Written by: Vaidik Mandloi
Translated by: Block unicorn
Introduction
Have you ever opened Etherscan and searched for your wallet address? Not to check transaction history, but just to see what it looks like from the outside?
Your current balance. Every token you have ever held. The NFTs you have purchased. The protocols you have interacted with. All those DeFi experiments conducted late at night. Every airdrop you have claimed and ignored.
Everything is there, and it is public.
Now, imagine sending this address to a freelancer who wants to pay you, or to a decentralized autonomous organization (DAO) that is granting you funding, or even to someone you just met at a conference. You are sharing not just where the funds are going, but your complete on-chain financial record.
This is because Ethereum, like most blockchains, is designed such that each address acts as a public ledger.
Most of us have felt this friction. Before pasting a wallet address, we all hesitate slightly. Some people even create a "new wallet" specifically to receive payments. Others will move funds around first to avoid leaking too much information about their balance. This instinctive reaction is not unique to cryptocurrency users. A 2023 survey by Consensys of 15,000 people worldwide found that 83% prioritize data privacy, yet only 45% trust current internet services to protect their data.
ERC-5564 aims to address this specific issue of address traceability. It introduces stealth addresses natively into Ethereum—this standard allows users to receive funds without exposing their main wallet every time.
In this article, I will technically dissect what ERC-5564 actually introduces, how stealth addresses work in practice, and where Ethereum stands in comparison to privacy-first chains and existing privacy tools.
What ERC-5564 Actually Introduces
If the problem lies in a single address permanently recording everything you do, then the most obvious question is: why does Ethereum require the reuse of the same address?
Think about how you receive money in the real world.
If someone wants to pay you via bank transfer, they ask for your bank account number. This account number does not change with every transaction. Over time, your bank account records your income, spending patterns, and saving behavior. The difference is that only you and your bank can see the complete transaction history.
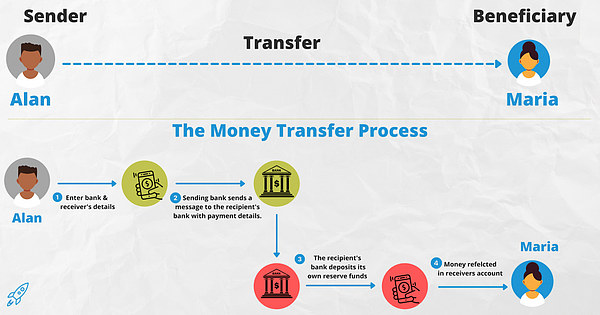
On Ethereum, your wallet address plays the exact same structural role. It serves as a persistent account in the global state of the network. When someone wants to send you money, they need your address. This address is permanent. Every payment goes there, and every interaction updates the same account. Over time, all activities accumulate under a visible identifier.
Researchers refer to this structural issue of classifying transaction activities under the same identifier as the “Glass Bank Account” problem. The problem is not that transactions are visible, but that they are automatically linked to a fixed address that rarely changes.
In the early days of cryptocurrency, this classification method revealed little information beyond basic transfer functionality. However, blockchain development has never been limited to transfers. They have evolved into lending markets, NFT platforms, governance systems, payment layers, and identity authentication layers. Today, a single address represents far more than it did a few years ago.
A common analogy used in privacy research helps explain this point.
Imagine playing a strategy game on the blockchain like Battleship, where every move is publicly visible. The rules still function correctly, and the system accurately records every action. However, once both players can see the position of every ship, the strategy disappears, as there is no longer any uncertainty.
The system operates perfectly as designed, but the experience changes because the transparency eliminates the sense of separation.
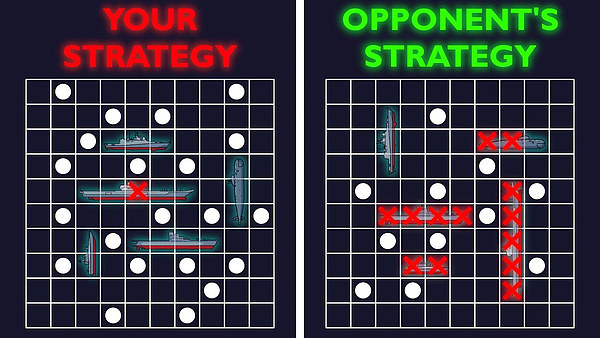
Financial coordination follows a similar logic. Not every payment needs to disclose the entire history associated with a particular address.
