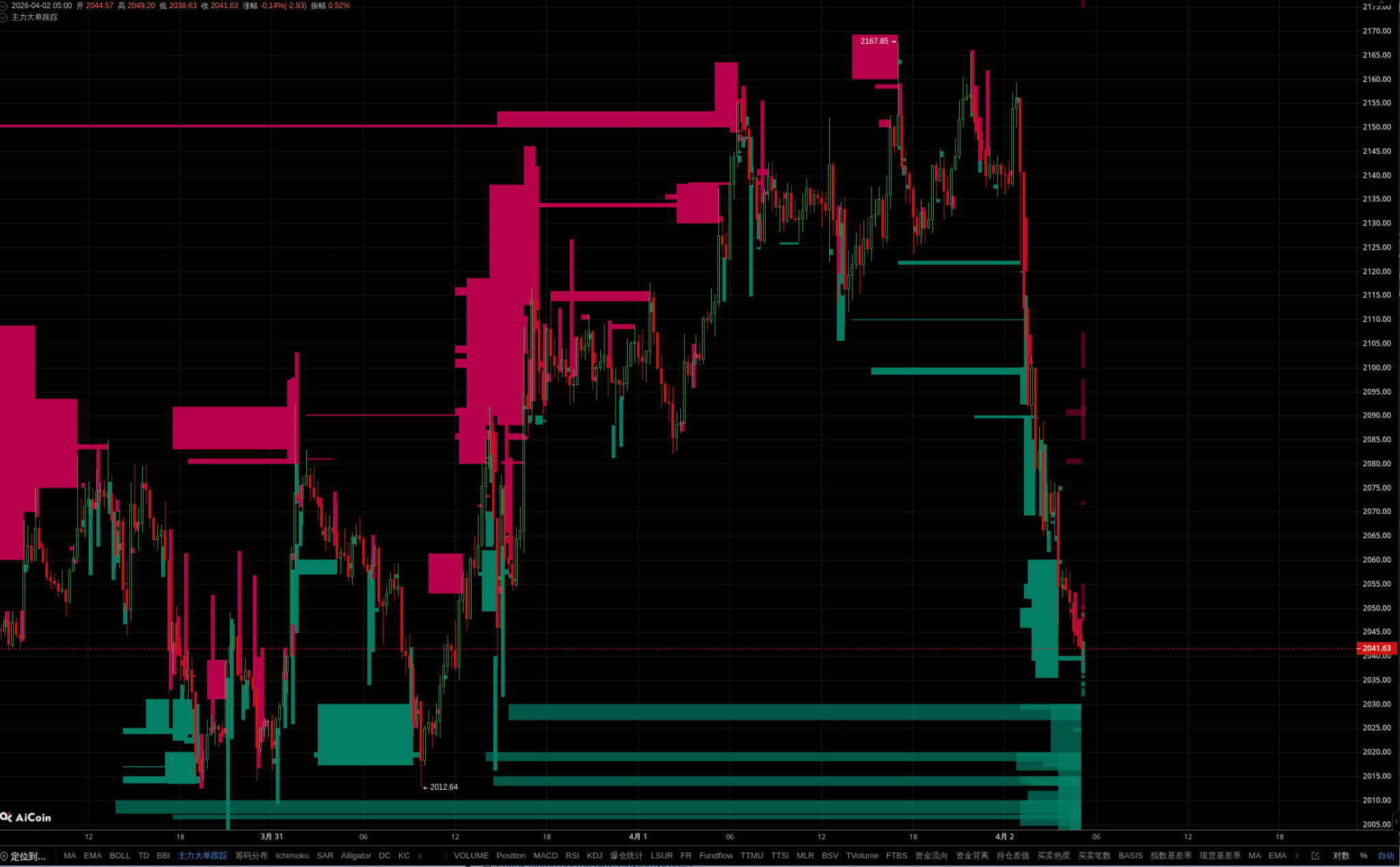
Nikkei's 13% Plunge and Korean Stocks' Heavy Decline Echo
On the same day as the supply chain attack, a macro market event took center stage in the Asian time zone — a stock market crash-level monthly correction. Data showed that the Nikkei 225 index fell by approximately 13.2% in a month, marking the largest single-month decline since the 2008 financial crisis; the South Korean KOSPI index plummeted by around 19.1%, indicating more severe selling pressure and liquidity exit. This was not just a technical correction for regional stock markets, but rather a concentrated repricing of global funds regarding expectations for Asia's growth and risks.
On the monetary level, upheaval further amplified this pressure. Market expectations for further depreciation of the yen rose, coupled with escalating geopolitical conflicts — for instance, incidents like the Iranian attacks on ships, which continuously boosted safe-haven sentiment. In macro trading, whales heavily built long positions in USD/JPY, becoming a barometer on trading desks: within their narratives, Asian currencies and stock markets are under structural pressure, while the dollar and safe-haven assets are poised to benefit amid volatility.
For cryptocurrency assets, this backdrop of “double killing” in stocks and currencies directly compresses the upward momentum of high Beta assets. The violent adjustments of the Nikkei and KOSPI are not merely a representation of regional market candlesticks but signal a re-evaluation of the “Asia factor” in the pricing model of global risk assets. Traders begin to reassess whether their cryptocurrency positions are closer to “tech growth” or if they have indeed become another form of high-leverage risk exposure.