Even Satoshi recognized the privacy limitations of Bitcoin's transparency and explored ways to improve it. The challenge at that time was how to enhance privacy without introducing complexities that could undermine verification. There were no viable solutions that could balance both aspects.
Ethereum inherited this transparency and built a robust account-based model on top of it. ERC-5564 does not attempt to remove Ethereum's transparency, nor does it introduce technical details such as cryptographic balances or shielded pools. Instead, it focuses on a more specific, practical issue: reducing the automatic traceability of the receiving layer.
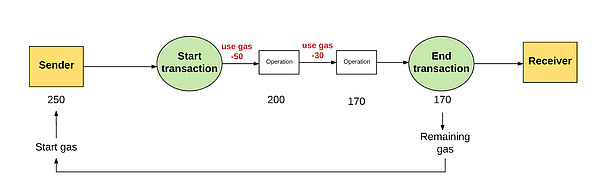
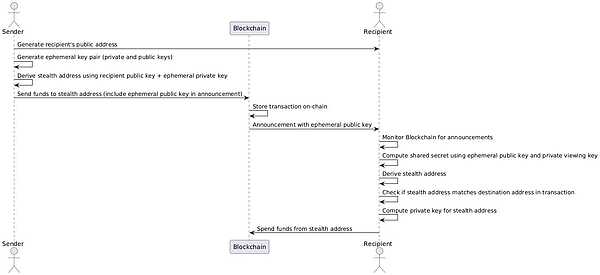
The core idea of ERC-5564 is very simple. You do not need to provide your wallet address directly; rather, you provide a stealth meta-address. This meta-address is not a destination address; it contains public cryptographic information that allows the sender to generate a unique receiving address for you.
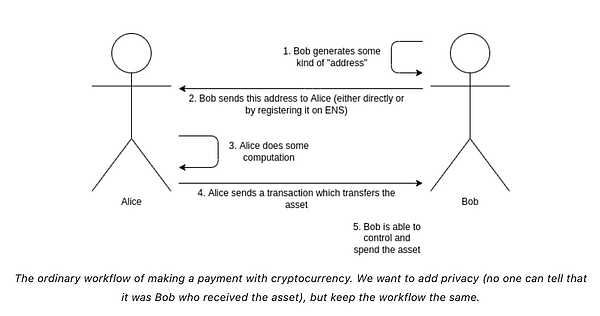
So, when someone pays you, they do not send money to your known wallet address. They generate a brand new address specifically for that transaction. On-chain, the money appears to be sent to a completely new account that has never been used before.
From the network's perspective, everything operates as usual. Transactions are processed the same way as other transactions. The difference is that each payment arrives at a different address, rather than continually accumulating transaction records under the same permanent account as before.
Does Ethereum Really Need This?
One way to answer this question is to observe how people behave on the network.
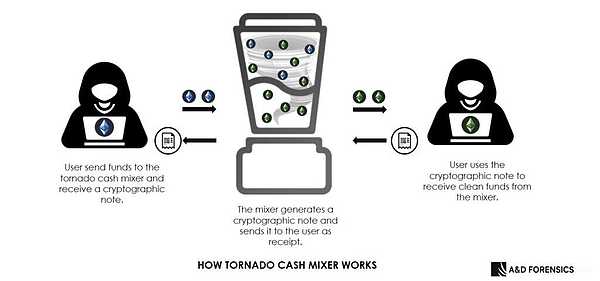
Take Tornado Cash as an example. It is a mixing protocol that allows users to deposit into a shared pool and then withdraw to a new address, thereby severing the on-chain link between sender and receiver. Even under sanctions and strict scrutiny, Tornado Cash's volume still exceeds $2.5 billion by 2025. This indicates that users are even willing to take on legal and reputational risks to hide transactions in their main wallets.
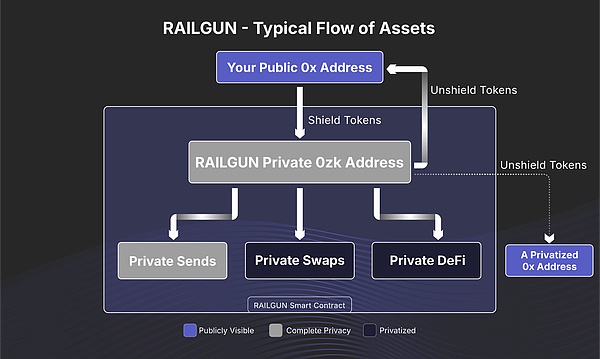
Then there's Railgun. Unlike mixers, Railgun uses zero-knowledge proofs to enable users to engage in privacy transactions without disclosing balances or transfer details. By 2025, Railgun's total value locked (TVL) is around $70 million, with cumulative transaction volumes surpassing $2 billion.
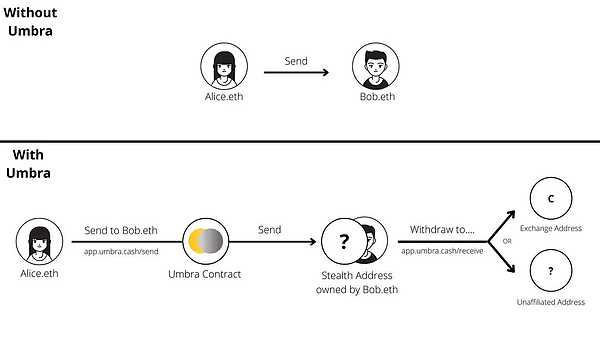
In terms of stealth receipts, Umbra has implemented application-level stealth payments on Ethereum. It allows users to publish concealed information and receive funds into disposable addresses, rather than their main wallets. By 2026, Umbra has recorded more than 77,000 active stealth addresses.
Compared to the entire cryptocurrency market, these numbers may not seem large, but they are significant.
This indicates that users actively seek isolation. They are willing to transfer funds to mixers, privacy layers, or even manually register stealth addresses, as the default model exposes too much associable information.
At the same time, all these tools have their pros and cons.
Tornado-style mixers require users to transfer funds between different contracts, adding operational friction, reducing compatibility with other applications, and putting users in a regulatory gray area. Railgun achieves privacy transactions through zero-knowledge proofs, but it remains a standalone privacy layer that users must actively choose to enable. Umbra demonstrates the practicality of stealth receiving, but it exists as a separate application rather than a wallet standard. Overall, implementing privacy protection on Ethereum requires adding extra steps beyond the default experience.
ERC-5564 takes a different approach.
It does not build another independent privacy protocol; rather, it standardizes stealth receiving at the wallet level. It addresses the simplest, most common sources of traceability, enabling address reuse without requiring users to deposit funds into pools, switch systems, or adopt specialized interfaces.
Where Does Ethereum Stand in Privacy?
Privacy in cryptocurrency is not a single design choice, but a result of a series of trade-offs.
At one end of this spectrum are protocols like Monero that embed privacy directly into the underlying system. Transaction amounts are hidden, and the addresses of senders and receivers are obfuscated. Privacy is not optional; it is enforced by design. Users do not need to choose to enable privacy protection, as confidentiality is the default state of the network.
Additionally, there is Zcash, which introduces shielded transactions using zero-knowledge proofs. Zcash allows users to choose between transparent and privacy transactions, but it operates in dedicated shielded pools rather than throughout the entire system. This architecture supports confidentiality, but it still represents a separate model rather than a fundamental behavior of the network.
Ethereum, however, has evolved along a different path.
From the start, Ethereum prioritized transparency and composability. Every contract is readable, every balance is verifiable, and any network participant can validate any state change. It is this openness that has allowed DeFi primitives, NFT markets, DAOs, and on-chain coordination to scale rapidly, as developers can rely on a shared, visible state.
The cost of this openness is structural traceability. Ethereum's privacy ecosystem has not embedded privacy into the underlying layer but has developed externally, layered on top of the protocol through tools like Tornado Cash, Railgun, and Umbra. These approaches externalize the privacy problem without altering the underlying account model.
ERC-5564 changes the way this issue is addressed. It does not add another external layer but introduces privacy as a privacy primitive within Ethereum's existing design, particularly in the receiving layer, as traceability naturally accumulates in that layer.
Privacy-focused blockchains prioritize anonymity at the protocol level, sometimes sacrificing auditability and regulatory convenience. Ethereum appears to be evolving toward a selective, programmable privacy model while preserving the transparency that initially allowed the ecosystem to function. In doing so, it expands rather than replaces its architecture.
If Monero regards privacy as foundational and Zcash views privacy as an optional mode, then ERC-5564 positions privacy as infrastructure integrated into wallet standards, rather than as something added through a separate chain or independent system.
A broader discussion is also evolving alongside this. The focus today is no longer whether blockchains should be fully transparent or completely private, but where privacy should exist, how much privacy is needed, and how it can coexist with verification and composability.
What Can Privacy Bring to Users and the Market?