Resonance of Technological Black Swans and Macroeconomic Storms
On a technical level, the OpenClaw supply chain attack is aimed at the layer of “weak middleware” behind exchange risk control systems and on-chain infrastructure. Even though the current incident primarily focuses on development tools and libraries, the market has begun to ask: if such supply chain attacks were to further approach core modules like matching engines, address risk controls, and on-chain monitoring, would it amplify systemic risks under extreme market conditions? On a day like March 31, where both stocks and currencies plummeted, any technical stumbling block could potentially evolve into a real financial stampede.
On a macro level, the simultaneous downturn of Asian stocks and currencies has created a clear trend in capital: demand for safety and value preservation is converging towards gold and gold-linked assets. The cryptocurrency market quickly provided a product-level mirrored feedback — Binance added XAUT as a collateral asset, which responds to users' needs for “gold substitutes” on-chain; while HTX launched EDGE trading, capturing another end of the demand: some traders wish to seek segment gains through highly volatile and more instrumental assets amid severe fluctuations.
In this process, leading platforms began to intentionally strengthen the narrative of “security and transparency,” such as through product upgrades like OKX Planet, showcasing their capabilities in security infrastructure, risk disclosure, and data visualization. This posture essentially signals to the market that at the intersection of technological black swans and macroeconomic storms, platforms not only need to provide tools for hedging or leverage but must also prove that they form the “protective layer that will not be easily torn apart by storms.”
The Dual Dilemma of Developers and Traders
For development teams, the reality after March 31 is fractious. On one hand, they must quickly mobilize to inspect project dependency chains, assess risks, and even temporarily isolate components involved with axios, OpenClaw, and their surrounding ecosystem; on the other hand, the tool stack cannot be completely replaced in the short term — CI pipelines, monitoring scripts, automated deployments, internal security scans, and other processes are deeply coupled with the existing ecosystem, and any radical switch could bring about new stability issues. Finding a balance between “immediate damage control” and “uninterrupted production” has become an unavoidable decision for technical managers.
Traders, on the other hand, face a dilemma reflected in asset prices and volatility. Confronted with adjustments at the stock market crash level and dramatic fluctuations in the yen, they must reassess whether to continue embracing high Beta cryptocurrency assets, viewing this wave of selling pressure as “an opportunity after liquidity reshuffling”; or choose to withdraw some positions, shifting into collateral or other safe-haven assets represented by XAUT, maintaining capital and leverage safety boundaries within a narrower volatility range.
Platforms find themselves in a similarly awkward position: on one hand, they strive to accommodate users’ diverse needs for hedging and speculation by adding new collateral, launching highly volatile trading pairs, and providing more flexible leverage tools; on the other hand, they must utilize more frequent security announcements, disclose dependency lists, and share third-party audit results to prove to the market that they have not been caught in the undercurrents of this supply chain attack. Any “unclear” gray areas could be exponentially amplified amid panic.
When the crisis of technical trust resonates with macroeconomic panic, market participants' decision-making processes undergo structural changes: they rely more on real-time intelligence, security reputation, and verifiable data. Those who can quickly present comprehensive dependency inspection reports, those who can explain their exposure to malicious versions of axios in real-time, and those who can provide clear risk limit guidance while the Nikkei and KOSPI are plummeting — all contribute to subtly reshuffling the hierarchy of trust in the industry.
Where Will the Next Chain Reaction Be Triggered?
The OpenClaw incident has provided a clear warning: the most basic and “taken for granted” development dependence is becoming a new entry point for attackers. Long-term defensive thinking must shift from “protecting business entry points” to “strengthening the roots of tools,” expanding from merely watching contracts and hot wallets to auditing the entire CI/CD and third-party ecosystem's supply chain security. For the cryptocurrency industry, every npm package and every automated script is no longer neutral; they all represent potential attack surfaces.
The Japanese and South Korean stock indices have plummeted by 13.2% and 19.1% respectively within a month, alongside intense fluctuations in the yen, showcasing another chain reaction pathway: regional risks can transmit globally to the pricing models of cryptocurrency assets within a very short period, through the interconnections of stock markets, currency markets, and safe-haven assets. Those financial news pieces that seemed only related to Tokyo or Seoul are reshaping the risk premium structure of Bitcoin and on-chain derivatives through capital curves.
At the intersection of these two pathways, exchanges and security teams will be compelled to incorporate supply chain audits and macro risk controls into the same emergency plan: an npm ecosystem poisoning could magnify during periods of macro vulnerability into a systemic event; a regional stock market crash could trigger cascading liquidations if infrastructure is breached. Security and risk control are no longer isolated departments but represent a network of correlations that needs unified modeling.
The real advantage in the future will belong to those participants who can quickly identify vulnerable links and convert black swan events into “hedgeable known risks” early on. Whether through automated Agents deeply inspecting dependency trees or through cross-market data models detecting anomalies in Asian stocks and currencies beforehand, these capabilities ultimately point towards one goal: allowing more unexpected events to be quietly digested as “risk factors incorporated into pricing” before they occur.
Join our community, let’s discuss and grow stronger together!
Official Telegram community: https://t.me/aicoincn
AiCoin Chinese Twitter: https://x.com/AiCoinzh
OKX福利群: https://aicoin.com/link/chat?cid=l61eM4owQ
Binance福利群: https://aicoin.com/link/chat?cid=ynr7d1P6Z
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。