Privacy is not just about hiding transactions; it also changes the incentive mechanisms and power distribution within the financial system. In this sense, privacy unlocks three core elements that we can explore one by one.
On a transparent blockchain, all operations are visible. This may seem trivial, but it is not.
When all transaction data is public, the biggest beneficiaries are not ordinary users, but those participants with the best data analytics tools, such as hedge funds, mobile internet bots, analytics firms, and AI models. The behavior of ordinary users is made public, while these savvy participants will observe, model, and extract value from it.
This creates structural asymmetry.
The issue is not transparency itself, but that transparency turns every economic action into a public signal, leading to strategies developed around these signals and profiting from them. This is also the reason democratic countries employ secret ballots. If voting is public, various interest-driven factors will overpower people's genuine intentions, causing them to vote under pressure rather than based on sincere beliefs.
The functioning of financial markets is similar.
When transactions are not easily exploitable, competition among participants is no longer about who has the more advanced monitoring tools, but about price and risk. This results in healthier, fairer market behaviors. This is the first step of privacy: it limits value extraction that arises merely because transaction activities are visible.
The second unlocking mechanism is even more significant. Privacy facilitates capital formation in ways that transparent systems cannot.
Retail users may tolerate complete transparency, but institutional users never will.
If every position can be monitored in real-time, funds cannot effectively be deployed into the DeFi space. If a fund holds a certain asset, the market may turn against it; if the fund hedges, competitors can also track the hedge operations. Strategy protection becomes impossible. The same logic applies to businesses. If supplier relationships are visible to competitors, a company cannot tokenize invoices on a public ledger; if compensation structures are fully transparent, the company cannot process salaries on-chain. Transparent systems favor experimentation but inhibit autonomous decision-making.
This is where the saying "transferring tokens is easy, but transferring keys is hard" becomes real.
On public chains, transferring assets between different networks is straightforward because all information is public. However, in privacy systems, once you leave the privacy domain, your historical transaction records are exposed, creating friction. Privacy-conscious users are more likely to stay in environments where their transaction records will not be leaked upon exit.
This dynamic creates a new type of network effect.
The competition of traditional blockchains is reflected in throughput, fees, and developer tools. Privacy introduces competition in terms of information isolation. The larger the private anonymous set, the higher the value remains within it. Liquidity also begins to concentrate in that area, as confidentiality tends to enhance with scale.
The third unlocking method can be called selective disclosure.
In today's systems, the choice of privacy is very binary: either fully public or fully hidden. But cryptography introduces a third option: you can prove certain things without exposing the underlying data.
A protocol can prove its solvency without disclosing all of its positions. An exchange can demonstrate its reserves without making personal account balances public. Users can prove their compliance with certain rules without revealing their entire transaction histories.
The rules have been verified, but the data itself does not need to be disclosed or permanently stored in centralized repositories.
This reduces the emergence of systemic data honeypots. At the same time, it lowers the trade-offs between privacy and regulation, thereby opening the door to entirely new financial application domains.
For example, private lending markets can enforce collateral rules and liquidation logic while concealing the identities of individual borrowers; platforms like Aleo and Secret Network are experimenting with this through confidential DeFi design.
On-chain dark pools can match trades without displaying order sizes or directions before execution, which is exactly what Renegade is building as a crypto trading infrastructure aimed at preventing traders from being front-run just because their intentions are visible.
Compliant stablecoins can provide regulators with access under appropriate legal procedures while preventing the public from understanding user behavior through transaction graphs. Private stablecoin projects like Paxos and Aleo, as well as the selective disclosure model pioneered by Zcash through view keys, are exploring this concept.
Trade finance platforms can tokenize invoices and prove that invoices have not been double-financed without disclosing supplier relationships. Enterprise networks like Canton Network are piloting this confidential infrastructure in collaboration with major financial institutions, allowing businesses to share ledger efficiencies without revealing sensitive commercial data.
All of this will also lead to long-term behavioral effects.
Transparent systems permanently link identity with financial behavior. Over time, this suppresses the inclination to deviate from the norm and lowers the willingness to try new things, as behavior cannot be uncoupled from long-term identity. Privacy restores the separation between participation and permanent exposure. It allows users to act without having every decision recorded in an immutable public record.
The primary purpose of transparent cryptocurrencies is verifiability. In contrast, privacy-designed cryptocurrencies extend this shared state to support autonomy, institutional capital, and selective disclosure without sacrificing verifiability.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



